LAB 1 Information Security CPIT 425 Instructor Bashair

LAB 1 Information Security CPIT 425 Instructor: Bashair Alrashed
OUTLINES: Discussed the Basics of encryption and decryption techniques know there are many algorithms for encryption and decryption Students will be divided into groups of 3 girls Understand how additive (Caesar) encryption and decryption works should implement the algorithm using a suitable programming language.
OUTCOMES: know the importance of encryption and decryption techniques Learn how to encrypt a plaintext using (Caesar) algorithm.
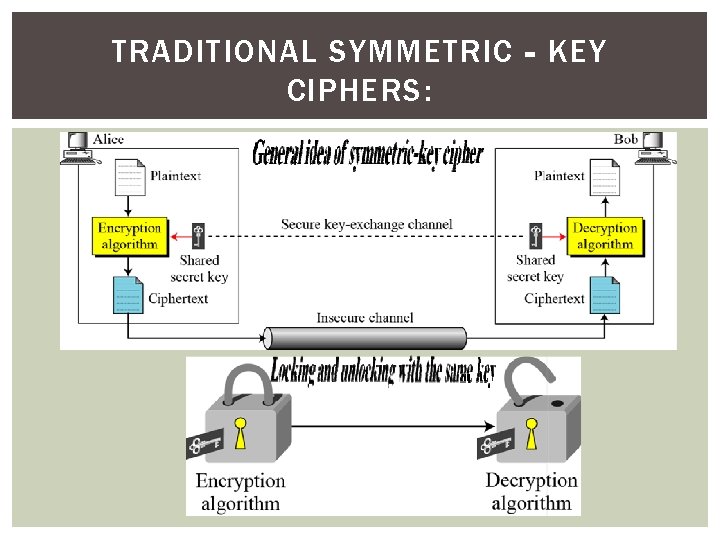
TRADITIONAL SYMMETRIC‐KEY CIPHERS:
TRADITIONAL SYMMETRIC‐KEY CIPHERS: Plaintext is read by the user, he wants to encrypt it in some manner. The hacker tries to decrypt the cipher text using different keys. The hacker only sees the cipher text, he didn’t know the key and way in which the plain text is encrypted. Encryption and decryption algorithms depend on the key itself.
