Agenda Azure Attack Surface Azure Bug Bounty Background

Agenda + =
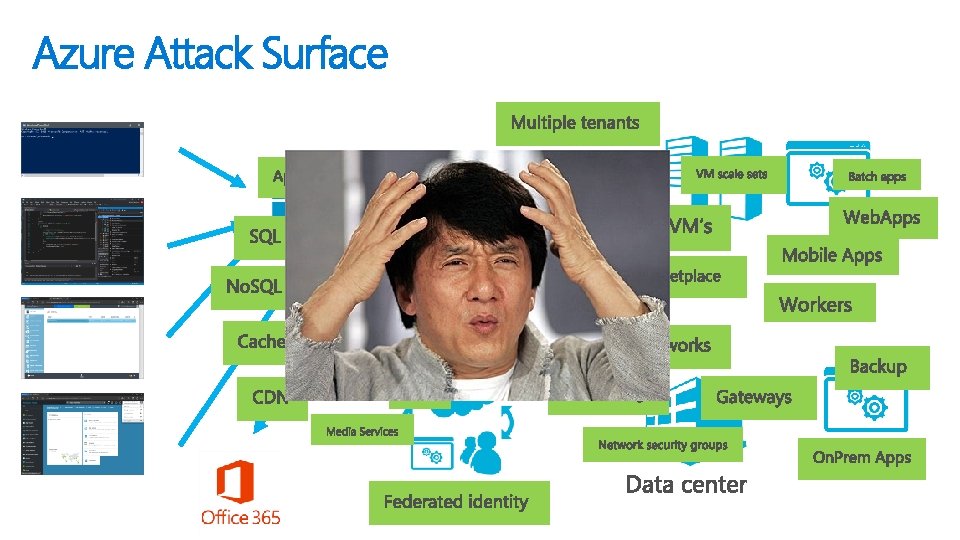
Azure Attack Surface
Azure Bug Bounty Background
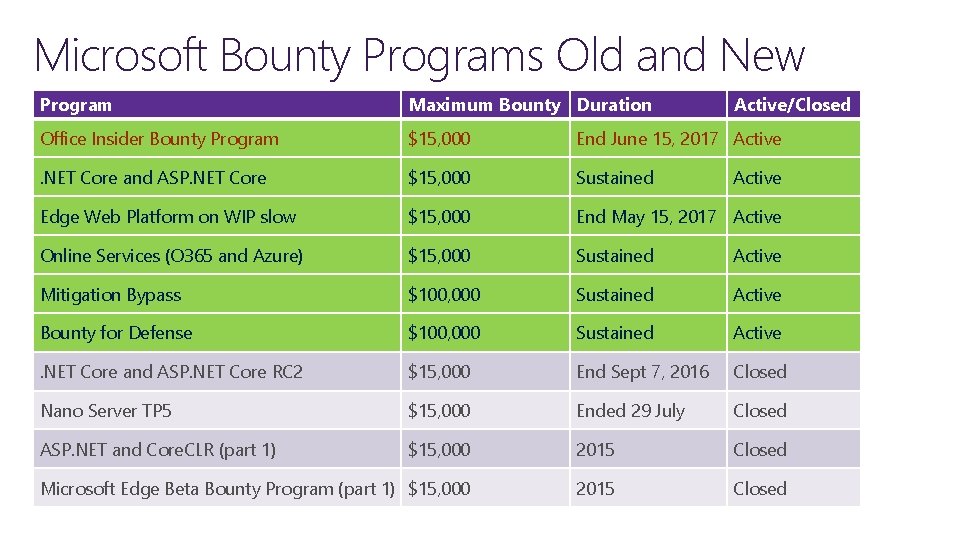
Microsoft Bounty Programs Old and New Program Maximum Bounty Duration Active/Closed Office Insider Bounty Program $15, 000 End June 15, 2017 Active . NET Core and ASP. NET Core $15, 000 Sustained Edge Web Platform on WIP slow $15, 000 End May 15, 2017 Active Online Services (O 365 and Azure) $15, 000 Sustained Active Mitigation Bypass $100, 000 Sustained Active Bounty for Defense $100, 000 Sustained Active . NET Core and ASP. NET Core RC 2 $15, 000 End Sept 7, 2016 Closed Nano Server TP 5 $15, 000 Ended 29 July Closed ASP. NET and Core. CLR (part 1) $15, 000 2015 Closed Microsoft Edge Beta Bounty Program (part 1) $15, 000 2015 Closed Active
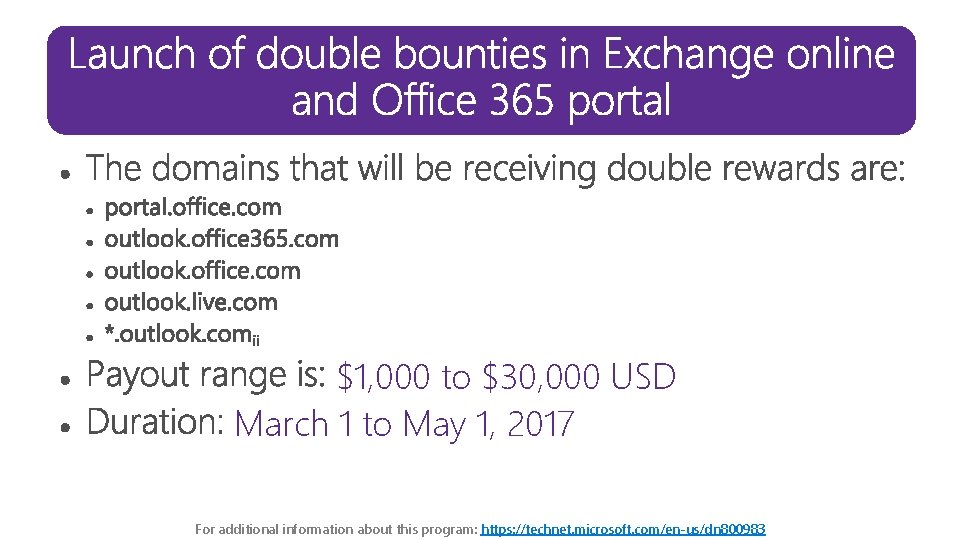
$1, 000 to $30, 000 USD March 1 to May 1, 2017 For additional information about this program: https: //technet. microsoft. com/en-us/dn 800983
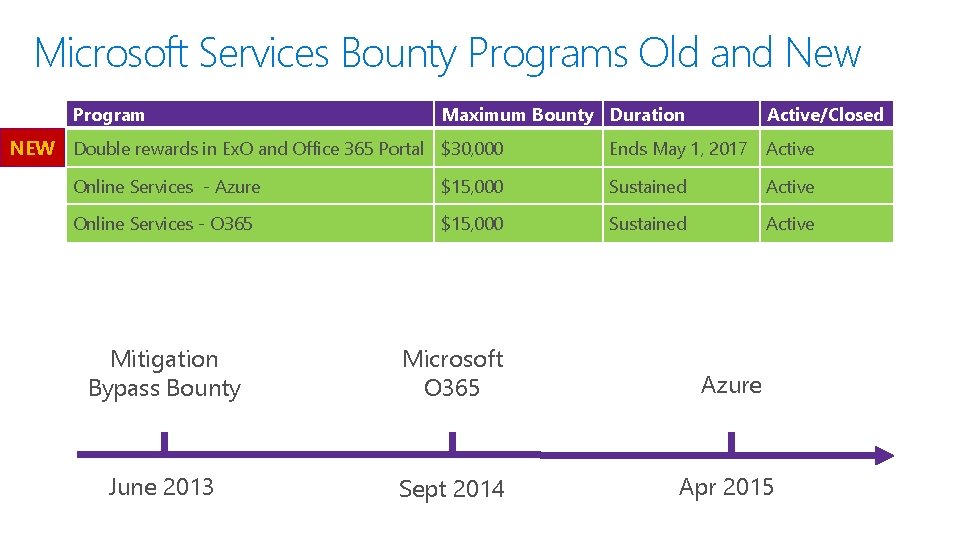
