Cryptography Review Day David Brumley dbrumleycmu edu Carnegie
Cryptography: Review Day David Brumley dbrumley@cmu. edu Carnegie Mellon University
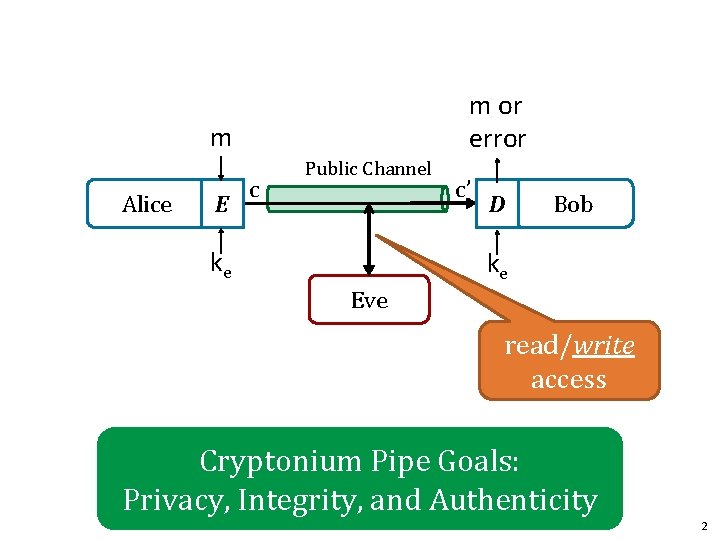
m or error m Alice E c Public Channel ke c’ D Bob ke Eve read/write access Cryptonium Pipe Goals: Privacy, Integrity, and Authenticity 2

3
Privacy and Encryption 4
![Perfect Secrecy [Shannon 1945] (Information Theoretic Secrecy) Defn Perfect Secrecy (informal): We’re no better Perfect Secrecy [Shannon 1945] (Information Theoretic Secrecy) Defn Perfect Secrecy (informal): We’re no better](http://slidetodoc.com/presentation_image_h2/959812b64667b7c391b6a0b3ccb9da3e/image-5.jpg)
Perfect Secrecy [Shannon 1945] (Information Theoretic Secrecy) Defn Perfect Secrecy (informal): We’re no better off determining the plaintext when given the ciphertext. Alice Bob Eve 1. Eve observes everything but the c. Guesses m 1 2. Eve observes c. Guesses m 2 Goal: 5
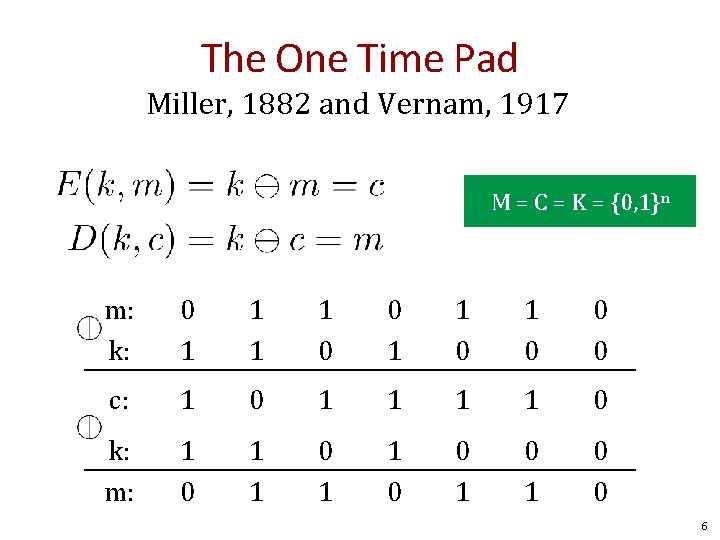
The One Time Pad Miller, 1882 and Vernam, 1917 M = C = K = {0, 1}n m: k: 0 1 1 0 0 0 c: 1 0 1 1 0 k: m: 1 0 1 1 0 0 6