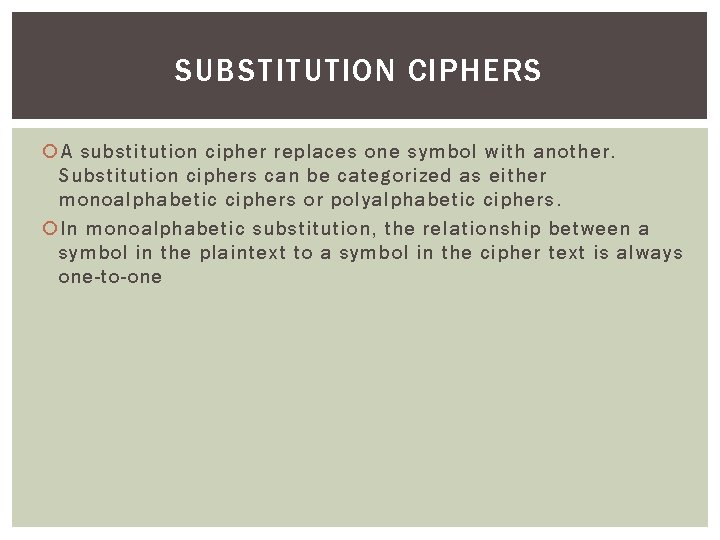
SUBSTITUTION CIPHERS A substitution cipher replaces one symbol with another. Substitution ciphers can be categorized as either monoalphabetic ciphers or polyalphabetic ciphers. In monoalphabetic substitution, the relationship between a symbol in the plaintext to a symbol in the cipher text is always one-to-one
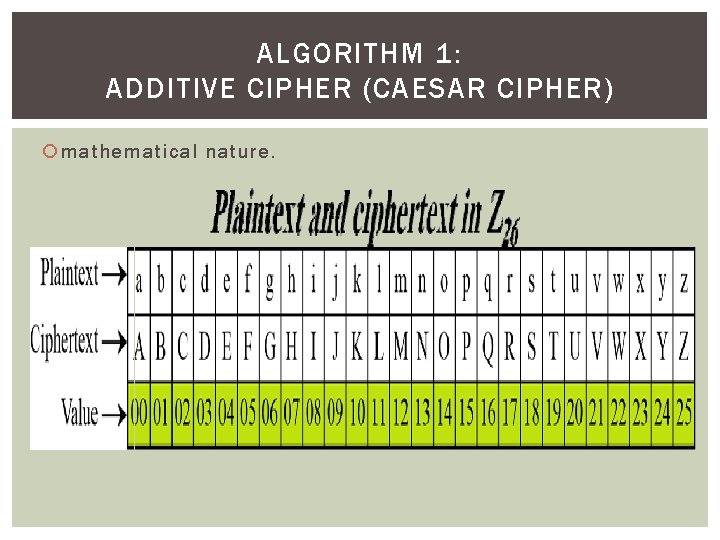
ALGORITHM 1: ADDITIVE CIPHER (CAESAR CIPHER) mathematical nature.
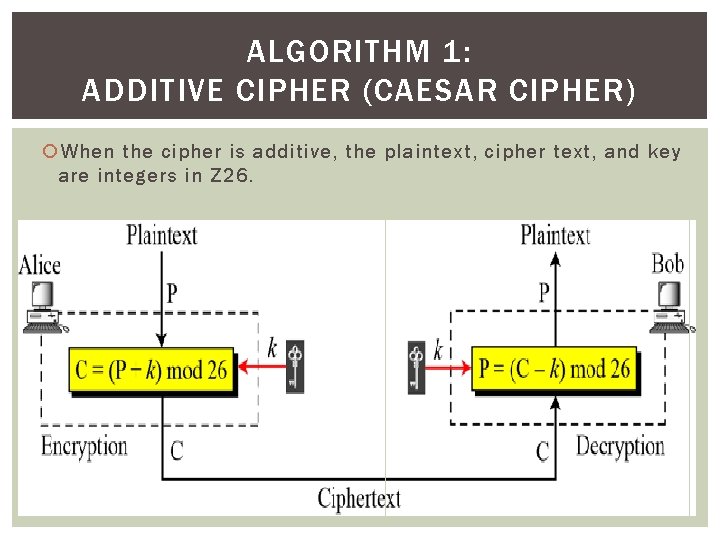
ALGORITHM 1: ADDITIVE CIPHER (CAESAR CIPHER) When the cipher is additive, the plaintext, cipher text, and key are integers in Z 26.
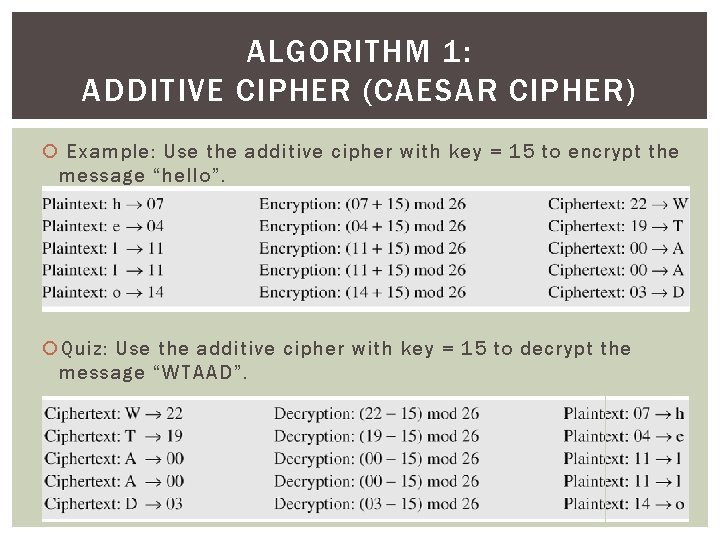
ALGORITHM 1: ADDITIVE CIPHER (CAESAR CIPHER) Example: Use the additive cipher with key = 15 to encrypt the message “hello”. Quiz: Use the additive cipher with key = 15 to decrypt the message “WTAAD”.
