Lest We Remember ColdBoot Attacks on Encryption Keys
Lest We Remember: Cold-Boot Attacks on Encryption Keys HEE SEOK KIM – 2017. 11. 06 AUTHORS: J. ALEX HALDERMAN, SETH D. SCHOEN, NADIA HENINGER, WILLIAM CLARKSON, WILLIAM PAUL, JOSEPH A. CALANDRINO, ARIEL J. FELDMAN, JACOB APPELBAUM, AND EDWARD W. FELTEN
On February 2008…
DRAMs…
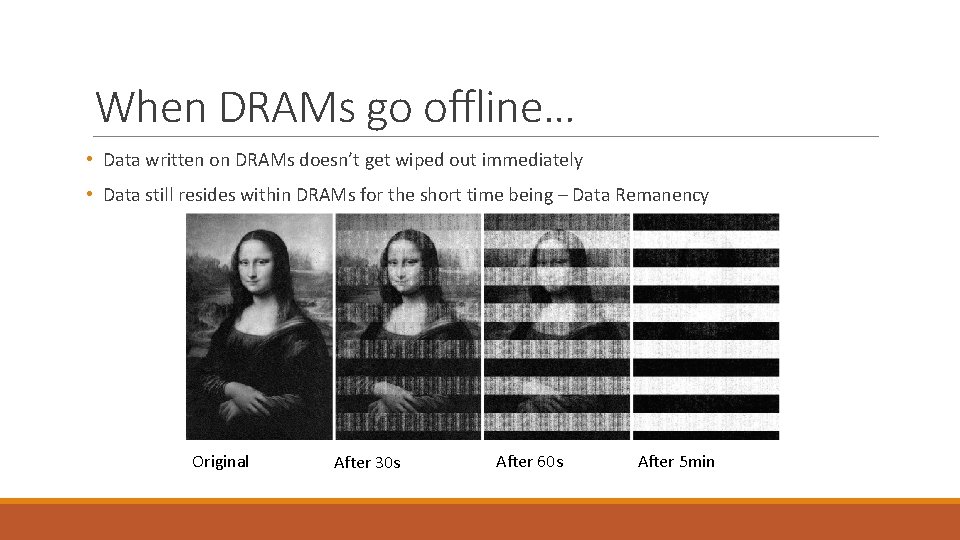
When DRAMs go offline… • Data written on DRAMs doesn’t get wiped out immediately • Data still resides within DRAMs for the short time being – Data Remanency Original After 30 s After 60 s After 5 min
When DRAMs go offline… • Also data fades slower in lower temperatures
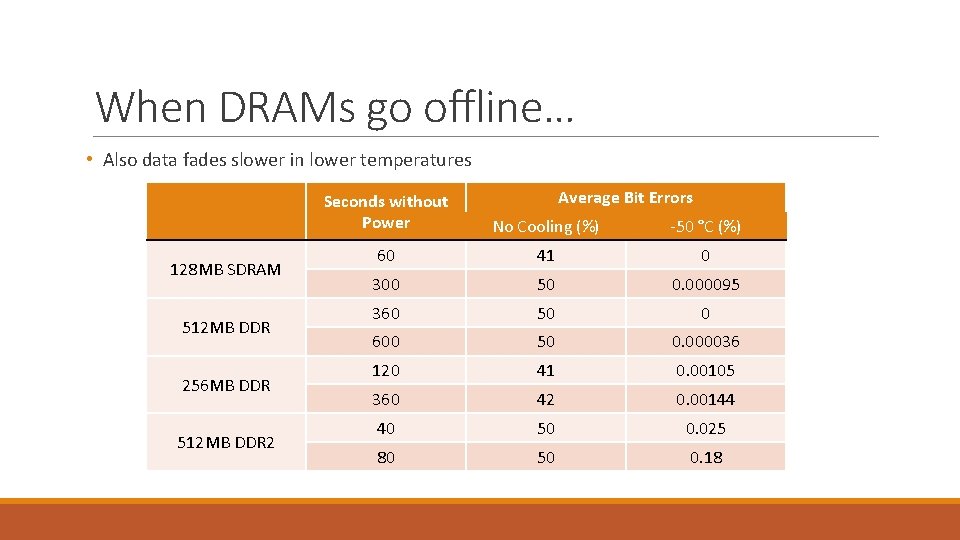
When DRAMs go offline… • Also data fades slower in lower temperatures 128 MB SDRAM 512 MB DDR 256 MB DDR 512 MB DDR 2 Average Bit Errors Seconds without Power No Cooling (%) -50 °C (%) 60 41 0 300 50 0. 000095 360 50 0 600 50 0. 000036 120 41 0. 00105 360 42 0. 00144 40 50 0. 025 80 50 0. 18
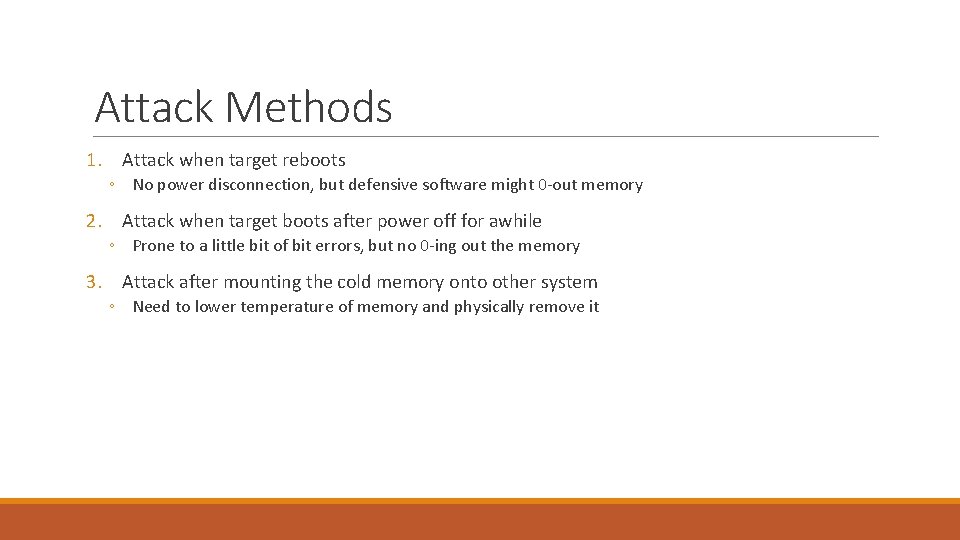
Attack Methods 1. Attack when target reboots ◦ No power disconnection, but defensive software might 0 -out memory 2. Attack when target boots after power off for awhile ◦ Prone to a little bit of bit errors, but no 0 -ing out the memory 3. Attack after mounting the cold memory onto other system ◦ Need to lower temperature of memory and physically remove it
