Anonymity in Networks Agenda n Overview of Anonymity
- Slides: 53
Anonymity in Networks
Agenda n Overview of Anonymity Mechanisms ¨ What is Anonymity Systems ¨ Kinds of Anonymity and Applications ¨ Mechanisms for Anonymity ¨ Open Issues n Mu. ON: A Protocol for Mutual Anonymity ¨ System Model ¨ Goals of Protocol ¨ Dissemination Protocol ¨ Performance of Mu. ON ¨ Conclusion
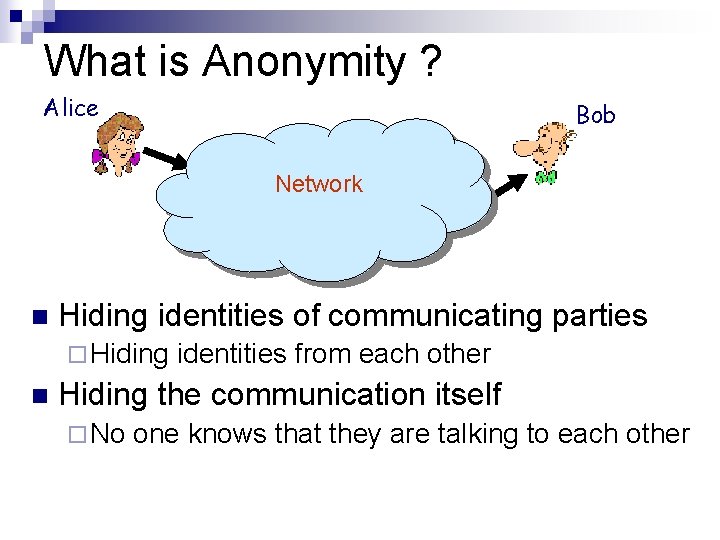
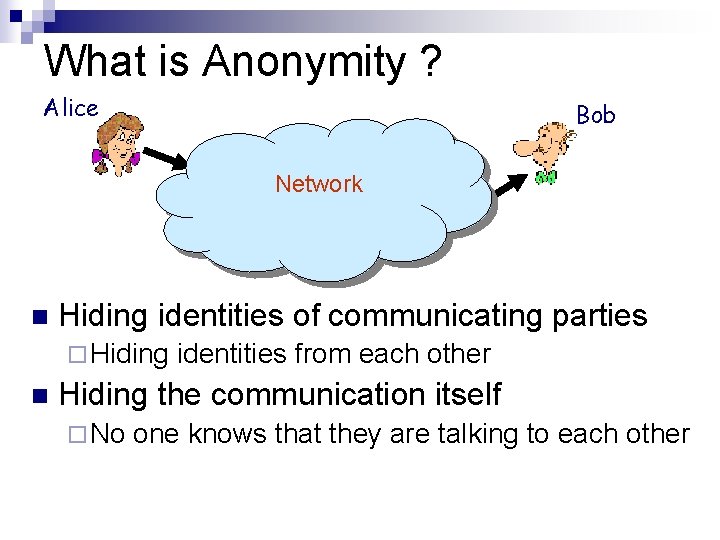
What is Anonymity ? Alice Bob Network n Hiding identities of communicating parties ¨ Hiding n identities from each other Hiding the communication itself ¨ No one knows that they are talking to each other
Possible Solution ? n Users can use false names ¨ When Alice and Bob are talking, Alice says her name is Judy and Bob says his name is Tim. n Alice and Bob encrypt their communication ¨ Third party does not know what they are talking But this is not sufficient !!
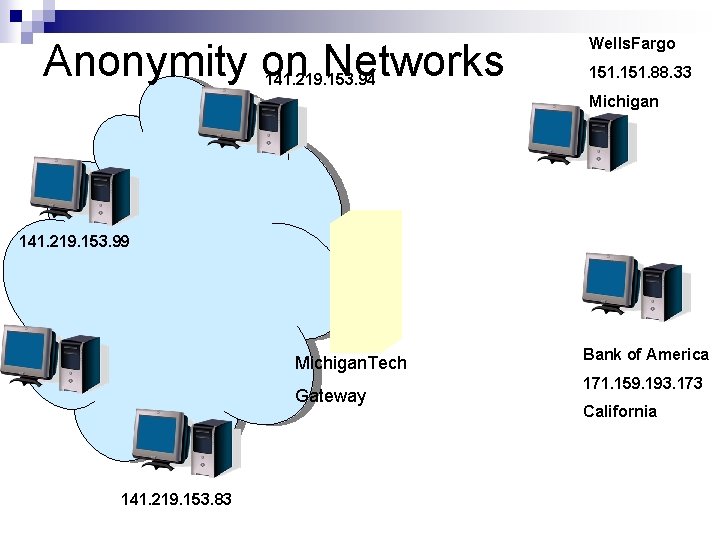
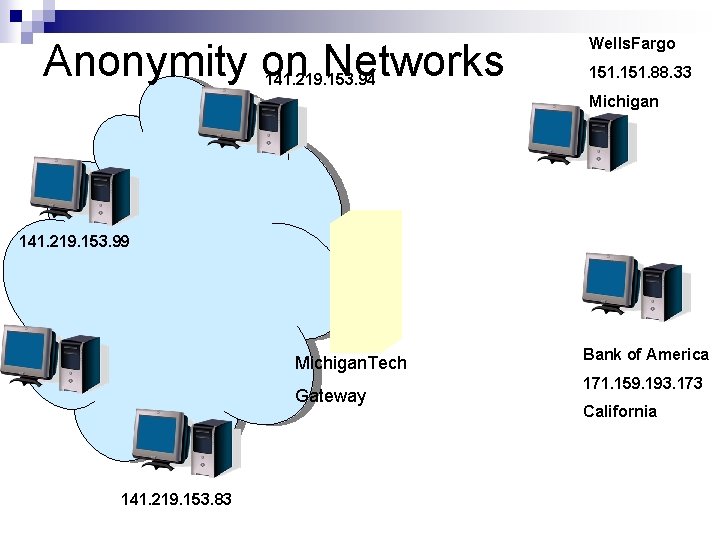
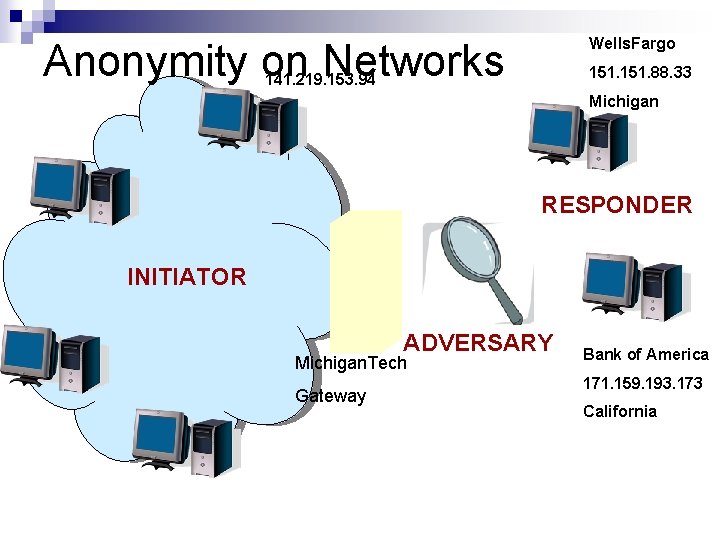
Anonymity on Networks 141. 219. 153. 94 Wells. Fargo 151. 88. 33 Michigan 141. 219. 153. 99 Michigan. Tech Gateway 141. 219. 153. 83 Bank of America 171. 159. 193. 173 California
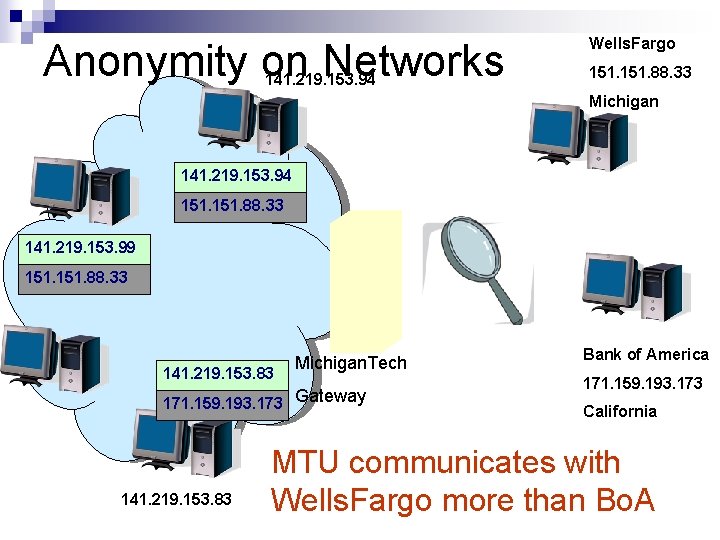
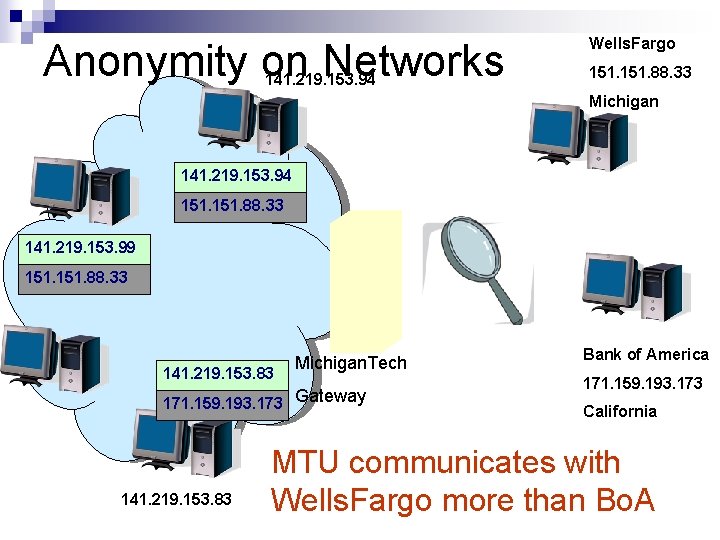
Anonymity on Networks 141. 219. 153. 94 Wells. Fargo 151. 88. 33 Michigan 141. 219. 153. 94 151. 88. 33 141. 219. 153. 99 151. 88. 33 141. 219. 153. 83 Michigan. Tech Gateway 151. 88. 33 171. 159. 193. 173 141. 219. 153. 83 Bank of America 171. 159. 193. 173 California MTU communicates with Wells. Fargo more than Bo. A