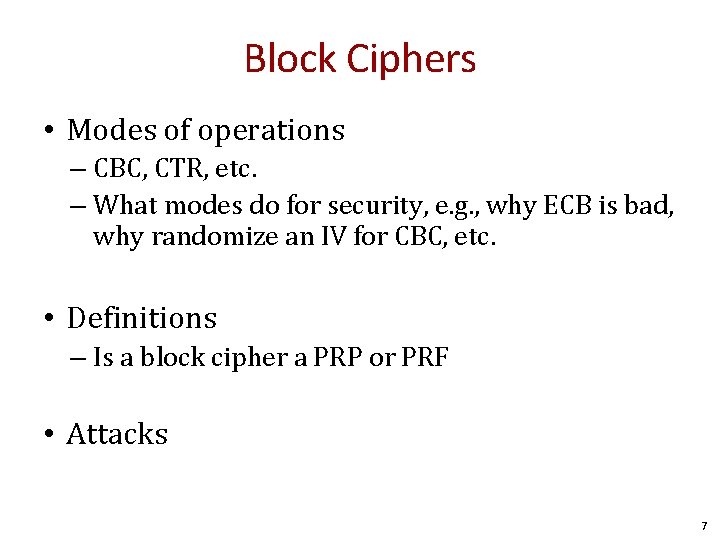
Block Ciphers • Modes of operations – CBC, CTR, etc. – What modes do for security, e. g. , why ECB is bad, why randomize an IV for CBC, etc. • Definitions – Is a block cipher a PRP or PRF • Attacks 7
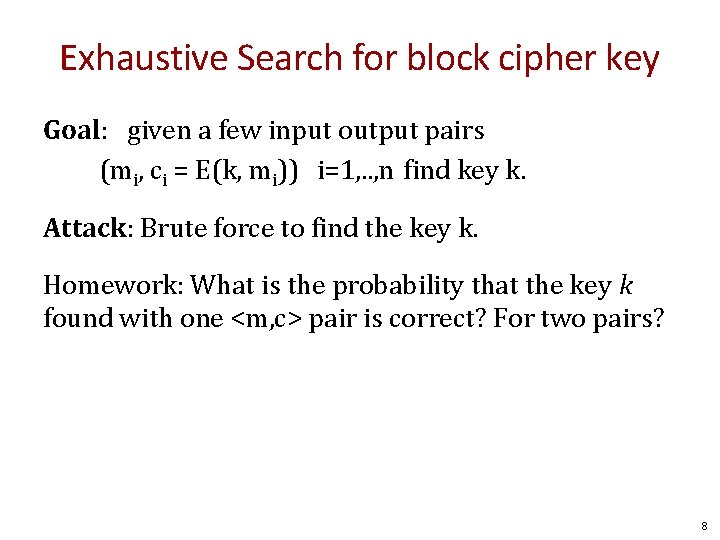
Exhaustive Search for block cipher key Goal: given a few input output pairs (mi, ci = E(k, mi)) i=1, . . , n find key k. Attack: Brute force to find the key k. Homework: What is the probability that the key k found with one <m, c> pair is correct? For two pairs? 8
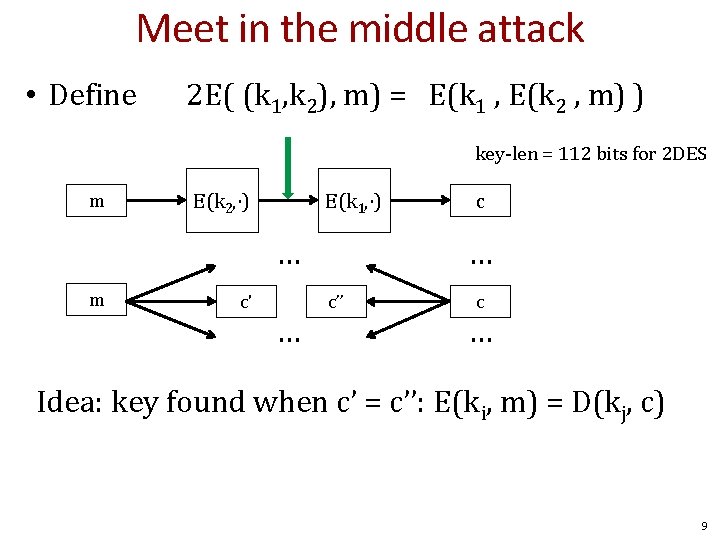
Meet in the middle attack • Define 2 E( (k 1, k 2), m) = E(k 1 , E(k 2 , m) ) key-len = 112 bits for 2 DES m E(k 2, ⋅) E(k 1, ⋅) … m c' … c’’ c … Idea: key found when c’ = c’’: E(ki, m) = D(kj, c) 9
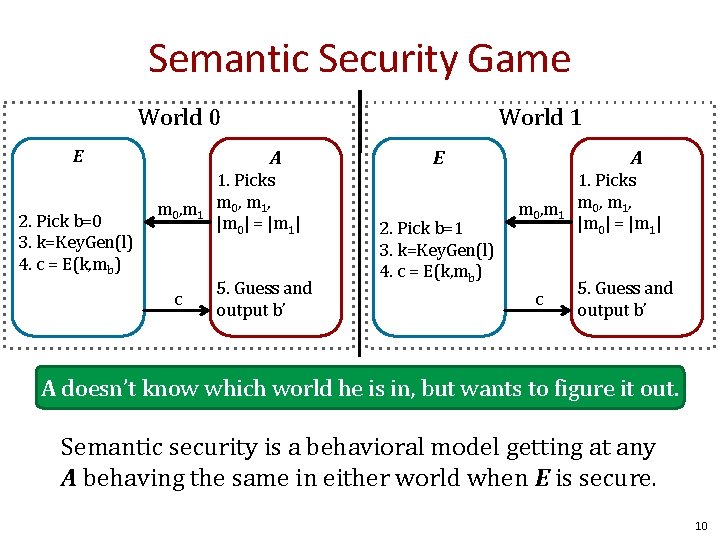
Semantic Security Game World 0 E 2. Pick b=0 3. k=Key. Gen(l) 4. c = E(k, mb) World 1 A m 0, m 1 c 1. Picks m 0 , m 1 , |m 0| = |m 1| 5. Guess and output b’ A E 2. Pick