Chapter 10 Intro to Routing Switching Upon completion


- Slides: 41

Chapter 10 Intro to Routing & Switching
� Upon completion of this chapter, you should be able to: � Explain how the functions of the application layer, session layer, and presentation layer work together to provide network services to end user applications. � Describe how common application layer protocols interact with end user applications. � Describe common application layer protocols that provide Internet services to end-users, including WWW services and email. � Describe application layer protocols that provide IP addressing services, including DNS and DHCP. � Describe the features and operation of well-known application layer protocols that allow for file sharing services. � Explain how data is moved across the network, from opening an application to receiving data.
10. 1
� Provides the interface between the applications we use to communicate & the network � Used to exchange data between source & destination � What are some of the application layer protocols?
� Formats data so it can be read � Compress/decompress data � Encrypt/decrypt data � MPEG, JPG, GIF
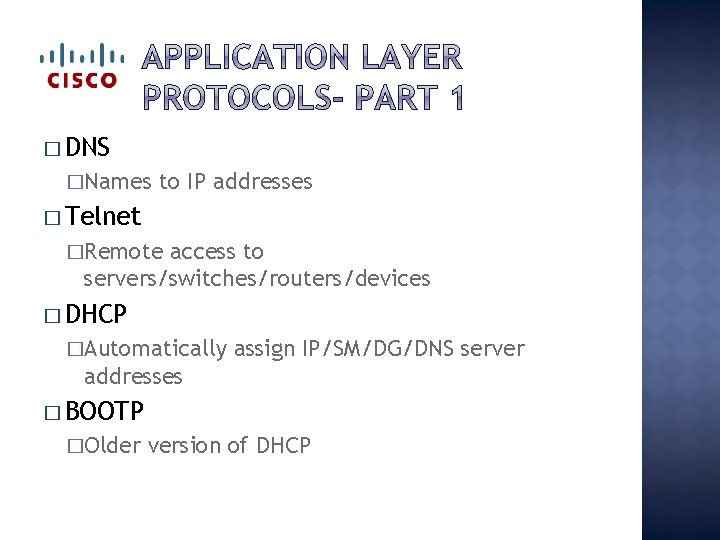
� DNS �Names to IP addresses � Telnet �Remote access to servers/switches/routers/devices � DHCP �Automatically assign IP/SM/DG/DNS server addresses � BOOTP �Older version of DHCP
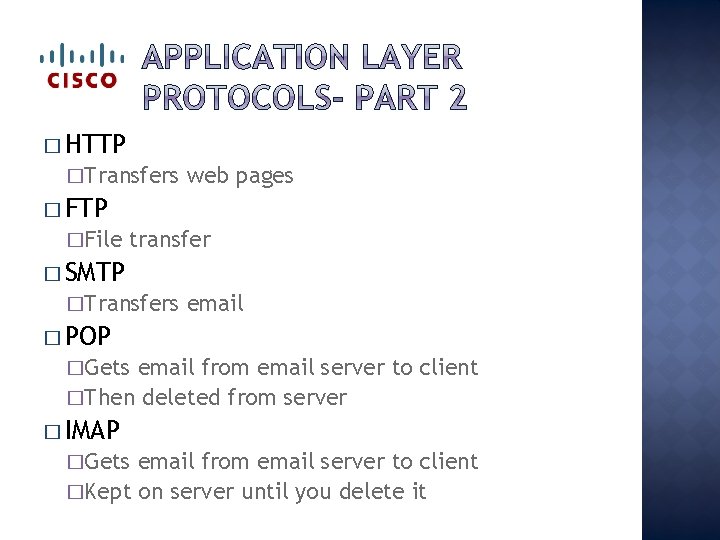
� HTTP �Transfers web pages � FTP �File transfer � SMTP �Transfers email � POP �Gets email from email server to client �Then deleted from server � IMAP �Gets email from email server to client �Kept on server until you delete it
� 10. 1. 1. 5
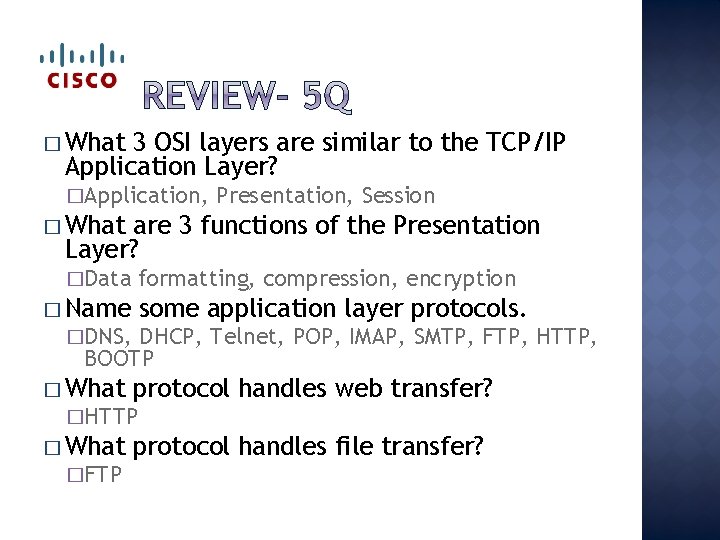
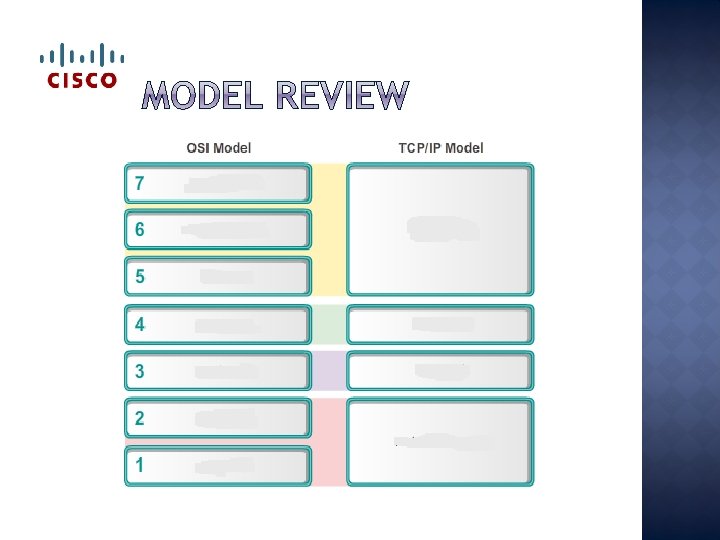
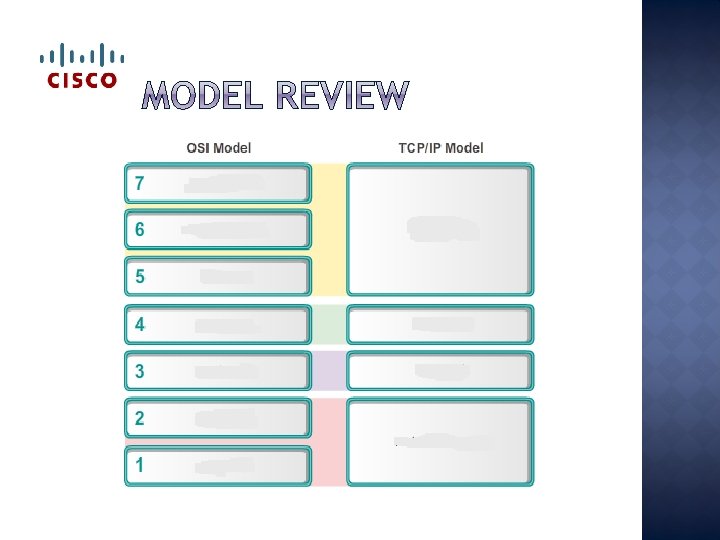