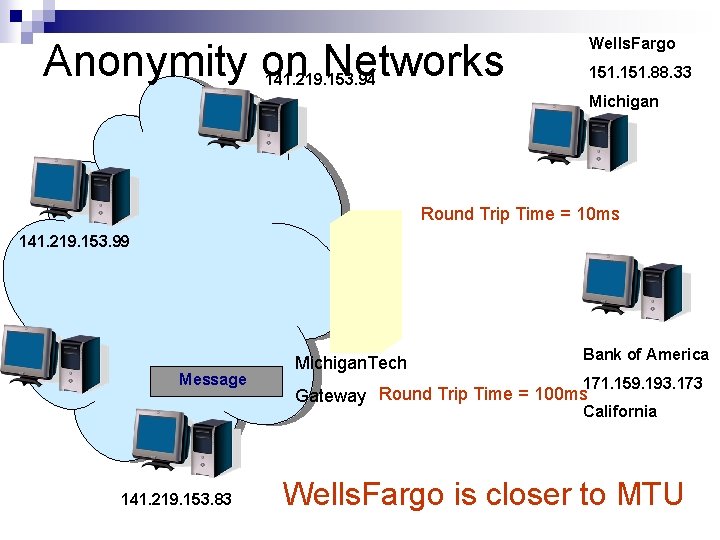
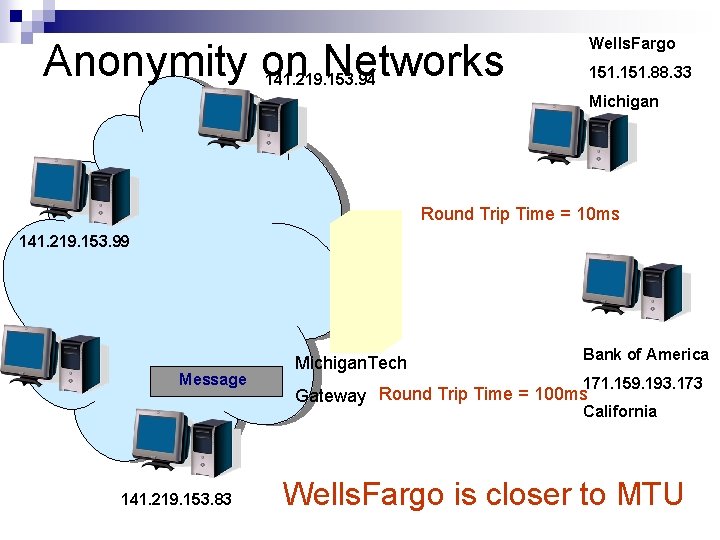
Wells. Fargo Anonymity on Networks 151. 88. 33 141. 219. 153. 94 Michigan Round Trip Time = 10 ms 141. 219. 153. 99 Message Michigan. Tech Bank of America 171. 159. 193. 173 Gateway Round Trip Time = 100 ms California 141. 219. 153. 83 Wells. Fargo is closer to MTU
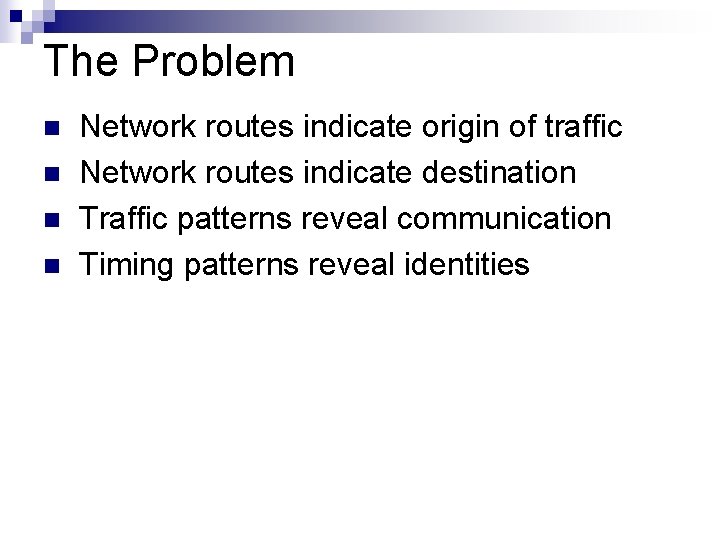
The Problem n n Network routes indicate origin of traffic Network routes indicate destination Traffic patterns reveal communication Timing patterns reveal identities
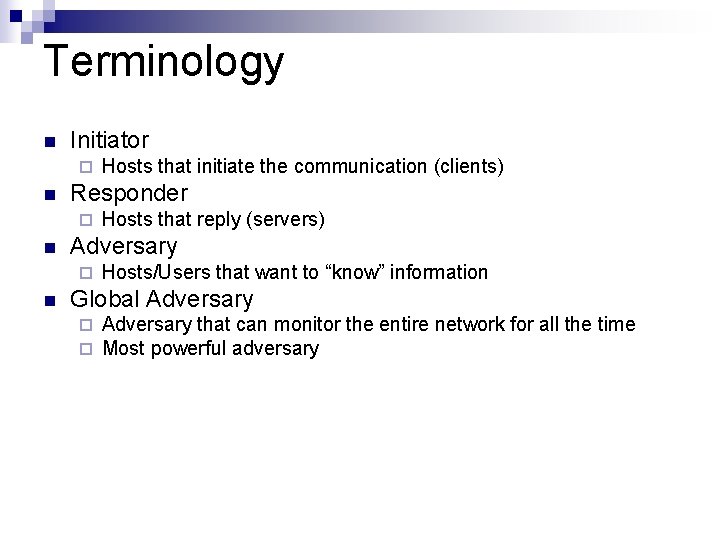
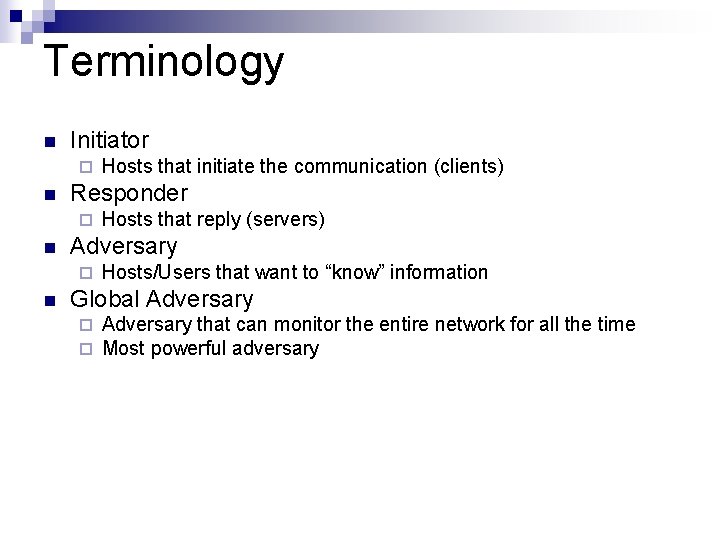
Terminology n Initiator ¨ n Responder ¨ n Hosts that reply (servers) Adversary ¨ n Hosts that initiate the communication (clients) Hosts/Users that want to “know” information Global Adversary ¨ ¨ Adversary that can monitor the entire network for all the time Most powerful adversary
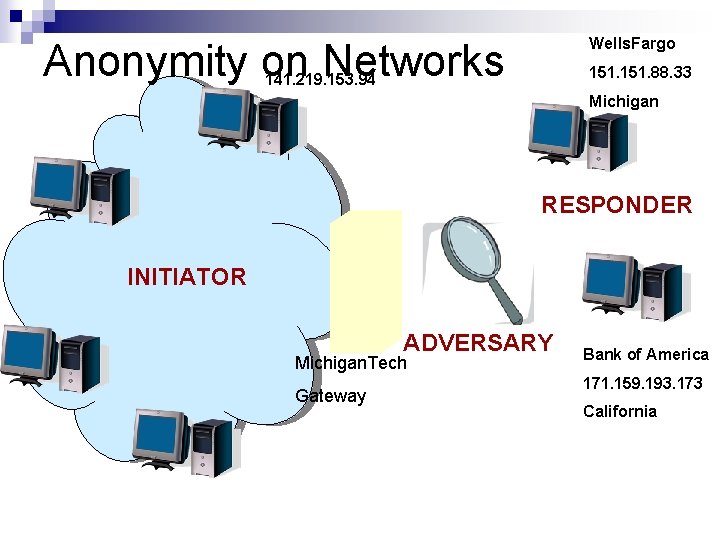
Wells. Fargo Anonymity on Networks 151. 88. 33 141. 219. 153. 94 Michigan RESPONDER INITIATOR ADVERSARY Michigan. Tech Gateway Bank of America 171. 159. 193. 173 California
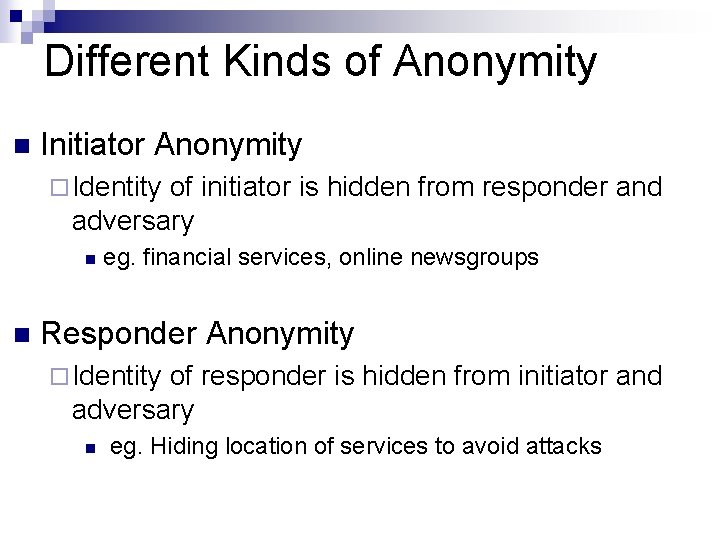
Different Kinds of Anonymity n Initiator Anonymity ¨ Identity of initiator is hidden from responder and adversary n n eg. financial services, online newsgroups Responder Anonymity ¨ Identity of responder is hidden from initiator and adversary n eg. Hiding location of services to avoid attacks