b=1 3. k=Key. Gen(l) 4. c = E(k, mb) m 0, m 1 c 1. Picks m 0 , m 1 , |m 0| = |m 1| 5. Guess and output b’ A doesn’t know which world he is in, but wants to figure it out. Semantic security is a behavioral model getting at any A behaving the same in either world when E is secure. 10
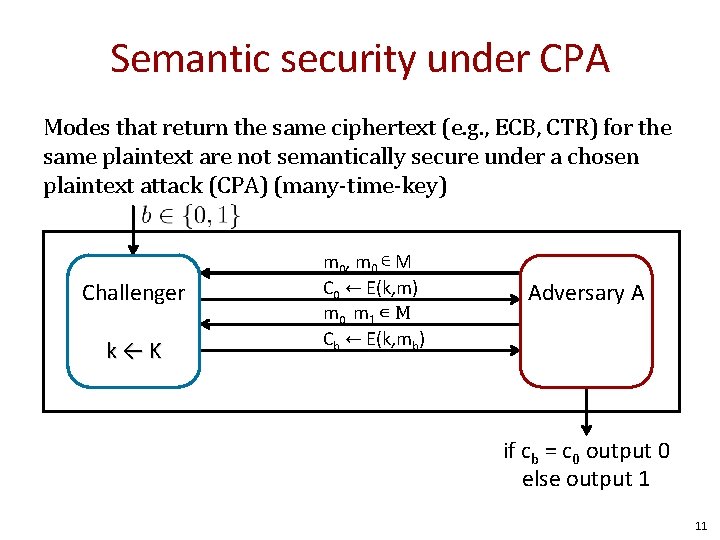
Semantic security under CPA Modes that return the same ciphertext (e. g. , ECB, CTR) for the same plaintext are not semantically secure under a chosen plaintext attack (CPA) (many-time-key) Challenger k←K m 0 , m 0 ∊ M C 0 ← E(k, m) m 0, m 1 ∊ M Cb ← E(k, mb) Adversary A if cb = c 0 output 0 else output 1 11
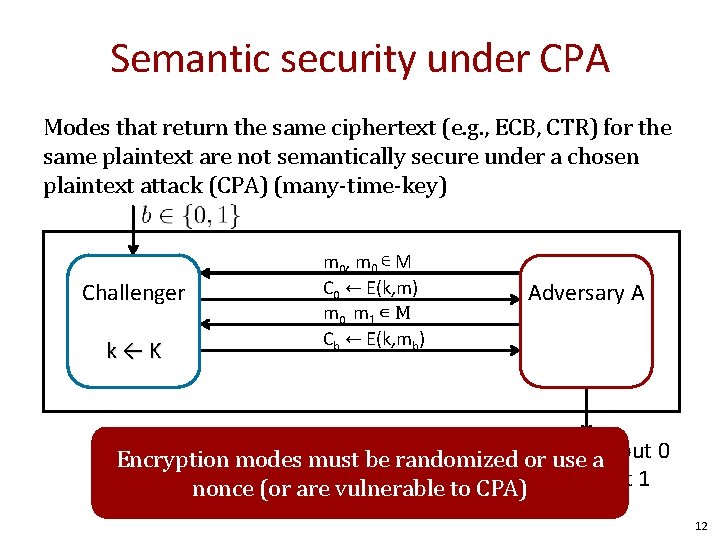
Semantic security under CPA Modes that return the same ciphertext (e. g. , ECB, CTR) for the same plaintext are not semantically secure under a chosen plaintext attack (CPA) (many-time-key) Challenger k←K m 0 , m 0 ∊ M C 0 ← E(k, m) m 0, m 1 ∊ M Cb ← E(k, mb) Adversary A if cor c 0 output 0 b =use Encryption modes must be randomized a nonce (or are vulnerable to CPA)else output 1 12
