LAB8 PKI DIGITAL CERTIFICATE CPIT 425 Public Key
LAB#8 PKI & DIGITAL CERTIFICATE CPIT 425
Public Key Infrastructure PKI 2 Public key infrastructure is the term used to describe the laws, policies, procedures, standards, and software that regulate or control the operation of certificates and public and private keys. http: //www. pki. gov. sa/ Our goal is to use Java APIs and tools to perform PKI operations Digital certificates the most basic building blocks of PKI. Certificates are digital documents, a stream of bytes, contains a public key with the identity of the corresponding private key owner and is signed by a trusted entity and known as Certification Authority or just CA. The owner of the private key is known as the subject and
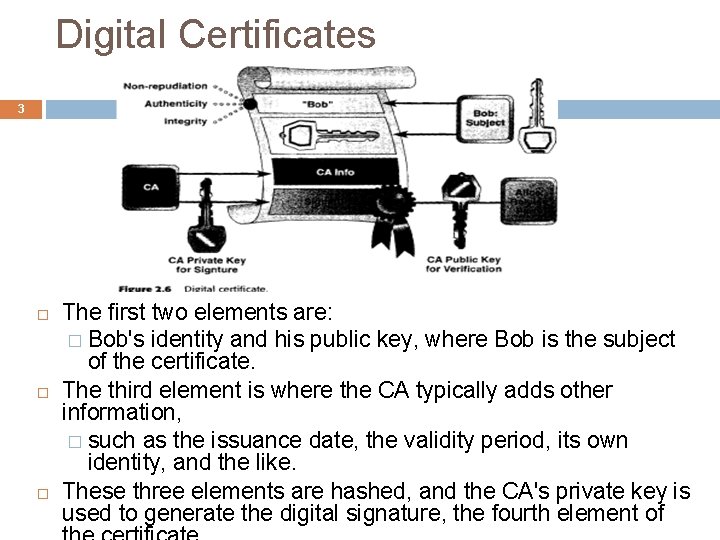
Digital Certificates 3 The first two elements are: � Bob's identity and his public key, where Bob is the subject of the certificate. The third element is where the CA typically adds other information, � such as the issuance date, the validity period, its own identity, and the like. These three elements are hashed, and the CA's private key is used to generate the digital signature, the fourth element of
4 Signed vs. Selfsigned Certificates When it comes down to trust; in signed certificates a certificate authority CA tells your customers that this server information of a particular website has been verified by a trusted source (Owner different than Issuer). When you use a certificate signed by a CA, you are saying, "Trust me – (Verisign, Comodo or Cacert …) (CAs) agrees I am who I say I am. “ When you use a self-signed certificate (Owner is the Issuer), you are saying to your customers "trust me - I am who I say I am“.
Self-signed Certificates 5 When Can You Use a Self-Signed Certificate? Self-signed certificates are great for testing servers. If you're creating a website that you need to test over an https connection, you don't have to pay for a signed certificate for that testing site. You just need to tell your testers that their browser may pop warning messages. If You're Doing Ecommerce You Need a Signed Certificate
JAVA: Keytool utility 6 keytool is a key and certificate management utility. It enables users to administer their own public/private key pairs and associated certificates for use in selfauthentication (where the user authenticates himself/herself to other users/services) or data integrity and authentication services, using digital signatures. You can generate self-signed certificates and manage them (import, export and list the contents) with JAVA utility called keytool. Keytool utility is an application comes with JDK 1. 4 and higher, Keytool Path is “C: Program Files Javajdk 1. 5. 0_06binkeytool. exe” in Windows Vista. A keystore is a password-protected file which stores the keys and certificates. The keytool use as default a keystore file “. keystore".
Keytool 7 Basic commands: � -genkey – creates public/private key pair and stores in keystore � -delete – deletes a key pair from a keystore � -export – exports a certificate � -import – import certificate from trusted authority � -list – list contents of keystore � -printcert – display a certificate
1)Generating Selfsigned Certificates 8 To Generate an RSA key pair and self-signed certificate: A. Open a Command Prompt window. B. Type the following command into the window: <your path to keytool> keytool -genkey -alias myalias -keyalg RSA -validity 365 –keystore my. keystore Where: <path to keytool> is the path to the keytool executable in the JDK which is usually in : C: Program FilesJavajdk 1. 5. 0_06bin. -genkey is the generate key option. -alias <friendly_name> is the friendly name that are using for your certificate Question: How could you go to a specific directory in DOS?