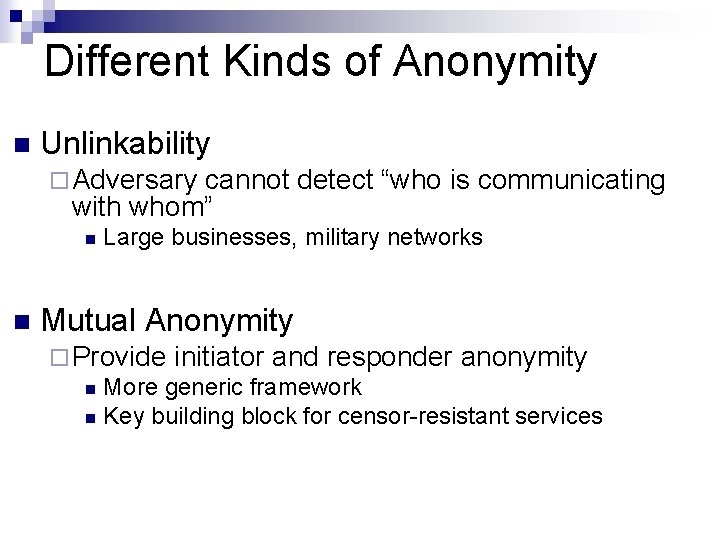
Different Kinds of Anonymity n Unlinkability ¨ Adversary cannot detect “who is communicating with whom” n n Large businesses, military networks Mutual Anonymity ¨ Provide initiator and responder anonymity n More generic framework n Key building block for censor-resistant services
Anonymity Mechanisms n Main categories ¨ Anonymity by Mixes ¨ Anonymity by Proxy ¨ Anonymity by Single-Path Forwarding ¨ Anonymity by Group Communication
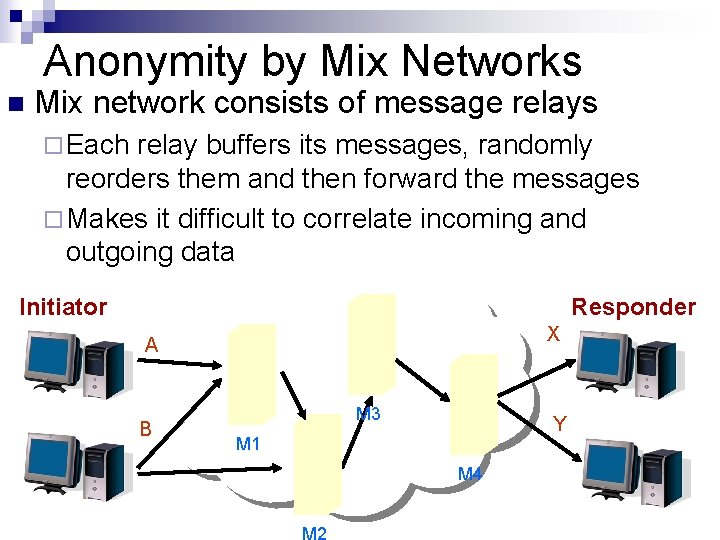
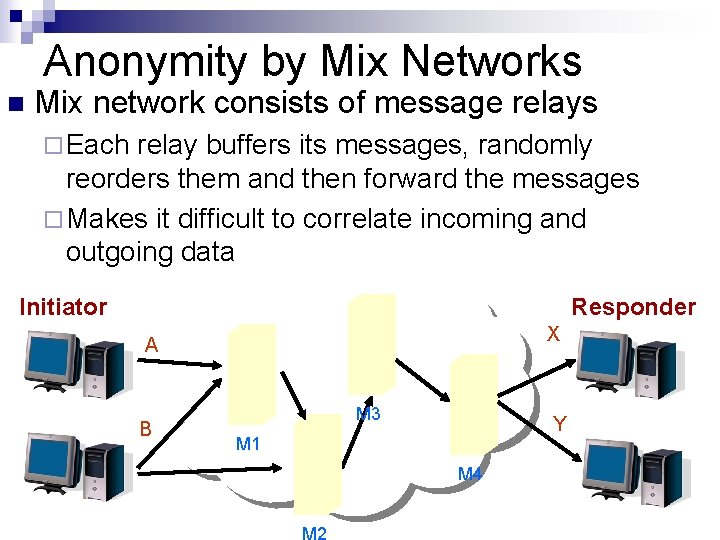
Anonymity by Mix Networks n Mix network consists of message relays ¨ Each relay buffers its messages, randomly reorders them and then forward the messages ¨ Makes it difficult to correlate incoming and outgoing data Initiator Responder X A B M 3 Y M 1 M 4 M 2
Anonymity by Mix Networks n Strong anonymity guarantees. ¨ Withstand global adversaries. Unbounded latencies due to buffering and random delaying n Eg. Mix. Net, Babel and Mixminion n
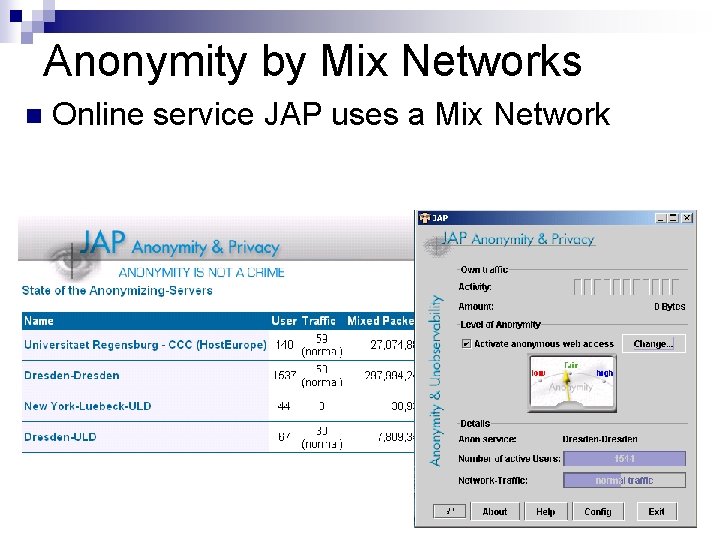
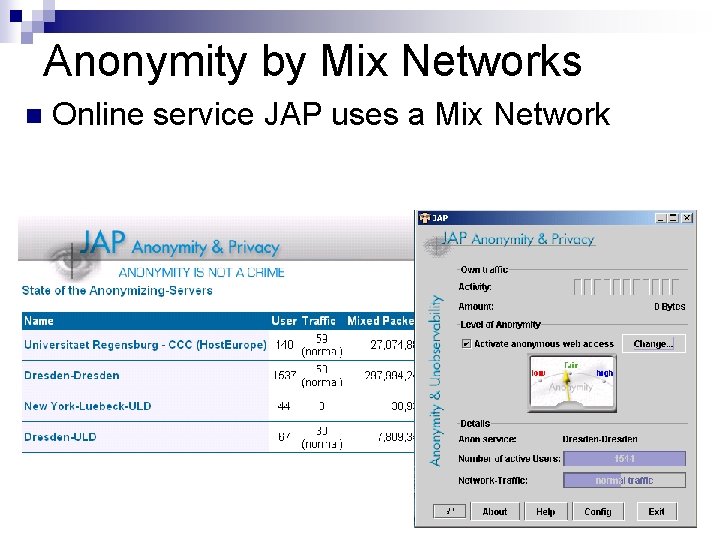
Anonymity by Mix Networks n Online service JAP uses a Mix Network
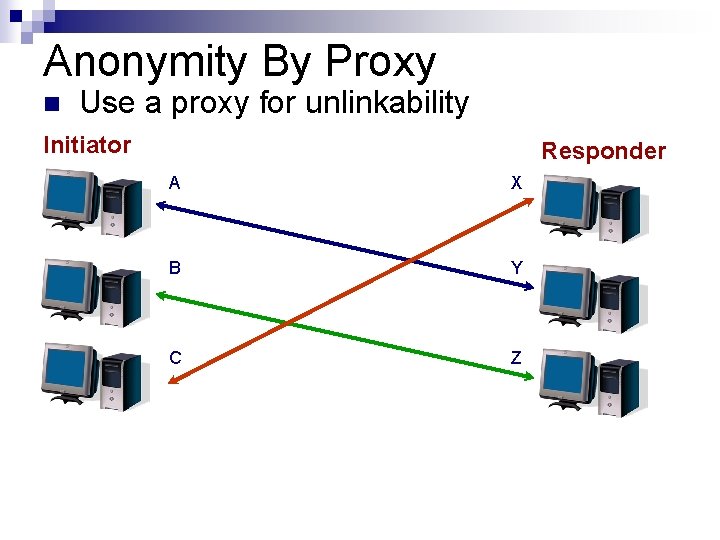
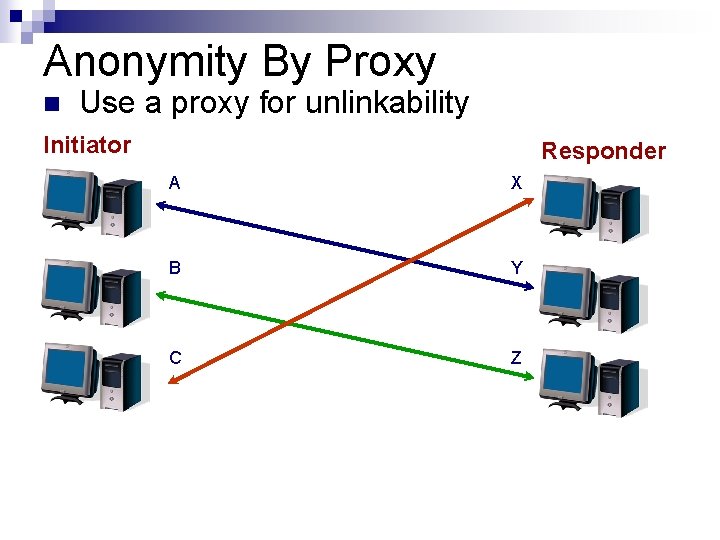
Anonymity By Proxy n Use a proxy for unlinkability Initiator Responder A X B Y C Z
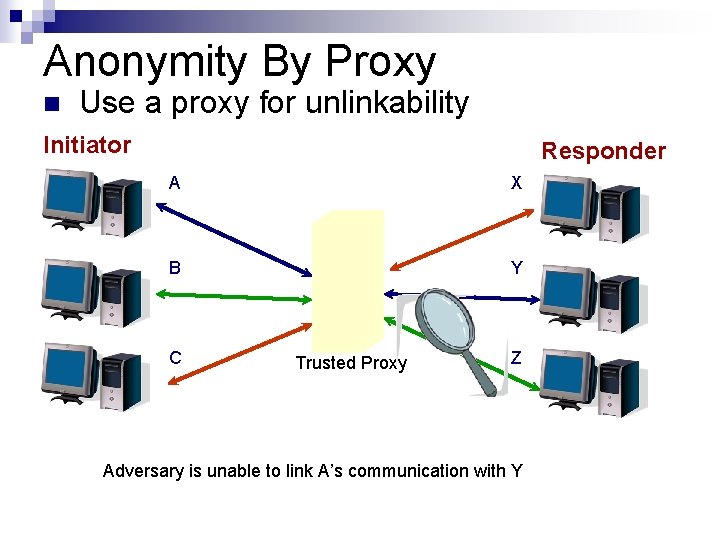
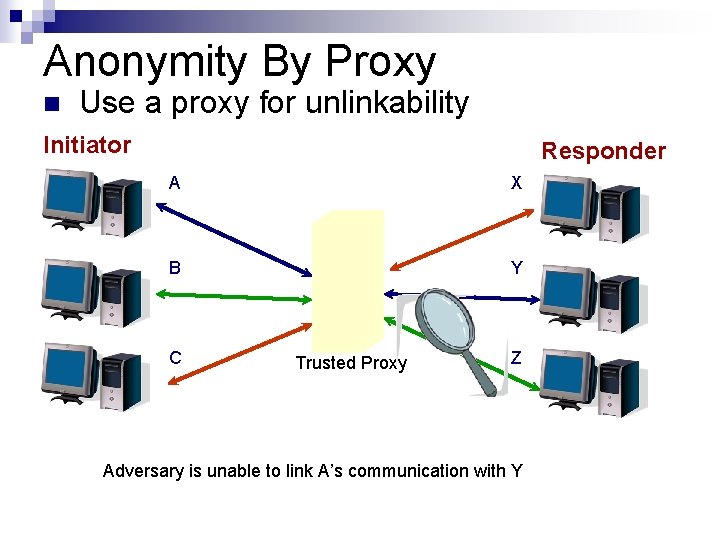
