Bitcoin and Anonymity Bitcoin and Anonymity Bitcoin is
Bitcoin and Anonymity
Bitcoin and Anonymity “Bitcoin is a secure and anonymous digital currency” — Wiki. Leaks donations page
Bitcoin and Anonymity “Bitcoin won't hide you from the NSA's prying eyes” — Wired UK
What do we mean by anonymity? Anonymous = without a name Bitcoin addresses are public key hashes, not real names. The address that you use is a pseudo-identity. Computer scientists call it pseudonymity.
Anonymity in computer science Anonymity refers to pseudonymity together with unlinkability Unlinkability: if a user interacts with the system repeatedly, these different interactions should not be able to be tied to each other from the point of view of the adversary in consideration.
Why do we need unlinkability? • Many bitcoin services require real identities. • A pseudonymous profile can be deanonymized due to side channels, or indirect leakages of information
Unlinkability in the Bitcoin context 1. It should be hard to link together different addresses of the same user. 2. It should be hard to link together different transactions made by the same user. 3. It should be hard to link the sender of a payment to its recipient.
Quantifying anonymity • Complete unlinkability is hard. • Anonymity set of a transaction: the set of transactions which the adversary cannot distinguish from your transaction. • We try to maximize the size of the anonymity set
Quantifying anonymity • Calculating the anonymity set: • concretely define what your adversary model is • reason carefully about what that adversary knows, what they don't know, and what the adversary cannot know for the transaction to be considered anonymous.
Why anonymous cryptocurrencies? In block chain-based currencies, all transactions are recorded on the ledger, they are publicly and permanently traceable to the associated addresses. The privacy of your Bitcoin transactions can potentially be far worse than with traditional banking. • If your real-world identity ever gets linked to a Bitcoin address, then you have totally lost privacy for all transactions — past, present, and future. • Since the block chain is publicly available, literally anyone might be able to carry out this type of deanonymization.
Ethics of anonymity • Most people are uncomfortable sharing their salaries with their friends and coworkers. • Organizations also have important financial privacy concerns. • Money laundering or other illegal activities. The interface between digital cash and fiat currencies is neither anonymous nor pseudonymous
Ethics of anonymity Can't we keep only the good uses of anonymity and the bad uses are somehow prohibited? No! Use cases that we classify as good or bad from a moral viewpoint are technologically identical. How could we task miners with making moral decisions about which transactions to include?
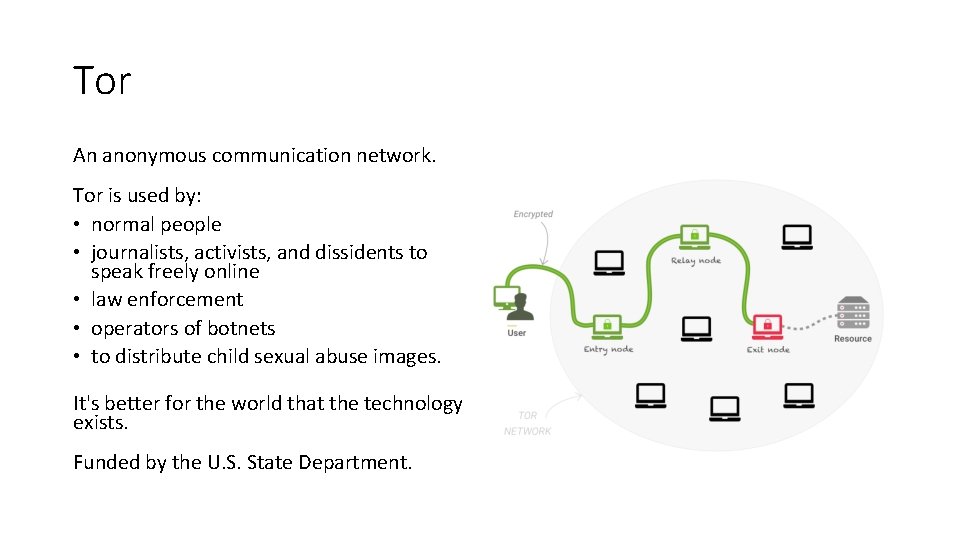
Tor An anonymous communication network. Tor is used by: • normal people • journalists, activists, and dissidents to speak freely online • law enforcement • operators of botnets • to distribute child sexual abuse images. It's better for the world that the technology exists. Funded by the U. S. State Department.