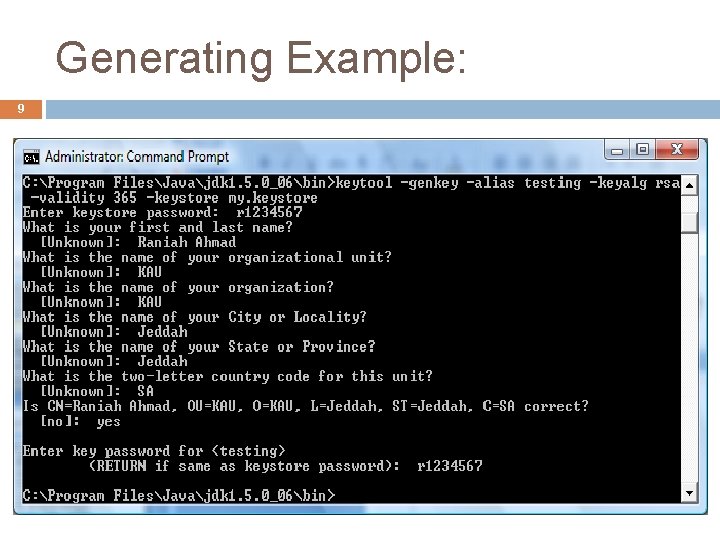
Generating Example: 9
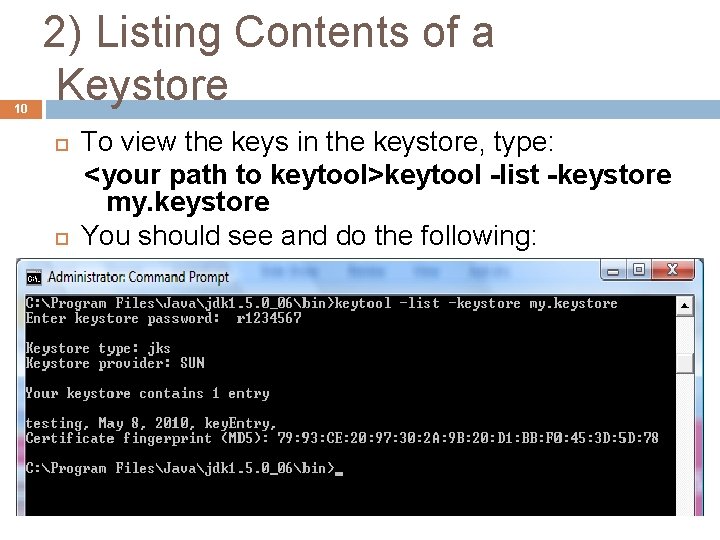
10 2) Listing Contents of a Keystore To view the keys in the keystore, type: <your path to keytool>keytool -list -keystore my. keystore You should see and do the following:
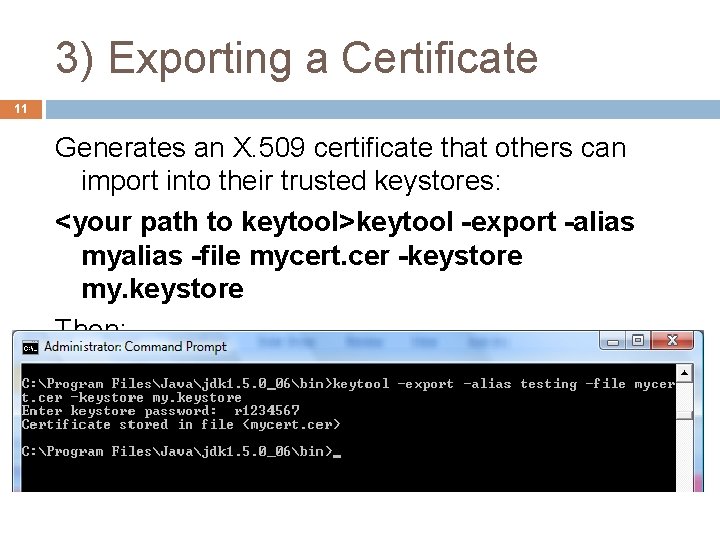
3) Exporting a Certificate 11 Generates an X. 509 certificate that others can import into their trusted keystores: <your path to keytool>keytool -export -alias myalias -file mycert. cer -keystore my. keystore Then:
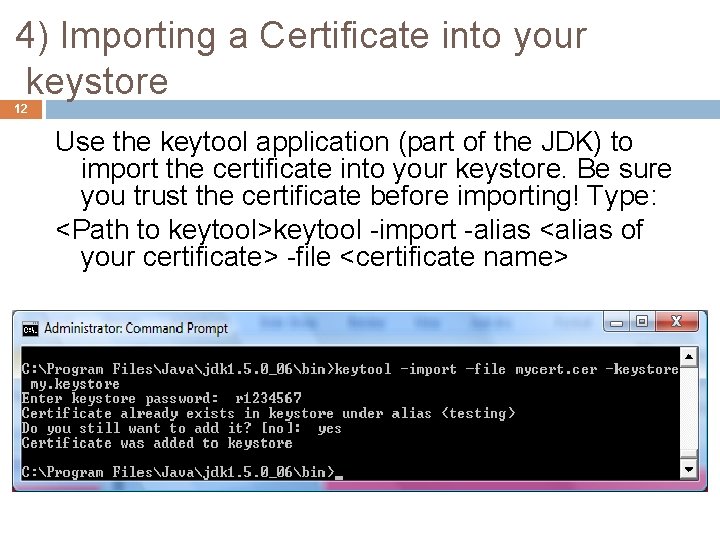
4) Importing a Certificate into your keystore 12 Use the keytool application (part of the JDK) to import the certificate into your keystore. Be sure you trust the certificate before importing! Type: <Path to keytool>keytool -import -alias <alias of your certificate> -file <certificate name>
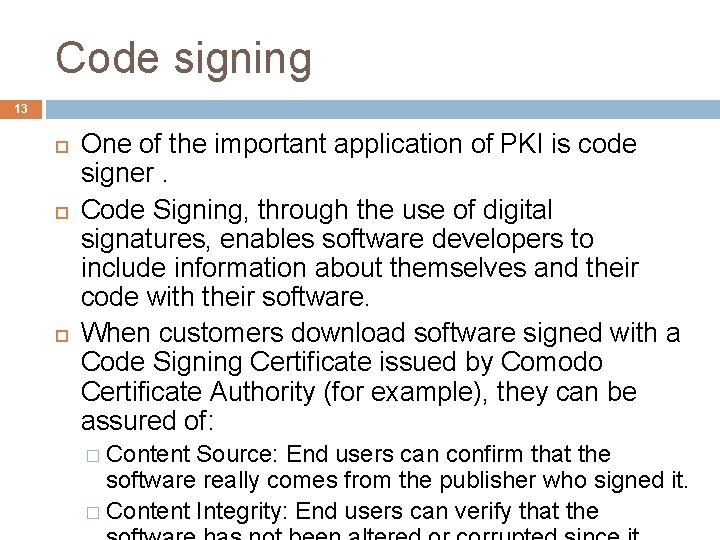