Microsoft Services Bounty Programs Old and New Program Maximum Bounty Duration NEW Double rewards in Ex. O and Office 365 Portal $30, 000 Active/Closed Ends May 1, 2017 Active Online Services - Azure $15, 000 Sustained Active Online Services - O 365 $15, 000 Sustained Active Mitigation Bypass Bounty Microsoft O 365 Azure June 2013 Sept 2014 Apr 2015
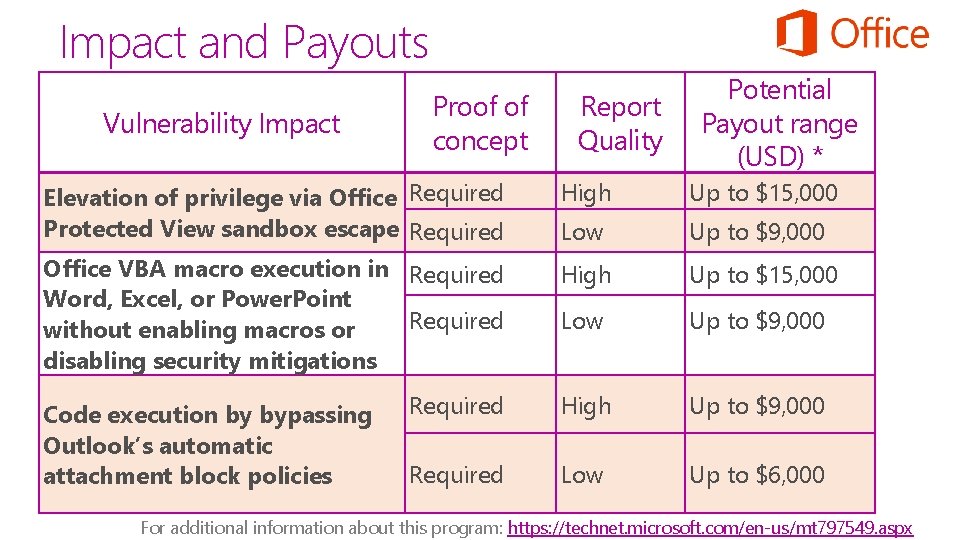
Impact and Payouts Vulnerability Impact Proof of concept Report Quality Potential Payout range (USD) * Elevation of privilege via Office Required Protected View sandbox escape Required High Up to $15, 000 Low Up to $9, 000 Office VBA macro execution in Required Word, Excel, or Power. Point Required without enabling macros or disabling security mitigations High Up to $15, 000 Low Up to $9, 000 Required High Up to $9, 000 Required Low Up to $6, 000 Code execution by bypassing Outlook’s automatic attachment block policies For additional information about this program: https: //technet. microsoft. com/en-us/mt 797549. aspx
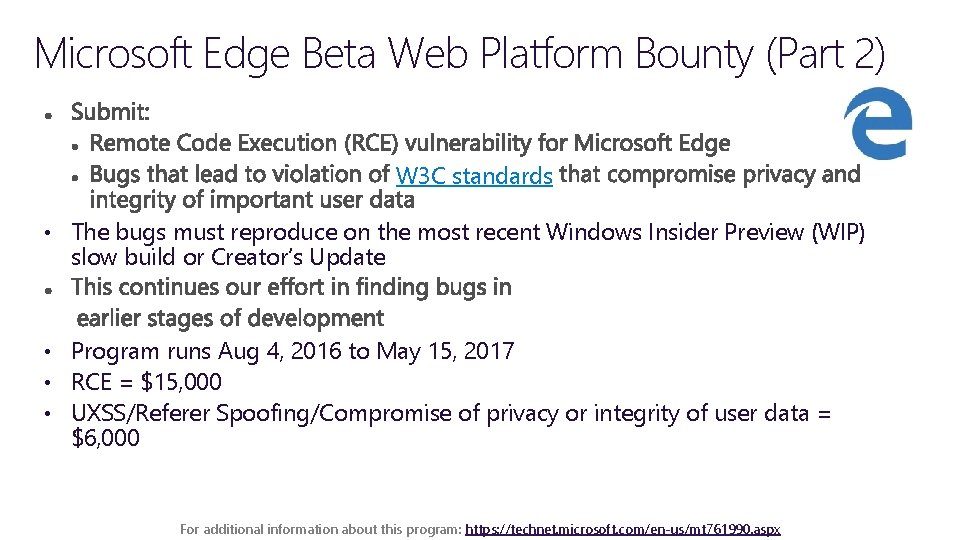