Hashes and MACS 13
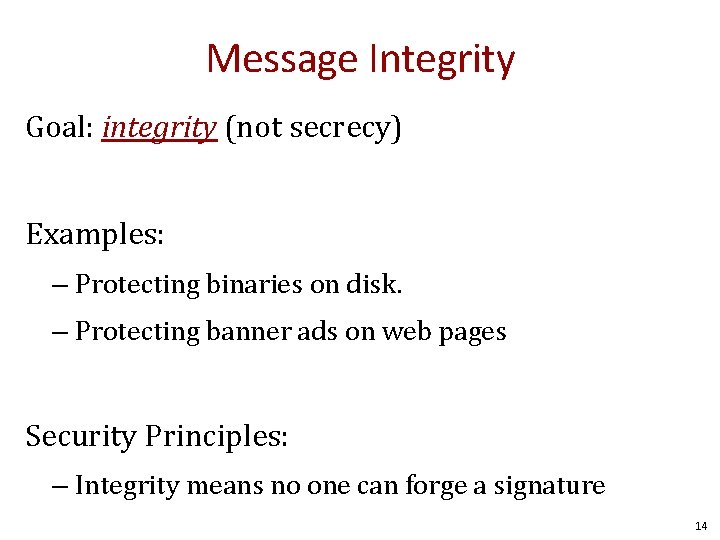
Message Integrity Goal: integrity (not secrecy) Examples: – Protecting binaries on disk. – Protecting banner ads on web pages Security Principles: – Integrity means no one can forge a signature 14
![PRF Security Game (A behavioral model) World 0 E World 1 A 2. if(tbl[x] PRF Security Game (A behavioral model) World 0 E World 1 A 2. if(tbl[x]](http://slidetodoc.com/presentation_image_h2/959812b64667b7c391b6a0b3ccb9da3e/image-15.jpg)
PRF Security Game (A behavioral model) World 0 E World 1 A 2. if(tbl[x] undefined) tbl[x] = rand() return y =tbl[x] A E 1. Picks x x 5. Guess and output b’ y 1. Picks x y = PRF(x) x 3. Outputs guess for b y A doesn’t know which world he is in, but wants to figure it out. For b=0, 1: Wb : = [ event that A(Wb) =1 ] Adv. SS[A, E] : = | Pr[ W 0 ] − Pr[ W 1 ] | ∈ [0, 1] Always 1 15
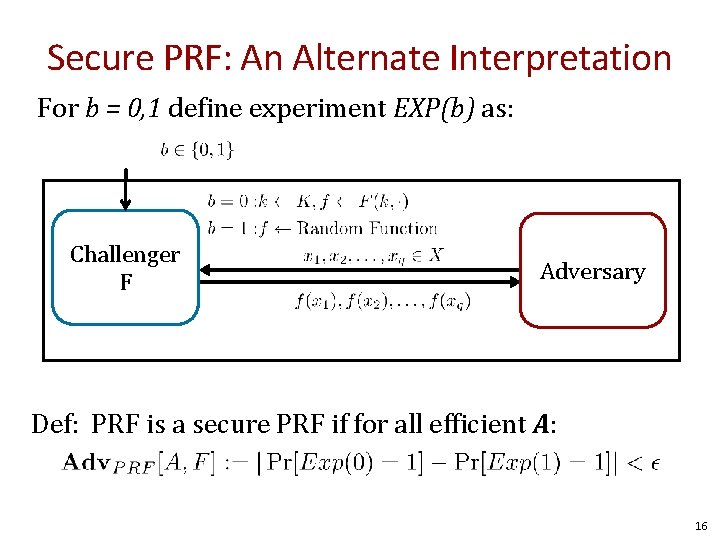
Secure PRF: An Alternate Interpretation For b = 0, 1 define experiment EXP(b) as: Challenger F Adversary Def: PRF is a secure PRF if for all efficient A: 16