Anonymous e-cash David Chaum, 1982 Blind signature: Two-party protocol to create digital signature without signer knowing the input
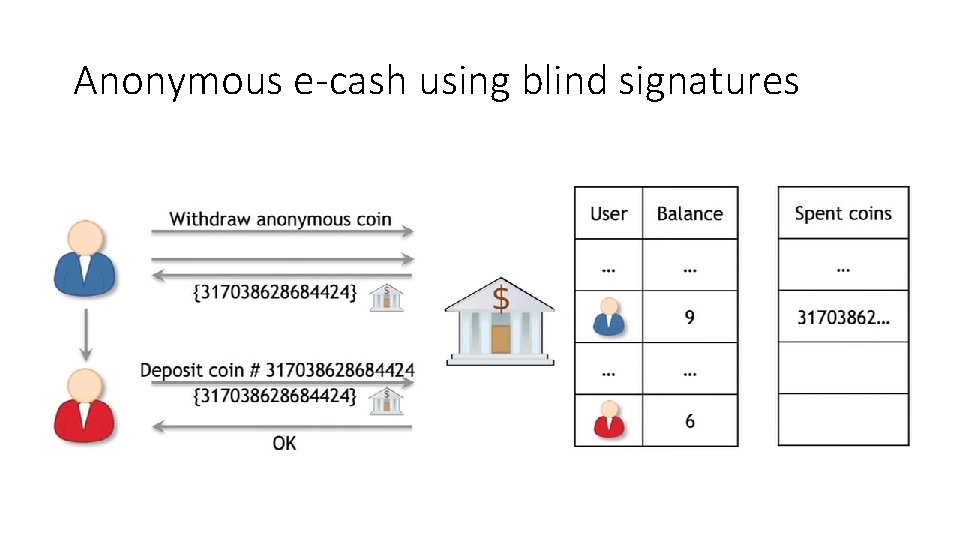
Anonymous e-cash using blind signatures
Anonymization vs. decentralization • Interactive protocols with a bank are hard to decentralize • Decentralization often achieved via public traceability to enforce security (e. g. prevent double spending)
Wiki. Leaks Donation
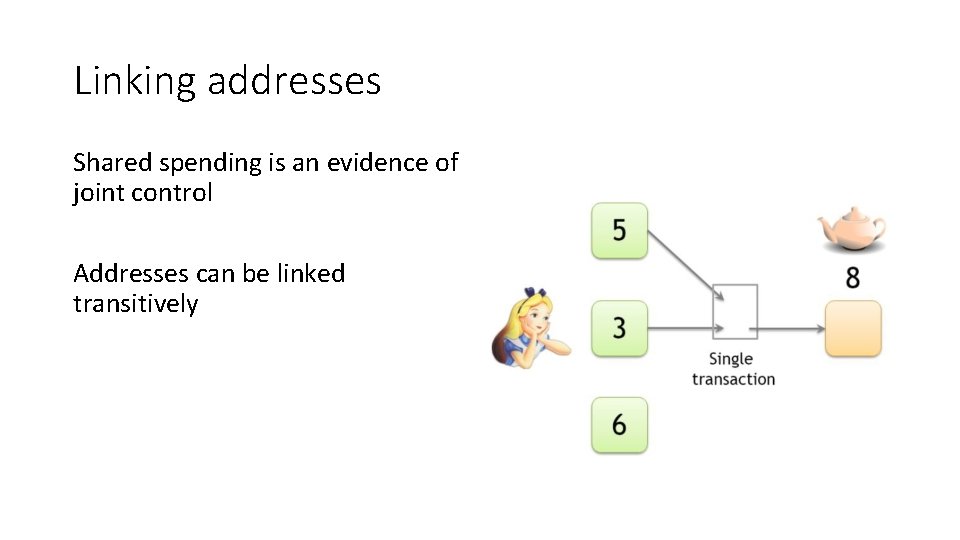
Linking addresses Shared spending is an evidence of joint control Addresses can be linked transitively
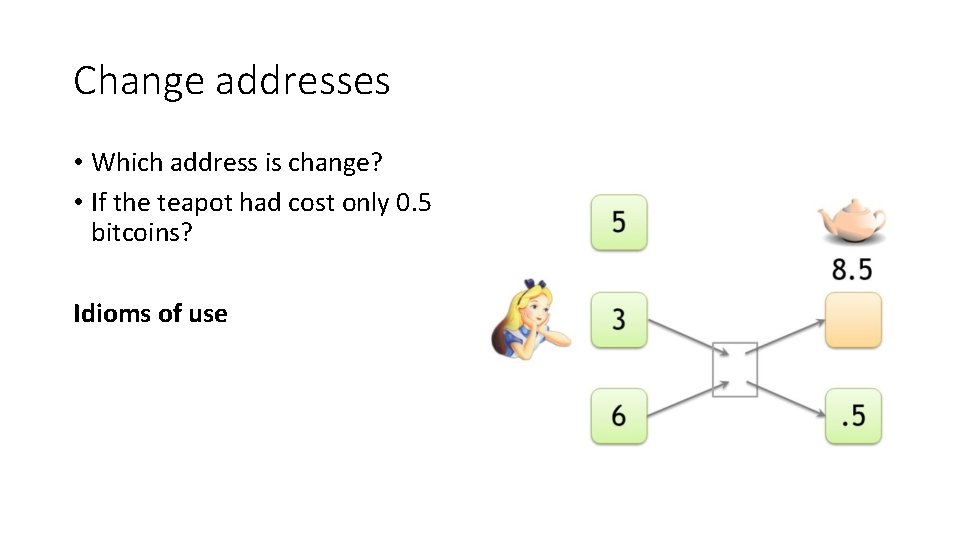
Change addresses • Which address is change? • If the teapot had cost only 0. 5 bitcoins? Idioms of use
Idioms of use Wallets typically generate a fresh address whenever a change address is required. Change addresses are generally addresses that have never before appeared in the block chain. Non-change outputs are often not new addresses and may have appeared previously in the block chain. This knowledge can distinguish change addresses and link them with the input addresses.