Lowering Bit Error Rate • Lower the temperature of memory • As shown in the experiment above, it prolongs data kept inside with lower corruption rate • Use error correcting algorithm provided • Algorithm can be used to recover DES, AES and RSA keys
DES Key Reconstruction • DES encryption uses 16 round-keys produced from key scheduling of a master key • 14 of those 16 round-keys have repeated key within • Consider those 14 round-keys as the repetition code of each bit from the original key, then correct error accordingly. • Experiments showed 98% chance of correctly reconstructing the original key with 50% bit error
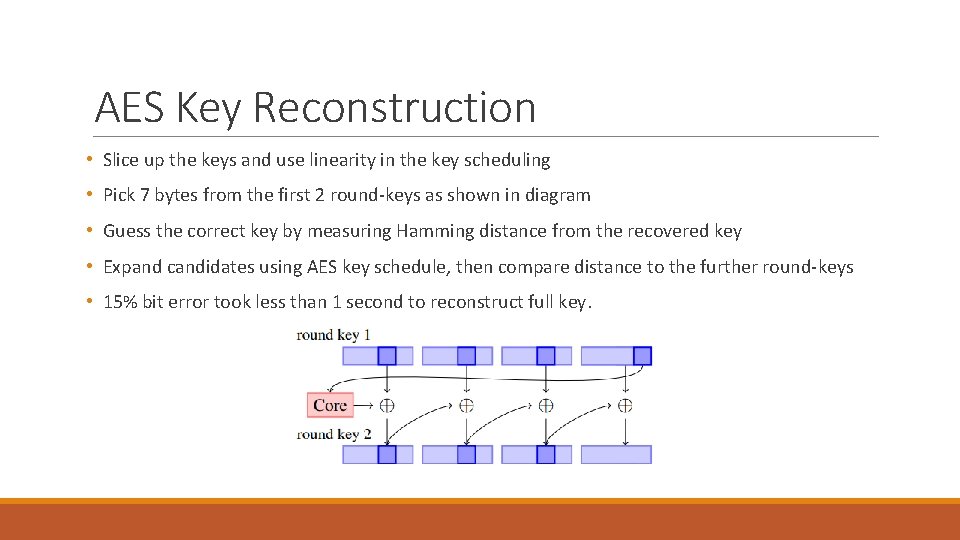
AES Key Reconstruction • Slice up the keys and use linearity in the key scheduling • Pick 7 bytes from the first 2 round-keys as shown in diagram • Guess the correct key by measuring Hamming distance from the recovered key • Expand candidates using AES key schedule, then compare distance to the further round-keys • 15% bit error took less than 1 second to reconstruct full key.