Code signing 13 One of the important application of PKI is code signer. Code Signing, through the use of digital signatures, enables software developers to include information about themselves and their code with their software. When customers download software signed with a Code Signing Certificate issued by Comodo Certificate Authority (for example), they can be assured of: � Content Source: End users can confirm that the software really comes from the publisher who signed it. � Content Integrity: End users can verify that the
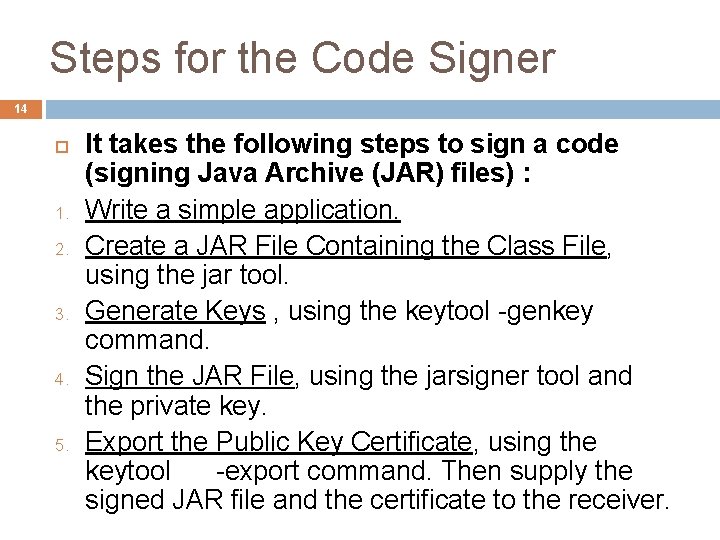
Steps for the Code Signer 14 1. 2. 3. 4. 5. It takes the following steps to sign a code (signing Java Archive (JAR) files) : Write a simple application. Create a JAR File Containing the Class File, using the jar tool. Generate Keys , using the keytool -genkey command. Sign the JAR File, using the jarsigner tool and the private key. Export the Public Key Certificate, using the keytool -export command. Then supply the signed JAR file and the certificate to the receiver.
