Crypt DBaa S Query Over Encrypted Data Base
Crypt. DBaa. S Query Over Encrypted Data. Base Amr Jamal Barakat Abwe Mohammad Hmedat Supervisor: Dr. Fadi Draidi
Outline • Introduction • Motivation • Design • Algorithms • Query Processing • Evaluation • Conclusion
Introduction • Technology today • Big Data • Cloud computing üSoftware as a Service (Saa. S) üInfrastructure as a Service (Iaa. S) üPlatform as a Service (Paa. S) üHypred Service (Ex. DBaa. S)
Motivation • Security issues. • Old Projects üCrypt. DB • Our Project üCIA Guaranteed
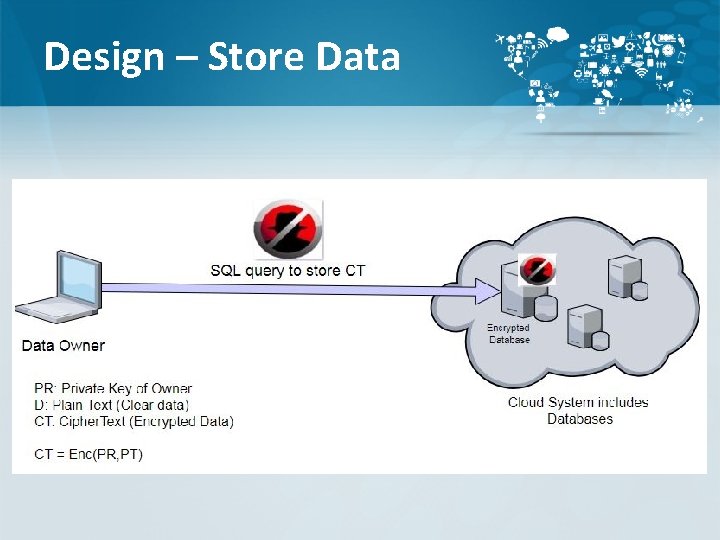
Design – Store Data
