CRYPTOGRAPHY Lecture 4 Secure transmission Steganography cryptography Transposition
- Slides: 22
CRYPTOGRAPHY Lecture 4
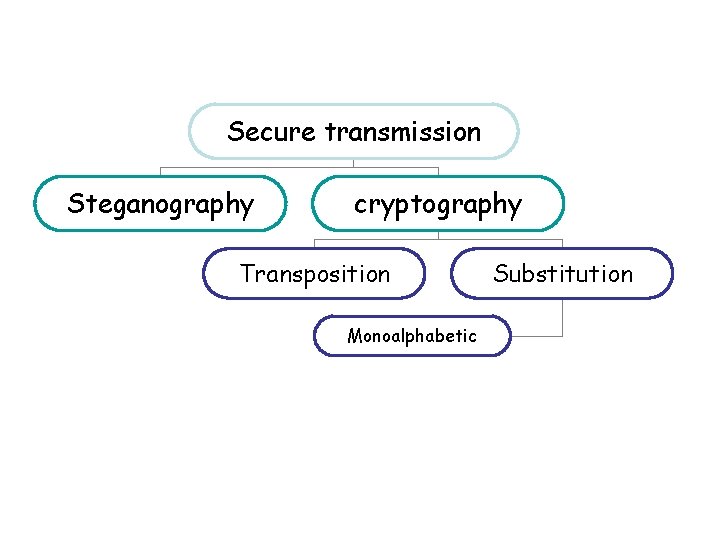
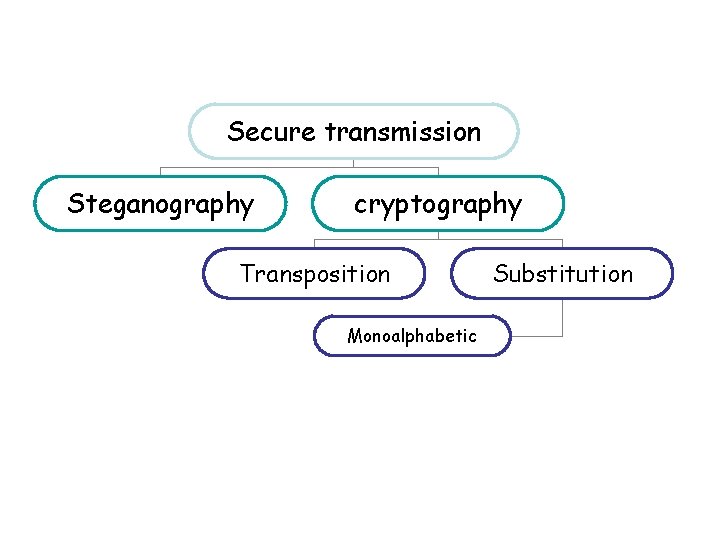
Secure transmission Steganography cryptography Transposition Monoalphabetic Substitution
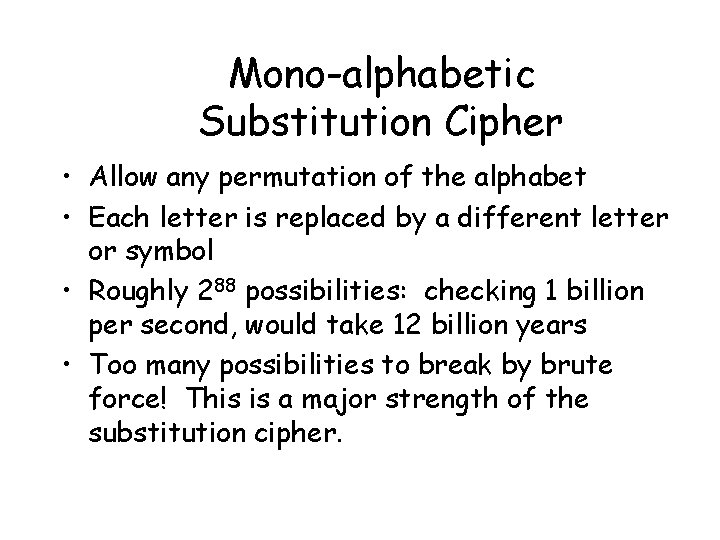
Mono-alphabetic Substitution Cipher • Allow any permutation of the alphabet • Each letter is replaced by a different letter or symbol • Roughly 288 possibilities: checking 1 billion per second, would take 12 billion years • Too many possibilities to break by brute force! This is a major strength of the substitution cipher.