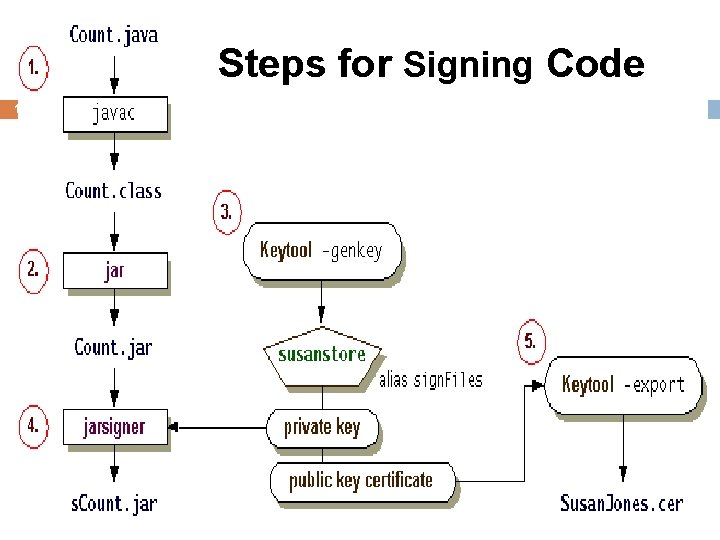
Steps for Signing Code 15
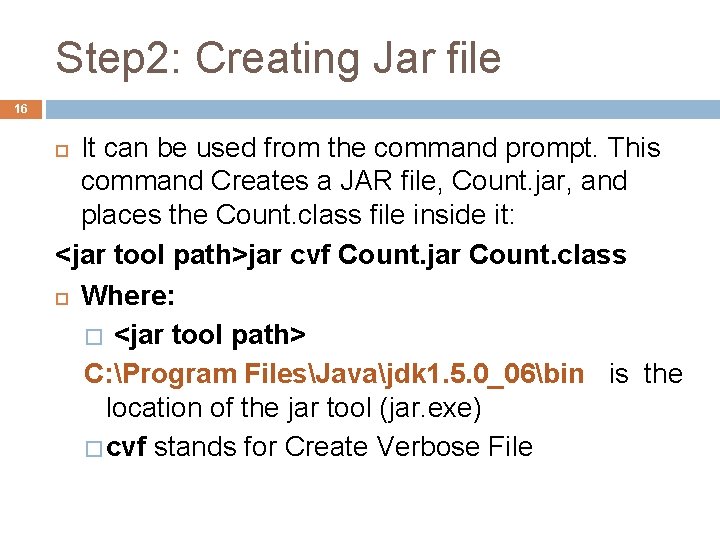
Step 2: Creating Jar file 16 It can be used from the command prompt. This command Creates a JAR file, Count. jar, and places the Count. class file inside it: <jar tool path>jar cvf Count. jar Count. class Where: � <jar tool path> C: Program FilesJavajdk 1. 5. 0_06bin is the location of the jar tool (jar. exe) � cvf stands for Create Verbose File
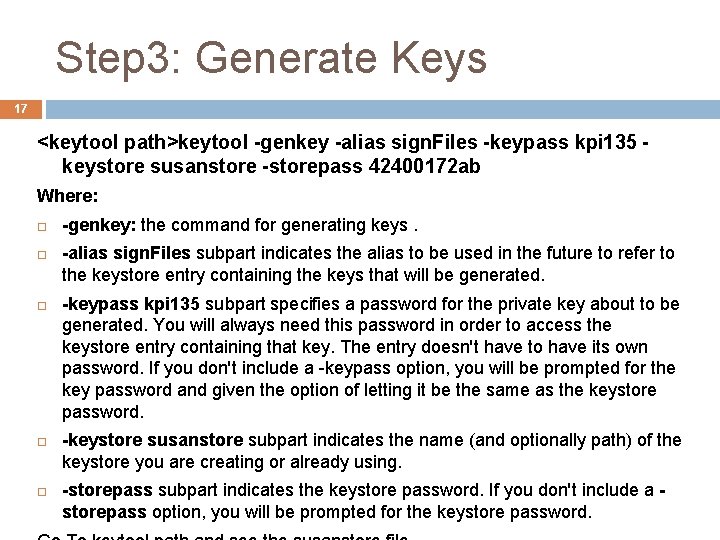
Step 3: Generate Keys 17 <keytool path>keytool -genkey -alias sign. Files -keypass kpi 135 keystore susanstore -storepass 42400172 ab Where: -genkey: the command for generating keys. -alias sign. Files subpart indicates the alias to be used in the future to refer to the keystore entry containing the keys that will be generated. -keypass kpi 135 subpart specifies a password for the private key about to be generated. You will always need this password in order to access the keystore entry containing that key. The entry doesn't have to have its own password. If you don't include a -keypass option, you will be prompted for the key password and given the option of letting it be the same as the keystore password. -keystore susanstore subpart indicates the name (and optionally