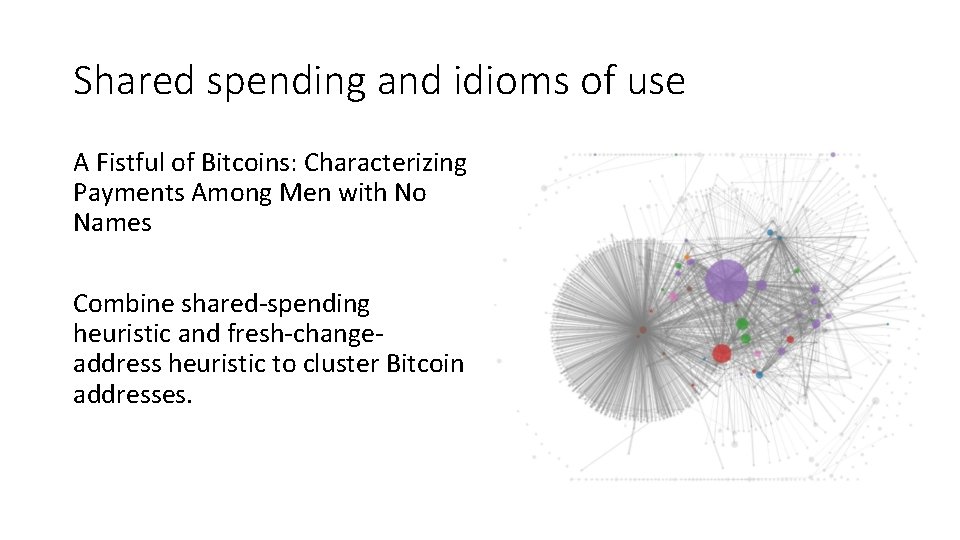
Shared spending and idioms of use A Fistful of Bitcoins: Characterizing Payments Among Men with No Names Combine shared-spending heuristic and fresh-changeaddress heuristic to cluster Bitcoin addresses.
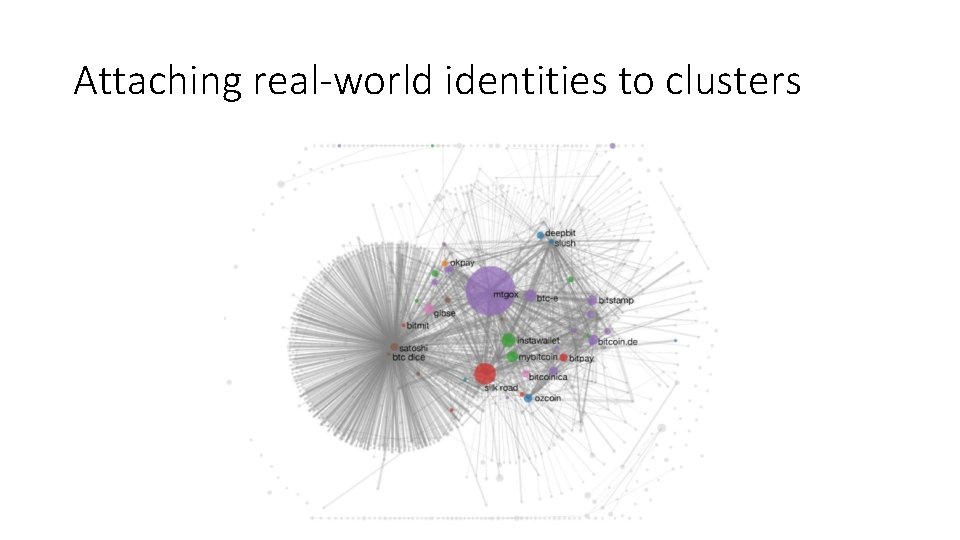
Attaching real-world identities to clusters
Identifying individuals Can we connect little clusters corresponding to individuals to their reallife identities? • Directly transacting. • Via service providers. • Carelessness. • Things get worse over time.