Anonymity By Proxy n Use a proxy for unlinkability Initiator Responder A X B Y C Trusted Proxy Z Adversary is unable to link A’s communication with Y
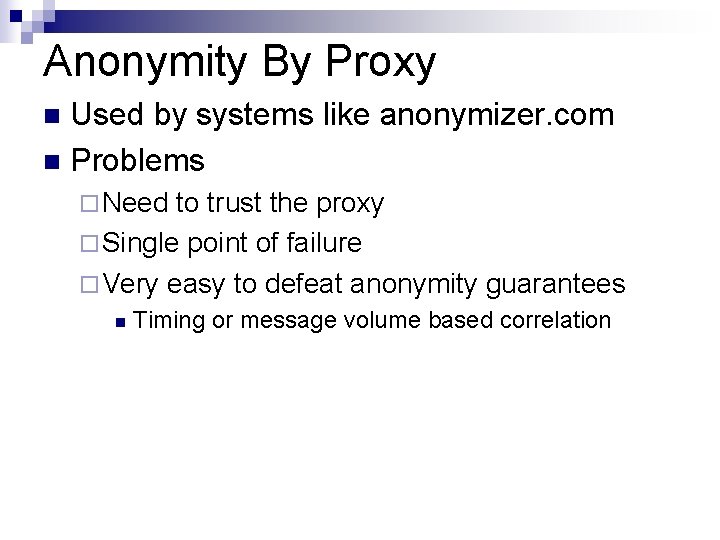
Anonymity By Proxy Used by systems like anonymizer. com n Problems n ¨ Need to trust the proxy ¨ Single point of failure ¨ Very easy to defeat anonymity guarantees n Timing or message volume based correlation
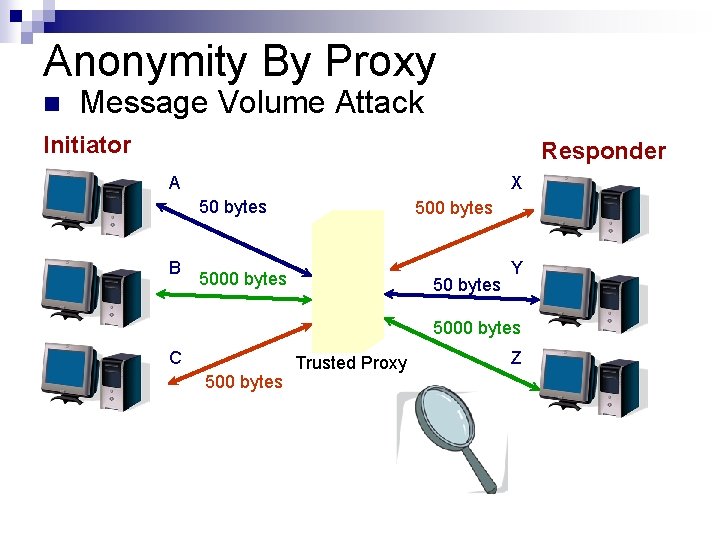
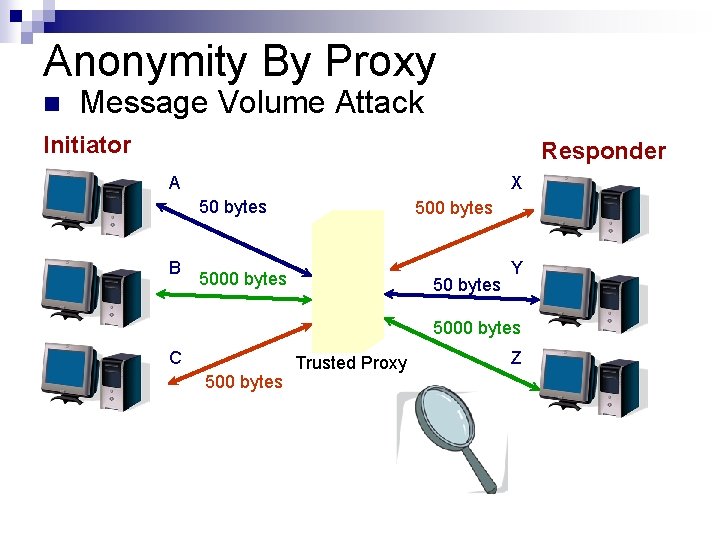
Anonymity By Proxy n Message Volume Attack Initiator Responder A X 50 bytes B 500 bytes 50 bytes Y 5000 bytes C 500 bytes Trusted Proxy Z
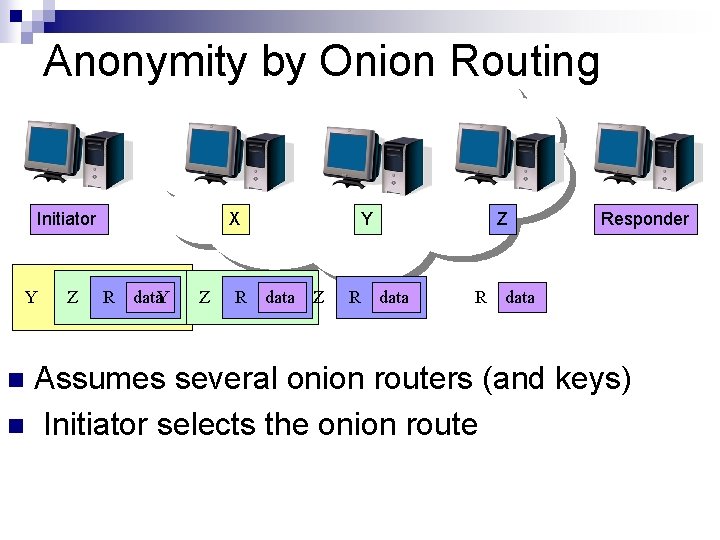
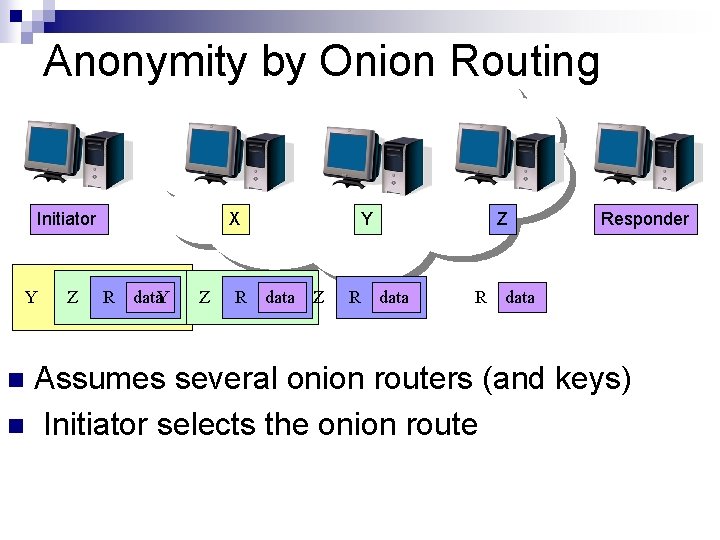
Anonymity by Onion Routing Initiator Y Z X R data. Y Z R Y data Z R Z data R Responder data Assumes several onion routers (and keys) n Initiator selects the onion route n
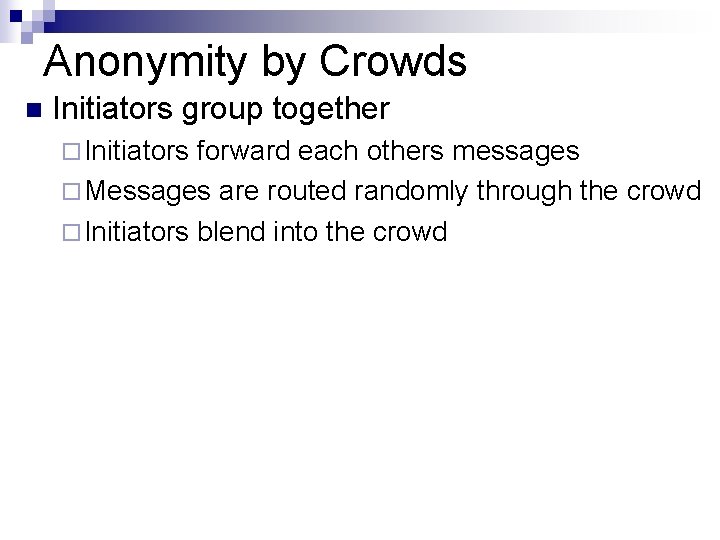
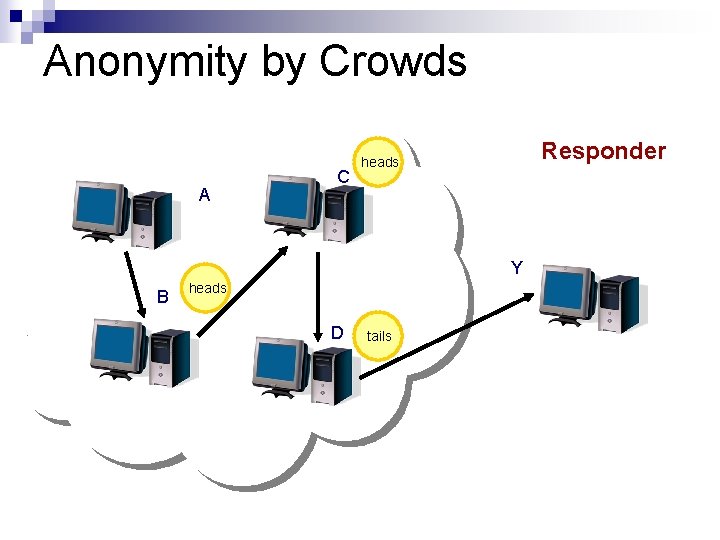
Anonymity by Crowds n Initiators group together ¨ Initiators forward each others messages ¨ Messages are routed randomly through the crowd ¨ Initiators blend into the crowd
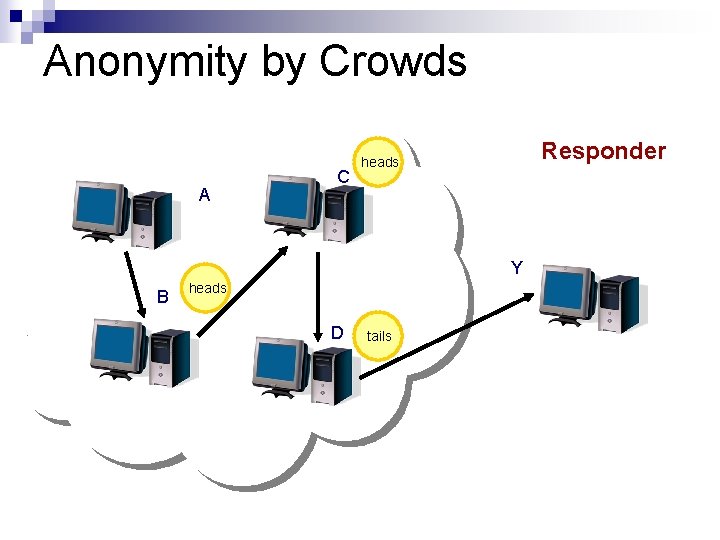
Anonymity by Crowds A C Responder heads Y B heads D tails
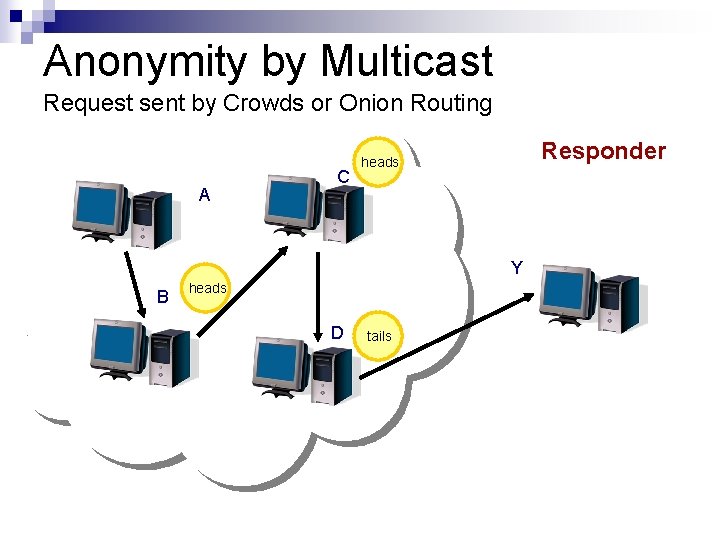
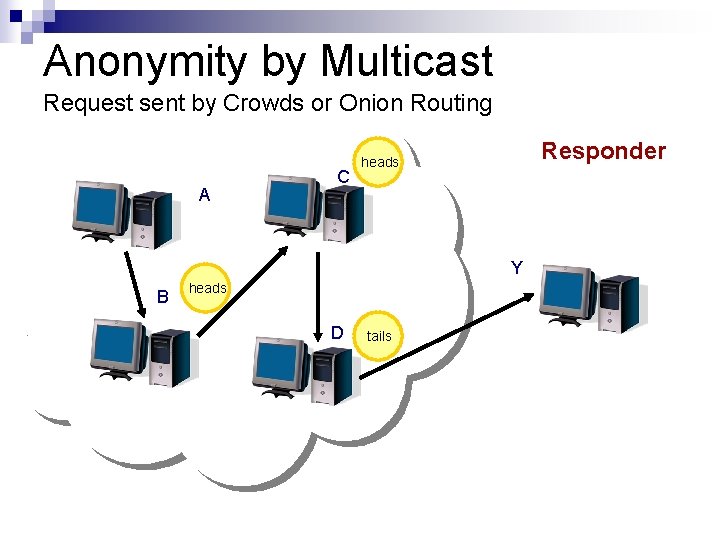
Anonymity by Multicast Request sent by Crowds or Onion Routing A C Responder heads Y B heads D tails
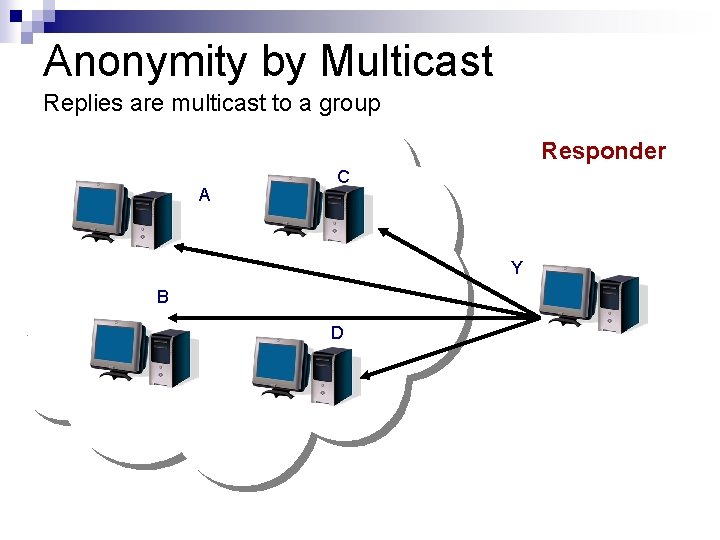
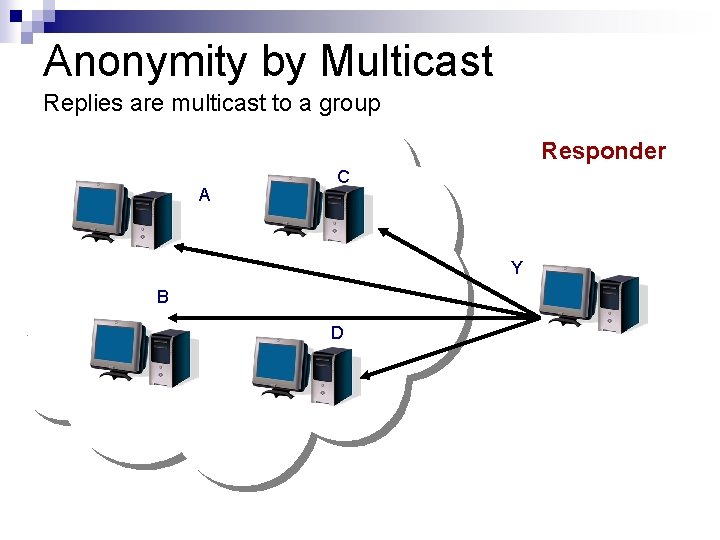
