Crowds Anonymity for Web Transactions Michael Reiter and
Crowds: Anonymity for Web Transactions Michael Reiter and Avi Rubin 1998
Privacy Online • Supreme Court Justice Louis Brandeis defined privacy as "the right to be let alone", which he said was one of the rights most cherished by Americans. • The Internet represents previously inconceivable opportunities to monitor your actions and personal information! • Just imagine the Mc. Carthy hearings now.
Strong Privacy Online • NSA, FBI, etc. • Consumer databases, Axciom, and Hackers • What about *Bad Guys*? Beware the Four Horsemen of the Information Apocalypse: terrorists, drug dealers, kidnappers, and child pornographers. Seems like you can scare any public into allowing the government to do anything with those four. - Bruce Schneier • Good Guys: CIA, Undercover Cops, Biz. , etc.
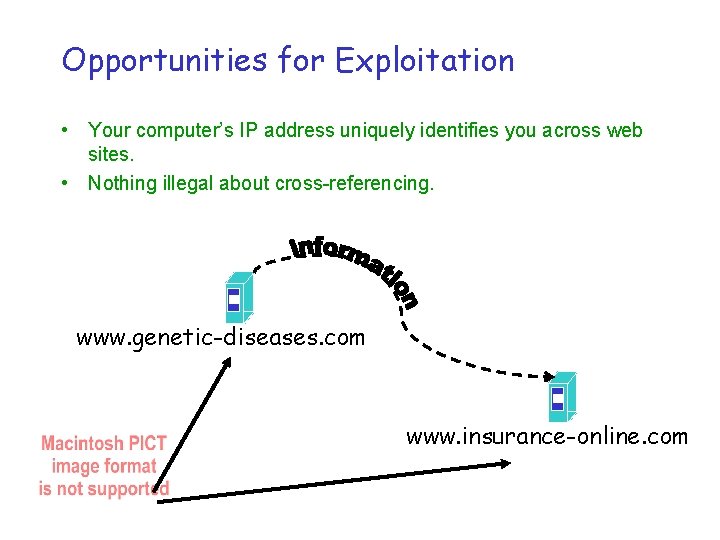
Opportunities for Exploitation • Your computer’s IP address uniquely identifies you across web sites. • Nothing illegal about cross-referencing. www. genetic-diseases. com www. insurance-online. com
Conclusions: Free Exchange • The Internet’s benefit increases directly with – the number of resources online – the privacy people having in obtaining it – The privacy people have in serving it • Anonymity is a promising technology for providing user privacy.
Why Anonymity? • Today, only 20% of web sites meet the FTC’s fair information practices. • Anonymity is a technical means to privacy – Without cooperation of the receiver. • Legitimate social uses on the Net – Allow for safe “whistle blowing” – Privacy in medical issues or psychological counseling – Web surfing privacy – Web serving privacy
Anonymous Routing • Anonymity is the state of being indistinguishable from other members of some group. • Our goal is to provide mechanism for routing that hides initiator’s IP address • Not trying to protect content of message. – Can use end-to-end encryption for that. • That said. . . – Does not protect higher-level protocols/data. – Doesn’t make sense to send “I’m Matt and my SSN is. . . ” anonymously.
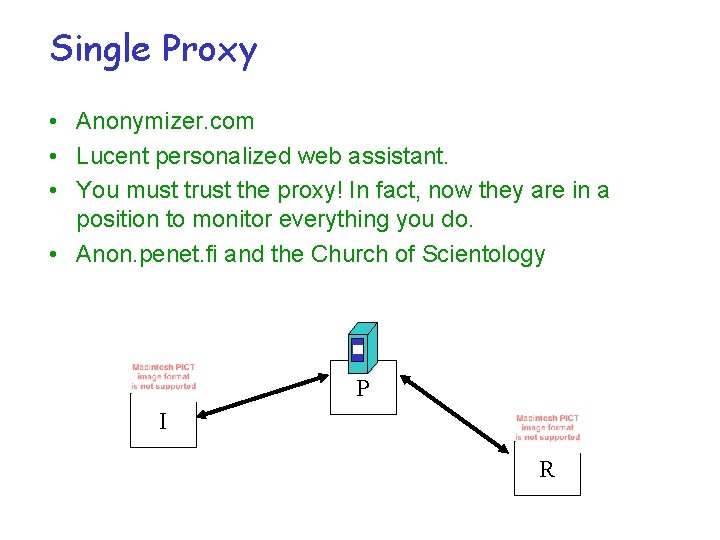
Single Proxy • Anonymizer. com • Lucent personalized web assistant. • You must trust the proxy! In fact, now they are in a position to monitor everything you do. • Anon. penet. fi and the Church of Scientology P I R
Crowds • Key Contributions?