Microsoft Edge Beta Web Platform Bounty (Part 2) W 3 C standards • The bugs must reproduce on the most recent Windows Insider Preview (WIP) slow build or Creator’s Update • Program runs Aug 4, 2016 to May 15, 2017 • RCE = $15, 000 • UXSS/Referer Spoofing/Compromise of privacy or integrity of user data = $6, 000 For additional information about this program: https: //technet. microsoft. com/en-us/mt 761990. aspx

. NET Core and ASP. NET Core Bug Bounty • Vulnerabilities in the latest available. NET builds • Program began September 1, 2016 (continuous) • All bugs have to reproduce in the latest beta or release candidates to qualify • Pays up to $15, 000 USD Vulnerability type Remote Code Execution Payout range (USD) $15, 000 to $1, 500 Security Design Flaw $10, 000 to $1, 500 Elevation of Privilege $10, 000 to $5, 000 Remote Do. S $5, 000 to $2, 500 Tampering / Spoofing $5, 000 to $500 Information Leaks $2, 500 to $750 Template CSRF or XSS $2, 000 to $500 For additional information about this program: https: //technet. microsoft. com/en-us/mt 764065

Online Services Bug Bounty Program O 365 + Azure Follow us on the MSRC Blogs to get information on new bounties https: //blogs. technet. microso ft. com/msrc/ • $500 to $15, 000 USD Double bounty on exchange online and O 365 portal for the next 2 months For additional information about this program: https: //technet. microsoft. com/en-us/dn 800983

Hyper-V escapes that will receive a bounty Up to $100, 000 USD For additional information about this program: https: //technet. microsoft. com/en-us/dn 425049
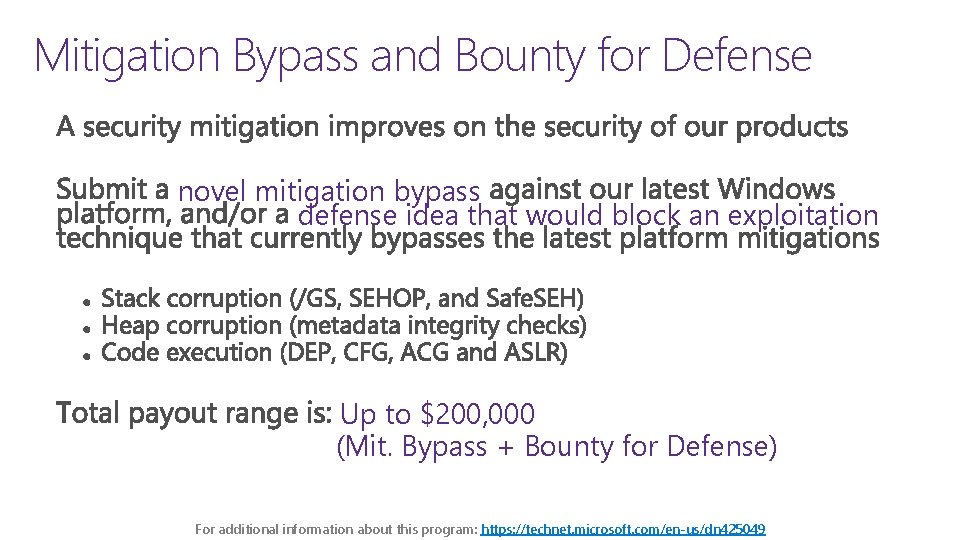
Mitigation Bypass and Bounty for Defense novel mitigation bypass defense idea that would block an exploitation Up to $200, 000 (Mit. Bypass + Bounty for Defense) For additional information about this program: https: //technet. microsoft. com/en-us/dn 425049

Past payouts MSRC case Amount Vulnerability Type Security Impact 31042 $24, 000. 00 OAuth 2 Authentication bypass Auth token theft 34219 $13, 350. 00 Azure virtual network gateway Auth Bypass Unauthorized Access 32235 $13, 000. 00 Federated identity impersonation via SAML Id. P Elevation of privileges 32377 $13, 000. 