� What 3 OSI layers are similar to the TCP/IP Application Layer? �Application, Presentation, Session � What are 3 functions of the Presentation Layer? �Data formatting, compression, encryption � Name some application layer protocols. �DNS, DHCP, Telnet, POP, IMAP, SMTP, FTP, HTTP, BOOTP � What protocol �HTTP � What �FTP handles web transfer? protocol handles file transfer?
10. 1. 1
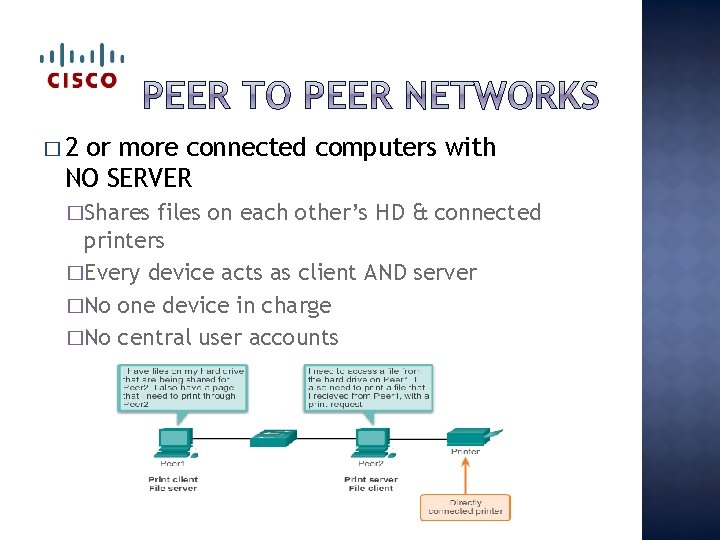
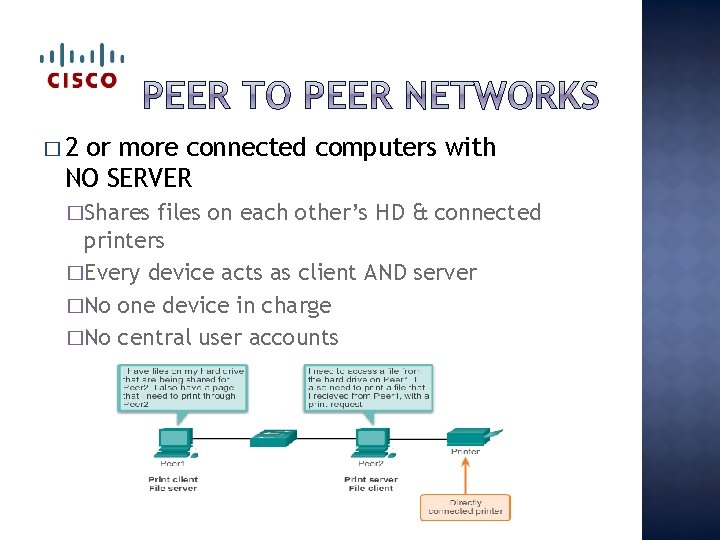
� 2 or more connected computers with NO SERVER �Shares files on each other’s HD & connected printers �Every device acts as client AND server �No one device in charge �No central user accounts
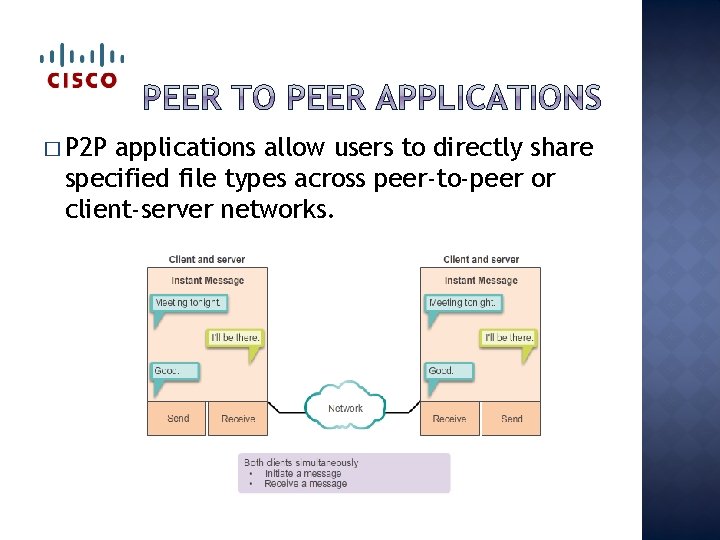
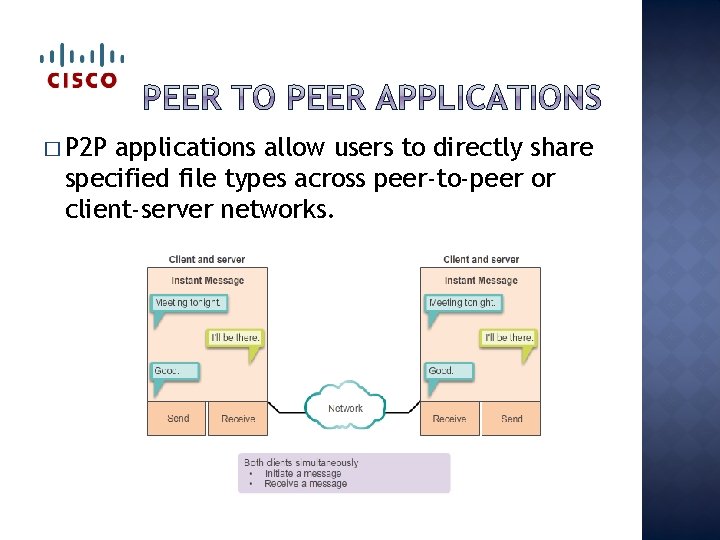
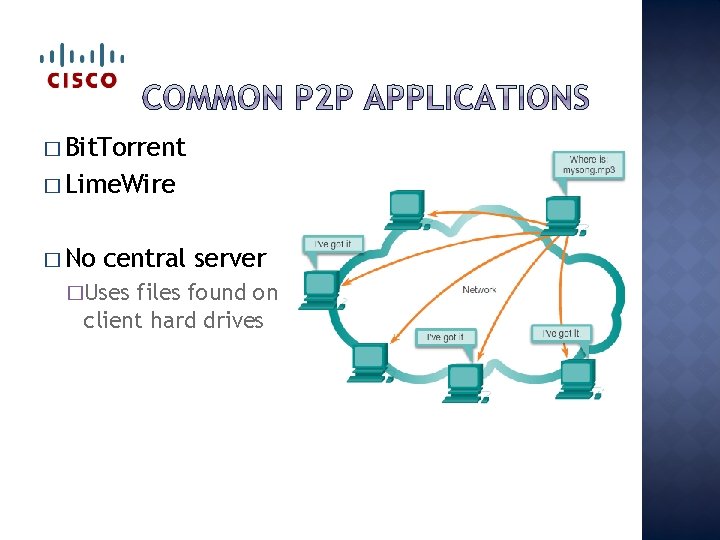
� P 2 P applications allow users to directly share specified file types across peer-to-peer or client-server networks.