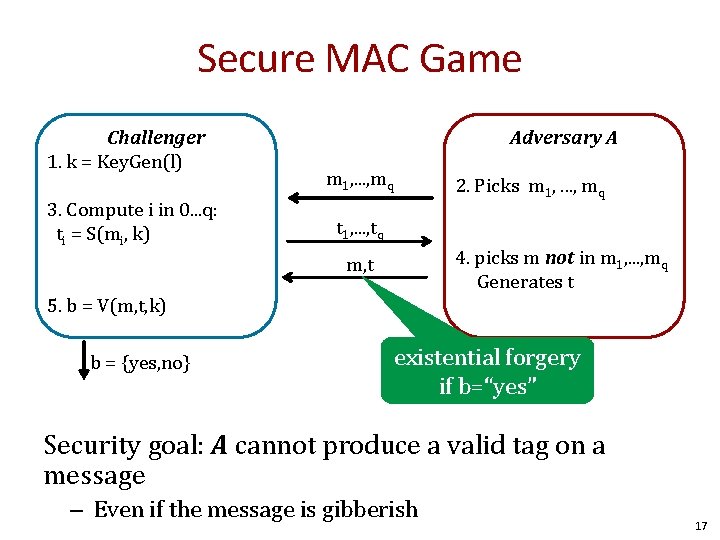
Secure MAC Game Challenger 1. k = Key. Gen(l) 3. Compute i in 0. . . q: ti = S(mi, k) Adversary A m 1, . . . , mq 2. Picks m 1, . . . , mq t 1, . . . , tq 4. picks m not in m 1, . . . , mq Generates t m, t 5. b = V(m, t, k) b = {yes, no} existential forgery if b=“yes” Security goal: A cannot produce a valid tag on a message – Even if the message is gibberish 17
Birthday Paradox Rule of Thumb Given N possibilities, and random samples x 1, . . . , xj, PR[xi = xj] ≈ 50% when j = N 1/2 18
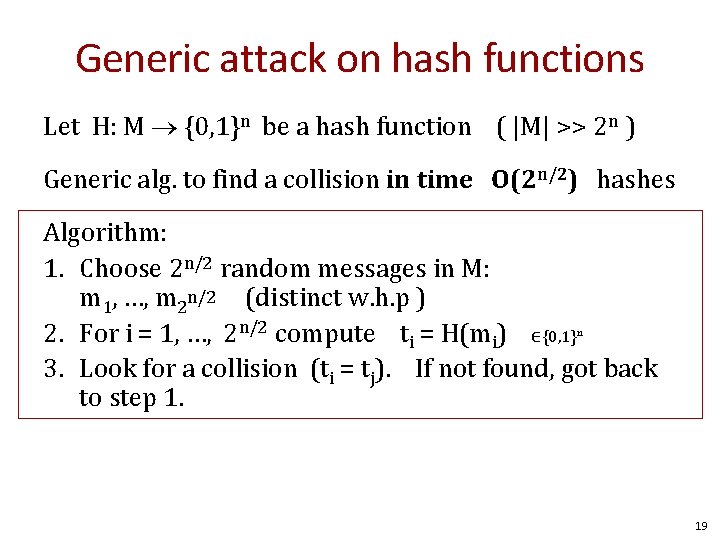
Generic attack on hash functions Let H: M {0, 1}n be a hash function ( |M| >> 2 n ) Generic alg. to find a collision in time O(2 n/2) hashes Algorithm: 1. Choose 2 n/2 random messages in M: m 1, …, m 2 n/2 (distinct w. h. p ) 2. For i = 1, …, 2 n/2 compute ti = H(mi) ∈{0, 1}n 3. Look for a collision (ti = tj). If not found, got back to step 1. How well will this work? 19
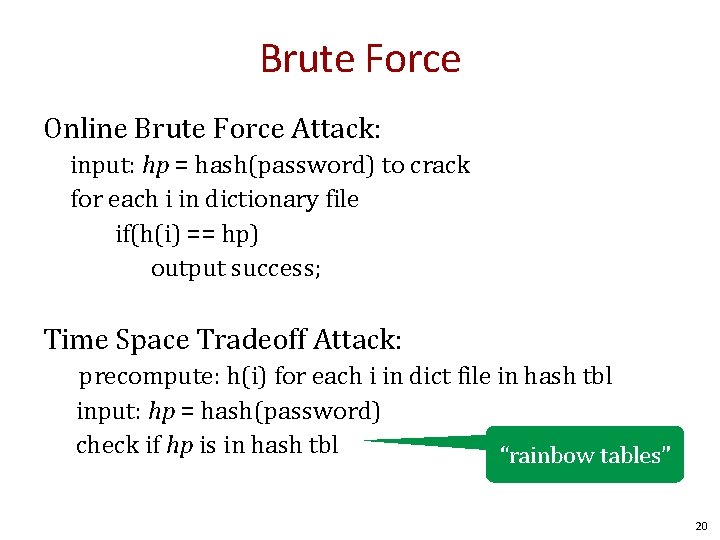