00 Double Unicode decoding in URL redirection. Auth token theft 31586 $12, 000. 00 XSS in OAuth 2 authorization Elevation of privileges 32583 $12, 000. 00 Embedded password in Azure Stack VHD Information Disclosure 32635 $ 10, 000. 00 Open redirection bypass (%80 char) Spoofing
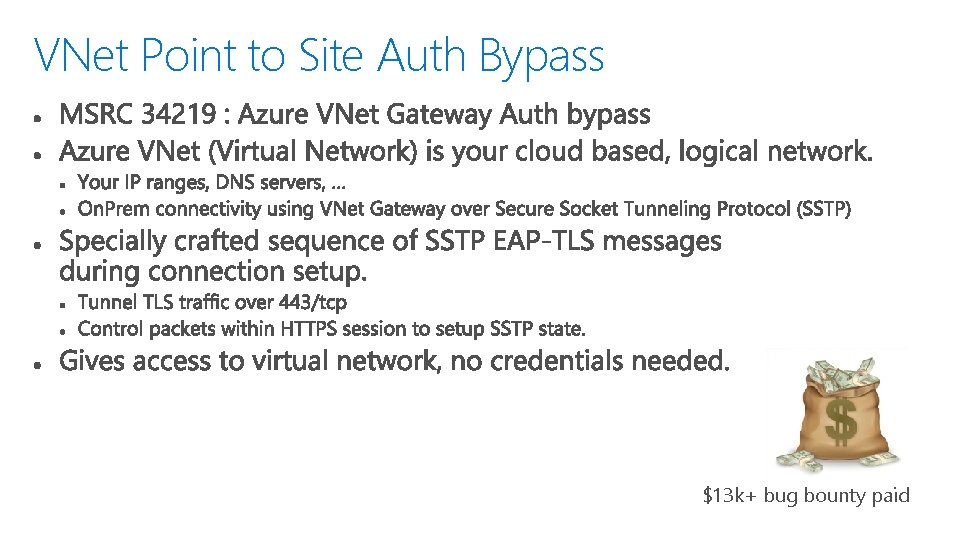
VNet Point to Site Auth Bypass $13 k+ bug bounty paid

Token leaking account. windowsazure. com%2 f evildomain. net This is seen as username to log in to domain Evildomain. net will get the token, not account. windowsazure. com $13 k bug bounty paid
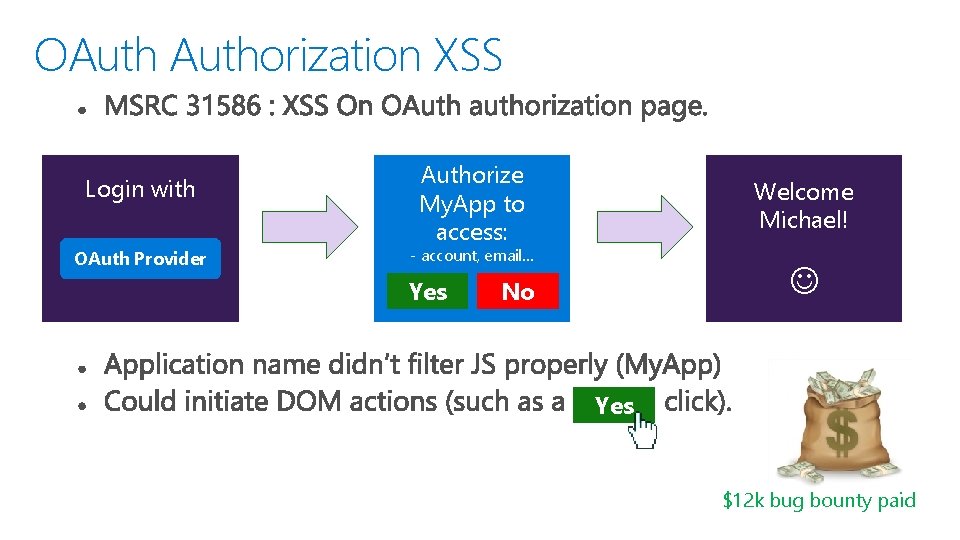
OAuthorization XSS Login with OAuth Provider Authorize My. App to access: Welcome Michael! - account, email… Yes No Yes $12 k bug bounty paid
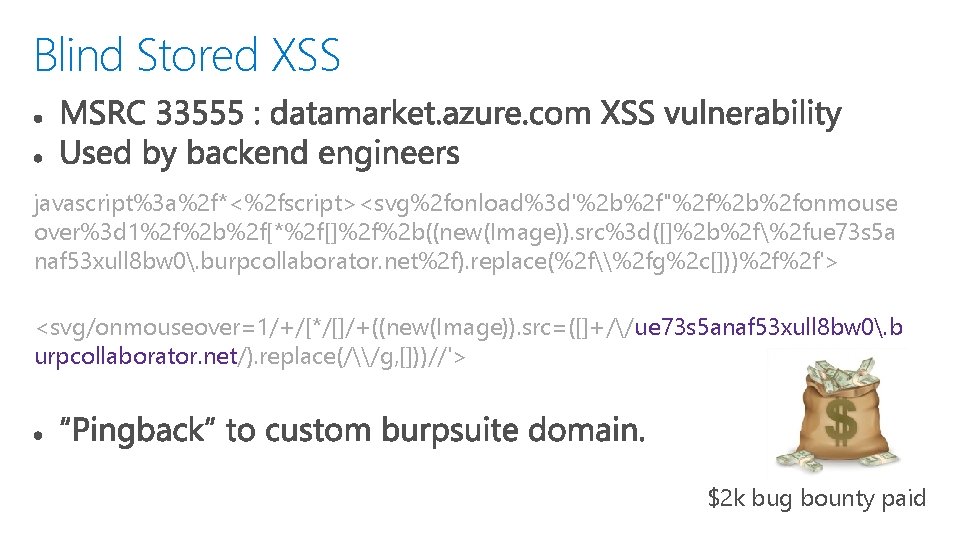
Blind Stored XSS javascript%3 a%2 f*<%2 fscript><svg%2 fonload%3 d'%2 b%2 f"%2 f%2 b%2 fonmouse over%3 d 1%2 f%2 b%2 f[*%2 f[]%2 f%2 b((new(Image)). src%3 d([]%2 b%2 f%2 fue 73 s 5 a naf 53 xull 8 bw 0. burpcollaborator. net%2 f). replace(%2 f\%2 fg%2 c[]))%2 f%2 f'> <svg/onmouseover=1/+/[*/[]/+((new(Image)). src=([]+//ue 73 s 5 anaf 53 xull 8 bw 0. b urpcollaborator. net/). replace(/\/g, []))//'> $2 k bug bounty paid