Network-layer deanonymization Dan Kaminsky at the 2011 Black Hat conference: “the first node to inform you of a transaction is probably the source of it. ” Link the transaction to the node’s IP address is close to a real-world identity. A solution: Tor
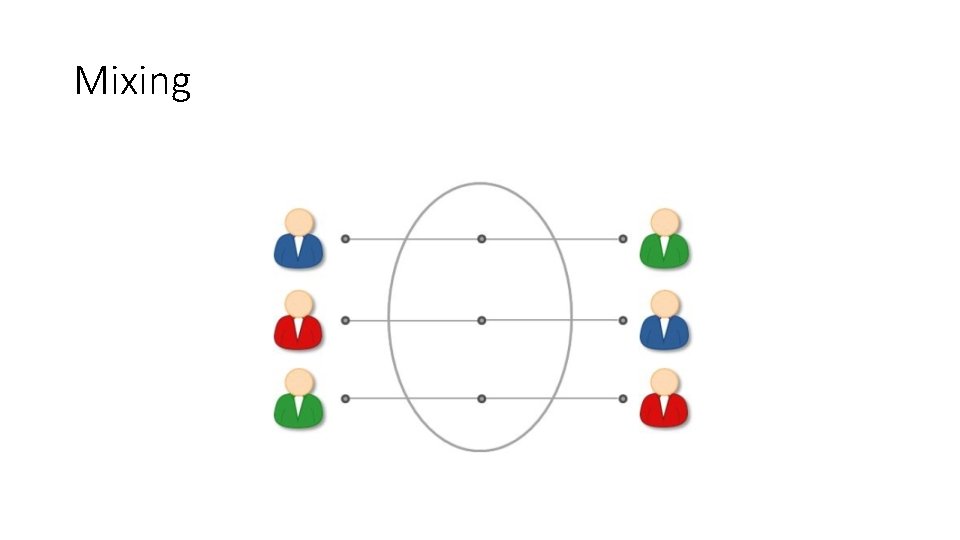
Mixing

Online wallets as mixes Store bitcoins online and withdraw them later. Typically the coins that you withdraw won’t be the same as the coins you deposited. They do provide a measure of unlinkability which can foil attempts at transaction graph analysis. The anonymity provided by online wallets is similar to that provided by the traditional banking system.
Dedicated mixing services Mix, Mixer or Laundry • Promise not to keep records • They do not require your identity
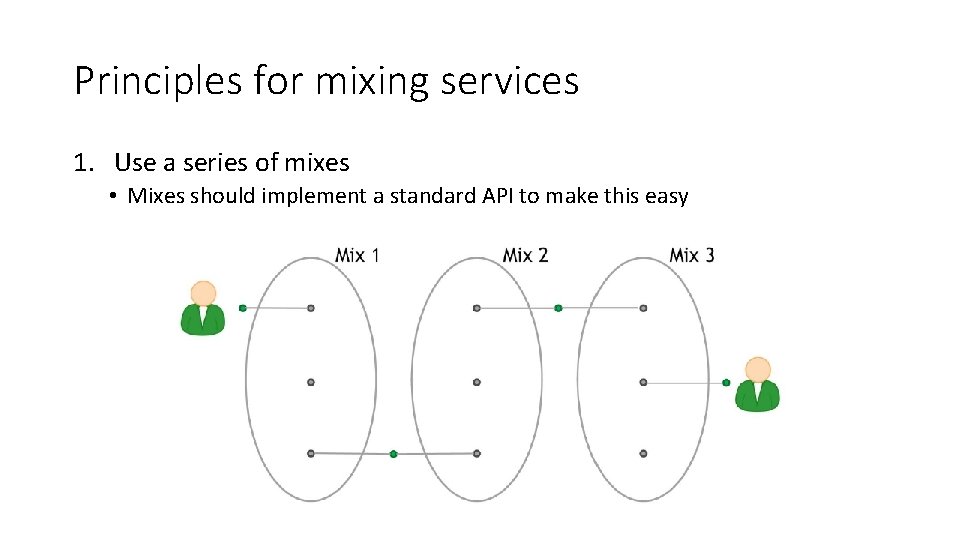
Principles for mixing services 1. Use a series of mixes • Mixes should implement a standard API to make this easy
Principles for mixing services 2. Uniform transactions • All mixes should agree on a standard chunk size • A series of two or three increasing chunk sizes will provide a reasonable tradeoff between efficiency and privacy. 3. Client side should be automated • A clever adversary can attempt to de-anonymize by observing the timing of transactions. 4. Fees must be all-or-nothing • Probabilistic fees: 0. 1% mixing fee = mix will swallow chunk with 0. 1% chance.
Decentralized Mixing Replace mixing services with a peer-to-peer protocol Advantages: • No bootstrapping problem • Theft is impossible • Better anonymity • More philosophically aligned with Bitcoin

Coinjoin Different users jointly create a single Bitcoin transaction. Signatures corresponding to each input are separate from and independent of each other. You don’t need one party to collect all of the private keys.