RSA Key Reconstruction • Previous attacks on RSA with least significant bit is not usable as bit errors may propagate onto those bits • Instead, deduce and build values from least significant bits. • Note that we know for sure that THE least significant bit is always 1, as prime number > 2 • With error rate 4%, reconstruction took 4. 5 secs as a median value, while 6% error took 2. 5 minutes.
Key Identification • AES key identification 1. 2. 3. 4. Consider 176 or 240 bytes as key schedule For each word ( byte ) in the potential key schedule, calculate distance between that byte to the byte that supposedly produced from surrounding bytes If Hamming distance is low, consider it as real key schedule, output the key Iterate through all the bytes in the memory
Key Identification • RSA key identification – Look for RSA private key formats. 1. 2. Query through memory for known fields in PKCS ( consists of version, modulus, public. Exponent, private. Exponent, prime 1, prime 2, exponent 1, exponent 2, and more fields ), then locate the private key. ( One can easily get public key component if attacking a server ) Search for the part of memory that has similar structure to DER encoding.
Attacking Bit. Locker • A disk encryption feature for Win Vista or 7 • Uses AES-CBC encryption • Laptop with 2 GB memory as a target medium • Need to recover secret padding key and CBC encryption key • Attacked on both reboot method and power off method without any cooling • Took 25 min to recover keys and decrypt entire disk https: //youtu. be/JDaic. PIgn 9 U? t=3 m
Attacking File. Vault • Disk encryption for Mac OS X • User password for Initialization vector • Encrypts through AES-CBC mode • Used Intel-based Machintosh using Mac OS 10. 4 • Need to find secret padding key and CBC encryption key ( IV is only need to decrypt first block )
Proposed Mitigations 1. Encrypting memory when suspending the system 2. Store keys in other places than memory 3. Limit booting from network or USB 4. Physical Defenses using something like sensors 5. Encrypting in the disk controller instead of memory
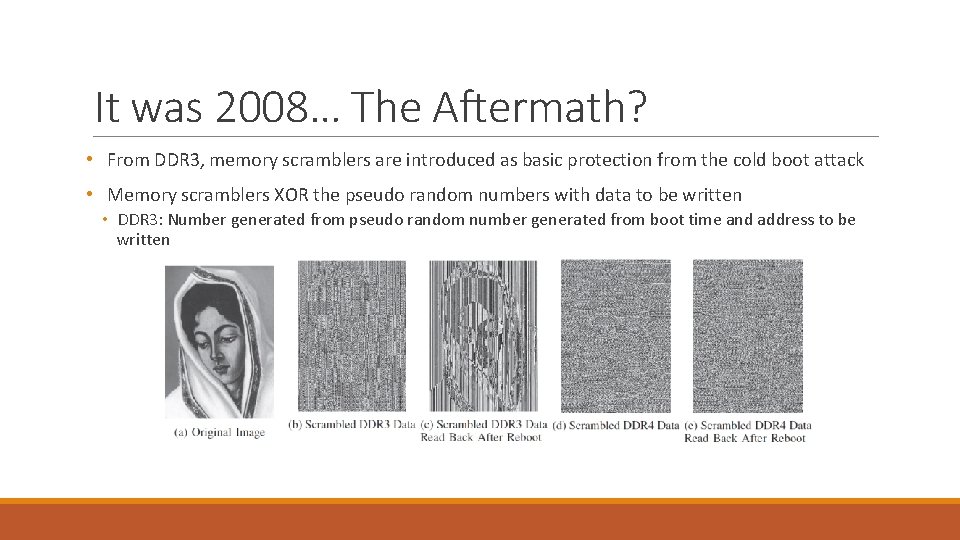
It was 2008… The Aftermath? • From DDR 3, memory scramblers are introduced as basic protection from the cold boot attack • Memory scramblers XOR the pseudo random numbers with data to be written • DDR 3: Number generated from pseudo random number generated from boot time and address to be written
It was 2008… The Aftermath? • DDR 3 was broken in 2016 • Attack effective on both DDR 3 and DDR 4 was released on 2017 • Intel SGX, by far, can provide effective defense against cold boot attack.
