Embedded Image Steganography lukas bijaminasmymail barry edu Abstract
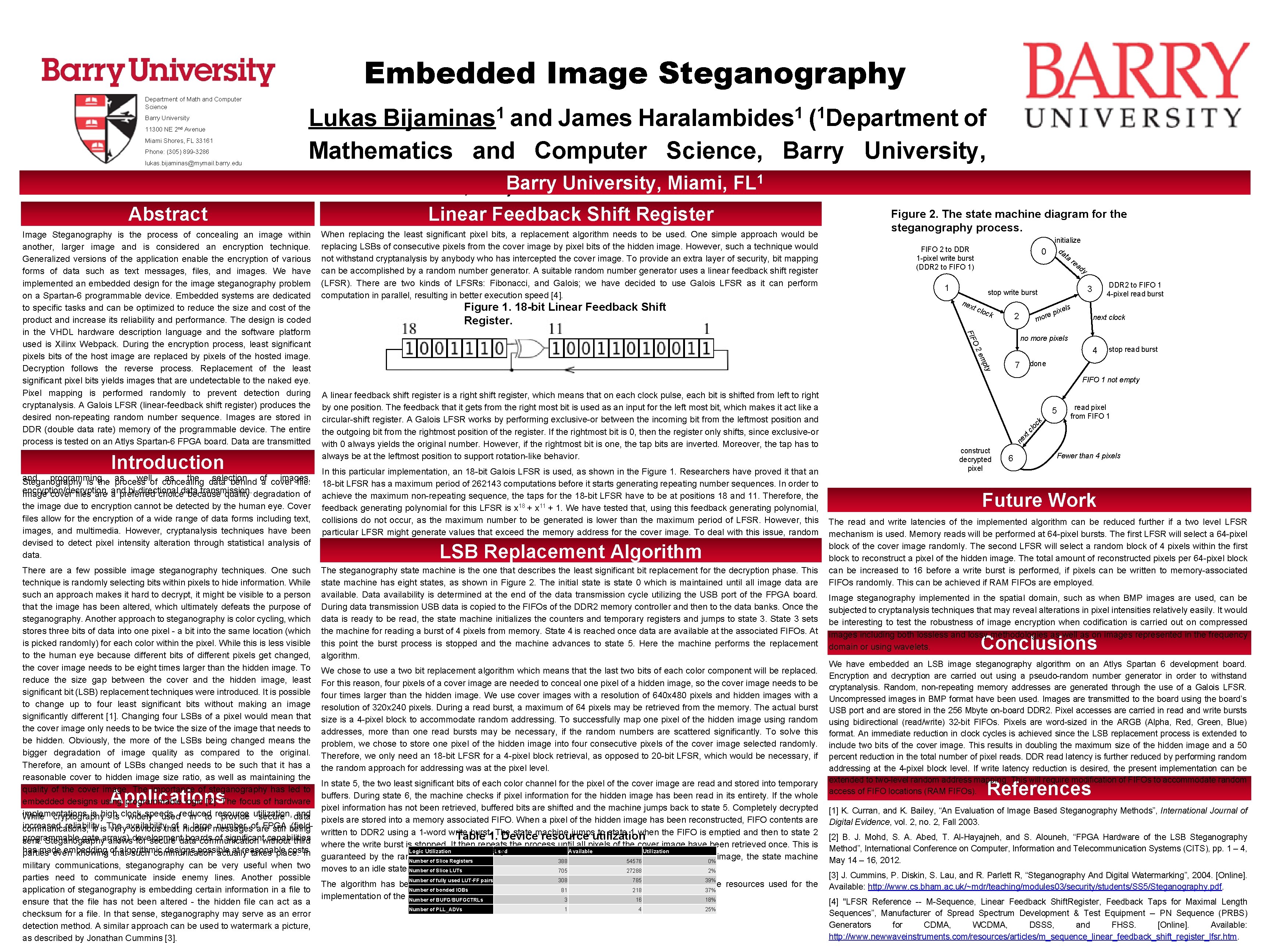
Embedded Image Steganography lukas. bijaminas@mymail. barry. edu Abstract Linear Feedback Shift Register Image Steganography is the process of concealing an image within another, larger image and is considered an encryption technique. Generalized versions of the application enable the encryption of various forms of data such as text messages, files, and images. We have implemented an embedded design for the image steganography problem on a Spartan-6 programmable device. Embedded systems are dedicated to specific tasks and can be optimized to reduce the size and cost of the product and increase its reliability and performance. The design is coded in the VHDL hardware description language and the software platform used is Xilinx Webpack. During the encryption process, least significant pixels bits of the host image are replaced by pixels of the hosted image. Decryption follows the reverse process. Replacement of the least significant pixel bits yields images that are undetectable to the naked eye. Pixel mapping is performed randomly to prevent detection during cryptanalysis. A Galois LFSR (linear-feedback shift register) produces the desired non-repeating random number sequence. Images are stored in DDR (double data rate) memory of the programmable device. The entire process is tested on an Atlys Spartan-6 FPGA board. Data are transmitted from/to the FPGA using a simplified USB protocol at an approximate rate of 48 Mbps. A graphical user interface allows for FPGA board initialization and programming as well as the data selection images, Steganography is the process of concealing behind of a cover file. encryption/decryption, and bi-directional data transmission. Image cover files are a preferred choice because quality degradation of When replacing the least significant pixel bits, a replacement algorithm needs to be used. One simple approach would be replacing LSBs of consecutive pixels from the cover image by pixel bits of the hidden image. However, such a technique would not withstand cryptanalysis by anybody who has intercepted the cover image. To provide an extra layer of security, bit mapping can be accomplished by a random number generator. A suitable random number generator uses a linear feedback shift register (LFSR). There are two kinds of LFSRs: Fibonacci, and Galois; we have decided to use Galois LFSR as it can perform computation in parallel, resulting in better execution speed [4]. 0 1 initialize da ta re ad y nex t clo ck e mor 2 DDR 2 to FIFO 1 4 -pixel read burst 3 stop write burst s ixel p next clock no more pixels O 2 4 em stop read burst done 7 pty the image due to encryption cannot be detected by the human eye. Cover files allow for the encryption of a wide range of data forms including text, images, and multimedia. However, cryptanalysis techniques have been devised to detect pixel intensity alteration through statistical analysis of data. FIFO 2 to DDR 1 -pixel write burst (DDR 2 to FIFO 1) FIF Introduction Figure 1. 