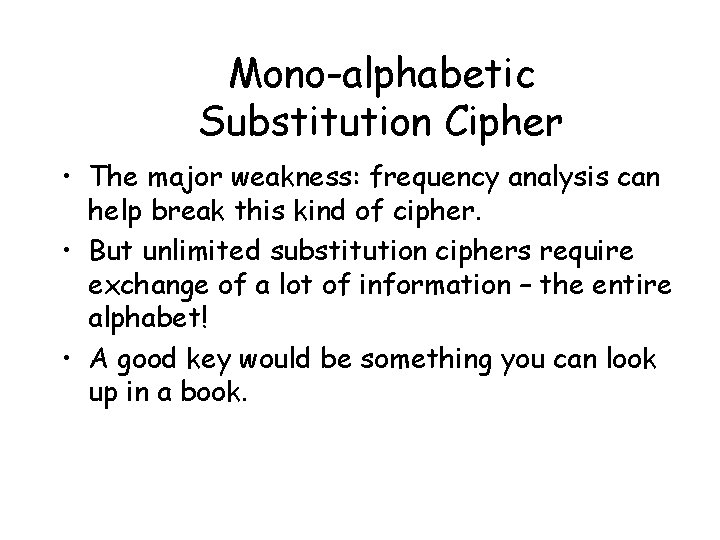
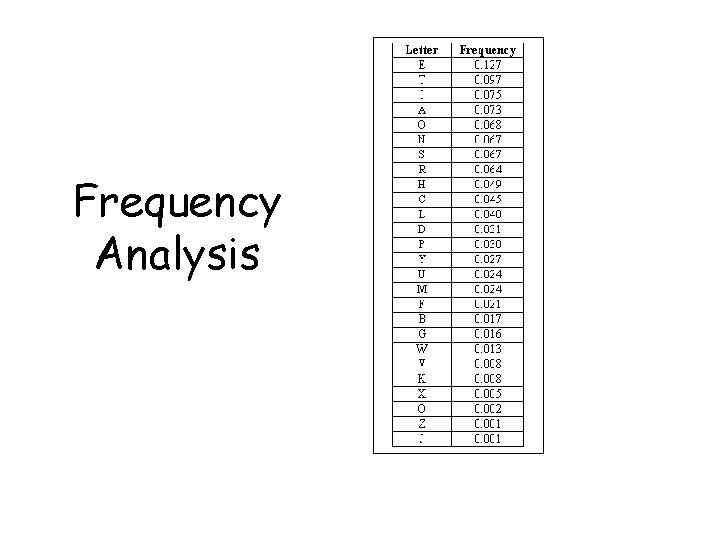
Mono-alphabetic Substitution Cipher • The major weakness: frequency analysis can help break this kind of cipher. • But unlimited substitution ciphers require exchange of a lot of information – the entire alphabet! • A good key would be something you can look up in a book.
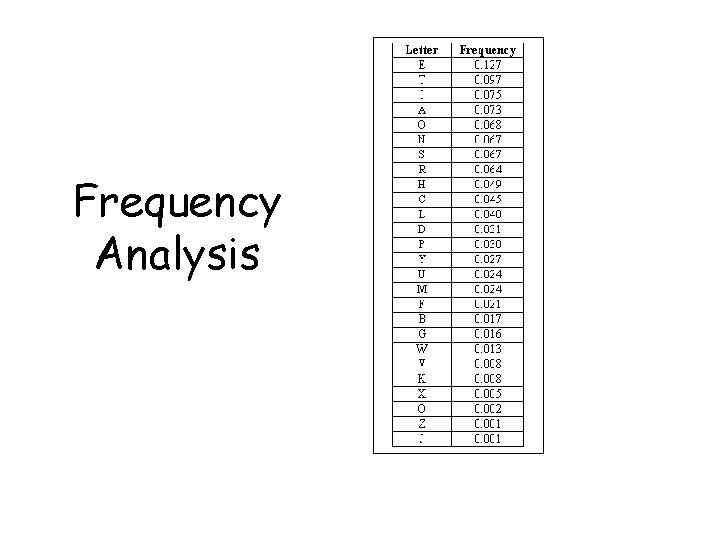
Frequency Analysis