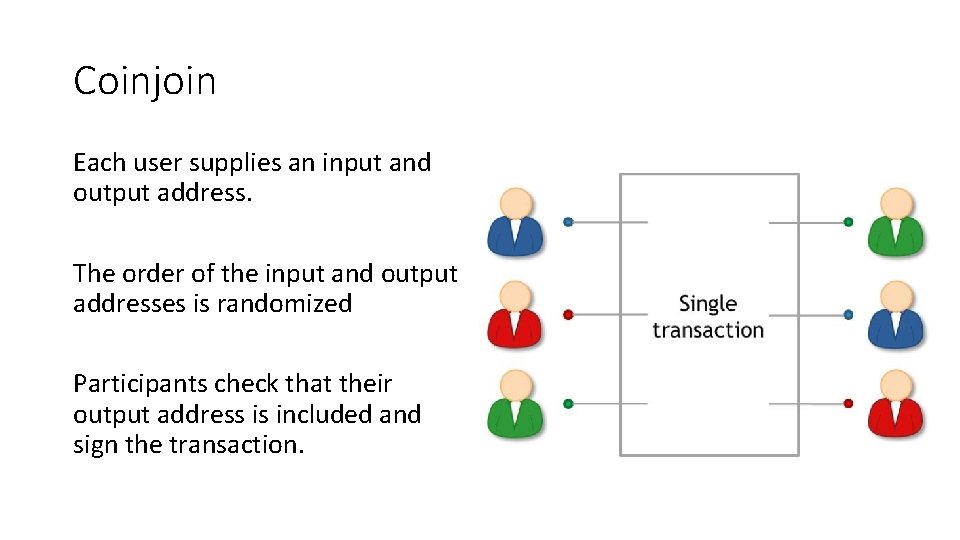
Coinjoin Each user supplies an input and output address. The order of the input and output addresses is randomized Participants check that their output address is included and sign the transaction.
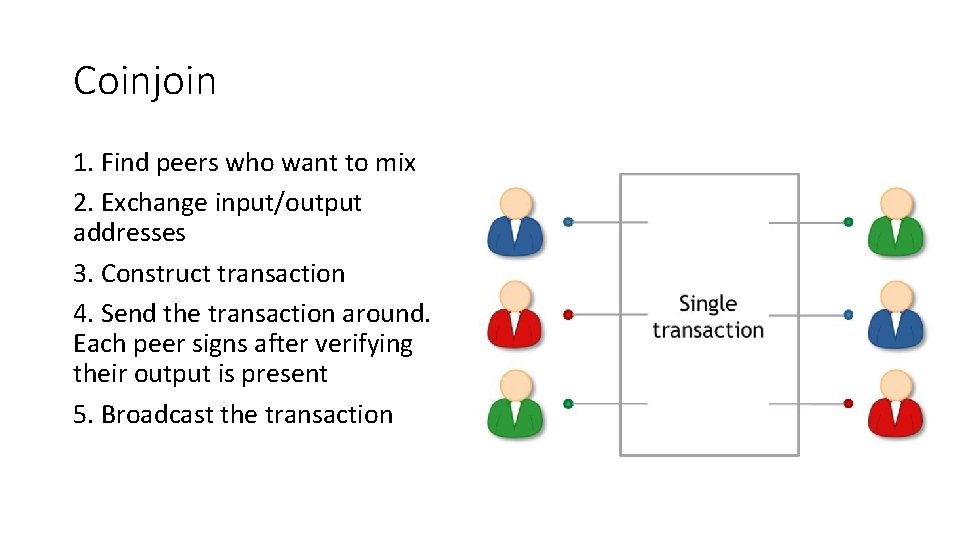
Coinjoin 1. Find peers who want to mix 2. Exchange input/output addresses 3. Construct transaction 4. Send the transaction around. Each peer signs after verifying their output is present 5. Broadcast the transaction
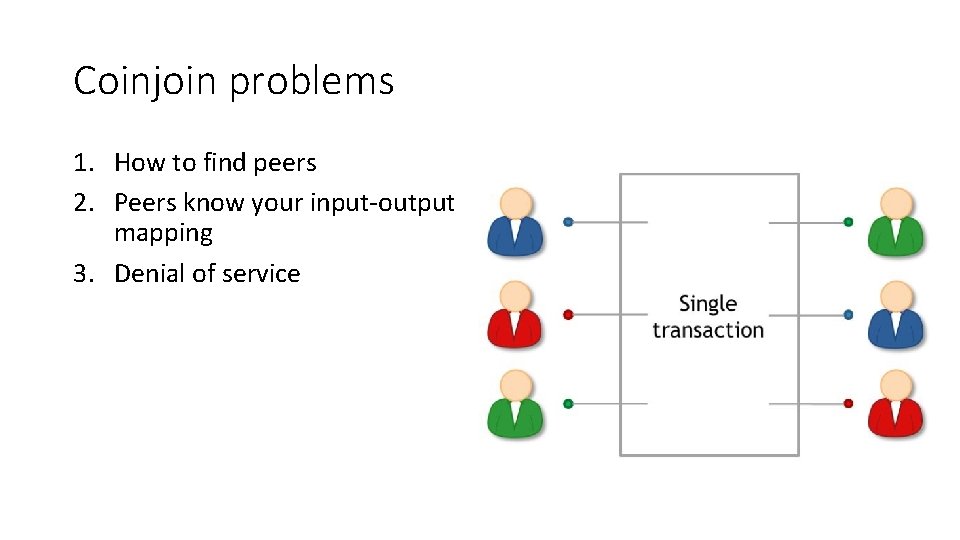
Coinjoin problems 1. How to find peers 2. Peers know your input-output mapping 3. Denial of service