path) of the keystore you are creating or already using. -storepass subpart indicates the keystore password. If you don't include a storepass option, you will be prompted for the keystore password.
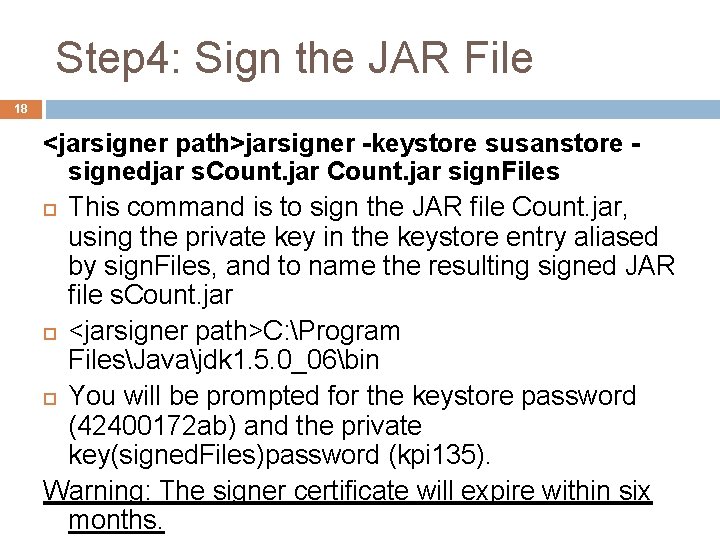
Step 4: Sign the JAR File 18 <jarsigner path>jarsigner -keystore susanstore signedjar s. Count. jar sign. Files This command is to sign the JAR file Count. jar, using the private key in the keystore entry aliased by sign. Files, and to name the resulting signed JAR file s. Count. jar <jarsigner path>C: Program FilesJavajdk 1. 5. 0_06bin You will be prompted for the keystore password (42400172 ab) and the private key(signed. Files)password (kpi 135). Warning: The signer certificate will expire within six months.
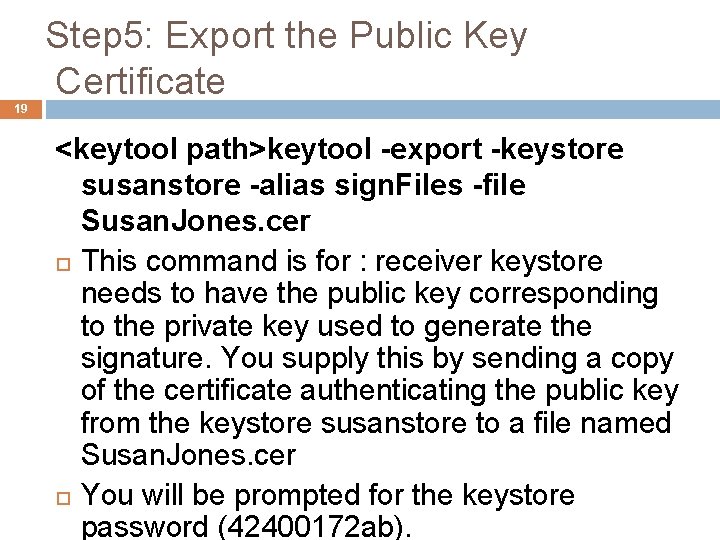
Step 5: Export the Public Key Certificate 19 <keytool path>keytool -export -keystore susanstore -alias sign. Files -file Susan. Jones. cer This command is for : receiver keystore needs to have the public key corresponding to the private key used to generate the signature. You supply this by sending a copy of the certificate authenticating the public key from the keystore susanstore to a file named Susan. Jones. cer You will be prompted for the keystore password (42400172 ab).