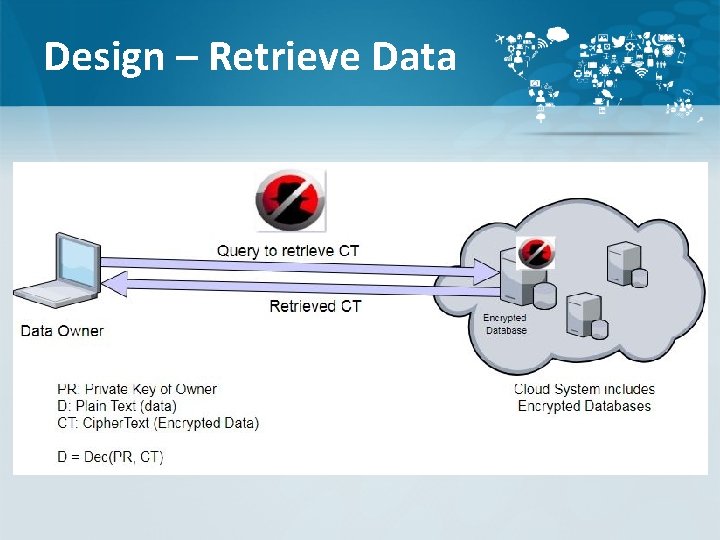
Design – Retrieve Data
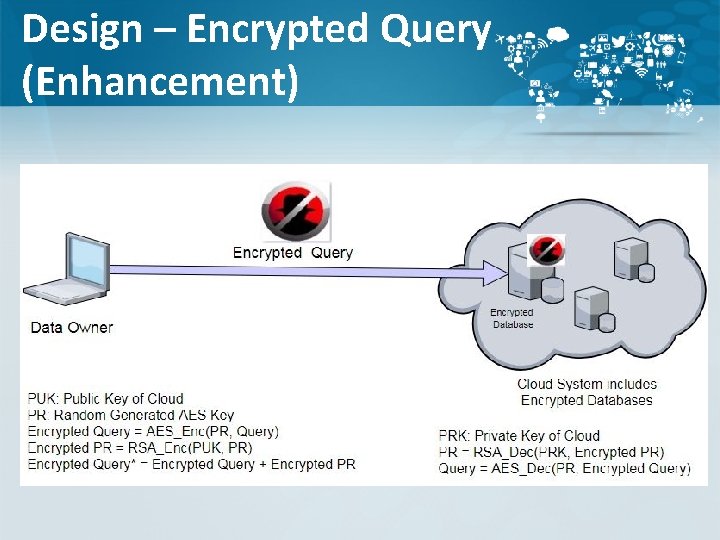
Design – Encrypted Query (Enhancement)
Algorithms • Advanced Encryption Standard (AES) - 256 • Order Preserving Encryption (OPE) – long key • Rivest Shamir Adleman (RSA) - 2048
Query Processing • Query with Exact Match Condition • Search over Encrypted Database. ü Key-Word Encryption technique üPer-Word Encryption technique • Aggregation functions • Join and Union
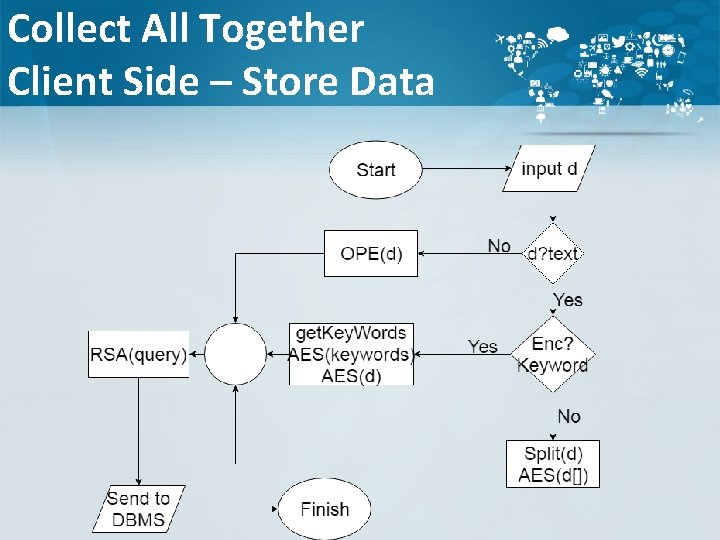
Collect All Together Client Side – Store Data
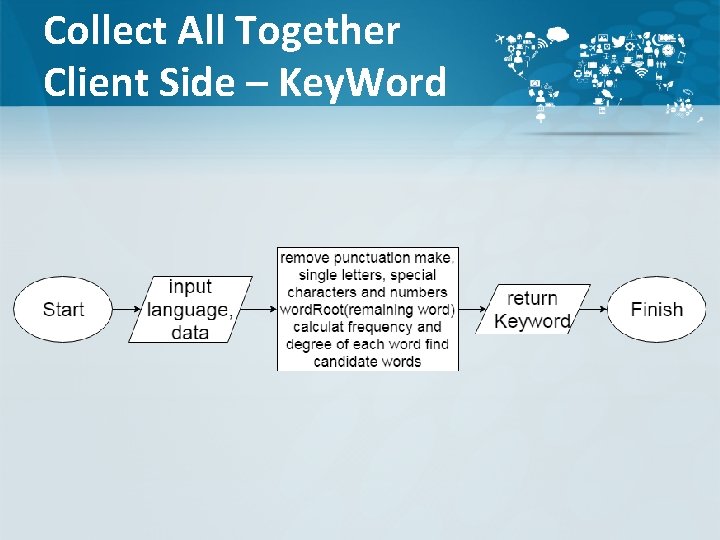