Brute Force Online Brute Force Attack: input: hp = hash(password) to crack for each i in dictionary file if(h(i) == hp) output success; Time Space Tradeoff Attack: precompute: h(i) for each i in dict file in hash tbl input: hp = hash(password) check if hp is in hash tbl “rainbow tables” 20
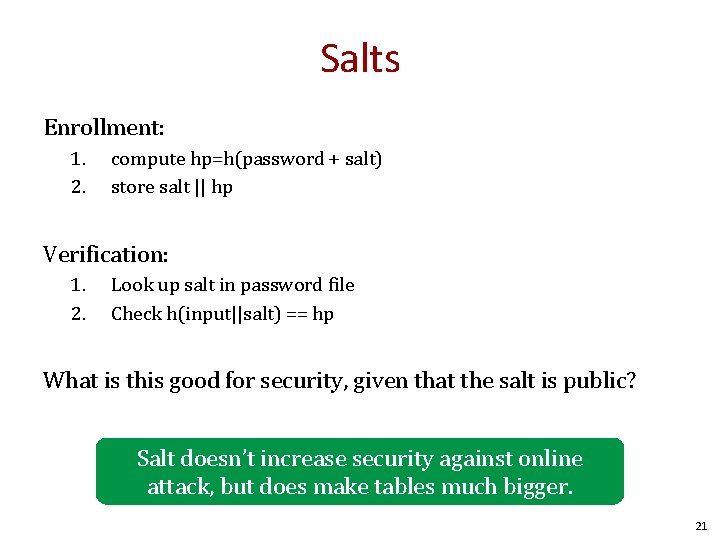
Salts Enrollment: 1. 2. compute hp=h(password + salt) store salt || hp Verification: 1. 2. Look up salt in password file Check h(input||salt) == hp What is this good for security, given that the salt is public? Salt doesn’t increase security against online attack, but does make tables much bigger. 21
Authenticated Encryption 22
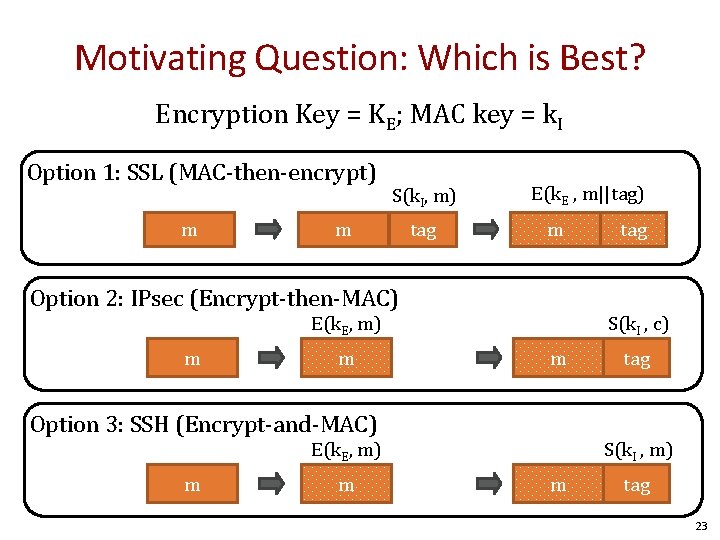
Motivating Question: Which is Best? Encryption Key = KE; MAC key = k. I Option 1: SSL (MAC-then-encrypt) m S(k. I, m) m tag E(k. E , m||tag) m Option 2: IPsec (Encrypt-then-MAC) S(k. I , c) E(k. E, m) m m m Option 3: SSH (Encrypt-and-MAC) m tag S(k. I , m) E(k. E, m) m tag 23
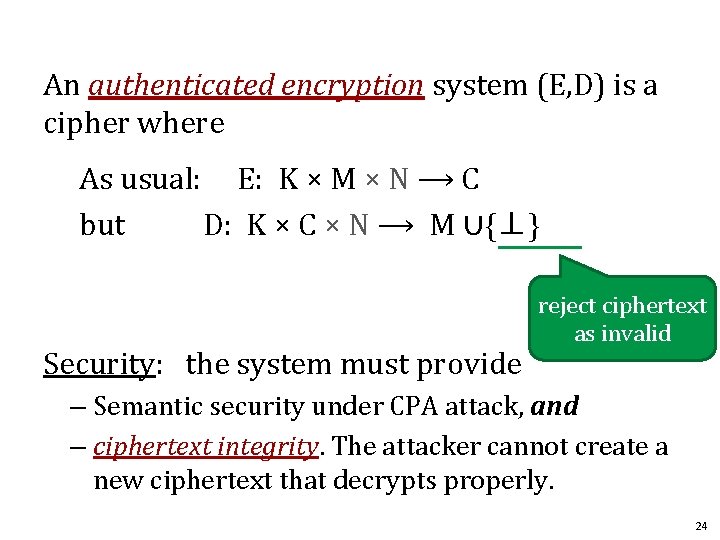