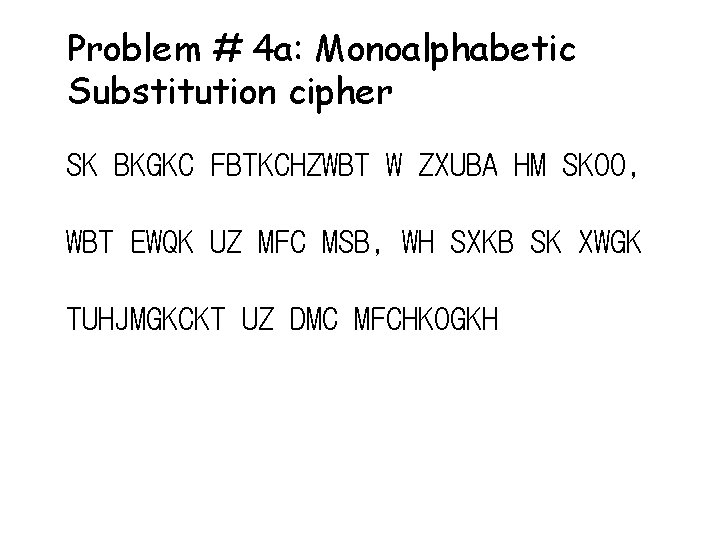
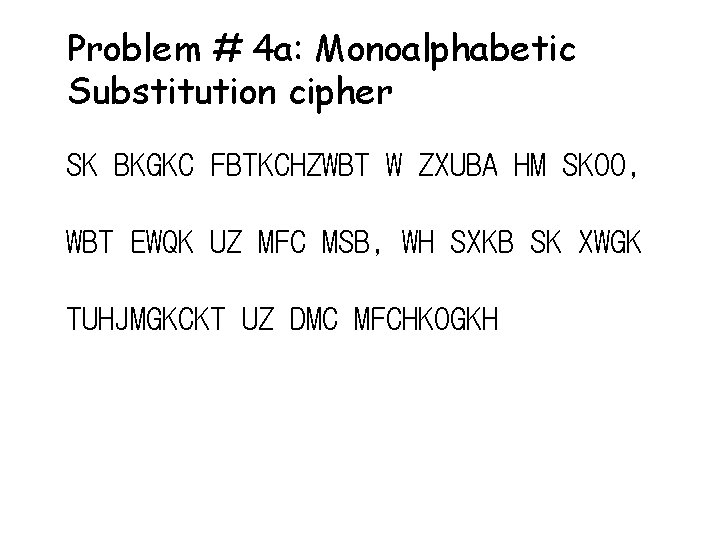
Problem # 4 a: Monoalphabetic Substitution cipher SK BKGKC FBTKCHZWBT W ZXUBA HM SKOO, WBT EWQK UZ MFC MSB, WH SXKB SK XWGK TUHJMGKCKT UZ DMC MFCHKOGKH
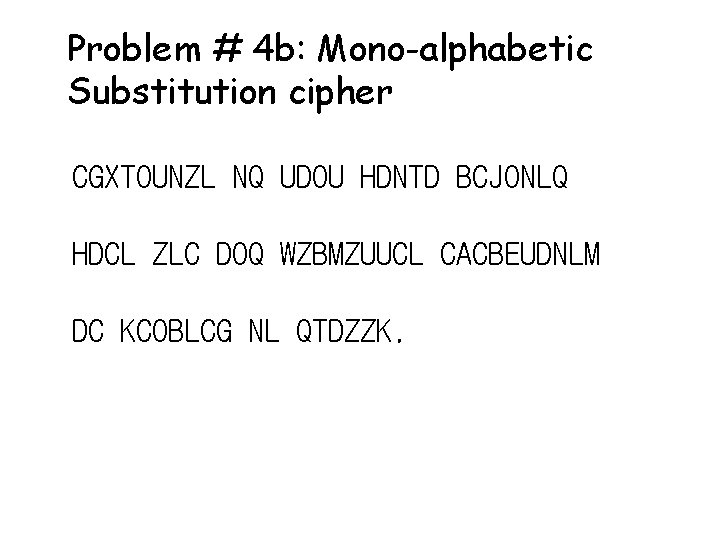
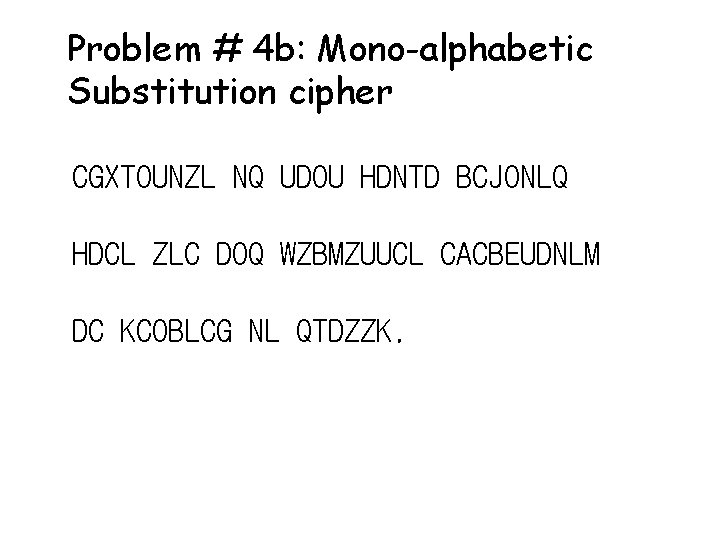
Problem # 4 b: Mono-alphabetic Substitution cipher CGXTOUNZL NQ UDOU HDNTD BCJONLQ HDCL ZLC DOQ WZBMZUUCL CACBEUDNLM DC KCOBLCG NL QTDZZK.