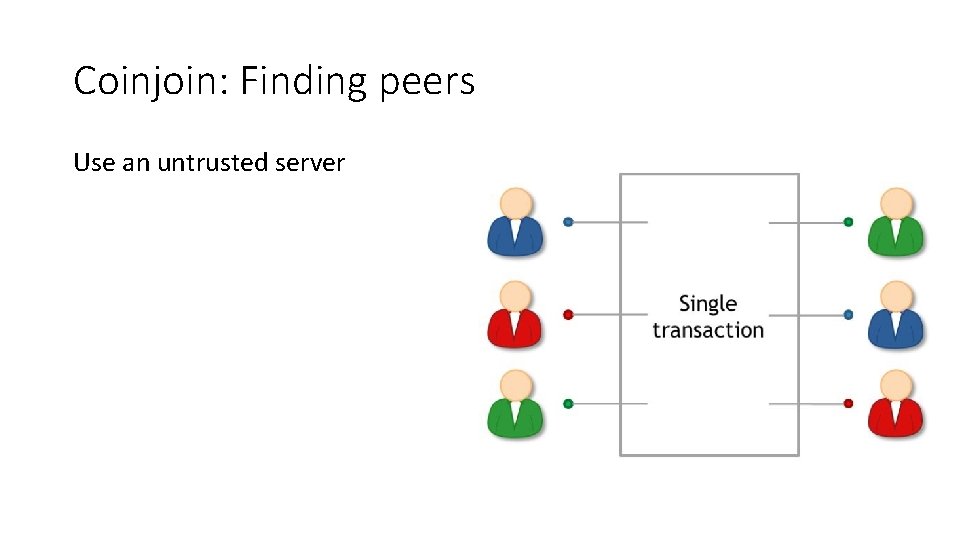
Coinjoin: Finding peers Use an untrusted server
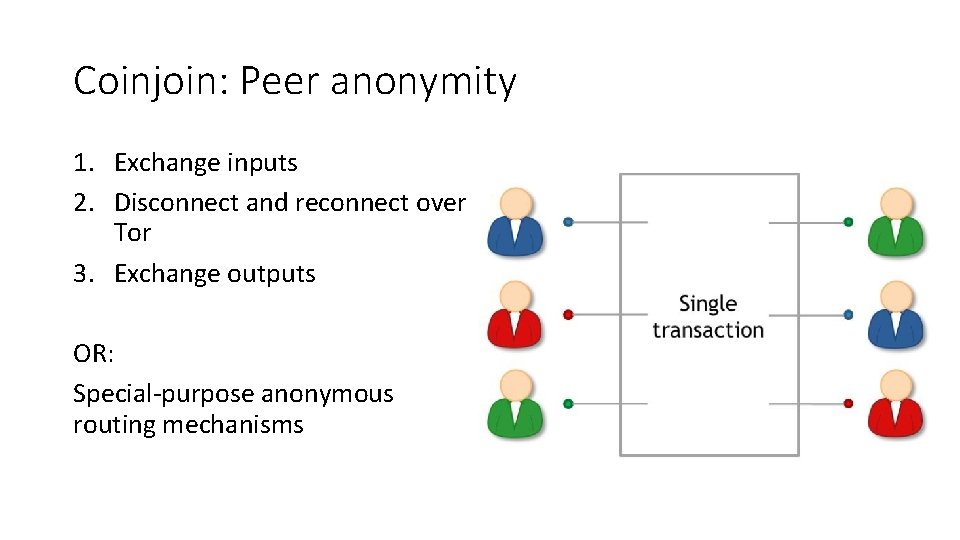
Coinjoin: Peer anonymity 1. Exchange inputs 2. Disconnect and reconnect over Tor 3. Exchange outputs OR: Special-purpose anonymous routing mechanisms

Coinjoin: Denial of service Possible solutions: • Proof-of-work • Proof-of-burn • Server kicks out malicious participant • Cryptographic “blame” protocol
High-level flows Alice receives 43. 12312 BTC / month at a particular perhaps as her salary. She automatically and immediately transfers 5% of that amount to her retirement account.
