LAB 2 CPIT 425 LAB MARKS Si No

LAB 2 CPIT 425
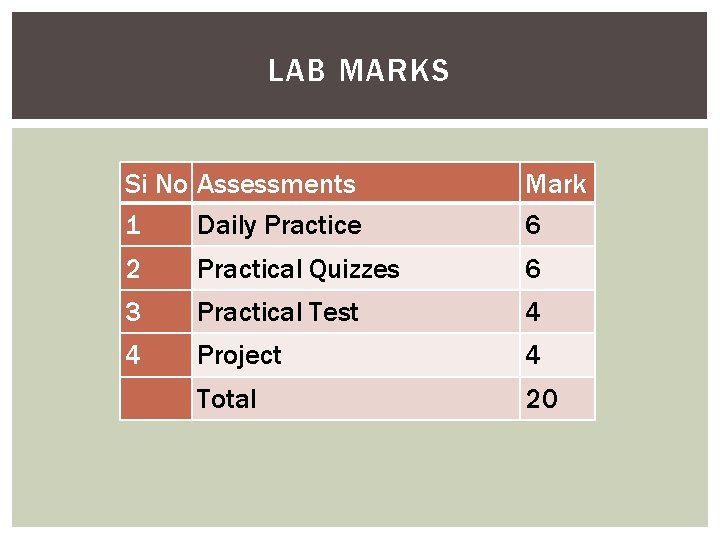
LAB MARKS Si No Assessments 1 Daily Practice Mark 6 2 Practical Quizzes 6 3 Practical Test 4 4 Project 4 Total 20
COURSEWORK Projects, assignments and etc… must be submitted on time and late submission would be subjected to reject the work or 25% minus mark for a given limited period of time extension like 3 days or one more week. Students must be capable of answering the questions asked by the instructor about the coursework going to be submitted. Each student must be able to explain his contribution in case the work has been done by a group. Grades may be different for each group members according to their participation and answering capability about the submitted coursework. Grades and feedback of course work will be informed the students within a week. All coursework must be submitted in a neat format with a cover page that contains name & ID of group members, topic and course number etc…, Students will not be entertained to include other names in any submitted coursework other than the names specified at the time of submission.
CHEATING / COPYING During practical tests/exams : - Copying fully or partially from any sources like books, photo copies, web sites and mobile phones will be declared as clear cheating and the involved students shall not be permitted to continue the session and their status in lab mark will be declared as DN. Projects/Assignments: - Copying or exchanging either soft or hard copy of any coursework between groups will result all members among the groups being declared as guilty. So such groups or members will not be allowed to resubmit the coursework and the status their lab mark will be declared as DN. Seek help from others or try to help others during practical tests or quizzes is also considered as cheating.