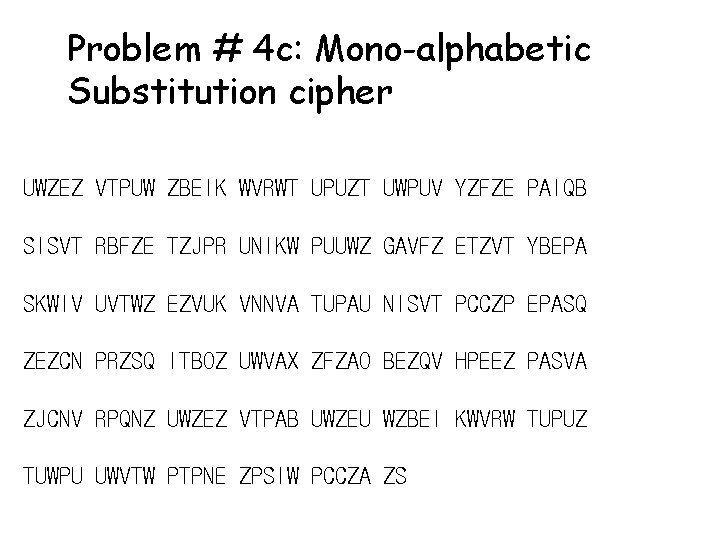
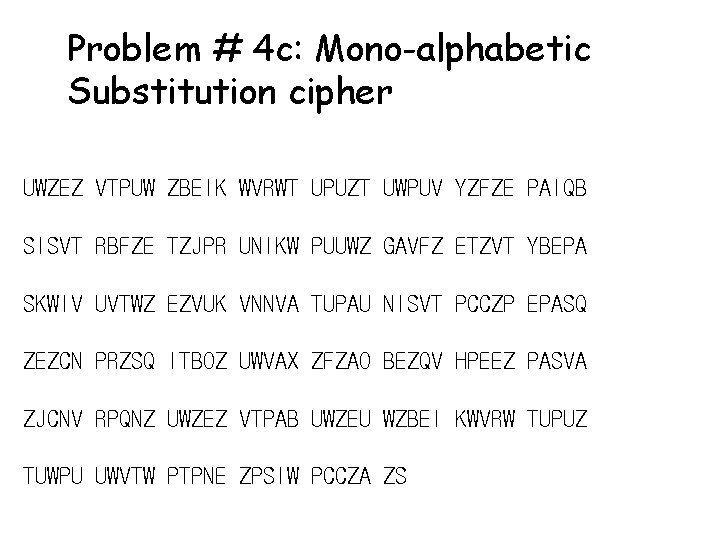
Problem # 4 c: Mono-alphabetic Substitution cipher UWZEZ VTPUW ZBEIK WVRWT UPUZT UWPUV YZFZE PAIQB SISVT RBFZE TZJPR UNIKW PUUWZ GAVFZ ETZVT YBEPA SKWIV UVTWZ EZVUK VNNVA TUPAU NISVT PCCZP EPASQ ZEZCN PRZSQ ITBOZ UWVAX ZFZAO BEZQV HPEEZ PASVA ZJCNV RPQNZ UWZEZ VTPAB UWZEU WZBEI KWVRW TUPUZ TUWPU UWVTW PTPNE ZPSIW PCCZA ZS
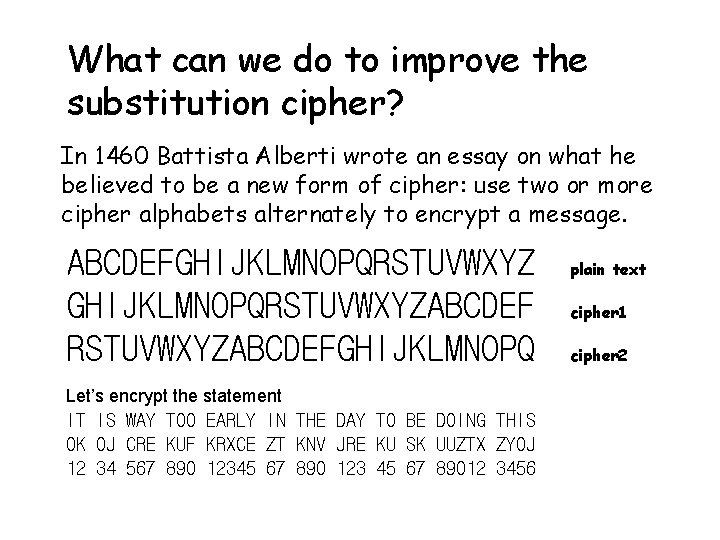
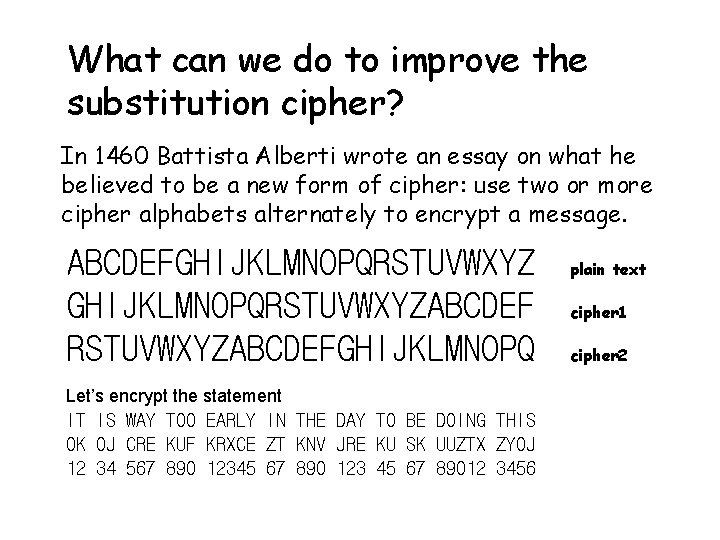
What can we do to improve the substitution cipher? In 1460 Battista Alberti wrote an essay on what he believed to be a new form of cipher: use two or more cipher alphabets alternately to encrypt a message. ABCDEFGHIJKLMNOPQRSTUVWXYZABCDEF RSTUVWXYZABCDEFGHIJKLMNOPQ Let’s encrypt the statement IT IS WAY TOO EARLY IN THE DAY TO BE DOING THIS OK OJ CRE KUF KRXCE ZT KNV JRE KU SK UUZTX ZYOJ 12 34 567 890 12345 67 890 123 45 67 89012 3456 plain text cipher 1 cipher 2
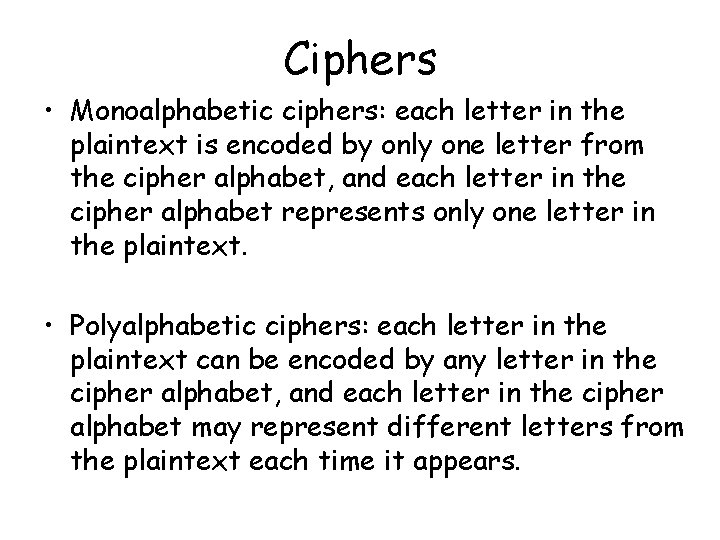
Ciphers • Monoalphabetic ciphers: each letter in the plaintext is encoded by only one letter from the cipher alphabet, and each letter in the cipher alphabet represents only one letter