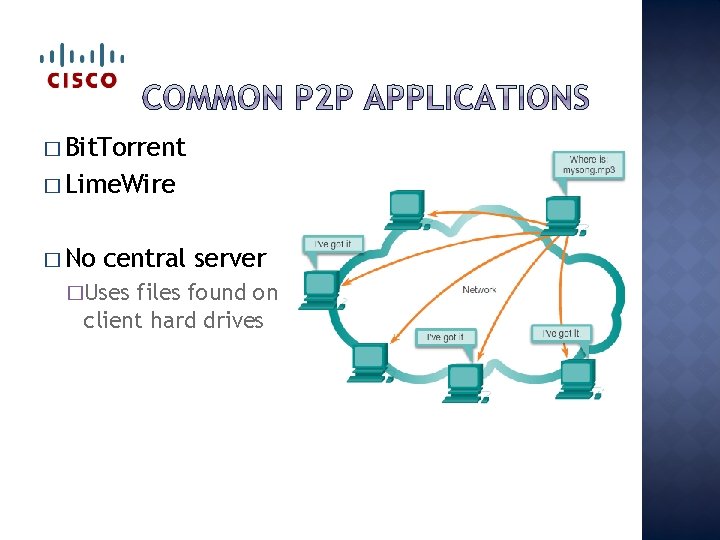
� Bit. Torrent � Lime. Wire � No central server �Uses files found on client hard drives
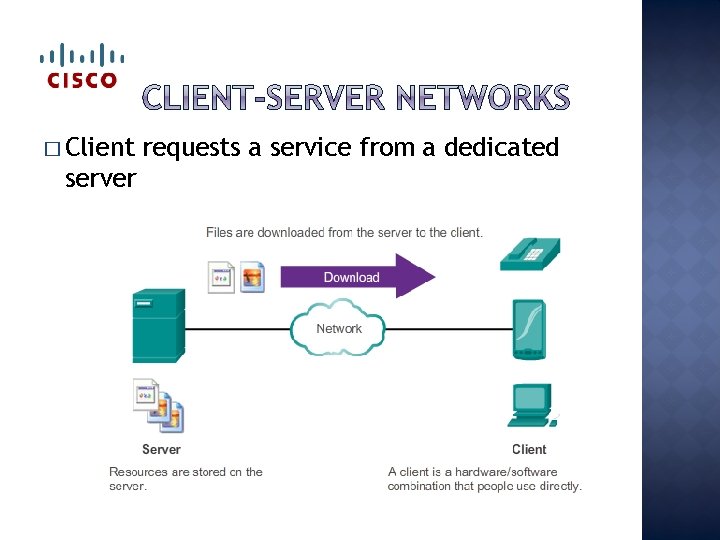
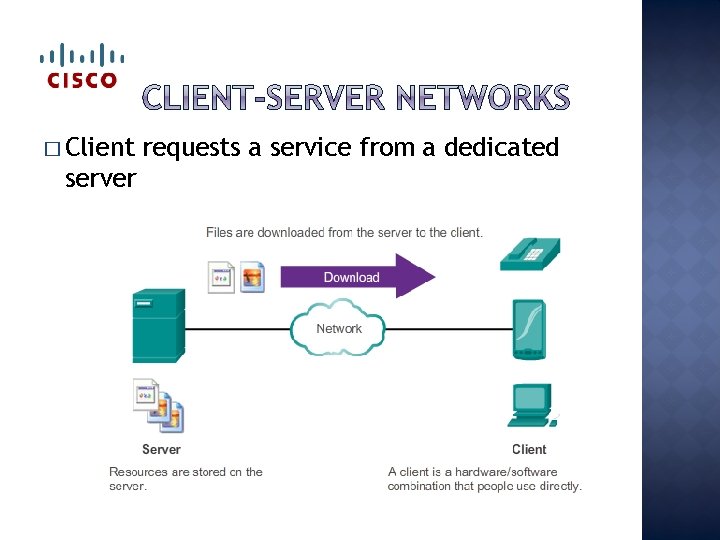
� Client server requests a service from a dedicated
� What type of network has centralized resources, such as central file storage? �Client-server � What type of network shares resources located on local computer hard drives? �Peer to peer � You type www. gcit. org into your web browser. A DNS request is created and then a we request is sent. What type of network is this? �Client-server
10. 2. 1
� What application layer protocols would you use on a daily basis?