Anonymity by Multicast Replies are multicast to a group Responder A C Y B D
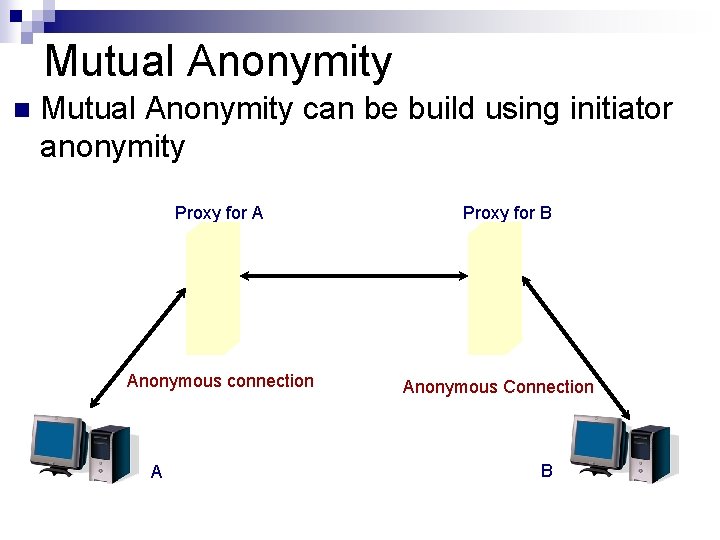
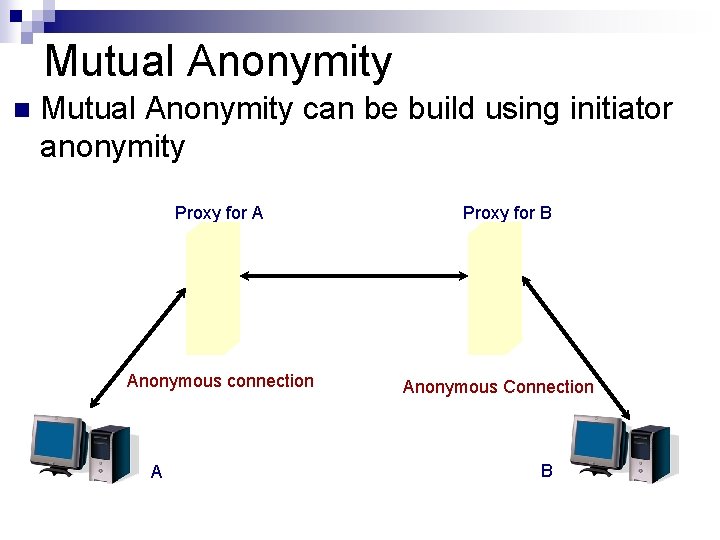
Mutual Anonymity n Mutual Anonymity can be build using initiator anonymity Proxy for A Anonymous connection A Proxy for B Anonymous Connection B
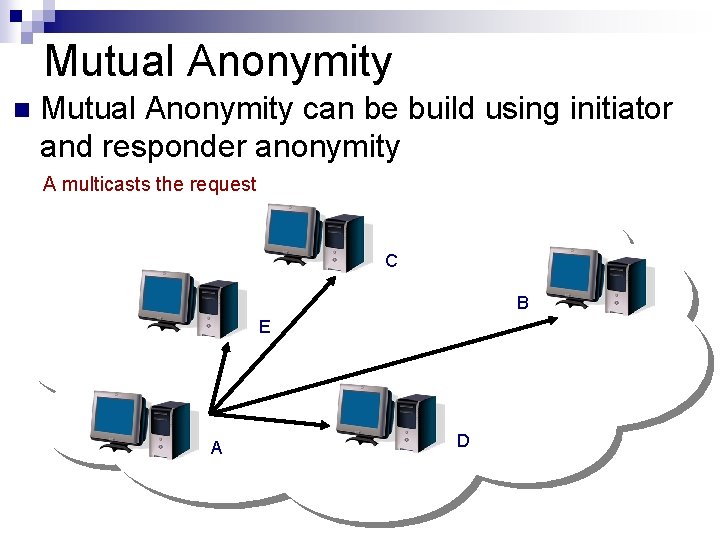
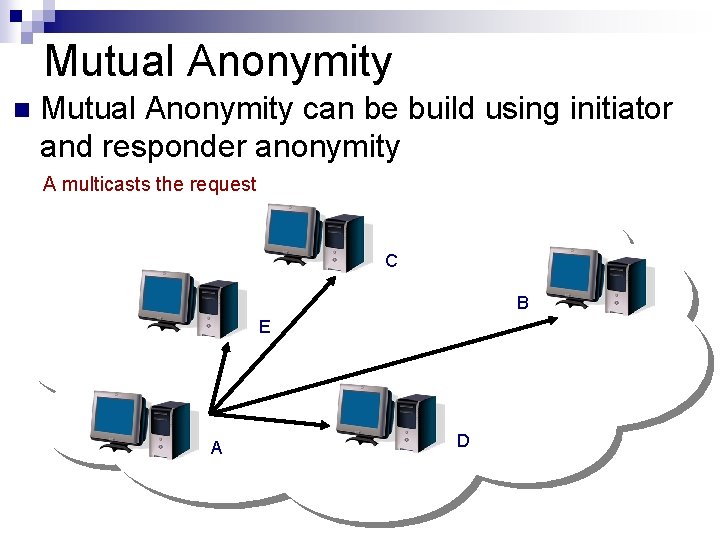
Mutual Anonymity n Mutual Anonymity can be build using initiator and responder anonymity A multicasts the request C B E A D
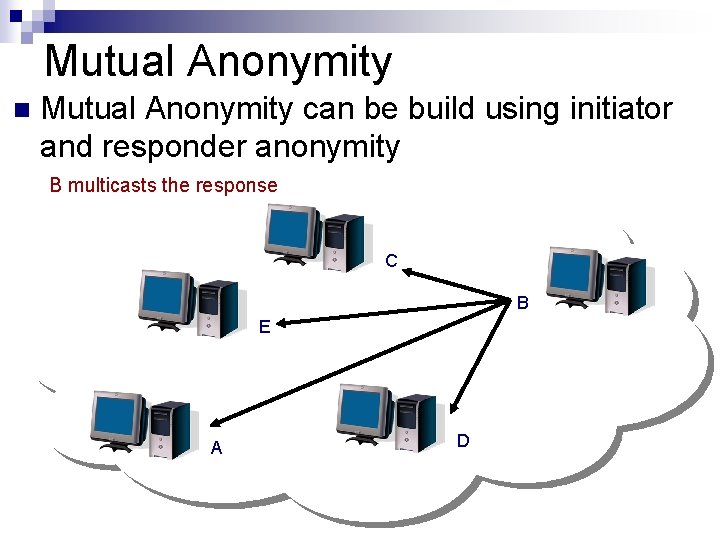
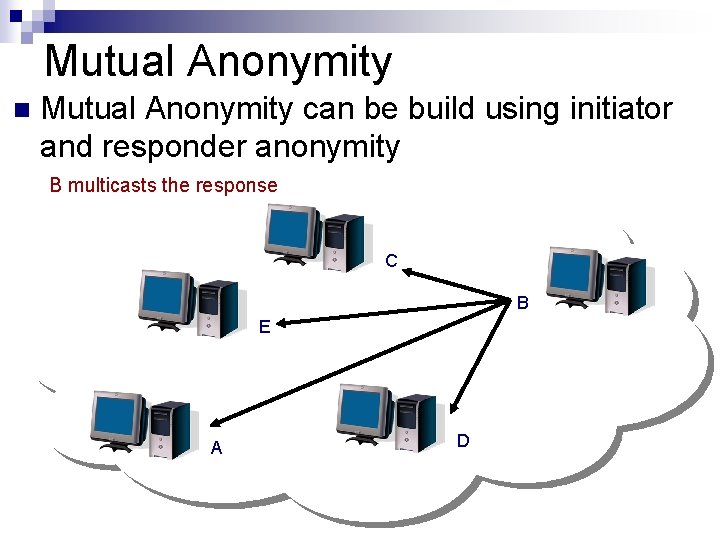
Mutual Anonymity n Mutual Anonymity can be build using initiator and responder anonymity B multicasts the response C B E A D
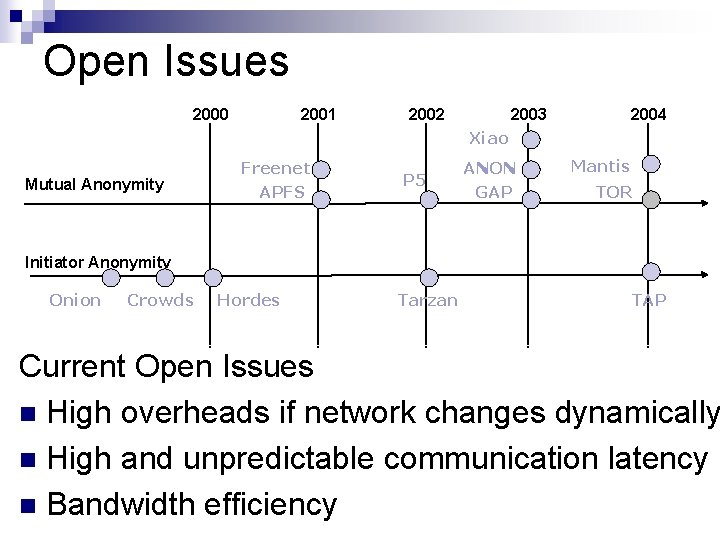
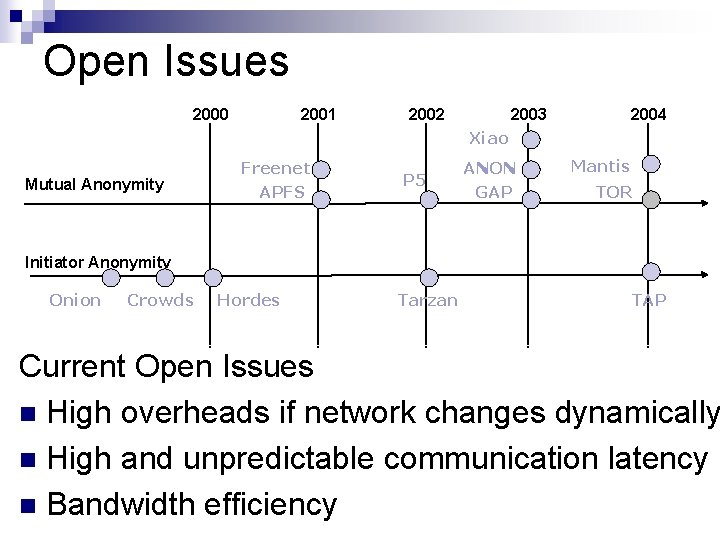
Open Issues 2000 2001 2002 2003 2004 Xiao Mutual Anonymity Freenet APFS P 5 ANON GAP Mantis TOR Initiator Anonymity Onion Crowds Hordes Tarzan TAP Current Open Issues n High overheads if network changes dynamically n High and unpredictable communication latency n Bandwidth efficiency
Mutual Anonymity in P 2 P Networks Joint work with: Ashish Malgi, Dr. Byung Choi, Dr. Jean Mayo
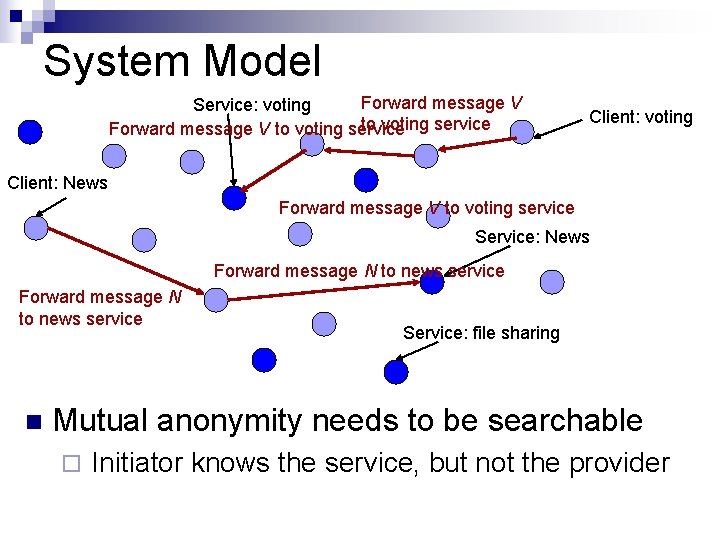
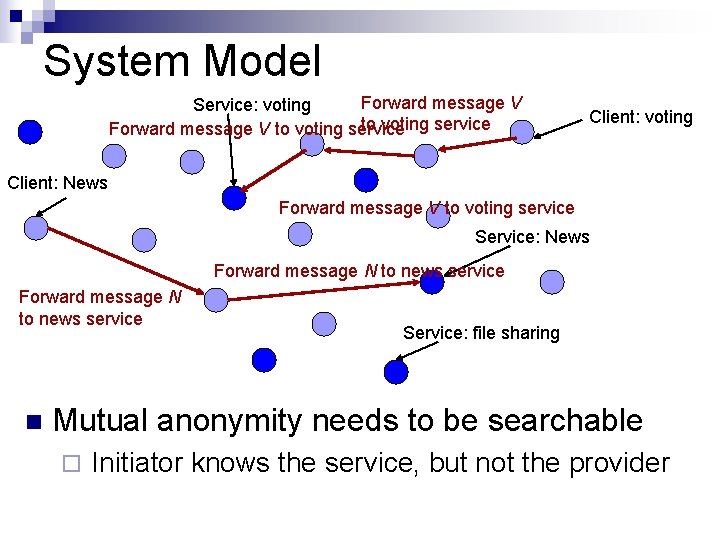
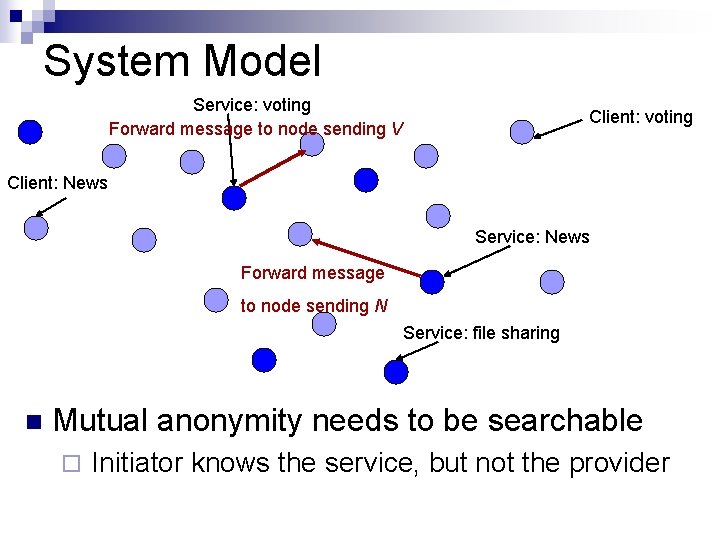
System Model Forward message V Service: voting to voting service Forward message V to voting service Client: voting Client: News Forward message V to voting service Service: News Forward message N to news service n Service: file sharing Mutual anonymity needs to be searchable ¨ Initiator knows the service, but not the provider