OBJECTIVE Know how Caesar algorithm works practically using an executable version of it in simple Excel sheet format. Students will try to guess the key using brute force approach by trying all possible keys until the correct key is matched. Learn how to adjust some parameters of Caesar algorithm, changing encryption equation and notice the affects on the cipher text. Multiplicative encryption is also presented to the students to increase their understanding of encryption and decryption techniques. 5. Some encryption ideas based on Caesar algorithm will be presented to the students such as multiple keys encryption (key vector).
OUTCOME students will increase their understanding of Caesar algorithm by testing the parameters practically using simple Excel sheet. Students will be able to guess an decryption key using brute force technique. Students will be able to encrypt plaintext using different methods such as multiple keys vector.
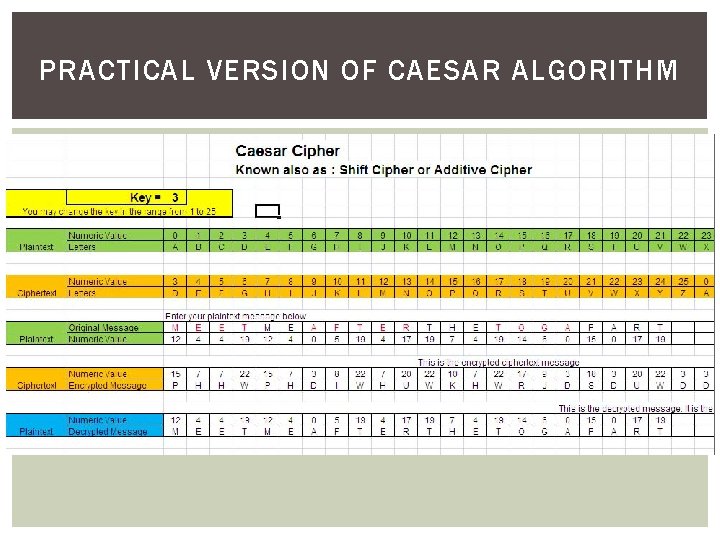
PRACTICAL VERSION OF CAESAR ALGORITHM
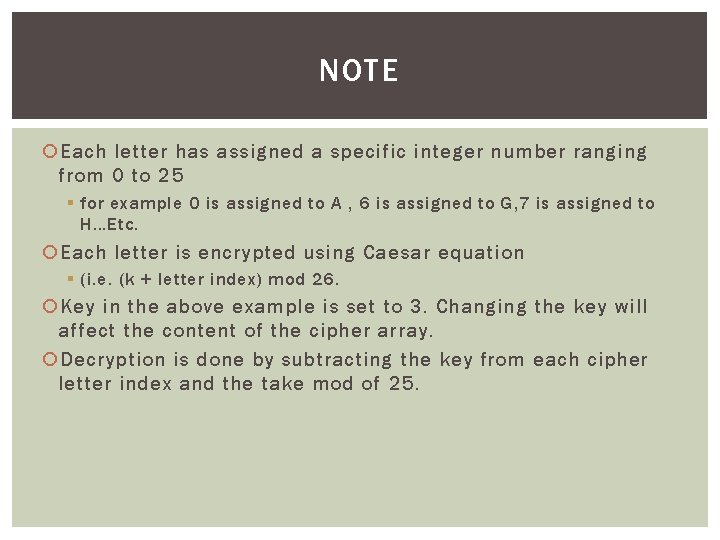
NOTE Each letter has assigned a specific integer number ranging from 0 to 25 § for example 0 is assigned to A , 6 is assigned to G, 7 is assigned to H…Etc. Each letter is encrypted using Caesar equation § (i. e. (k + letter index) mod 26. Key in the above example is set to 3. Changing the key will affect the content of the cipher array. Decryption is done by subtracting the key from each cipher letter index and the take mod of 25.
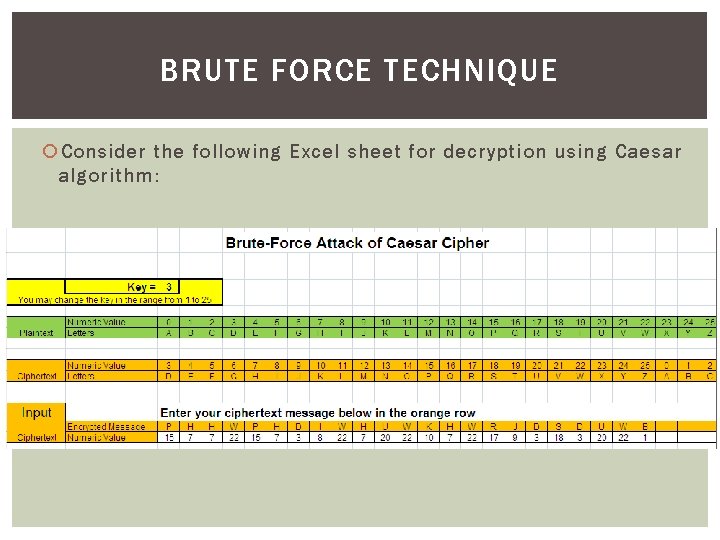
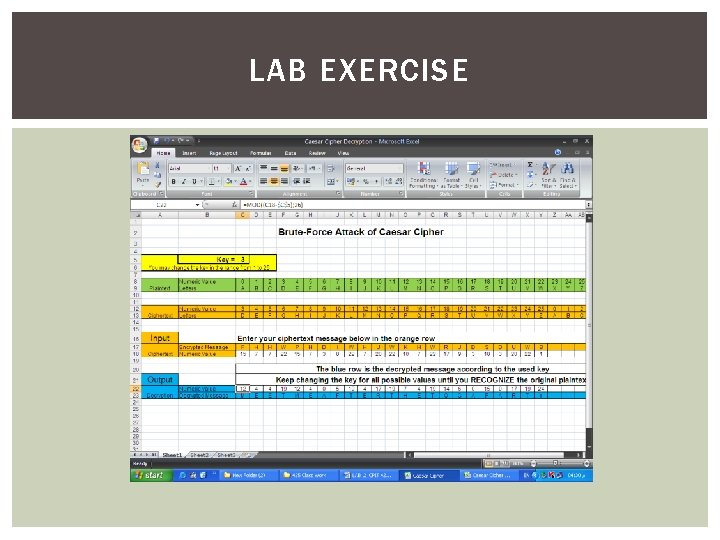