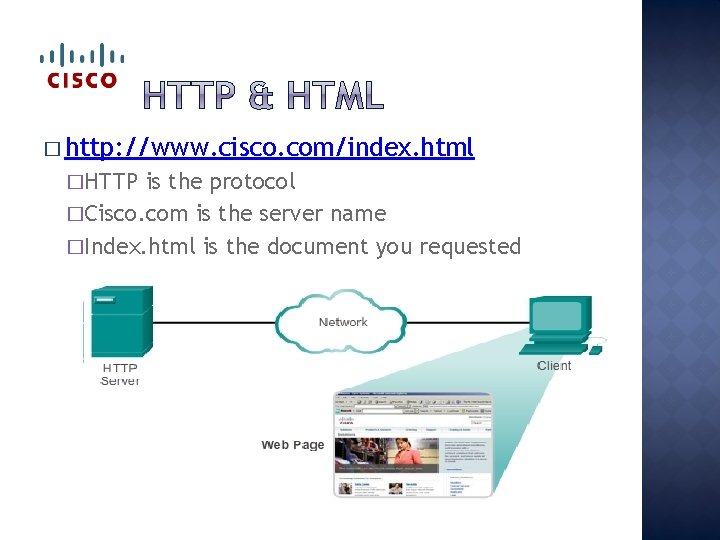
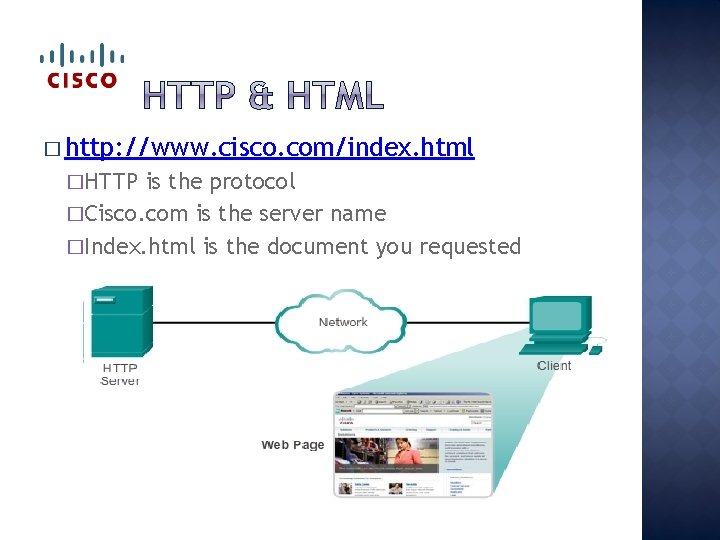
� http: //www. cisco. com/index. html �HTTP is the protocol �Cisco. com is the server name �Index. html is the document you requested
� Layer 4 port: �HTTP: 80 �HTTPS: 443 � Browser messages �GET (requests page from web server) �POST & PUT (uploads to web server) � HTTPS �Secure �Uses SSL to encrypt
� Layer 4 ports: �SMTP-25 �POP 3 - 110 �IMAP-143 � Send � Get mail to server & server to server; SMTP mail from email server; POP 3 & IMAP �POP deletes mail from server when sent to client �IMAP sends copy of email to client and server keeps mail until deleted
� PT Lab 10. 2. 1. 8 Web & Email �In this activity, you will configure HTTP and email services using the simulated server in Packet Tracer. You will then configure clients to access the HTTP and email services.
� Why would you use IMAP instead of POP? �IMAP keeps the emails until manually deleted � Which protocol uses GET, PUT, and POST? �HTTP � Which email protocol send you a copy of the email and deletes it from the server? �POP � What port # is POP? � 110 � What �SSL does HTTPS use to encrypt?
10. 2. 2
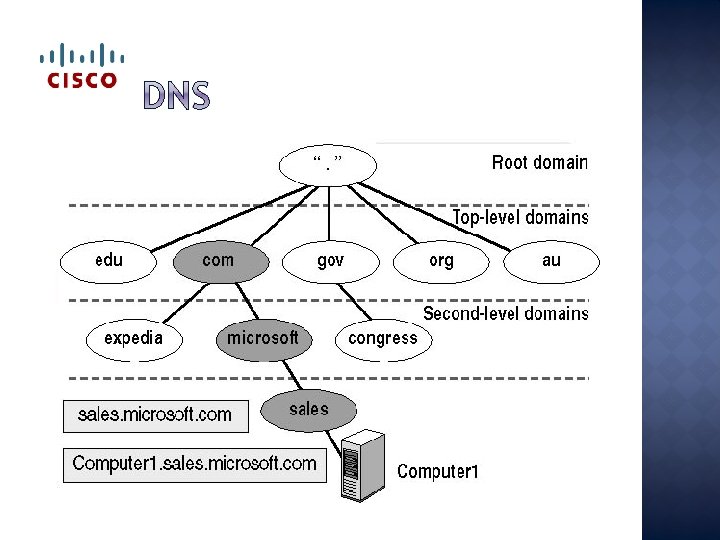