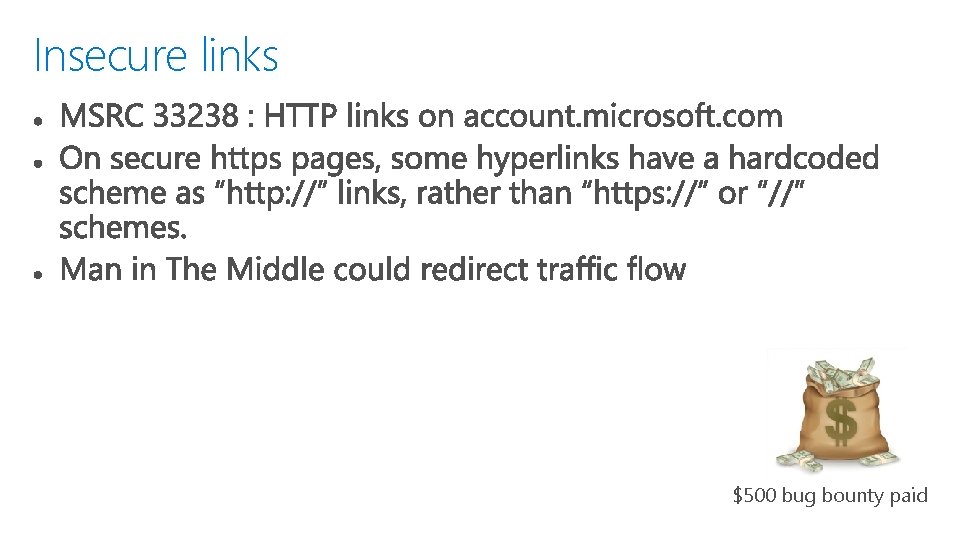
Insecure links $500 bug bounty paid
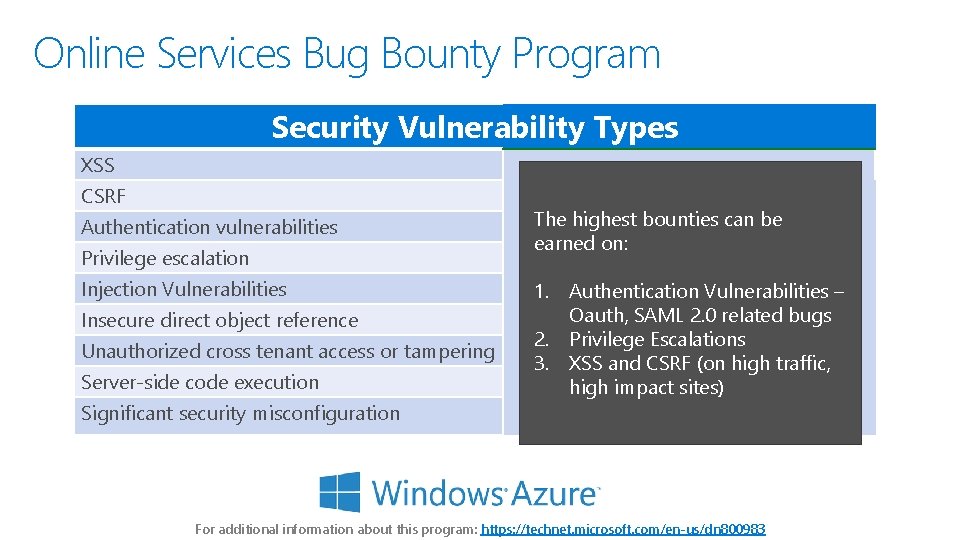
Online Services Bug Bounty Program Security Vulnerability Types XSS CSRF Authentication vulnerabilities Privilege escalation Injection Vulnerabilities Insecure direct object reference Unauthorized cross tenant access or tampering Server-side code execution Significant security misconfiguration The highest bounties can be earned on: 1. Authentication Vulnerabilities – Oauth, SAML 2. 0 related bugs 2. Privilege Escalations 3. XSS and CSRF (on high traffic, high impact sites) For additional information about this program: https: //technet. microsoft. com/en-us/dn 800983
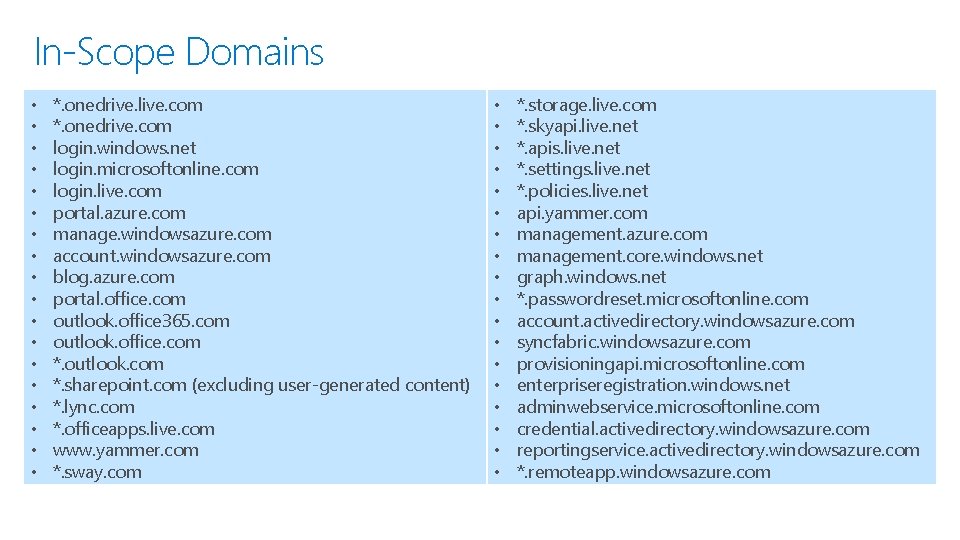
In-Scope Domains • • • • • *. onedrive. live. com *. onedrive. com login. windows. net login. microsoftonline. com login. live. com portal. azure. com manage. windowsazure. com account. windowsazure. com blog. azure. com