BRUTE FORCE TECHNIQUE Consider the following Excel sheet for decryption using Caesar algorithm:
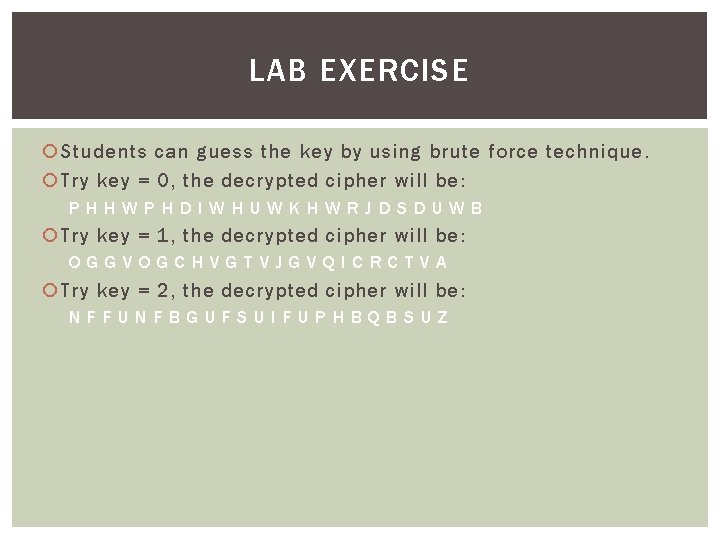
LAB EXERCISE Students can guess the key by using brute force technique. Try key = 0, the decrypted cipher will be: PHHWPHDIWHUWKHWRJDSDUWB Try key = 1, the decrypted cipher will be: OGGVOGCHVGTVJGVQICRCTVA Try key = 2, the decrypted cipher will be: NFFUNFBGUFSUIFUPHBQBSUZ
LAB EXERCISE Try key = 3, the decrypted cipher will be: MEETMEAFTERTHETOGAPARTY Matched!! So key =3
LAB EXERCISE
MULTIPLICATIVE ALGORITHM It is similar to additive encryption The difference we multiply by key instead of adding it. The relationship between a symbol in the plaintext to a symbol in the cipher text is one-to-one. Encryption equation: (key * letter index) mod 26.
QUIZ Each student should try to conclude the decryption equation for multiplicative algorithm. (key / letter index) mod 26.
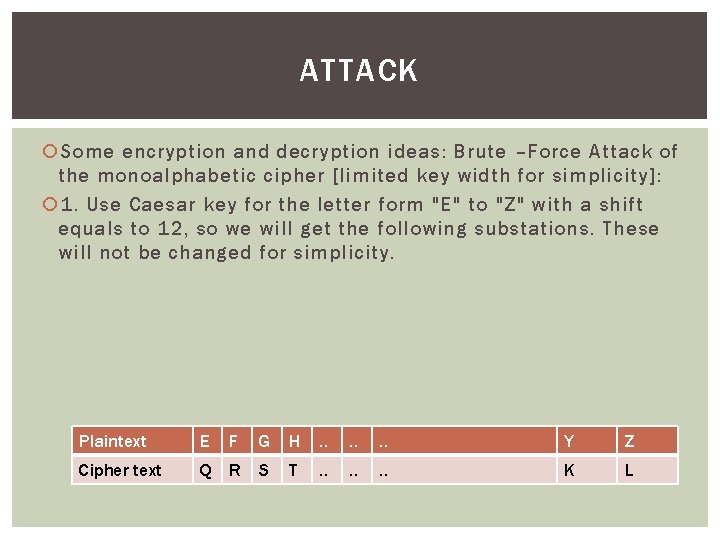
ATTACK Some encryption and decryption ideas: Brute –Force Attack of the monoalphabetic cipher [limited key width for simplicity]: 1. Use Caesar key for the letter form "E" to "Z" with a shift equals to 12, so we will get the following substations. These will not be changed for simplicity. Plaintext E F G H . . . Y Z Cipher text Q R S T . . . K L
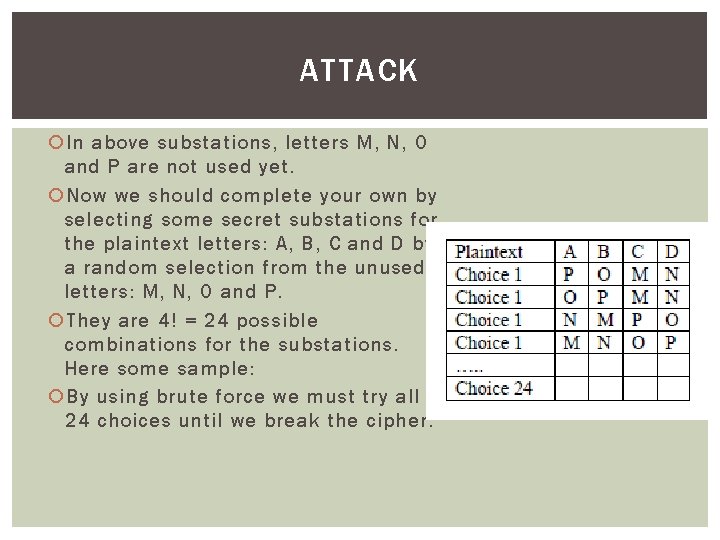
ATTACK In above substations, letters M, N, O and P are not used yet. Now we should complete your own by selecting some secret substations for the plaintext letters: A, B, C and D by a random selection from the unused letters: M, N, O and P. They are 4! = 24 possible combinations for the substations. Here some sample: By using brute force we must try all 24 choices until we break the cipher.
- Slides: 16