Collect All Together Client Side – Key. Word
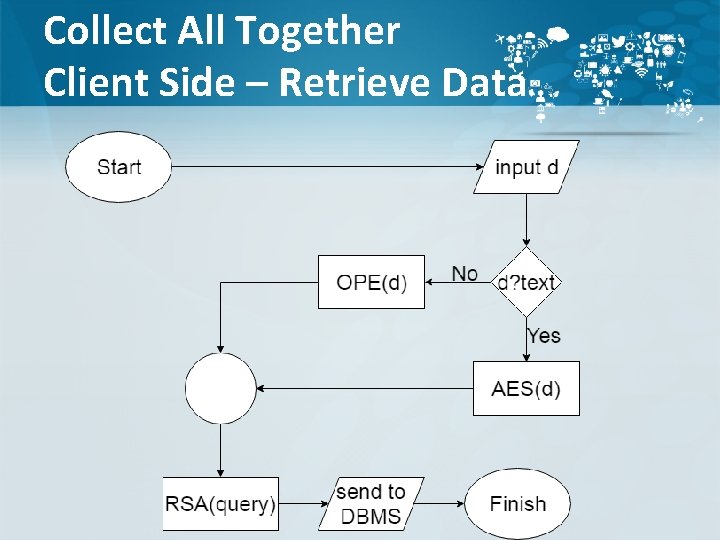
Collect All Together Client Side – Retrieve Data
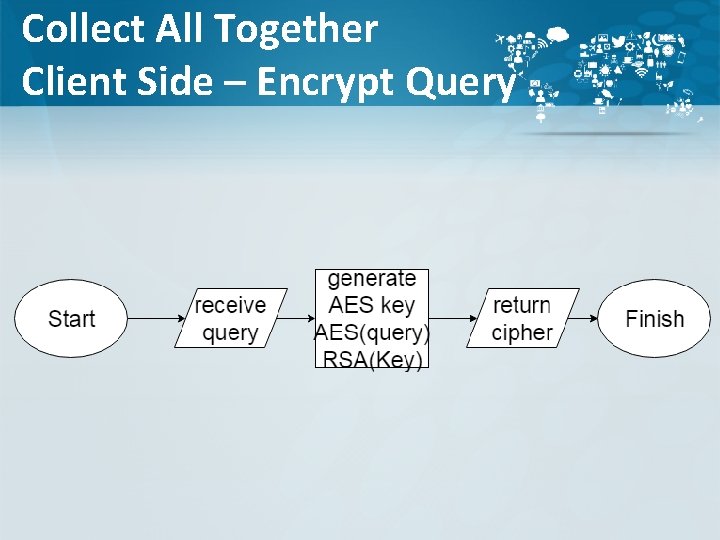
Collect All Together Client Side – Encrypt Query
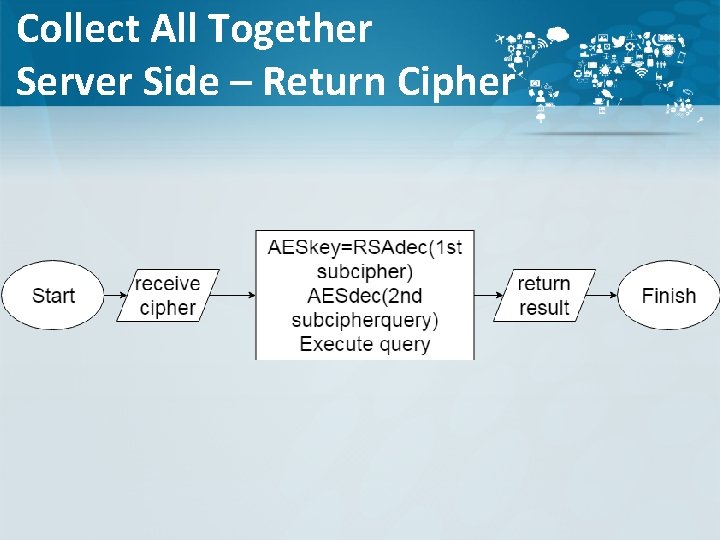
Collect All Together Server Side – Return Cipher
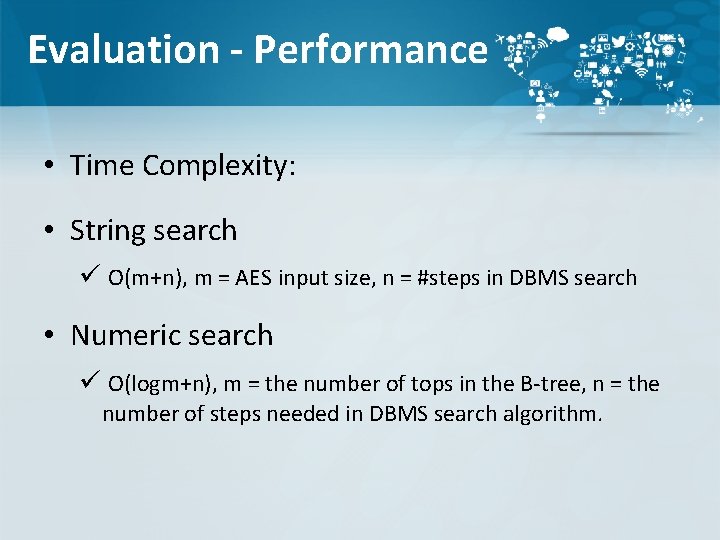
Evaluation - Performance • Time Complexity: • String search ü O(m+n), m = AES input size, n = #steps in DBMS search • Numeric search ü O(logm+n), m = the number of tops in the B-tree, n = the number of steps needed in DBMS search algorithm.