18 -bit Linear Feedback Shift Register. Figure 2. The state machine diagram for the steganography process. H 2 O Phone: (305) 899 -3286 Lukas and James of Mathematics and Computer Science, Barry University, 1 Miami Shores, FL)Barry University, Miami, FL FIFO 1 not empty A linear feedback shift register is a right shift register, which means that on each clock pulse, each bit is shifted from left to right by one position. The feedback that it gets from the right most bit is used as an input for the left most bit, which makes it act like a circular-shift register. A Galois LFSR works by performing exclusive-or between the incoming bit from the leftmost position and the outgoing bit from the rightmost position of the register. If the rightmost bit is 0, then the register only shifts, since exclusive-or with 0 always yields the original number. However, if the rightmost bit is one, the tap bits are inverted. Moreover, the tap has to always be at the leftmost position to support rotation-like behavior. In this particular implementation, an 18 -bit Galois LFSR is used, as shown in the Figure 1. Researchers have proved it that an 18 -bit LFSR has a maximum period of 262143 computations before it starts generating repeating number sequences. In order to achieve the maximum non-repeating sequence, the taps for the 18 -bit LFSR have to be at positions 18 and 11. Therefore, the feedback generating polynomial for this LFSR is x 18 + x 11 + 1. We have tested that, using this feedback generating polynomial, collisions do not occur, as the maximum number to be generated is lower than the maximum period of LFSR. However, this particular LFSR might generate values that exceed the memory address for the cover image. To deal with this issue, random numbers are buffered during preprocessing, thus eliminating any latency due to address verification. A buffer size of 16 addresses prevents the introduction of delays in the steganography state machine. 5 read pixel from FIFO 1 ck Miami Shores, FL 33161 1 1 Haralambides ( Department clo 11300 NE 2 nd Avenue 1 Bijaminas xt Barry University ne Department of Math and Computer Science construct decrypted pixel 6 Fewer than 4 pixels Future Work The read and write latencies of the implemented algorithm can be reduced further if a two level LFSR mechanism is used. Memory reads will be performed at 64 -pixel bursts. The first LFSR will select a 64 -pixel block of the cover image randomly. The second LFSR will select a random block of 4 pixels within the first block to reconstruct a pixel of the hidden image. The total amount of reconstructed pixels per 64 -pixel block There a few possible image steganography techniques. One such The steganography state machine is the one that describes the least significant bit replacement for the decryption phase. This can be increased to 16 before a write burst is performed, if pixels can be written to memory-associated technique is randomly selecting bits within pixels to hide information. While state machine has eight states, as shown in Figure 2. The initial state is state 0 which is maintained until all image data are FIFOs randomly. This can be achieved if RAM FIFOs are employed. such an approach makes it hard to decrypt, it might be visible to a person available. Data availability is determined at the end of the data transmission cycle utilizing the USB port of the FPGA board. Image steganography implemented in the spatial domain, such as when BMP images are used, can be that the image has been altered, which ultimately defeats the purpose of During data transmission USB data is copied to the FIFOs of the DDR 2 memory controller and then to the data banks. Once the subjected to cryptanalysis techniques that may reveal alterations in pixel intensities relatively easily. It would steganography. Another approach to steganography is color cycling, which data is ready to be read, the state machine initializes the counters and temporary registers and jumps to state 3. State 3 sets be interesting to test the robustness of image encryption when codification is carried out on