Crypt DB Protecting Confidentiality with Encrypted Query Processing
Crypt. DB: Protecting Confidentiality with Encrypted Query Processing Raluca Ada Popa, Catherine M. S. Redfield, Nickolai Zeldovich, and Hari Balakrishnan MIT CSAIL Presenter Kecong Tang
DBA story n Rules – Should never read the data. – If you have to, FORGET them TOTALY after you’re done! n Some Jobs need to read the data – “hey we get data conflicted ” – “we need you to recover some data” – “we need a special data collection”
Problems Online applications are vulnerable to theft of sensitive information. n Who? n – Curious & Malicious DBA – Attackers gain Admin or DBA level access n What? – Confidentiality
Solutions: n Crypt. DB n Encrypted Query Processing
Introducing Crypt. DB n Encrypted database – Nothing is pain text – By different keys and encryptions for different columns and users’ data
Three key ideas: n SQL-aware encryption n Adjustable query-based encryption n Chain encryption keys to user passwords
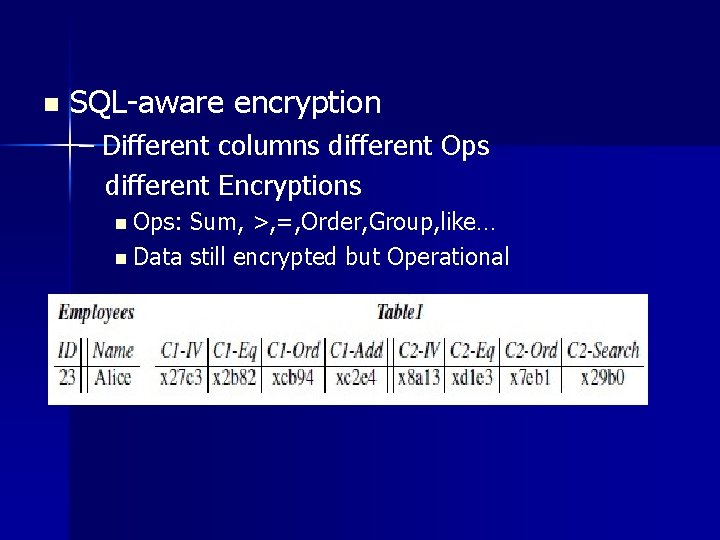
n SQL-aware encryption – Different columns different Ops different Encryptions n Ops: Sum, >, =, Order, Group, like… n Data still encrypted but Operational
n Adjustable query-based encryption Type Date usually for “order by” What if I search “ 2012 -04 -01”? Re-encryption to the required format.
n Chain encryption keys to user passwords – Data is only availably when user login – Different users’ data different encryption keys n This can deal with SQL injection n Hacker will get encrypted data without keys
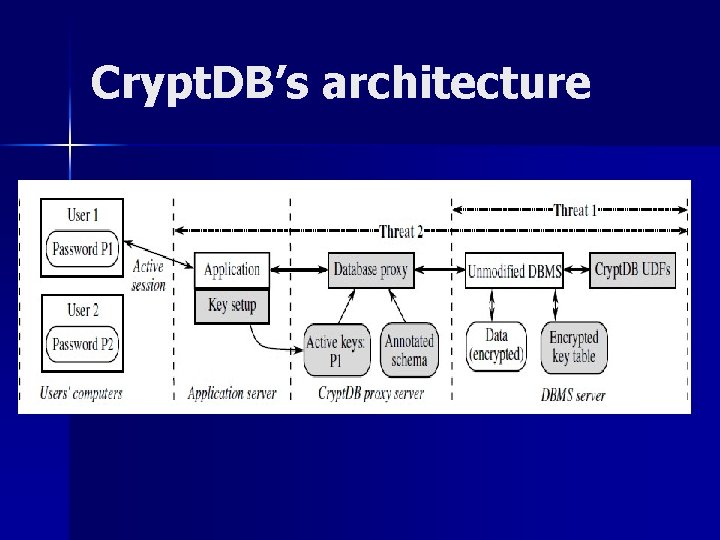
Crypt. DB’s architecture
n Application server – Normal front web page – User login – Key setup to Database poxy n Crypt. DB proxy server – Active keys – Annotate schema n DBMS server – – – Normal DBMS with encrypted data User defined functions to encrypt Encrypted Key table
n Threat 1: DBMS server Compromise full access DBA or attacker usually read data Server cannot compute the (encrypted) results
n Threat 2: All servers are compromised Different user different key Inactive users’ key are not available Only logged-in users’ key can be decrypted
Case Studies php. BB is a widely used open source forum with a rich set of access control settings. n Hot. CRP is a popular conference review application n grad-apply is a graduate admissions system used by MIT EECS n
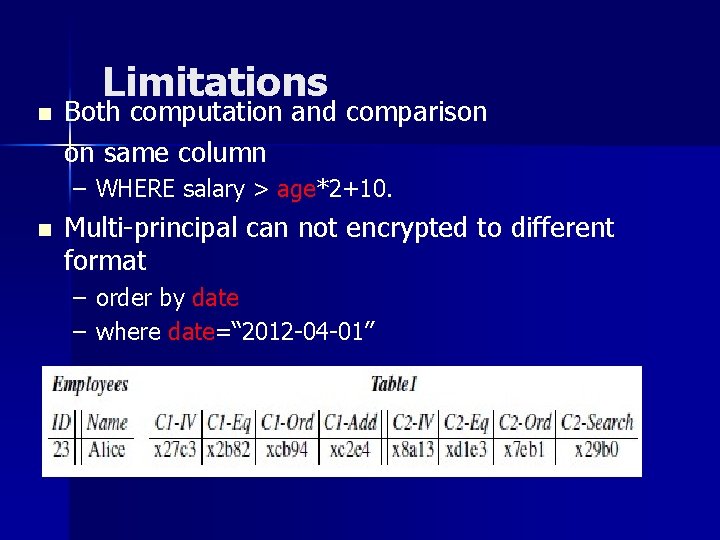
n Limitations Both computation and comparison on same column – WHERE salary > age*2+10. n Multi-principal can not encrypted to different format – order by date – where date=“ 2012 -04 -01”
Contribution n Definitely improve Data Security n Prevent data leaking even the server totally compromise
Weakness n Performance – Frequently Re-write Time, update 1 column in an-over-100 k-lines MYSQL table will take ? ? minutes. Harddrive life: frequently Harddrive writting n Data repair and Offical Investigate – It takes time even they can decrypt.
Improvement n Should we open a Back Door? – “One button to decrypt all data”…
Thanks n Questions?
- Slides: 19