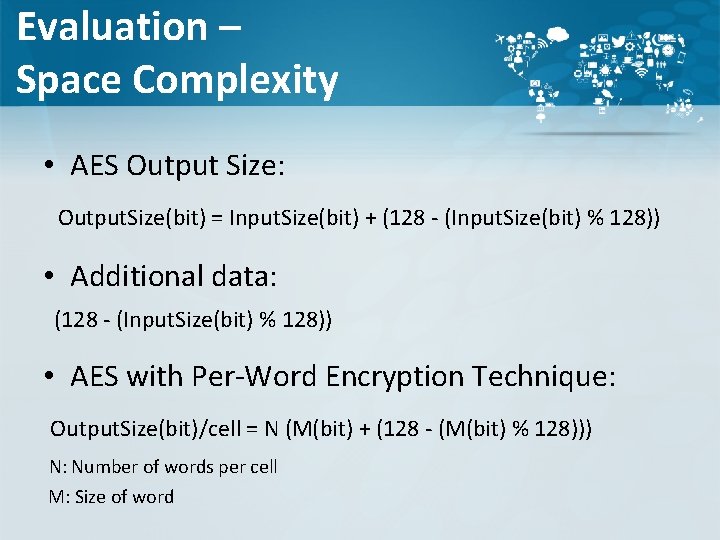
Evaluation – Space Complexity • AES Output Size: Output. Size(bit) = Input. Size(bit) + (128 - (Input. Size(bit) % 128)) • Additional data: (128 - (Input. Size(bit) % 128)) • AES with Per-Word Encryption Technique: Output. Size(bit)/cell = N (M(bit) + (128 - (M(bit) % 128))) N: Number of words per cell M: Size of word
Evaluation – Space Complexity • AES with Key-Word Extraction encryption technique: Worst Cast: number of key-words per cell equals the original number of words in that cell. • Order-preserving Encryption:
Evaluation – Security • Third-Party Trust issue. • Confidentiality Guaranteed. • Algorithm Evaluation: ü Key size (Brute force time). ü Cryptanalytic Attacks.
Evaluation – Security • AES-256 • The AES Cipher is resistant against known attacks except the brute force. • RSA-2048 • Key can be broken not by trying every possible key, but rather factoring. < 512 • Typically RSA key sizes are 1024 -bits+.
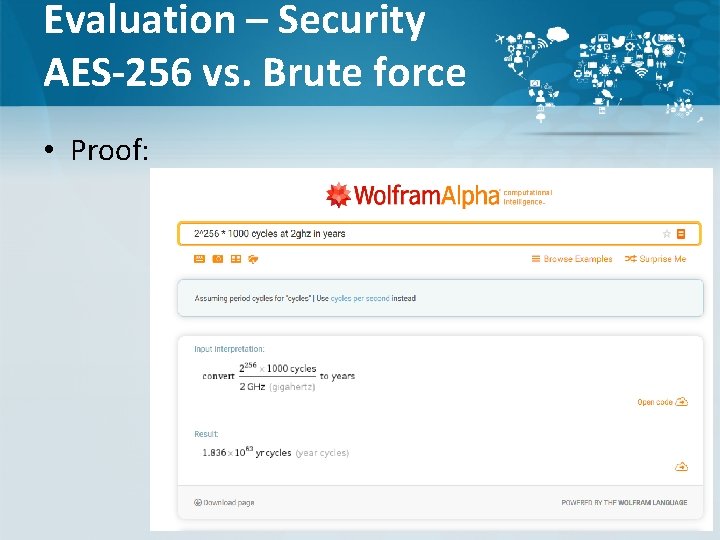
Evaluation – Security AES-256 vs. Brute force • Proof:
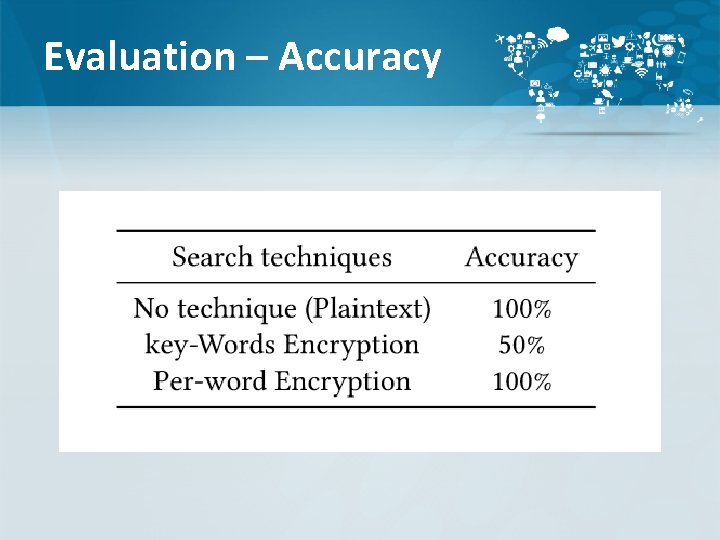
Evaluation – Accuracy
Conclusion • Crypt. DBaa. S is a security model which describes how to securely store your data. • Crypt. DBaa. S guarantee the confidentiality between cloud and data owner. • Crypt. DBaa. S uses strong encryption algorithms suitable to query and operate over encrypted data. • No need for third-party.
Problems • Hardware scheduling • Formating before send • Time (couldn't edit DBMS code)
Plans • AI keyword. • Implement indexing/feltering for sreach. • Increasing number of languages.


- Slides: 26