Crowds • Decentralized P 2 P solution • Anonymous within the Crowd • Jondo (John Doe) – Proxy – User • Path based
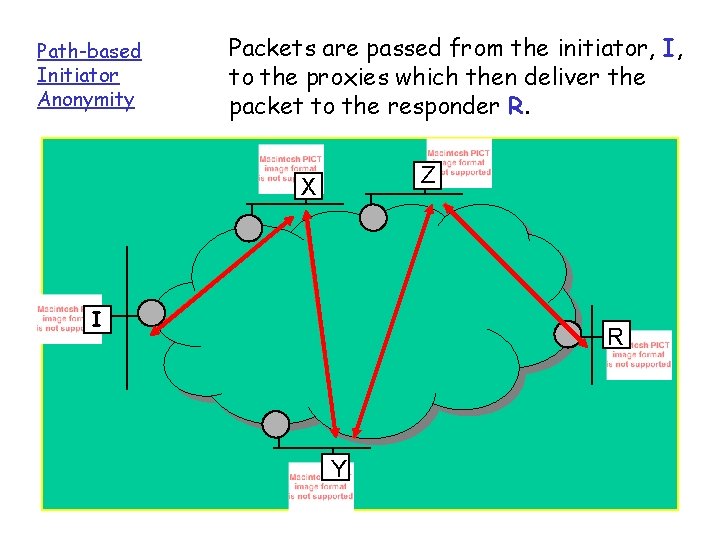
Path-based Initiator Anonymity Packets are passed from the initiator, I, to the proxies which then deliver the packet to the responder R. Z X I R Y
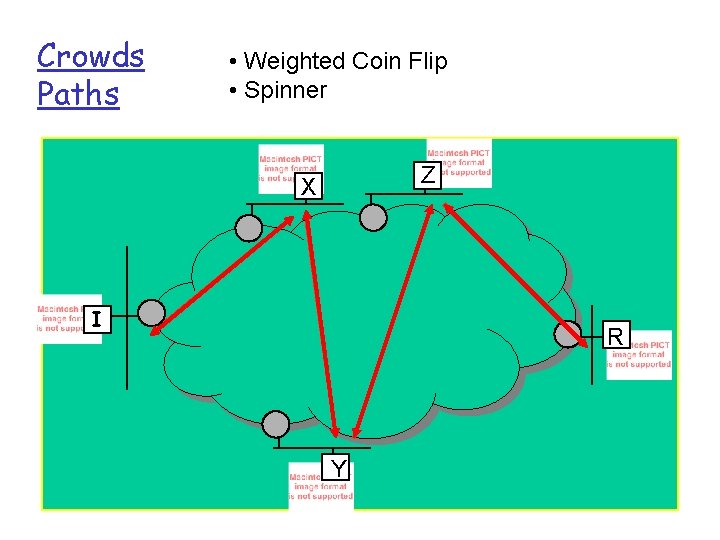
Crowds Paths • Weighted Coin Flip • Spinner Z X I R Y

Does it work? • Threat models: – Responder (end server): Beyond Suspicion! – Local eavesdropper – Malicious (collaborating) Jondos • Types of attacks: – Timing attacks – Passive logging – Traceback
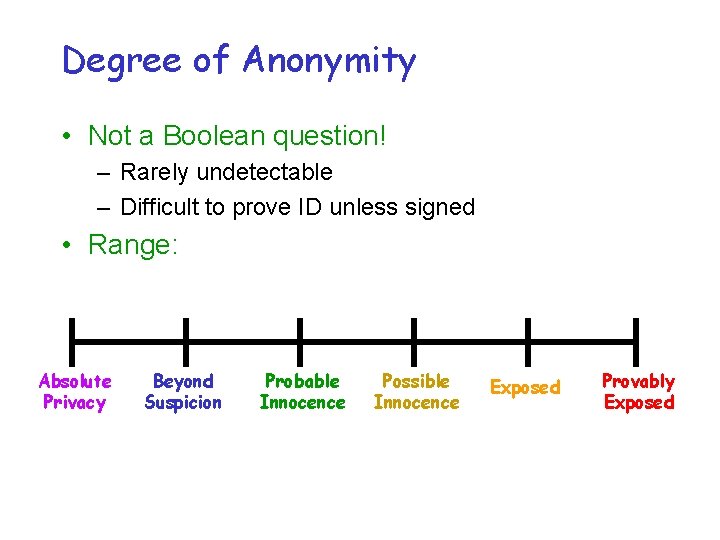
Degree of Anonymity • Not a Boolean question! – Rarely undetectable – Difficult to prove ID unless signed • Range: Absolute Privacy Beyond Suspicion Probable Innocence Possible Innocence Exposed Provably Exposed
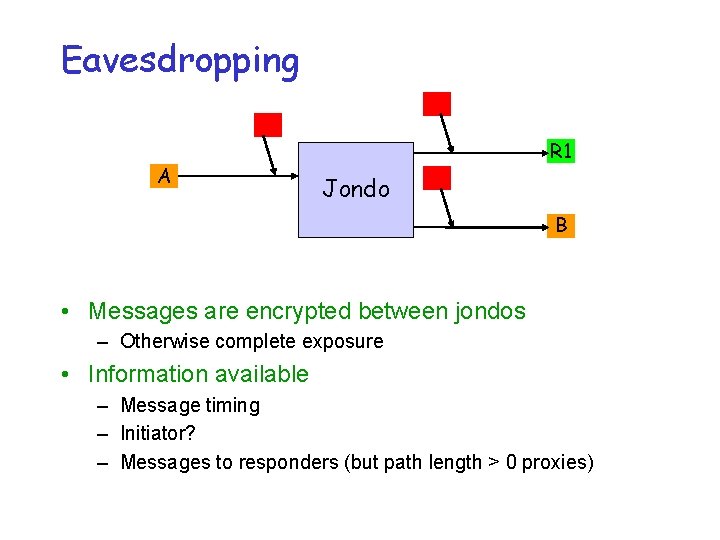
Eavesdropping A R 1 Jondo B • Messages are encrypted between jondos – Otherwise complete exposure • Information available – Message timing – Initiator? – Messages to responders (but path length > 0 proxies)

Malicious Jondos • Giving information – Your IP address is seen by the next node in the path – Being on the path means you might be the initiator • Many attackers – Ratio of attackers (c) to total (n) is important – So is weight of the coin flip (pf) • Innocent? – If pf = 3/4 and n 3(c+1), probable innocence – Higher pf implies greater resilience to attackers I 5 1 2 R 4 3