in the plaintext. • Polyalphabetic ciphers: each letter in the plaintext can be encoded by any letter in the cipher alphabet, and each letter in the cipher alphabet may represent different letters from the plaintext each time it appears.
What can we do to improve the substitution cipher? Alberti was followed by Johannes Trithemius (born 1462) and Giovanni Porta (born 1535) who developed his ideas. Finally, Vigenere put all these ideas together. Let’s take a whole table of Caesar shift alphabets. The first row will have a Caesar shift of 1, the second of 2, etc. Each letter in the plaintext message can be enciphered by a different row.
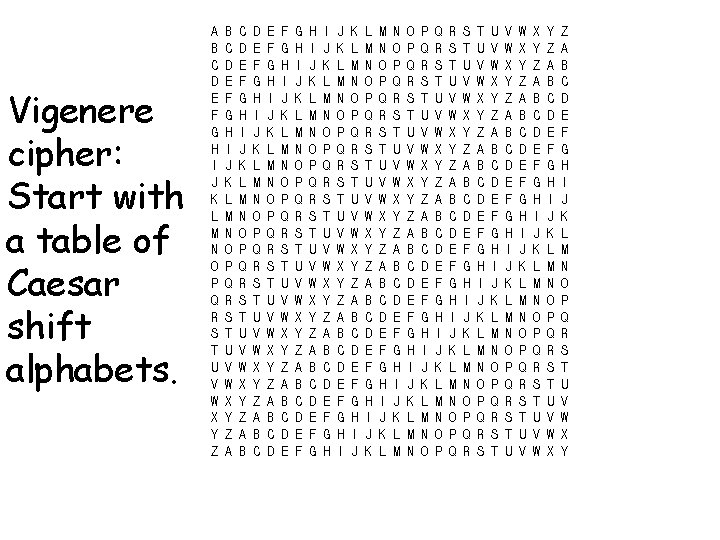
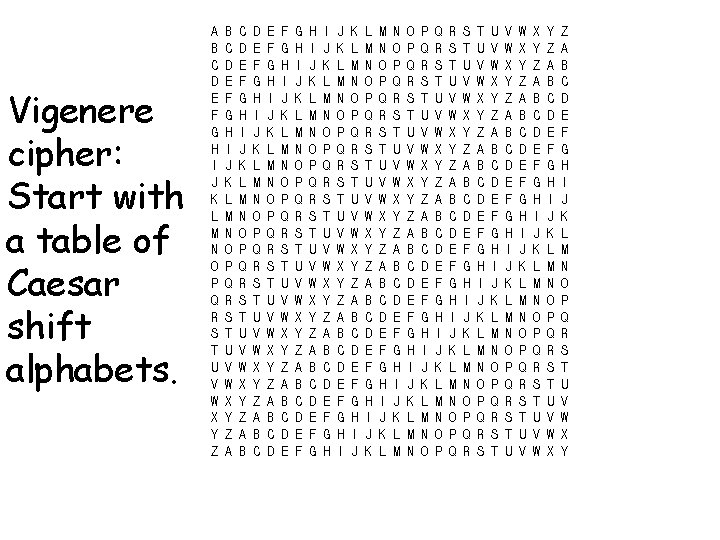
Vigenere cipher: Start with a table of Caesar shift alphabets. A B C D E F G H I J K L M N O P Q R S T U V W X Y Z A B C E F G H I J K L M N O P Q R S T U V W X Y Z A B C D E F G I J K L M N O P Q R S T U V W X Y Z A B C D E F G H I J K M N O P Q R S T U V W X Y Z A B C D E F G H I J K L M N O Q R S T U V W X Y Z A B C D E F G H I J K L M N O P Q R S U V W X Y Z A B C D E F G H I J K L M N O P Q R S T U V W Y Z A B C D E F G H I J K L M N O P Q R S T U V W X Y