An authenticated encryption system (E, D) is a cipher where As usual: E: K × M × N ⟶ C but D: K × C × N ⟶ M ∪{⊥} Security: the system must provide reject ciphertext as invalid – Semantic security under CPA attack, and – ciphertext integrity. The attacker cannot create a new ciphertext that decrypts properly. 24
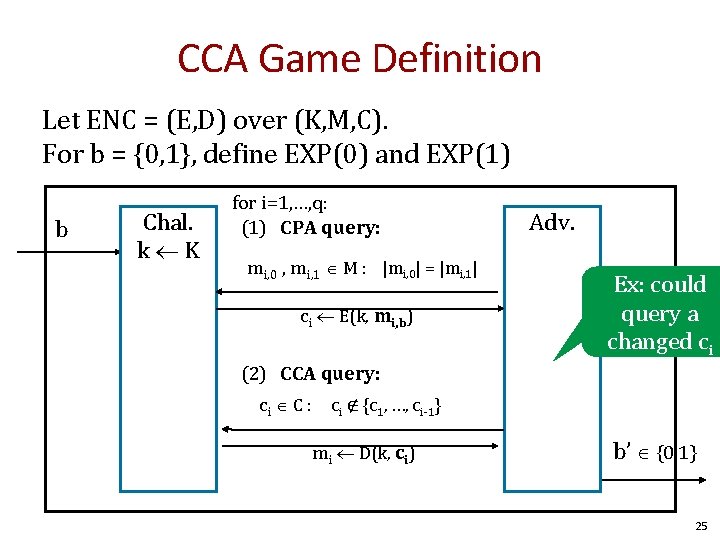
CCA Game Definition Let ENC = (E, D) over (K, M, C). For b = {0, 1}, define EXP(0) and EXP(1) b Chal. k K for i=1, …, q: (1) CPA query: mi, 0 , mi, 1 M : |mi, 0| = |mi, 1| ci E(k, mi, b) Adv. Ex: could query a changed ci (2) CCA query: ci C : ci ∉ {c 1, …, ci-1} mi D(k, ci) b’ {0, 1} 25
Public Key Cryptography 26
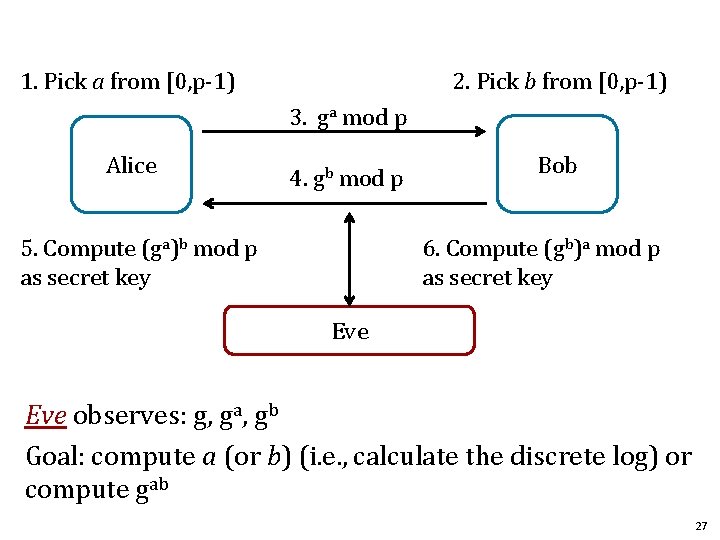
1. Pick a from [0, p-1) 2. Pick b from [0, p-1) 3. ga mod p Alice 4. gb mod p 5. Compute (ga)b mod p as secret key Bob 6. Compute (gb)a mod p as secret key Eve observes: g, ga, gb Goal: compute a (or b) (i. e. , calculate the discrete log) or compute gab 27
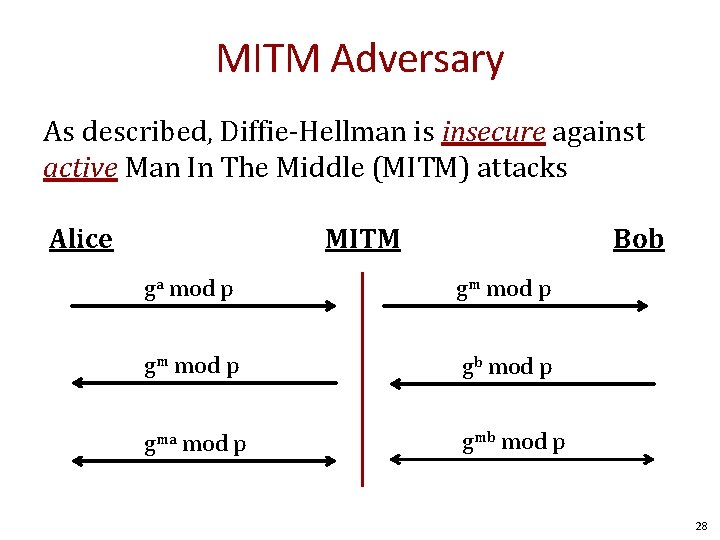
MITM Adversary As described, Diffie-Hellman is insecure against active Man In The Middle (MITM) attacks Alice MITM Bob ga mod p gm mod p gb mod p gma mod p gmb mod p 28