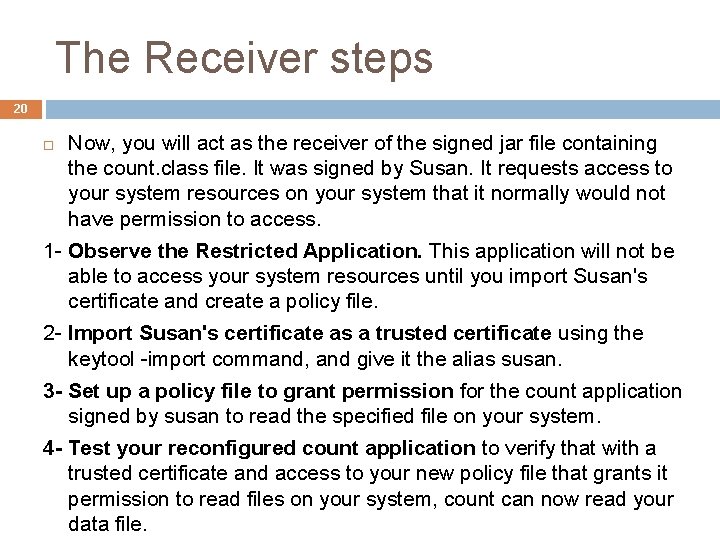
The Receiver steps 20 Now, you will act as the receiver of the signed jar file containing the count. class file. It was signed by Susan. It requests access to your system resources on your system that it normally would not have permission to access. 1 - Observe the Restricted Application. This application will not be able to access your system resources until you import Susan's certificate and create a policy file. 2 - Import Susan's certificate as a trusted certificate using the keytool -import command, and give it the alias susan. 3 - Set up a policy file to grant permission for the count application signed by susan to read the specified file on your system. 4 - Test your reconfigured count application to verify that with a trusted certificate and access to your new policy file that grants it permission to read files on your system, count can now read your data file.
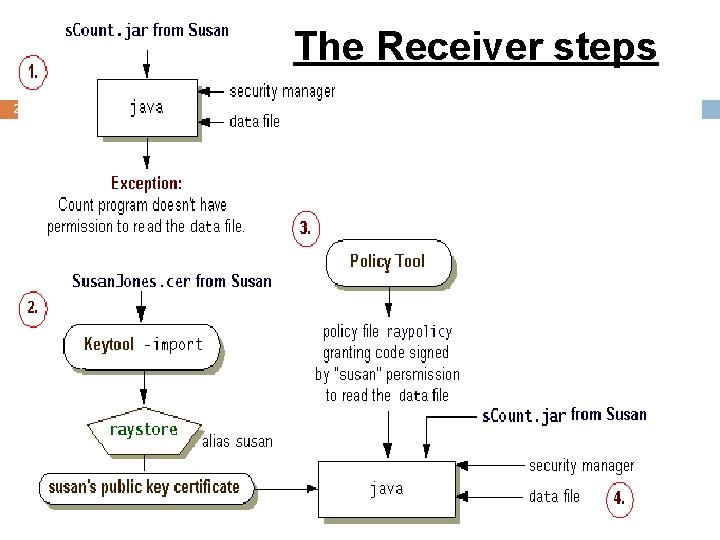
The Receiver steps 21
TO DO … 22 Implement code signer and receiver steps. Follow the steps explained in sun website http: //java. sun. com/docs/books/tutorial/secur ity/toolsign/index. html
- Slides: 22