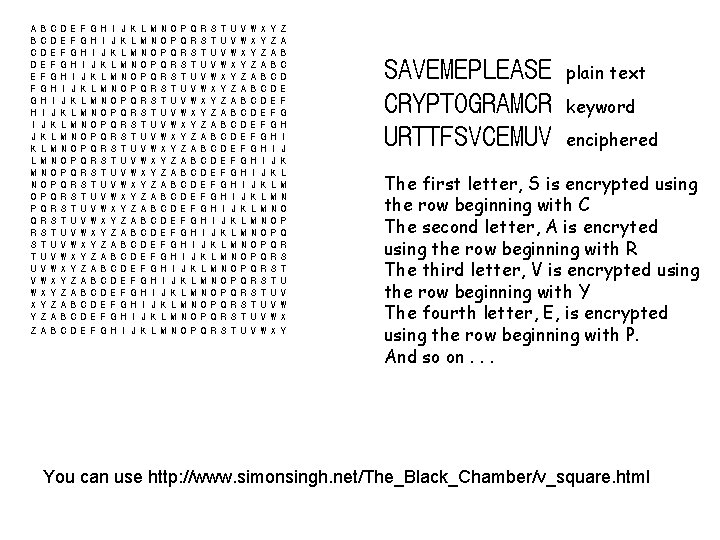
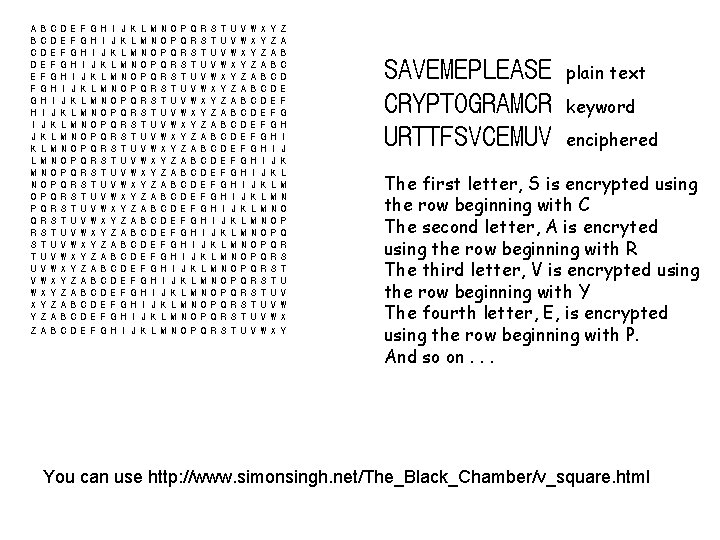
A B C D E F G H I J K L M N O P Q R S T U V W X Y Z A B C E F G H I J K L M N O P Q R S T U V W X Y Z A B C D E F G I J K L M N O P Q R S T U V W X Y Z A B C D E F G H I J K M N O P Q R S T U V W X Y Z A B C D E F G H I J K L M N O Q R S T U V W X Y Z A B C D E F G H I J K L M N O P Q R S U V W X Y Z A B C D E F G H I J K L M N O P Q R S T U V W Y Z A B C D E F G H I J K L M N O P Q R S T U V W X Y SAVEMEPLEASE CRYPTOGRAMCR URTTFSVCEMUV plain text keyword enciphered The first letter, S is encrypted using the row beginning with C The second letter, A is encryted using the row beginning with R The third letter, V is encrypted using the row beginning with Y The fourth letter, E, is encrypted using the row beginning with P. And so on. . . You can use http: //www. simonsingh. net/The_Black_Chamber/v_square. html
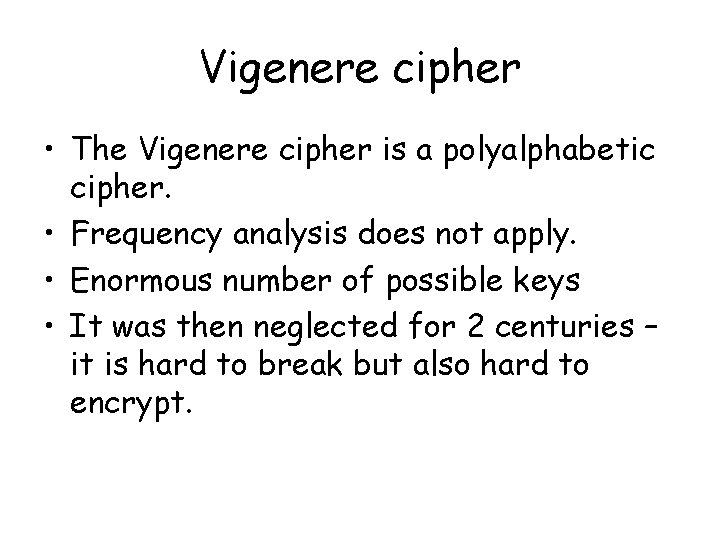
Vigenere cipher • The Vigenere cipher is a polyalphabetic cipher. • Frequency analysis does not apply. • Enormous number of possible keys • It was then neglected for 2 centuries – it is hard to break but also hard to encrypt.