� Layer 4 port: 53 � Servers that translates names to IP addresses � DNS servers know some, forward rest to other DNS servers � Nslookup �Get in the mode and then enter domain � Ipconfig /displaydns �Displays cached DNS
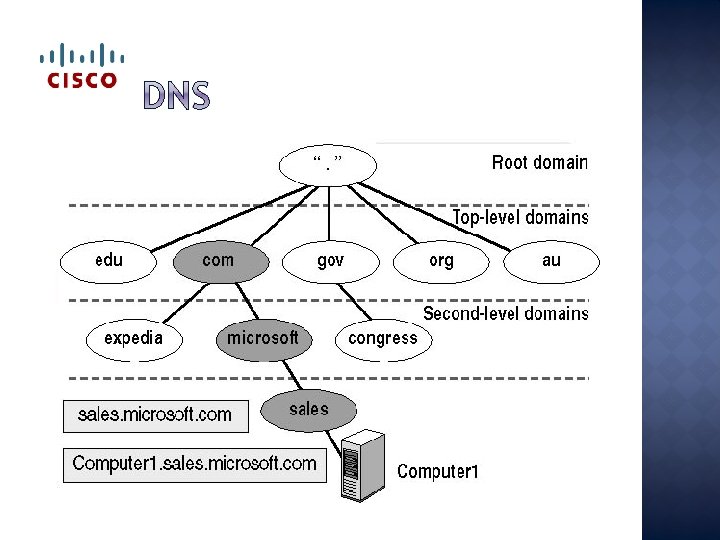
� DNS servers are in a hierarchy �Top-level, most trusted: . com, . edu, . gov Contains 2 nd-level domain server records �Second-level: � MX Contains records for the company only used for mail
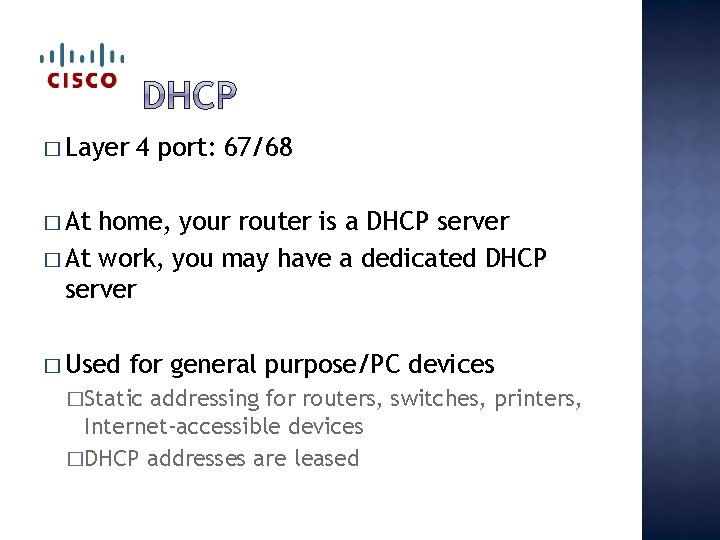
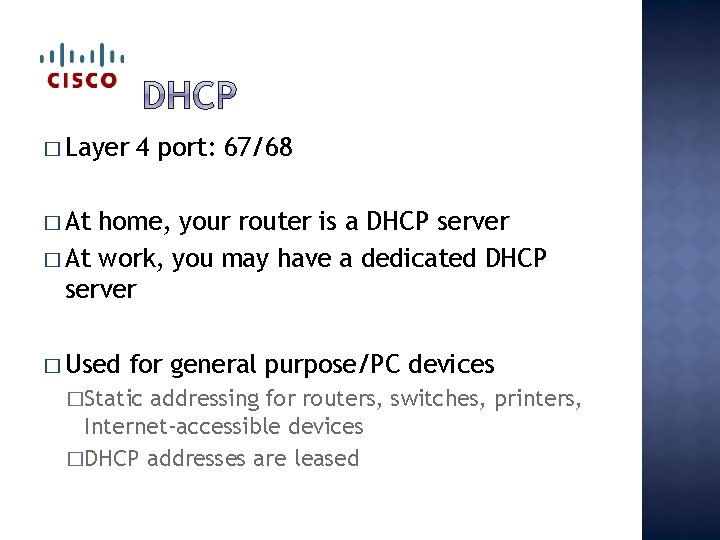
� Layer 4 port: 67/68 � At home, your router is a DHCP server � At work, you may have a dedicated DHCP server � Used for general purpose/PC devices �Static addressing for routers, switches, printers, Internet-accessible devices �DHCP addresses are leased
� PT Lab 10. 2. 2. 8 �DHCP & DNS Services �In this activity, you will configure and verify static IP addressing and DHCP addressing. You will then configure a DNS server to map IP addresses to the website names. � HW: Lab 10. 2. 2. 9 �Observing DNS �You will observe the DNS Conversion of a URL to an IP Address, observe DNS Lookup Using the nslookup Command on a Web Site, and observe DNS Lookup Using the nslookup Command on Mail Servers.