Performance • Path length – A function of pf : larger = longer paths • Latency – note: all local nodes, no error info. – note 2: older machines; encryption is more expensive – latency of up to 13. 5 seconds! (8. 6 for 1 -hop) – No 0 -hop tests
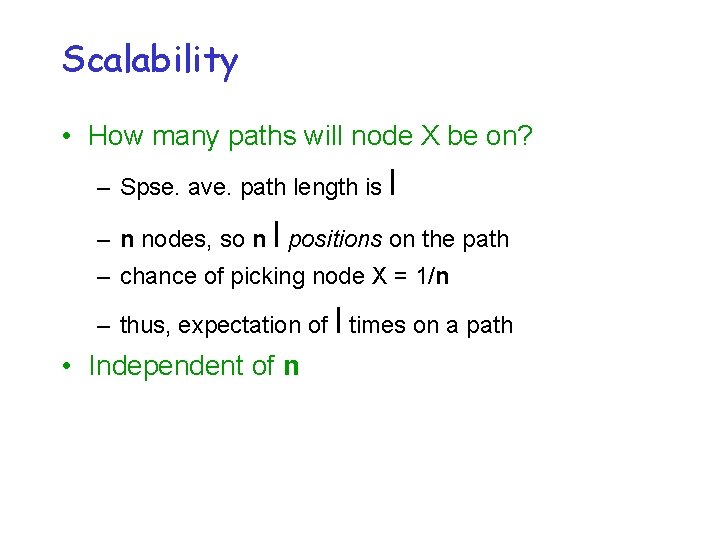
Scalability • How many paths will node X be on? – Spse. ave. path length is l – n nodes, so n l positions on the path – chance of picking node X = 1/n – thus, expectation of l times on a path • Independent of n
End of Crowds
Strengths • Performance & Scaling • Security against weak attackers – single operators generally fail • ISP, web site, your neighborhood eavesdropper, one person with a few jondos • Parameter to trade off security/performance
Usability Weaknesses • Must disable Java & Active. X • More generally, a good proxy required – clean all traces – could be bypassed? • Group membership – keeping a full list may be hard/expensive – centralizing it provides a way to attack – (intersection attack) • Delay in joining • Group size – required to have either small or large groups • Network delays
Security Weaknesses • Problem – strong eavesdroppers exist – Sybil attacks (many bad peers) – Combined attacks possible (e. g. local eavesdropper + responder) • Collaborating members – increasing bad peers guarantees compromise – growing threat over time • DOS + Sybil attack – always changing non-sending members
Security Weaknesses • Possible eavesdrop – When many peers use the same ISP (cable modem, DSL), a full path may be controlled by the ISP. • Exposure of information – a path of nodes that sees all – info. can allow attackers to guess at initiators – can change web requests
- Slides: 23