Vigenere cipher: the unbreakable code • At first glance the Vigenère Cipher appears to be unbreakable, due to its use of up to 26 different cipher alphabets. Ciphers like this, which use more than one cipher alphabet are known as Polyalphabetic Ciphers. These can be incredibly difficult to decipher, because of their resistance to letter frequency analysis. Indeed, over time, the Vigenère cipher became known as 'Le Chiffre Undechiffrable', or 'The Unbreakable Cipher'. This slide and the next few copied directly from Simon Singh’s website.
Vigenere cipher: the unbreakable code • It wasn't until 1854, over two hundred years later, that the Vigenère Cipher was finally cracked by the British cryptographer Charles Babbage employed a mix of cryptographic genius, intuition and sheer cunning to break the Vigenère Cipher. Amazingly, his work was never published in his lifetime, and it was over a hundred years later, in the 1970's, that his technique was finally made public. This slide and the next few copied directly from Simon Singh’s website.
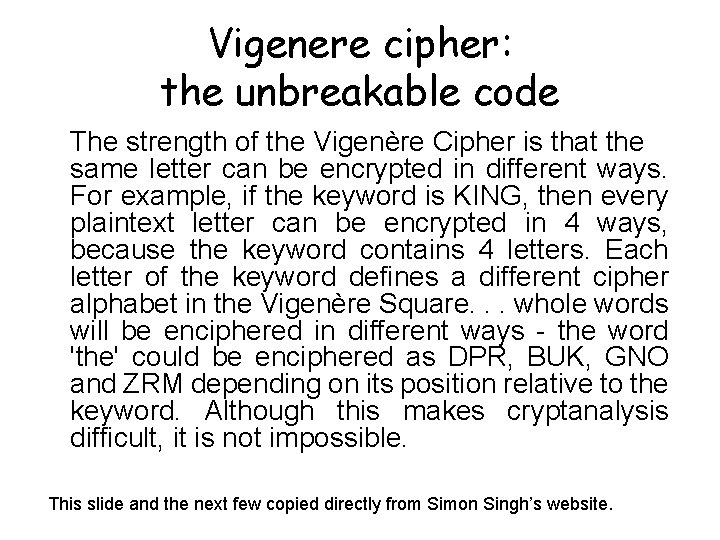
Vigenere cipher: the unbreakable code The strength of the Vigenère Cipher is that the same letter can be encrypted in different ways. For example, if the keyword is KING, then every plaintext letter can be encrypted in 4 ways, because the keyword contains 4 letters. Each letter of the keyword defines a different cipher alphabet in the Vigenère Square. . . whole words will be enciphered in different ways - the word 'the' could be enciphered as DPR, BUK, GNO and ZRM depending on its position relative to the keyword. Although this makes cryptanalysis difficult, it is not impossible. This slide and the next few copied directly from Simon Singh’s website.
Next time. . . How Babbage cracked the undecipherable cipher.
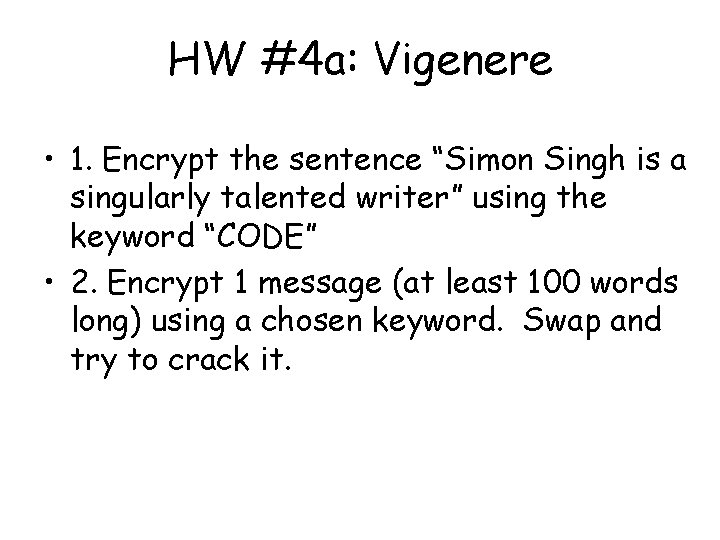
HW #4 a: Vigenere • 1. Encrypt the sentence “Simon Singh is a singularly talented writer” using the keyword “CODE” • 2. Encrypt 1 message (at least 100 words long) using a chosen keyword. Swap and try to crack it.