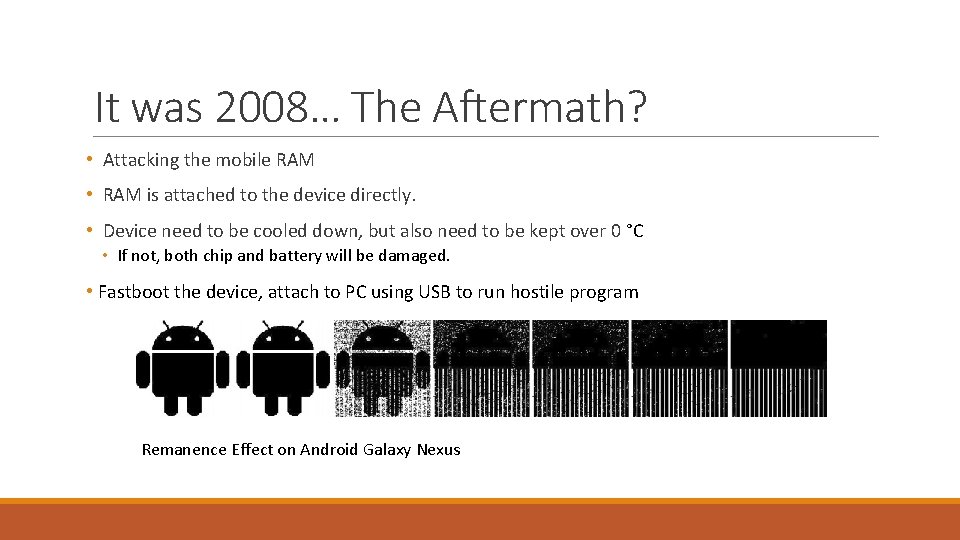
It was 2008… The Aftermath? • Attacking the mobile RAM • RAM is attached to the device directly. • Device need to be cooled down, but also need to be kept over 0 °C • If not, both chip and battery will be damaged. • Fastboot the device, attach to PC using USB to run hostile program Remanence Effect on Android Galaxy Nexus
Recent Defenses Encrypting outside of DRAM: 1. Cache-based: ◦ Copker – 2011 ◦ Sentry – 2015 ◦ Ca. SE - 2016 2. Register-based: ◦ TRESOR – 2014 3. GPU-based: ◦ Pixel. Vault – 2014
Conclusion • Remanency of RAM lasts long • Just hibernating laptops or phones wouldn’t save you • Information on DRAM is easy to attack
Additional References Yitbarek, Salessawi Ferede, et al. "Cold Boot Attacks are Still Hot: Security Analysis of Memory Scramblers in Modern Processors. " High Performance Computer Architecture (HPCA), 2017 IEEE International Symposium on. IEEE, 2017. Bauer, Johannes, Michael Gruhn, and Felix C. Freiling. "Lest we forget: Cold-boot attacks on scrambled DDR 3 memory. " Digital Investigation 16 (2016): S 65 -S 74. Müller, Tilo, and Michael Spreitzenbarth. "Frost. " International Conference on Applied Cryptography and Network Security. Springer, Berlin, Heidelberg, 2013. Müller, Tilo, Felix C. Freiling, and Andreas Dewald. "TRESOR Runs Encryption Securely Outside RAM. " USENIX Security Symposium. Vol. 17. 2011. Guan, Le, et al. "Copker: Computing with Private Keys without RAM. " NDSS. 2014. Vasiliadis, Giorgos, et al. "Pixelvault: Using gpus for securing cryptographic operations. " Proceedings of the 2014 ACM SIGSAC Conference on Computer and Communications Security. ACM, 2014. Colp, Patrick, et al. "Protecting data on smartphones and tablets from memory attacks. " ACM SIGPLAN Notices 50. 4 (2015): 177189. Zhang, Ning, et al. "Ca. SE: Cache-assisted secure execution on ARM processors. " Security and Privacy (SP), 2016 IEEE Symposium on. IEEE, 2016.
Q&A THANK YOU FOR LISTENING
- Slides: 23