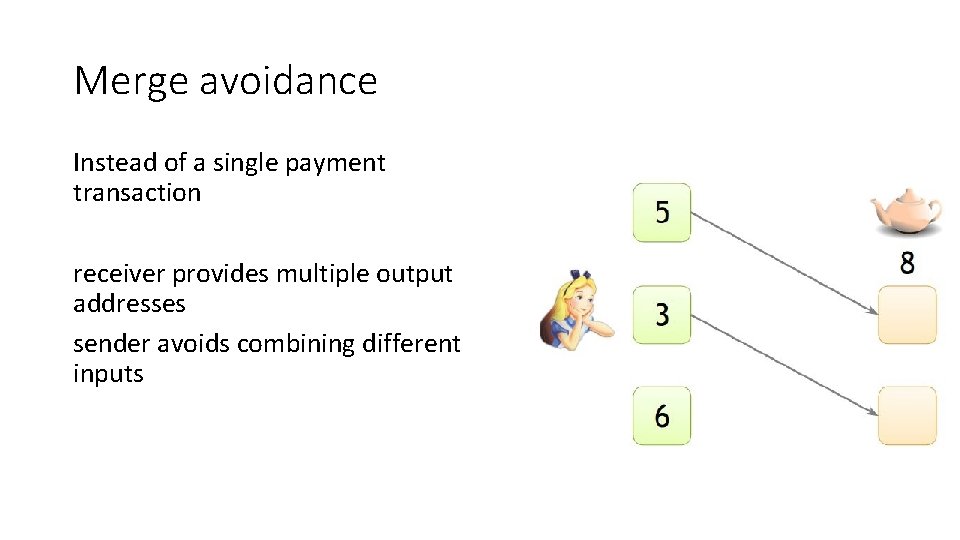
Merge avoidance Instead of a single payment transaction receiver provides multiple output addresses sender avoids combining different inputs
Zerocoin and Zerocash Technically possible to deploy Zerocoin with a soft fork to Bitcoin but infeasible. With Zerocash, a fork is not even possible. An altcoin is the only option.
Zerocoin: Protocol-level mixing Anonymity properties come with cryptographic guarantees. Qualitatively better guarantees than those of the other mixing technologies. No need for trust, promise of anonymity relies only on the adversary’s computational limits Not currently compatible with Bitcoin
Basecoin and Zerocoin Basecoin is an Altcoin Zerocoin is an extension of Basecoins can be converted into Zerocoins and back Provides unlinkability.
Zerocoins A Zerocoin is a cryptographic proof that you owned a Basecoin and made it unspendable. Miners can verify these proofs A Zerocoin gives you the right to redeem a new Basecoin
Zerocoins: The challenges How to construct the proofs? How to make sure each proof can only be “spent” once?
Zero-knowledge proofs A way to prove a statement without revealing any other information. Examples: • “I know an input that hashes to “ 45 d 1 a 758 n 5” • “I know an input that hashes to some hash in the set {h 1, h 2, …hn}
Minting Zerocoins come in standard denominations (assume 1 Basecoin) Anyone can make one They have value once put on the blockchain that costs 1 Basecoin