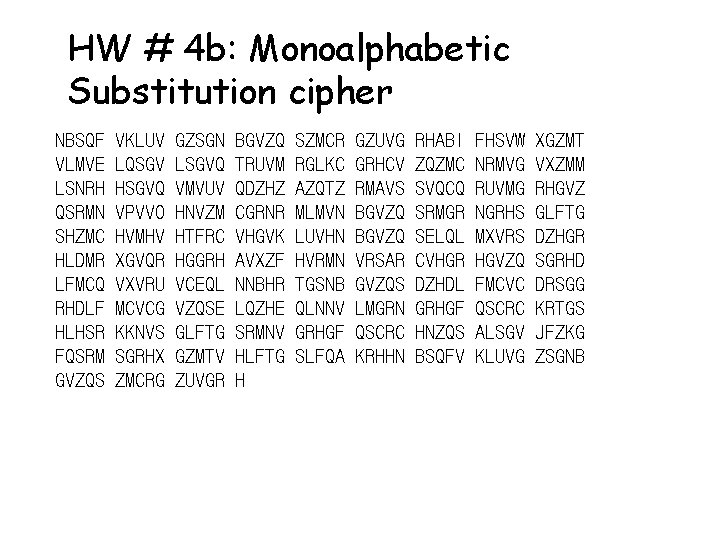
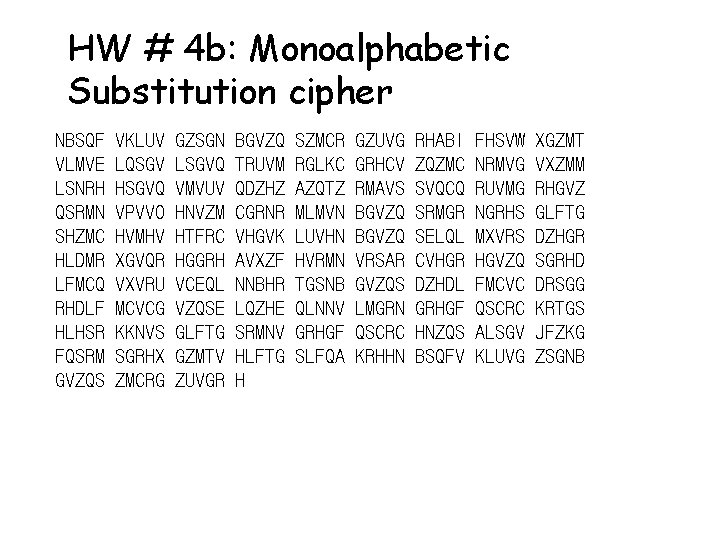
HW # 4 b: Monoalphabetic Substitution cipher NBSQF VLMVE LSNRH QSRMN SHZMC HLDMR LFMCQ RHDLF HLHSR FQSRM GVZQS VKLUV LQSGV HSGVQ VPVVO HVMHV XGVQR VXVRU MCVCG KKNVS SGRHX ZMCRG GZSGN LSGVQ VMVUV HNVZM HTFRC HGGRH VCEQL VZQSE GLFTG GZMTV ZUVGR BGVZQ TRUVM QDZHZ CGRNR VHGVK AVXZF NNBHR LQZHE SRMNV HLFTG H SZMCR RGLKC AZQTZ MLMVN LUVHN HVRMN TGSNB QLNNV GRHGF SLFQA GZUVG GRHCV RMAVS BGVZQ VRSAR GVZQS LMGRN QSCRC KRHHN RHABI ZQZMC SVQCQ SRMGR SELQL CVHGR DZHDL GRHGF HNZQS BSQFV FHSVW NRMVG RUVMG NGRHS MXVRS HGVZQ FMCVC QSCRC ALSGV KLUVG XGZMT VXZMM RHGVZ GLFTG DZHGR SGRHD DRSGG KRTGS JFZKG ZSGNB
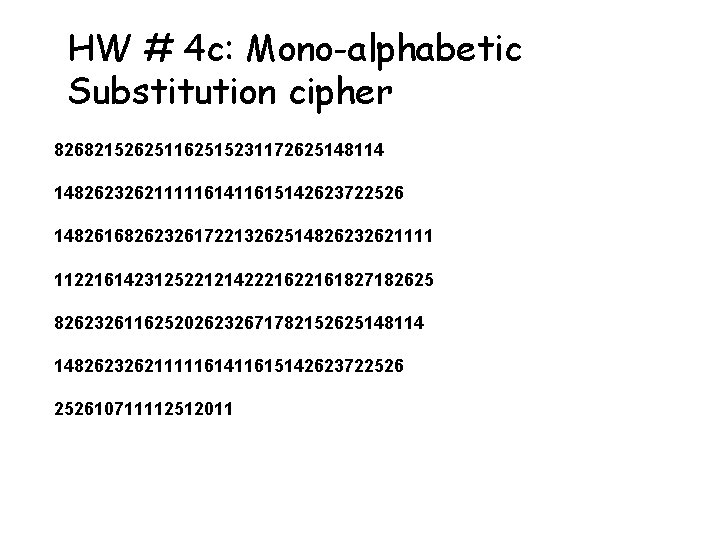
HW # 4 c: Mono-alphabetic Substitution cipher 826821526251162515231172625148114 14826232621111161411615142623722526 14826168262326172213262514826232621111 1122161423125221214222161827182625 8262326116252026232671782152625148114 14826232621111161411615142623722526 252610711112512011
Websites which help http: //www. geocities. com/cryptogramcorner/ http: //cs. colgate. edu/faculty/nevison/Core 139 Web/tools/substitution. html