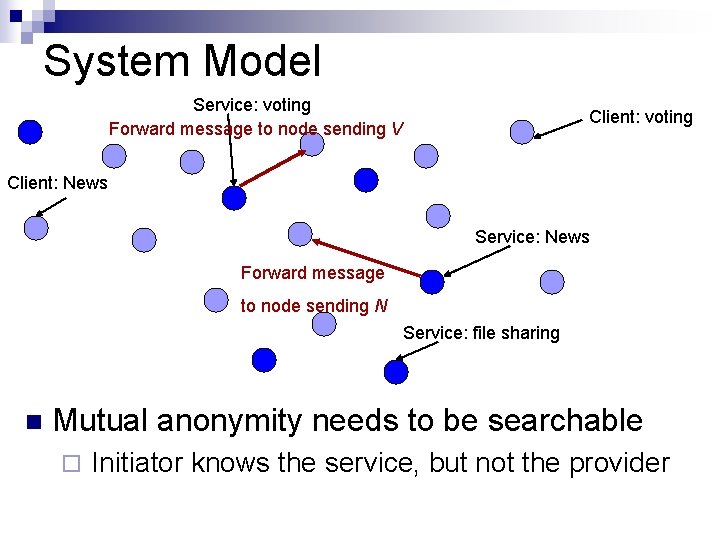
System Model Service: voting Forward message to node sending V Client: voting Client: News Service: News Forward message to node sending N Service: file sharing n Mutual anonymity needs to be searchable ¨ Initiator knows the service, but not the provider
Goals of the Protocol (Mu. ON) 1. 2. 3. 4. 5. Mutual anonymity and unlinkability Low communication overhead Scale with increasing overlay size and churn High reliability Bounded latency
Design Decision n Use of Multicasting ¨ Provides mutual anonymity ¨ Tolerates peer dynamics ¨ Short latencies ¨ Since many nodes get the message, any one of them could be the initiator/responder n Overheads in multicast ¨ High because so many nodes get the message ¨ Consumes bandwidth and computational resources
Basic Principle n A header is generated for each message ¨ size of header much less than size of message ¨ Headers contain signed checksums for integrity ¨ Messages are encrypted for confidentiality n Dissemination of data ¨ Headers are disseminated to all N nodes ¨ Messages are disseminated to p*N nodes (0 < p < 1) ¨ p is a protocol parameter, tradeoff between anonymity and performance n Based on a class of protocols called epidemic protocols
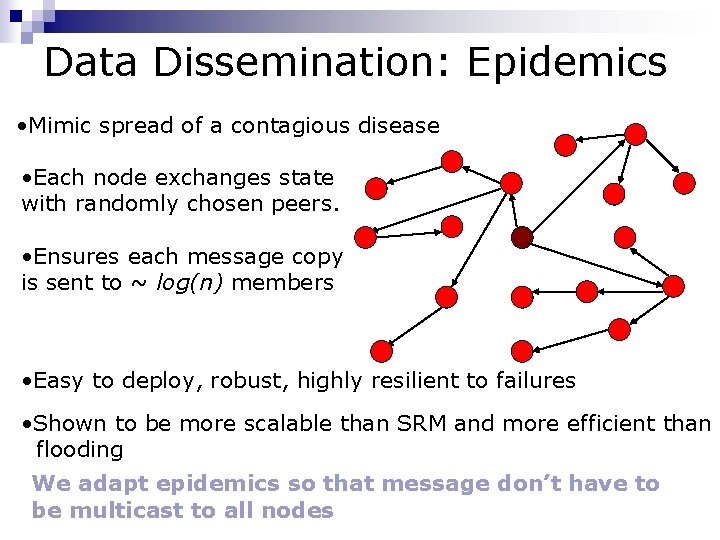
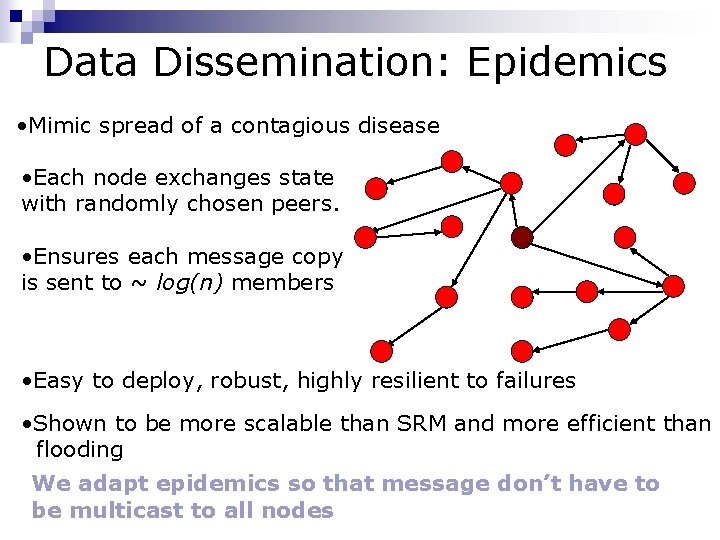