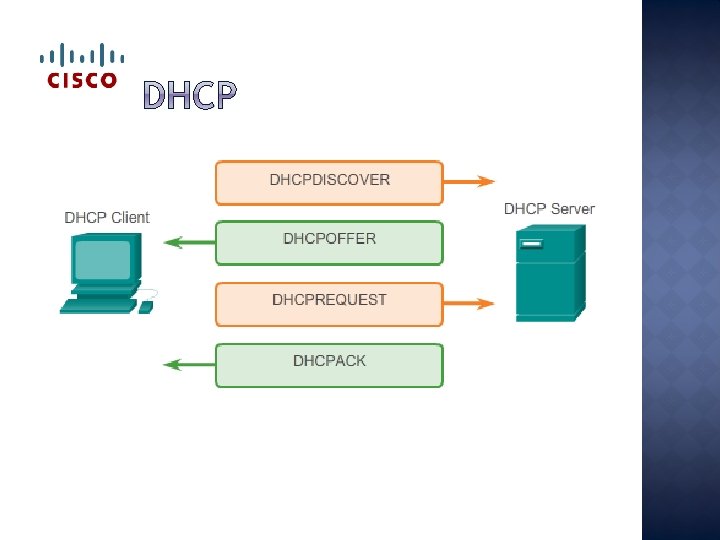
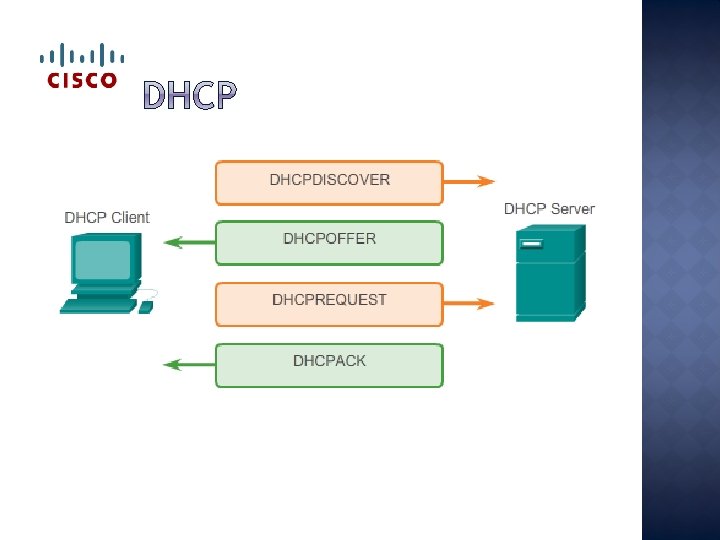
� Which broadcast message gets sent out from a PC to a DHCP server when it turns on? �DCHPDiscover � What does the DHCP server send back to the PC? �DHCPOffer � What �All � Who does the DHCP request look like? 255’s gets & responds to that request? �Everyone in local network gets it; only DHCP server responds
10. 2. 3
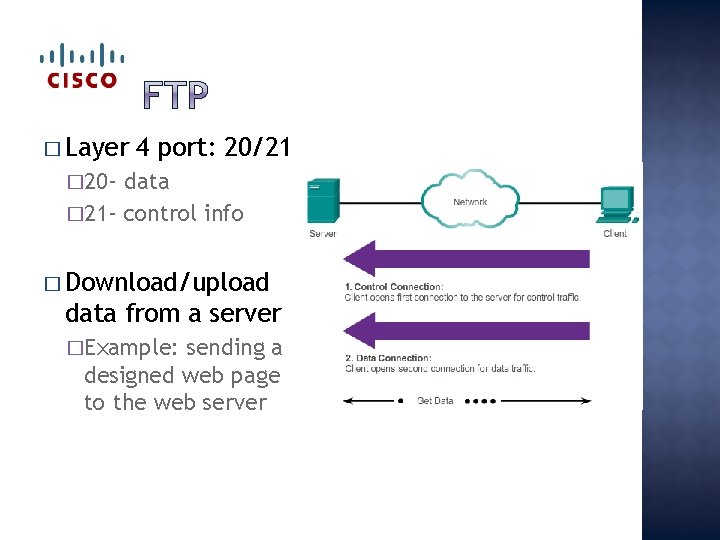
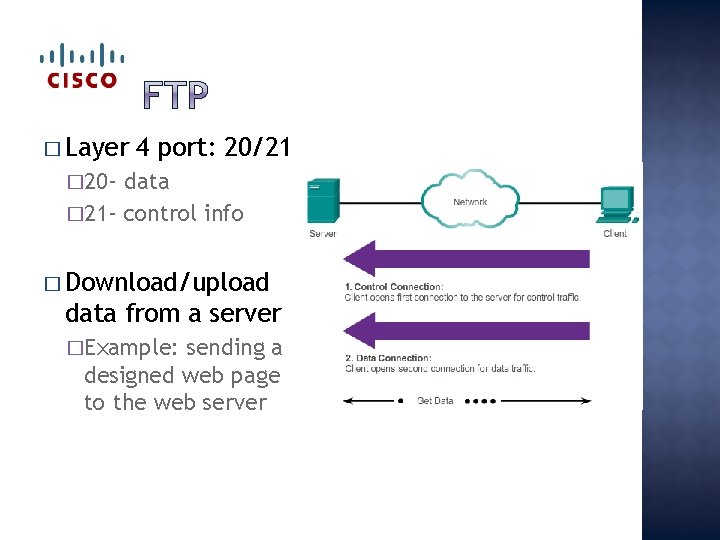
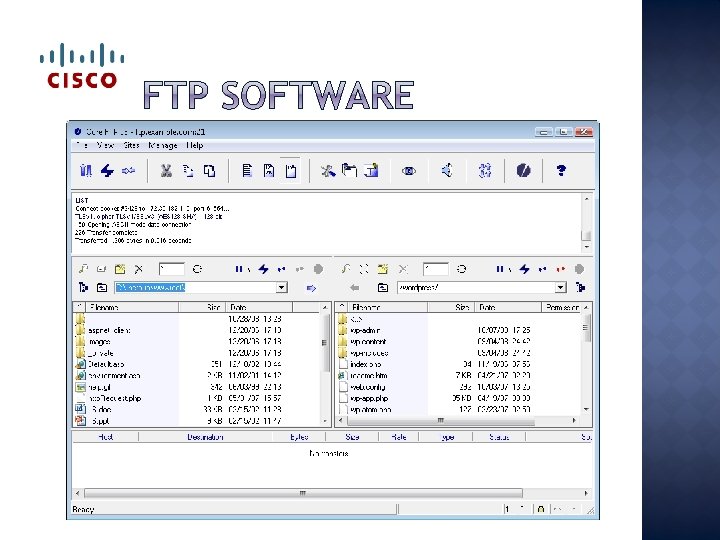
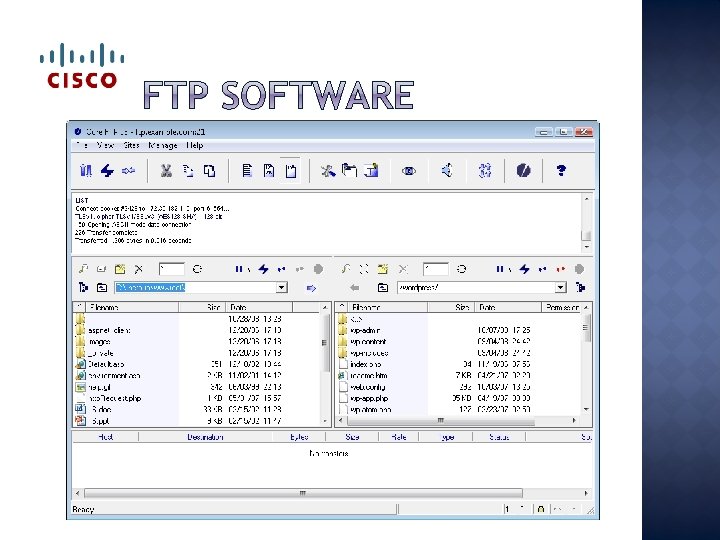
� Layer 4 port: 20/21 � 20 - data � 21 - control info � Download/upload data from a server �Example: sending a designed web page to the web server
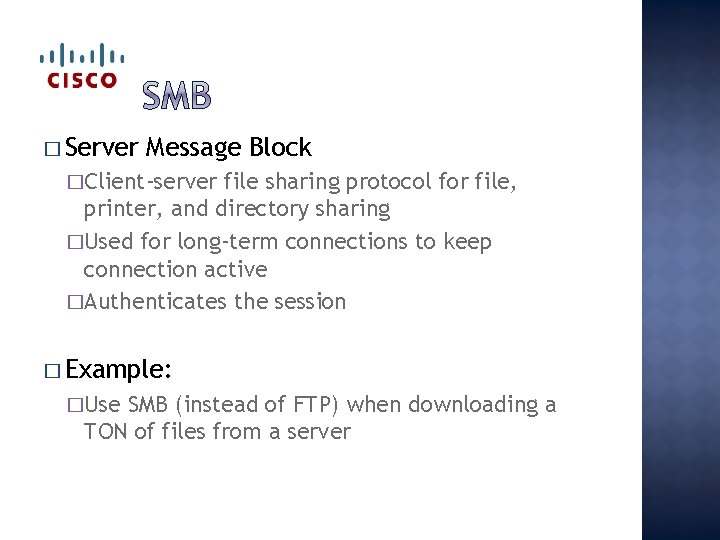
� Server Message Block �Client-server file sharing protocol for file, printer, and directory sharing �Used for long-term connections to keep connection active �Authenticates the session � Example: �Use SMB (instead of FTP) when downloading a TON of files from a server
� PT Lab 10. 2. 3. 2 �In this activity, you will configure FTP services. You will then use the FTP services to transfer files between clients and the server.
� What program runs on an FTP server that listens for requests? �FTPdaemon � What runs on a PC that will request services from an FTP server? �FTP � If Client software you need to download many files from a server, which could take hours, which protocol would you use? �SMB
� Which command did you use to manually get the name to IP information? �nslookup � What port is HTTPS? � 443 � What type of applications need a specific application interface and background service running between hosts? �P 2 P application, like IM
� Applications are computer programs with which the user interacts and which initiate the data transfer process at the user’s request. � Services are background programs that provide the connection between the application layer and the lower layers of the networking model. � Protocols provide a structure of agreed-upon rules and processes that ensure services running on one particular device can send and receive data from a range of different network devices
� HTTP supports the delivery of web pages to end devices � SMTP, POP, and IMAP support sending and receiving email � FTP enable users to share files � P 2 P applications make it easier for consumers to seamlessly share media � DNS resolves the human legible names used to refer to network resources into numeric addresses usable by the network � All of these elements work together, at the application layer. � The application layer enables users to work and play over the Internet.
� Complete � Take the study guide handout the quiz on netacad. com � Jeopardy review

Chapter 10 Intro to Routing & Switching