compressed stores three bits of data into one pixel - a bit into the same location (which the machine for reading a burst of 4 pixels from memory. State 4 is reached once data are available at the associated FIFOs. At images including both lossless and lossy methodologies as well as on images represented in the frequency is picked randomly) for each color within the pixel. While this is less visible this point the burst process is stopped and the machine advances to state 5. Here the machine performs the replacement domain or using wavelets. to the human eye because different bits of different pixels get changed, algorithm. the cover image needs to be eight times larger than the hidden image. To We chose to use a two bit replacement algorithm which means that the last two bits of each color component will be replaced. We have embedded an LSB image steganography algorithm on an Atlys Spartan 6 development board. reduce the size gap between the cover and the hidden image, least For this reason, four pixels of a cover image are needed to conceal one pixel of a hidden image, so the cover image needs to be Encryption and decryption are carried out using a pseudo-random number generator in order to withstand cryptanalysis. Random, non-repeating memory addresses are generated through the use of a Galois LFSR. significant bit (LSB) replacement techniques were introduced. It is possible four times larger than the hidden image. We use cover images with a resolution of 640 x 480 pixels and hidden images with a Uncompressed images in BMP format have been used. Images are transmitted to the board using the board’s to change up to four least significant bits without making an image resolution of 320 x 240 pixels. During a read burst, a maximum of 64 pixels may be retrieved from the memory. The actual burst USB port and are stored in the 256 Mbyte on-board DDR 2. Pixel accesses are carried in read and write bursts significantly different [1]. Changing four LSBs of a pixel would mean that size is a 4 -pixel block to accommodate random addressing. To successfully map one pixel of the hidden image using random using bidirectional (read/write) 32 -bit FIFOs. Pixels are word-sized in the ARGB (Alpha, Red, Green, Blue) the cover image only needs to be twice the size of the image that needs to addresses, more than one read bursts may be necessary, if the random numbers are scattered significantly. To solve this format. An immediate reduction in clock cycles is achieved since the LSB replacement process is extended to be hidden. Obviously, the more of the LSBs being changed means the problem, we chose to store one pixel of the hidden image into four consecutive pixels of the cover image selected randomly. include two bits of the cover image. This results in doubling the maximum size of the hidden image and a 50 bigger degradation of image quality as compared to the original. Therefore, we only need an 18 -bit LFSR for a 4 -pixel block retrieval, as opposed to 20 -bit LFSR, which would be necessary, if percent reduction in the total number of pixel reads. DDR read latency is further reduced by performing random Therefore, an amount of LSBs changed needs to be such that it has a the random approach for addressing was at the pixel level. addressing at the 4 -pixel block level. If write latency reduction is desired, the present implementation can be reasonable cover to hidden image size ratio, as well as maintaining the In state 5, the two least significant bits of each color channel for the pixel of the cover image are read and stored into temporary extended to