Data Dissemination: Epidemics • Mimic spread of a contagious disease • Each node exchanges state with randomly chosen peers. • Ensures each message copy is sent to ~ log(n) members • Easy to deploy, robust, highly resilient to failures • Shown to be more scalable than SRM and more efficient than flooding We adapt epidemics so that message don’t have to be multicast to all nodes
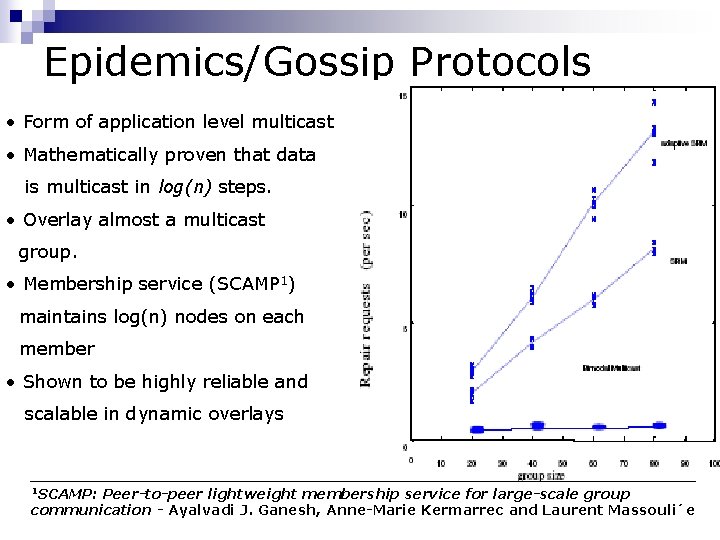
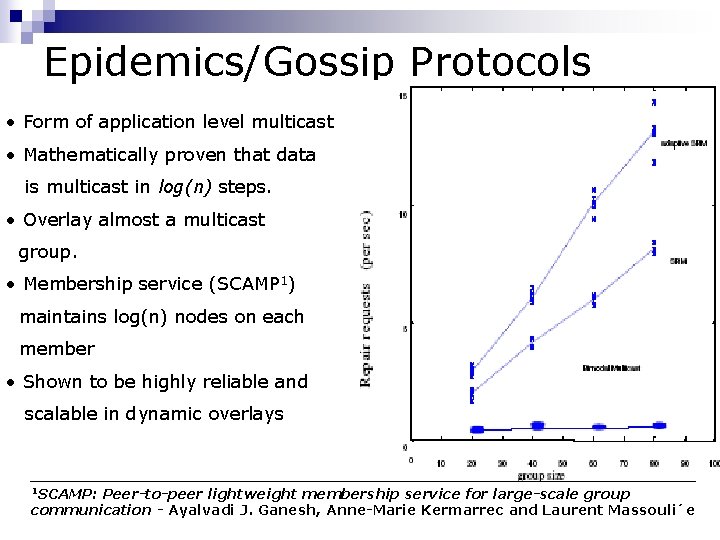
Epidemics/Gossip Protocols • Form of application level multicast • Mathematically proven that data is multicast in log(n) steps. • Overlay almost a multicast group. • Membership service (SCAMP 1) maintains log(n) nodes on each member • Shown to be highly reliable and scalable in dynamic overlays 1 SCAMP: Peer-to-peer lightweight membership service for large-scale group communication - Ayalvadi J. Ganesh, Anne-Marie Kermarrec and Laurent Massouli´e
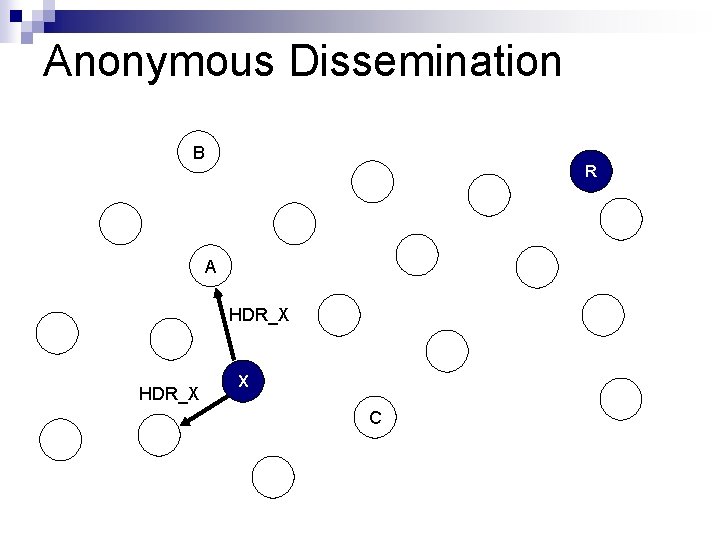
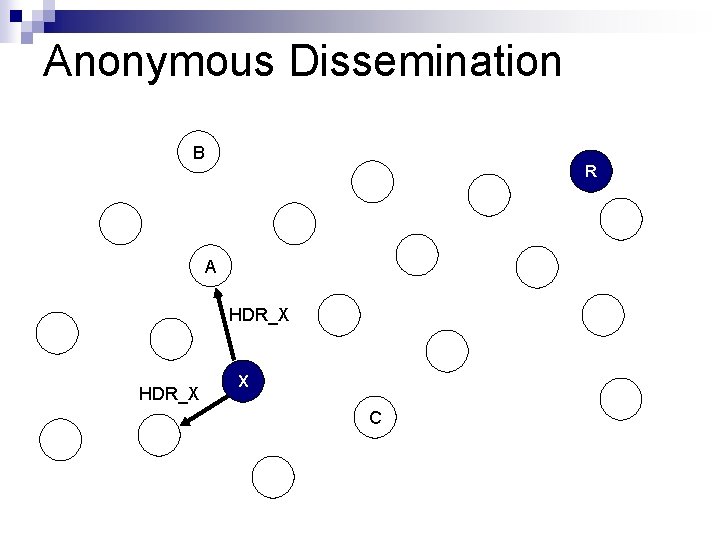
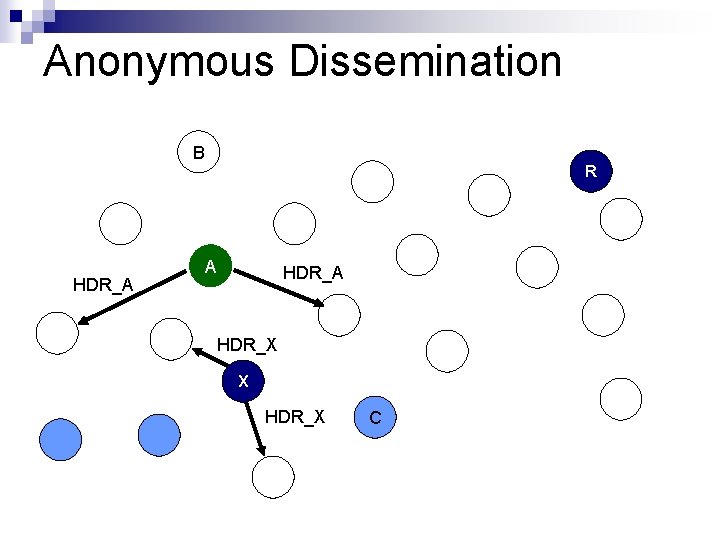
Anonymous Dissemination B R A HDR_X X C
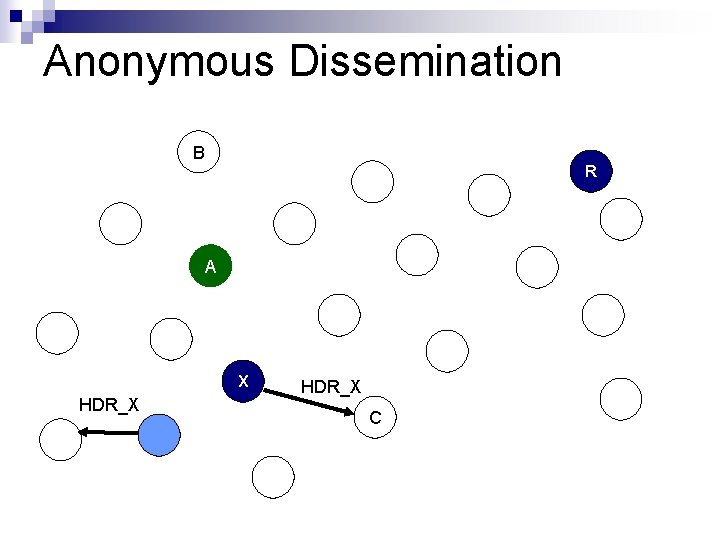
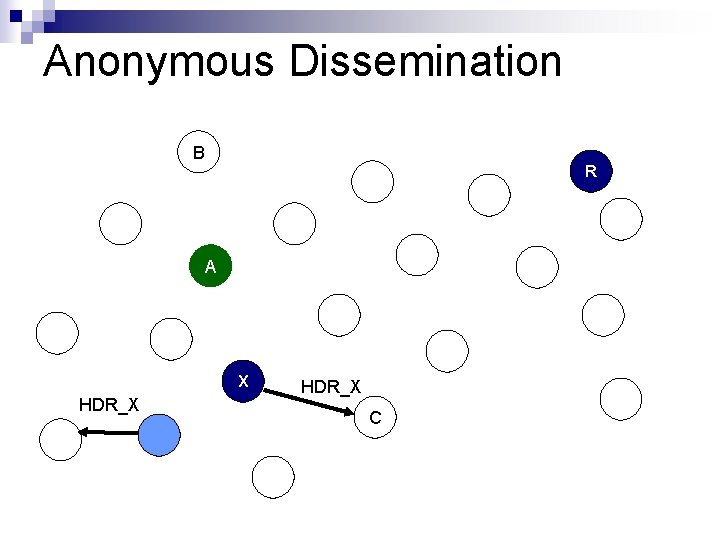
Anonymous Dissemination B R A X HDR_X C
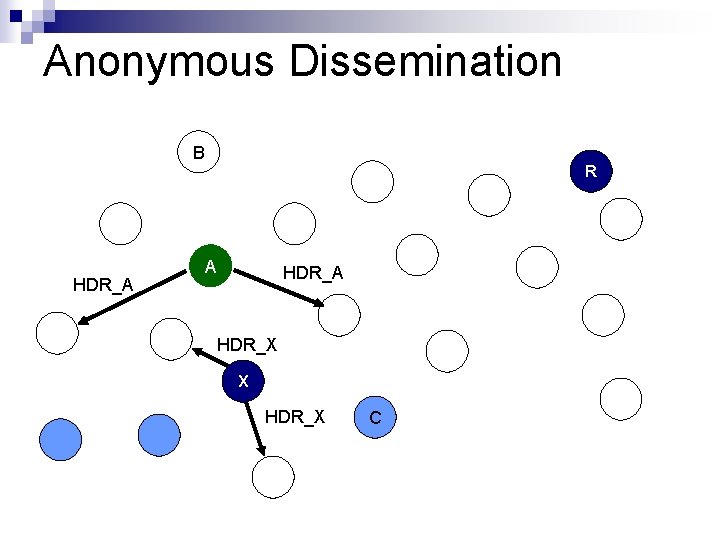
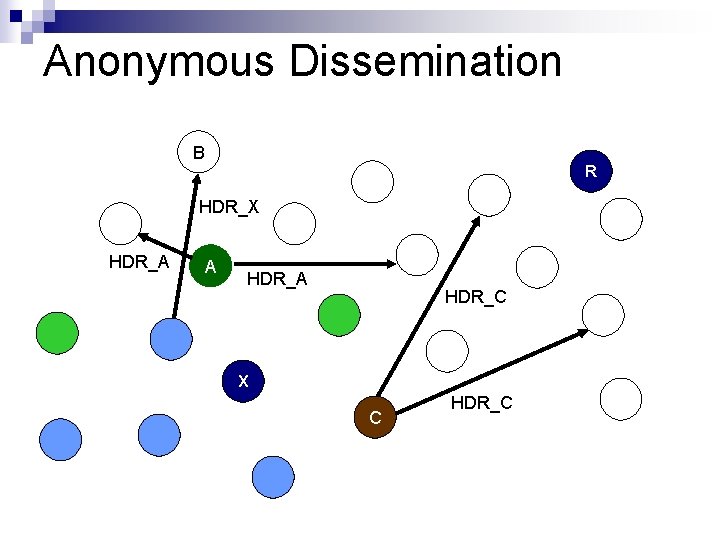
Anonymous Dissemination B R HDR_A A HDR_X X HDR_X C
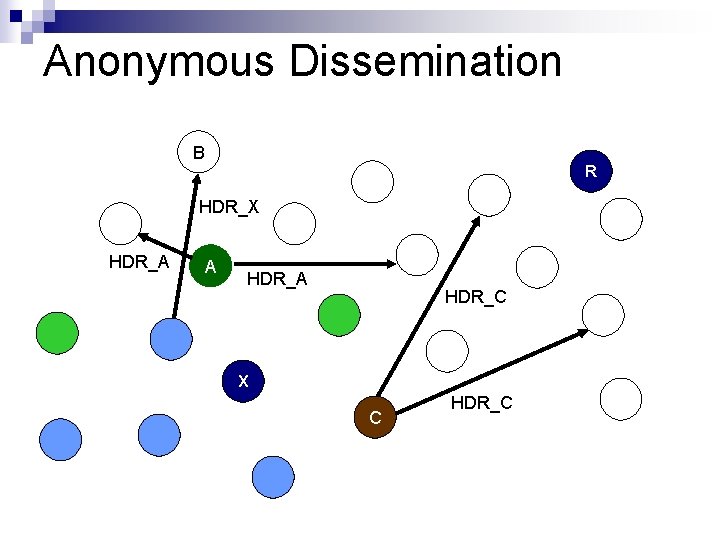
Anonymous Dissemination B R HDR_X HDR_A A HDR_C X C HDR_C
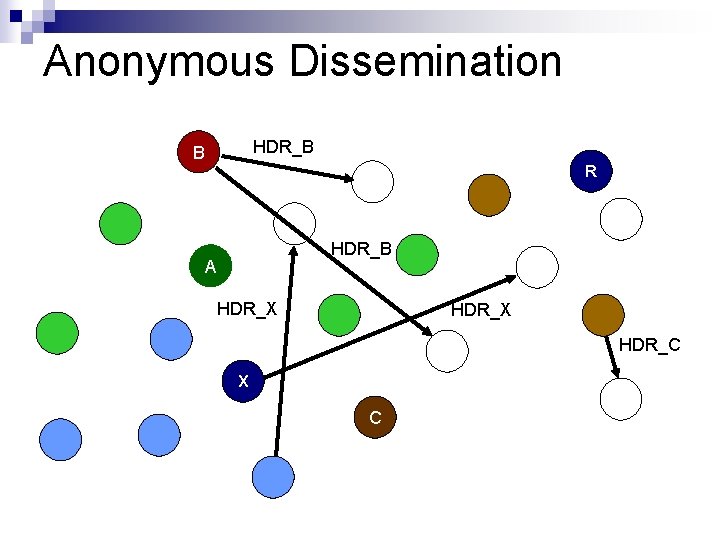
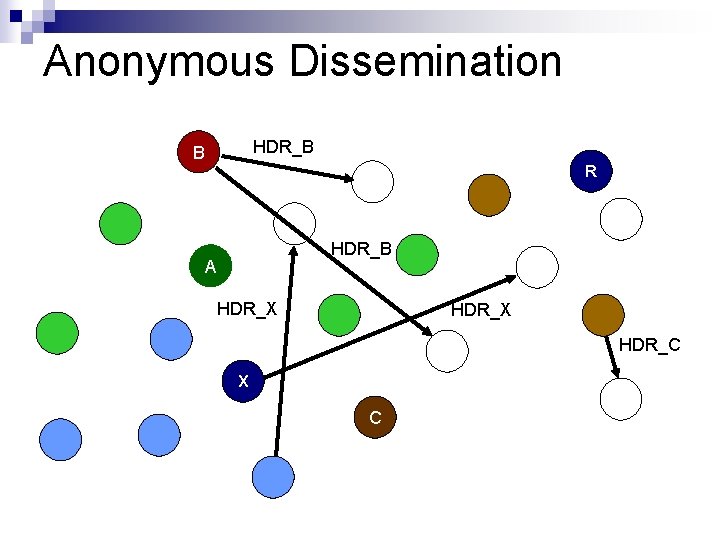
Anonymous Dissemination HDR_B B R HDR_B A HDR_X HDR_C X C