Minting Zerocoins Generate: a serial number S (eventually made public) a random secret r (never public, ensures unlinkability) Compute H(S, r) Keep S and r secret for now
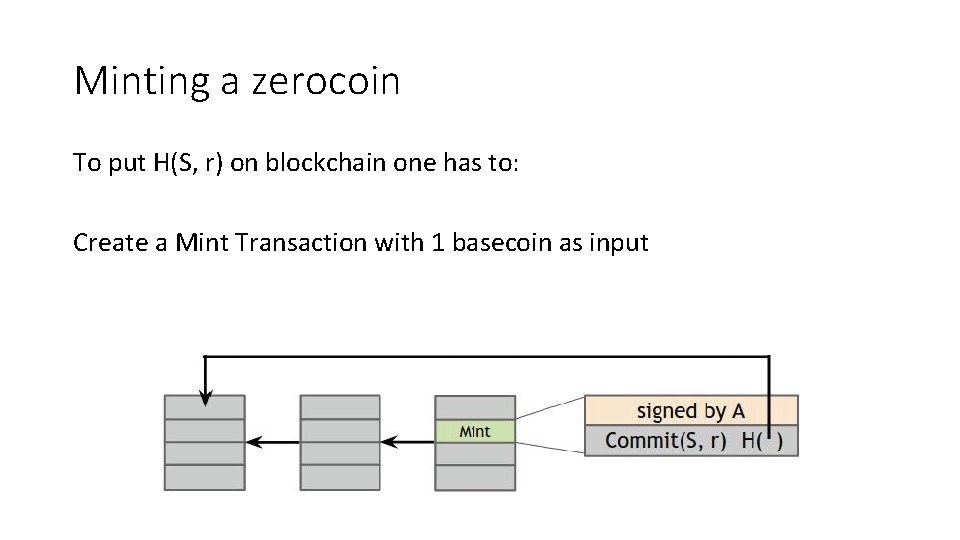
Minting a zerocoin To put H(S, r) on blockchain one has to: Create a Mint Transaction with 1 basecoin as input
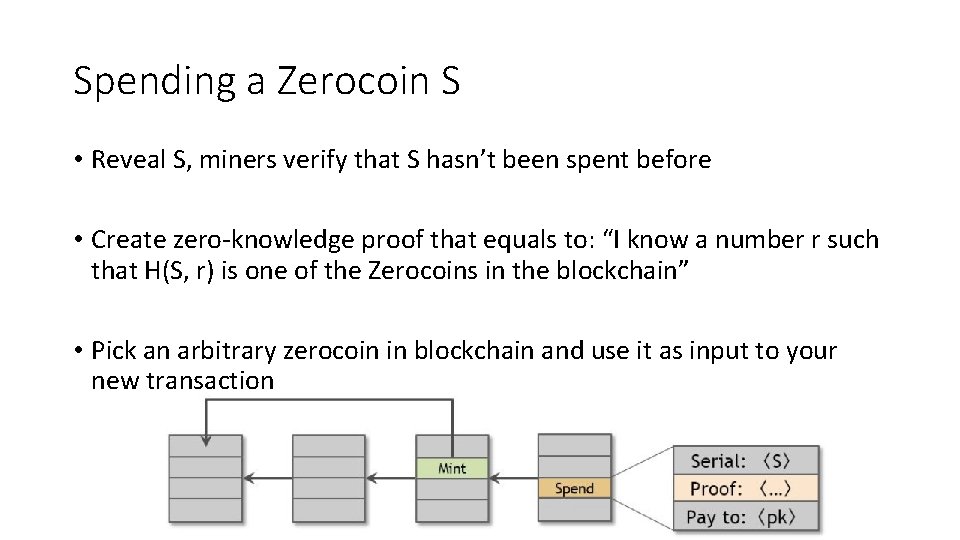
Spending a Zerocoin S • Reveal S, miners verify that S hasn’t been spent before • Create zero-knowledge proof that equals to: “I know a number r such that H(S, r) is one of the Zerocoins in the blockchain” • Pick an arbitrary zerocoin in blockchain and use it as input to your new transaction
Zerocoin Anonymity: r is secret, no one can figure out which zerocoin corresponds to serial number S Efficiency: “I know r such that Commit(S, r) is in the set { c 1 , c 2 , . . . , c n }”. Zerocoin manages to make the size of these proofs only logarithmic in n
Zerocash: Zerocoin without Basecoin Differences: • Different cryptography tools for proofs, zero-knowledge SNARKs (zk. SNARKS) • Run the system without Basecoin
Zerocash All transactions are zerocoins Splitting and merging is supported Put transaction value inside the envelope Ledger merely records the existence of transactions
Zerocash Random, secret inputs are required to generate public parameters. These secret inputs must than be securely destroyed. No one can know them.
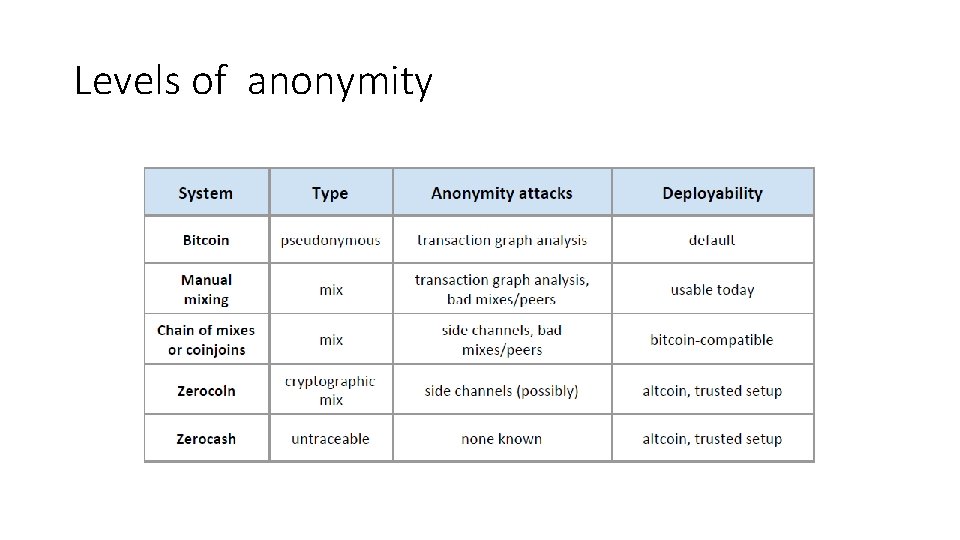
Levels of anonymity
- Slides: 54