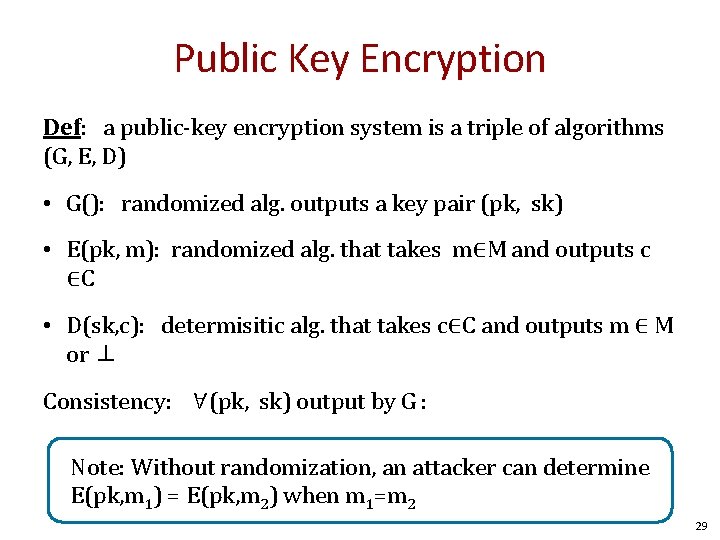
Public Key Encryption Def: a public-key encryption system is a triple of algorithms (G, E, D) • G(): randomized alg. outputs a key pair (pk, sk) • E(pk, m): randomized alg. that takes m∈M and outputs c ∈C • D(sk, c): determisitic alg. that takes c∈C and outputs m ∈ M or ⊥ Consistency: ∀(pk, sk) output by G : ∀m∈M: D(sk, E(pk, m) ) = m Note: Without randomization, an attacker can determine E(pk, m 1) = E(pk, m 2) when m 1=m 2 29
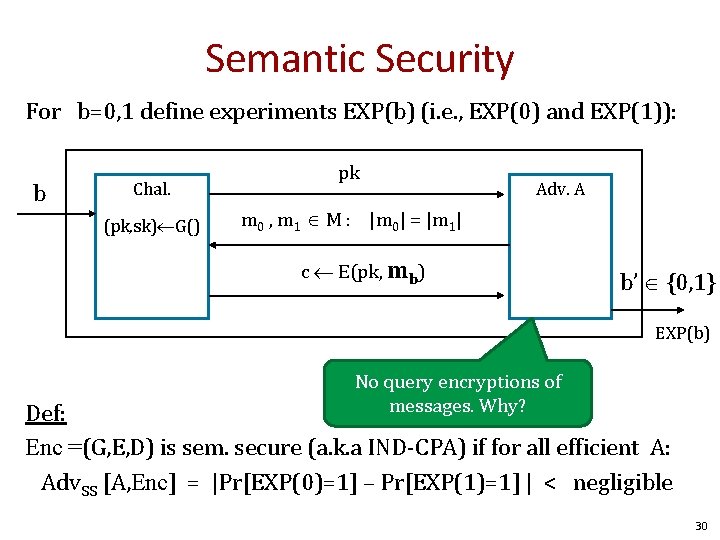
Semantic Security For b=0, 1 define experiments EXP(b) (i. e. , EXP(0) and EXP(1)): b Chal. (pk, sk) G() pk Adv. A m 0 , m 1 M : |m 0| = |m 1| c E(pk, mb) b’ {0, 1} EXP(b) No query encryptions of messages. Why? Def: Enc =(G, E, D) is sem. secure (a. k. a IND-CPA) if for all efficient A: Adv. SS [A, Enc] = |Pr[EXP(0)=1] – Pr[EXP(1)=1] | < negligible 30
Easy and Hard Problems • Factoring • Discrete Log • Exponentiation 31

Questions? 32
END

Thought 34
- Slides: 34