two-level random address mapping. This will require modification of FIFOs to accommodate random quality of the cover image. The importance of steganography has led to buffers. During state 6, the machine checks if pixel information for the hidden image has been read in its entirety. If the whole access of FIFO locations (RAM FIFOs). embedded designs using programmable logic [2]. The focus of hardware pixel information has not been retrieved, buffered bits are shifted and the machine jumps back to state 5. Completely decrypted [1] K. Curran, and K. Bailey, “An Evaluation of Image Based Steganography Methods”, International Journal of implementations is high speeds, and While cryptography is clock widely used reduced in to resource provide utilization, secure data pixels are stored into a memory associated FIFO. When a pixel of the hidden image has been reconstructed, FIFO contents are Digital Evidence, vol. 2, no. 2, Fall 2003. increased reliability. of hidden a large messages number of are FPGA (fieldcommunications, it is The very availability obvious that still being written to DDR 2 using a 1 -word write burst. The state machine jumps to state 1 when the FIFO is emptied and then to state 2 Table 1. Device resource utilization [2] B. J. Mohd, S. Abed, T. Al-Hayajneh, and S. Alouneh, “FPGA Hardware of the LSB Steganography programmable gate arrays) development boards of significant capabilities sent. Steganography allows for secure data communication without third where the write burst is stopped. It then repeats the process until all pixels of the cover image have been retrieved once. This is Method”, International Conference on Computer, Information and Telecommunication Systems (CITS), pp. 1 – 4, has made embedding of algorithmic designs possible at reasonable costs. Logic Utilization summary. Used Available Utilization parties even knowing that such communication actually takes place. In guaranteed by the random number generator used. Upon reconstruction of all pixels of the hidden image, the state machine Number of Slice Registers 388 54576 0% May 14 – 16, 2012. military communications, steganography can be very useful when two moves to an idle state (state 7). Number of Slice LUTs 705 27288 2% [3] J. Cummins, P. Diskin, S. Lau, and R. Parlett R, “Steganography And Digital Watermarking”, 2004. [Online]. parties need to communicate inside enemy lines. Another possible Number of fully used LUT-FF pairs 308 785 39% The algorithm has been implemented on an Atlys Spartan 6 development board. Table 1 lists the resources used for the Available: http: //www. cs. bham. ac. uk/~mdr/teaching/modules 03/security/students/SS 5/Steganography. pdf. Number of bonded IOBs 81 218 37% application of steganography is embedding certain information in a file to implementation of the steganography algorithm. Number of BUFG/BUFGCTRLs 3 16 18% [4] "LFSR Reference -- M-Sequence, Linear Feedback Shift. Register, Feedback Taps for Maximal Length ensure that the file has not been altered - the hidden file can act as a Number of PLL_ADVs 1 4 25% Sequences”, Manufacturer of Spread Spectrum Development & Test Equipment -- PN Sequence (PRBS) checksum for a file. In that sense, steganography may serve as an error Generators for CDMA, WCDMA, DSSS, and FHSS. [Online]. Available: detection method. A similar approach can be used to watermark a picture, http: //www. newwaveinstruments. com/resources/articles/m_sequence_linear_feedback_shift_register_lfsr. htm. as described by Jonathan Cummins [3]. LSB Replacement Algorithm Conclusions Applications References
- Slides: 1