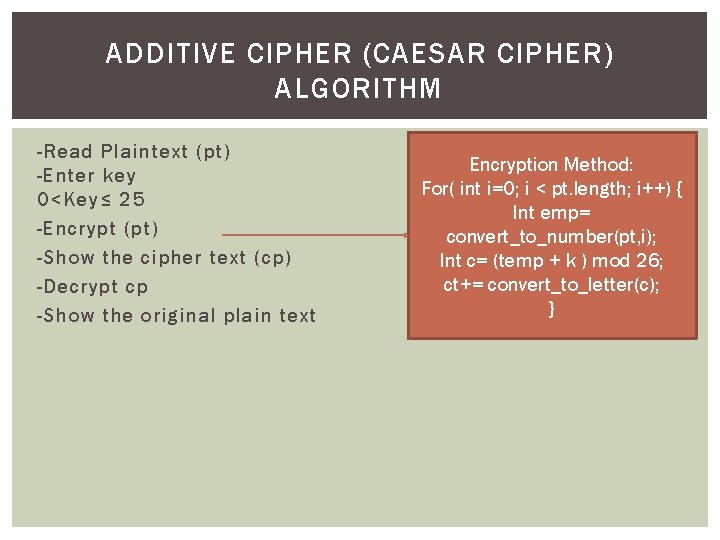
ADDITIVE CIPHER (CAESAR CIPHER) ALGORITHM -Read Plaintext (pt) -Enter key 0<Key≤ 25 -Encrypt (pt) -Show the cipher text (cp) -Decrypt cp -Show the original plain text Encryption Method: For( int i=0; i < pt. length; i++) { Int emp= convert_to_number(pt, i); Int c= (temp + k ) mod 26; ct+= convert_to_letter(c); }
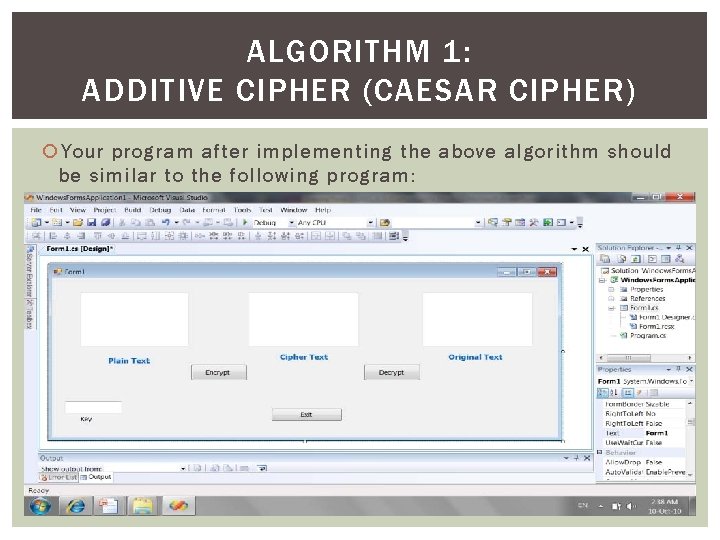
ALGORITHM 1: ADDITIVE CIPHER (CAESAR CIPHER) Your program after implementing the above algorithm should be similar to the following program:
HOME WORK 1 Implement (Caesar) algorithm using a suitable programming language. Note: The expected time to finish submitting next lab
- Slides: 12