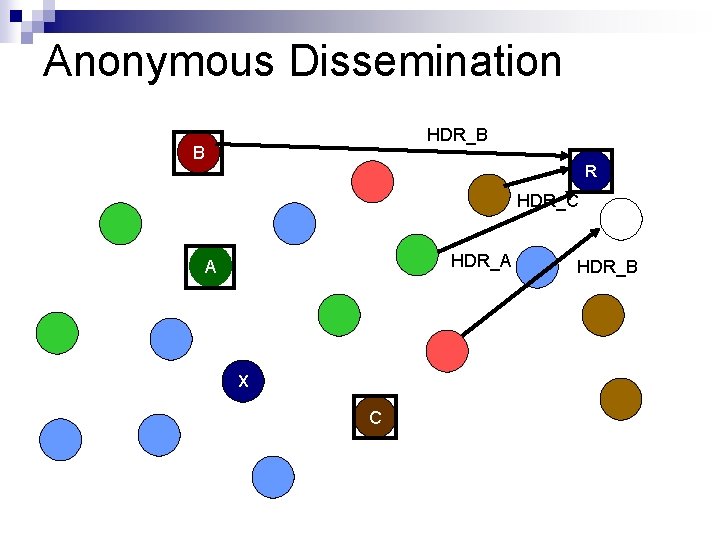
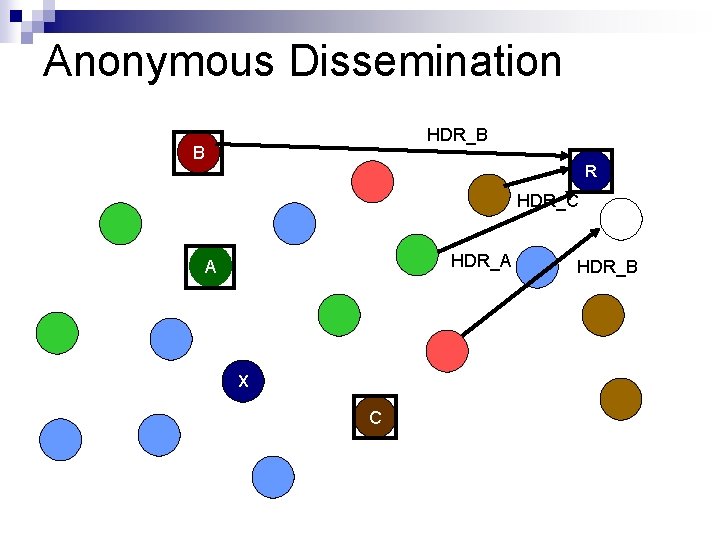
Anonymous Dissemination HDR_B B R HDR_C HDR_A A X C HDR_B
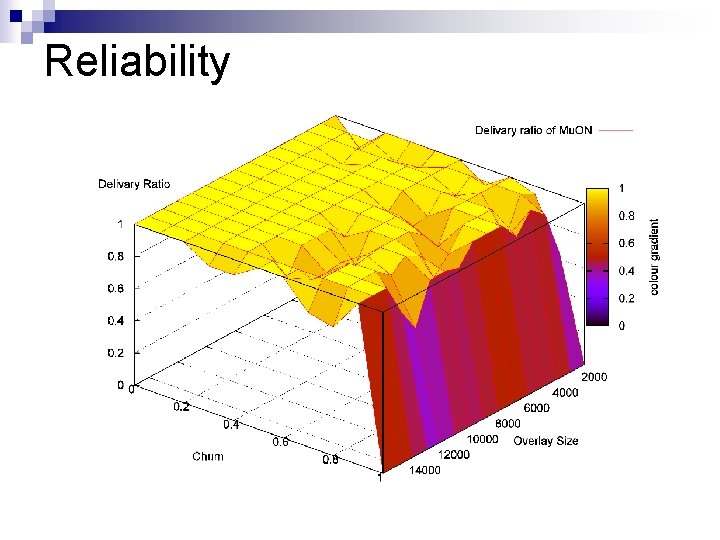
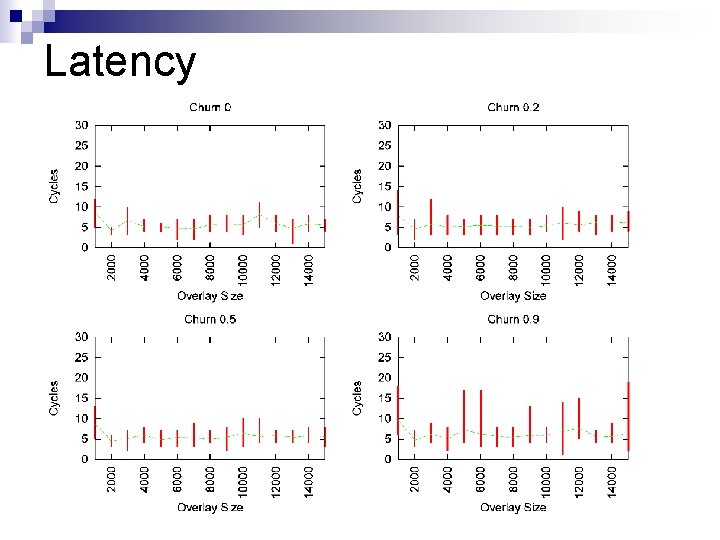
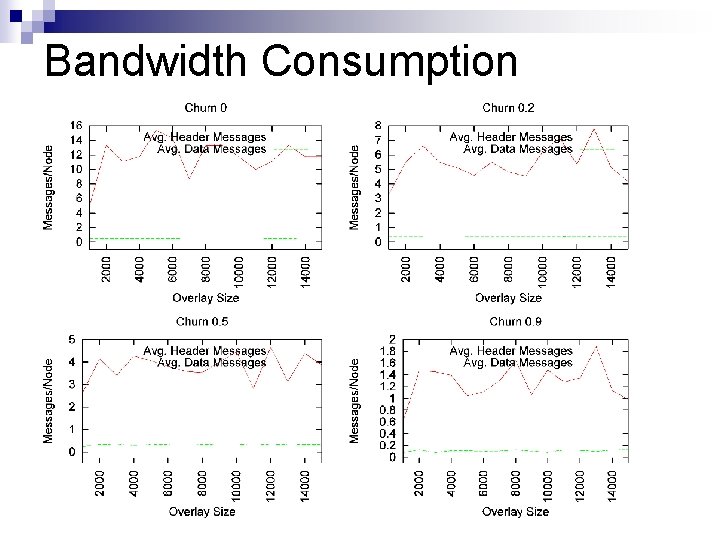
Performance Evaluation n Study the protocol for large networks ¨ Performance n metrics should scale well Study protocol for dynamic networks ¨ Performance metrics should be sustained for varying degrees of network disturbance
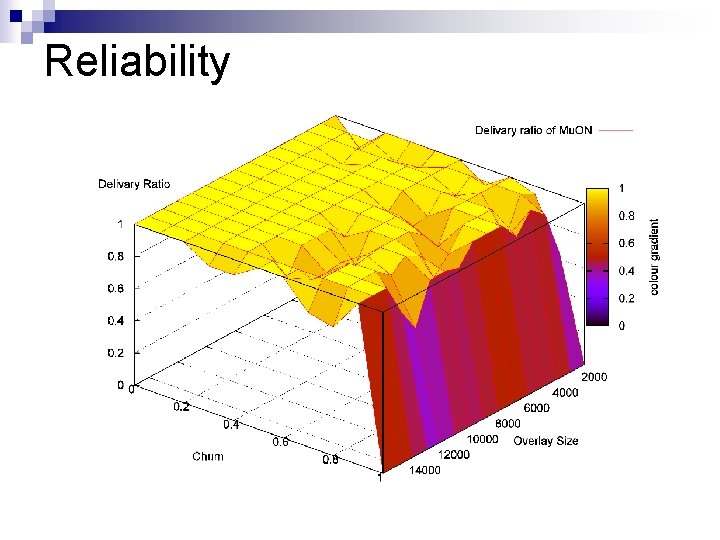
Reliability
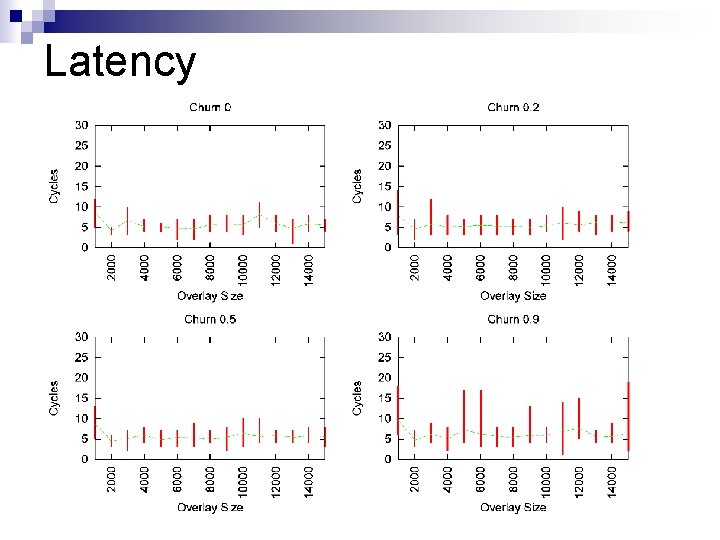
Latency
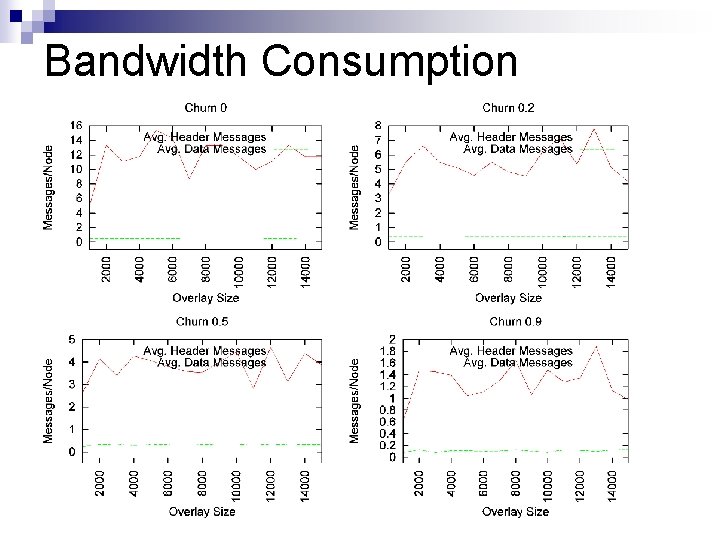
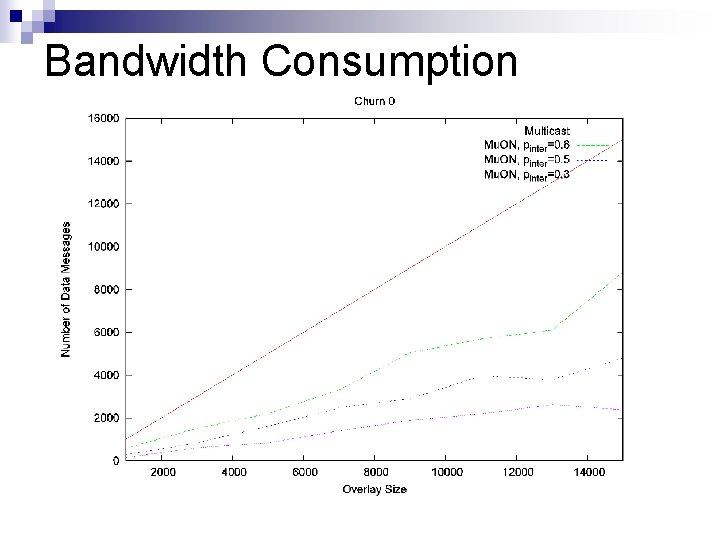
Bandwidth Consumption
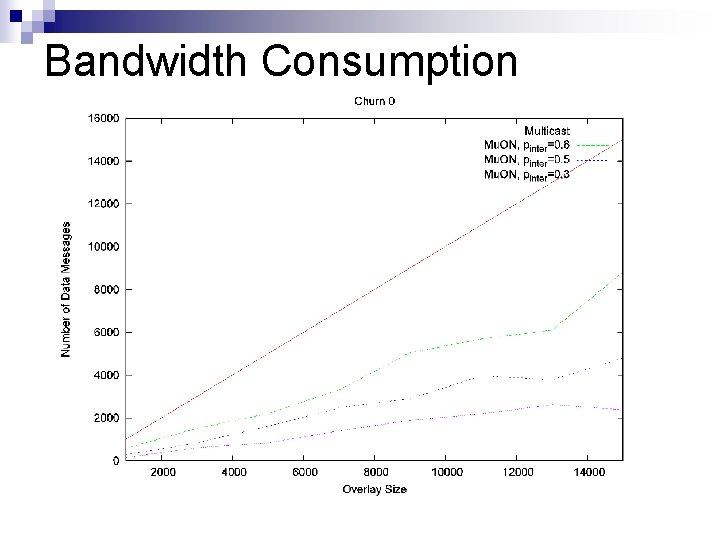
Bandwidth Consumption
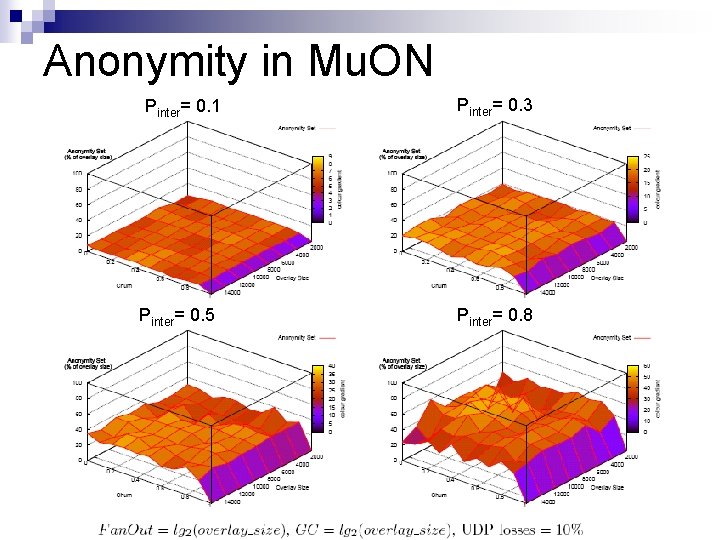
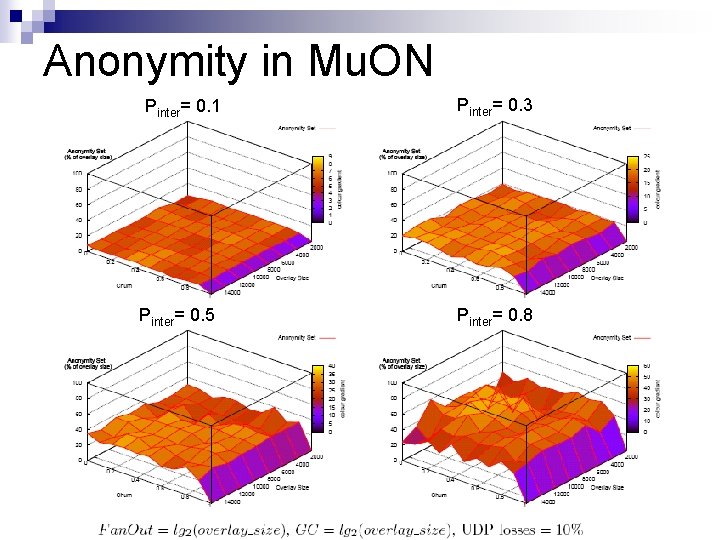
Anonymity in Mu. ON Pinter= 0. 1 Pinter= 0. 5 Pinter= 0. 3 Pinter= 0. 8
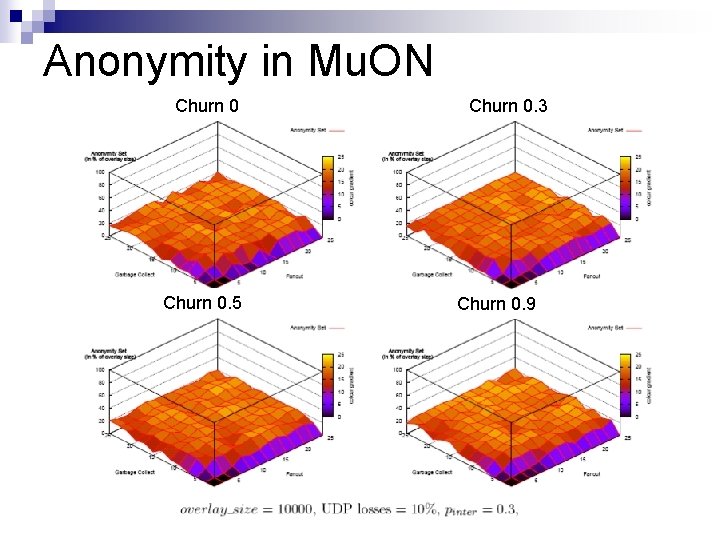
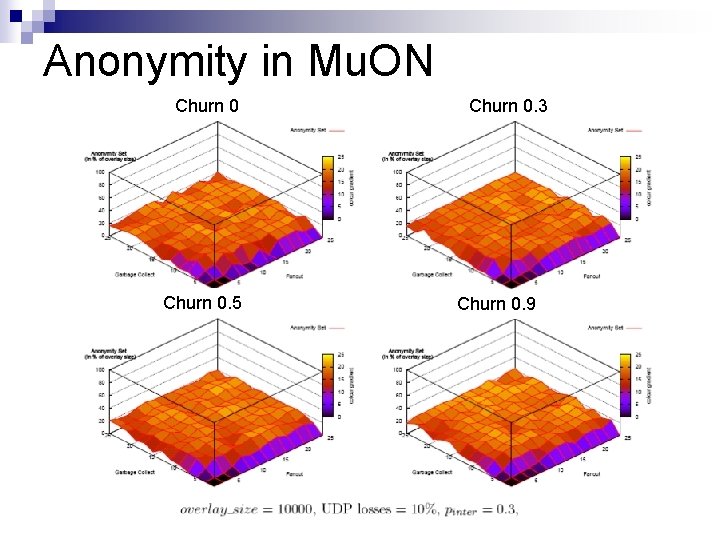
Anonymity in Mu. ON Churn 0. 5 Churn 0. 3 Churn 0. 9
Anonymity in Mu. ON n n Analysis indicates that Mu. ON provides anonymity under most known forms of attacks Mu. ON cannot tolerate a global adversary
Conclusion n Overview of approaches for anonymity ¨ Proxy, random forwarding, onion routing, mix networks and multicasting ¨ Open issues were dynamic networks, low overheads and latency n Contributions of our protocol (Mu. ON) ¨ Searchable mutual anonymity ¨ Low overheads and latency ¨ Performance scales well with large overlay