portal. office. com outlook. office 365. com outlook. office. com *. outlook. com *. sharepoint. com (excluding user-generated content) *. lync. com *. officeapps. live. com www. yammer. com *. sway. com • • • • • *. storage. live. com *. skyapi. live. net *. apis. live. net *. settings. live. net *. policies. live. net api. yammer. com management. azure. com management. core. windows. net graph. windows. net *. passwordreset. microsoftonline. com account. activedirectory. windowsazure. com syncfabric. windowsazure. com provisioningapi. microsoftonline. com enterpriseregistration. windows. net adminwebservice. microsoftonline. com credential. activedirectory. windowsazure. com reportingservice. activedirectory. windowsazure. com *. remoteapp. windowsazure. com

In-Scope Domains (continued) • • • • • <Tenant>. scm. azurewebsites. net (excluding user-generated content) <Tenant>. ftp. azurewebsites. net (excluding user-generated content) <Tenant>. batch. core. windows. net (excluding user-generated content) <Tenant>. batchapps. core. windows. net (excluding user-generated content) <Tenant>. trafficmanager. net (excluding user-generated content) <Tenant>. media. windows. net (excluding user-generated content) <Tenant>. azure-mobile. net (excluding user-generated content) <Tenant>. task. core. windows. net (excluding user-generated content) <Tenant>. watask. core. windows. net (excluding user-generated content) <Tenant>. workflow. windows. net (excluding user-generated content) <Tenant>. biztalk. windows. net (excluding user-generated content) <Tenant>. servicebus. windows. net (excluding user-generated content) <Tenant>. vault. azure. net (excluding user-generated content) <Tenant>. blob. core. windows. net (excluding user-generated content) <Tenant>. table. core. windows. net (excluding user-generated content) <Tenant>. queue. core. windows. net (excluding user-generated content) <Tenant>. files. core. windows. net (excluding user-generated content) List available on : https: //technet. microsoft. com/en-us/security/dn 800983
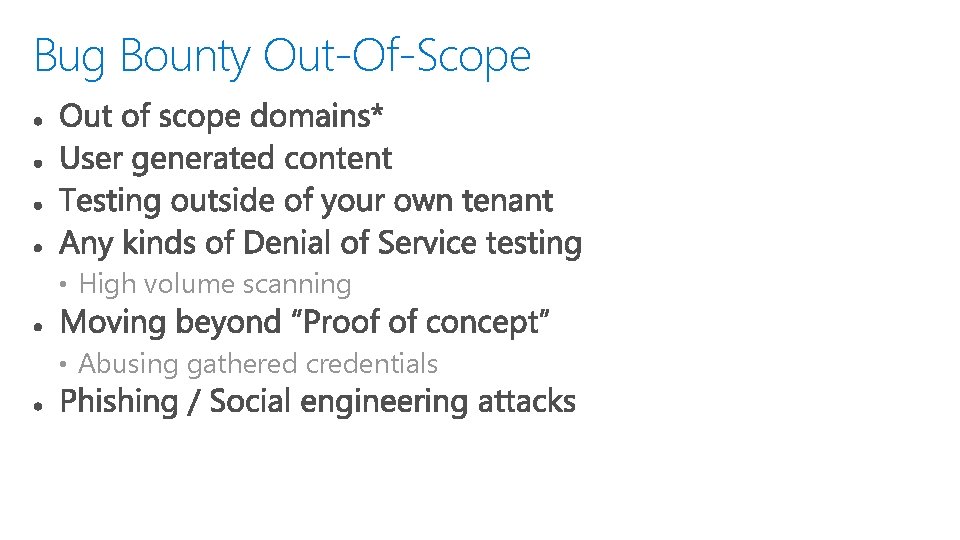
Bug Bounty Out-Of-Scope • High volume scanning • Abusing gathered credentials
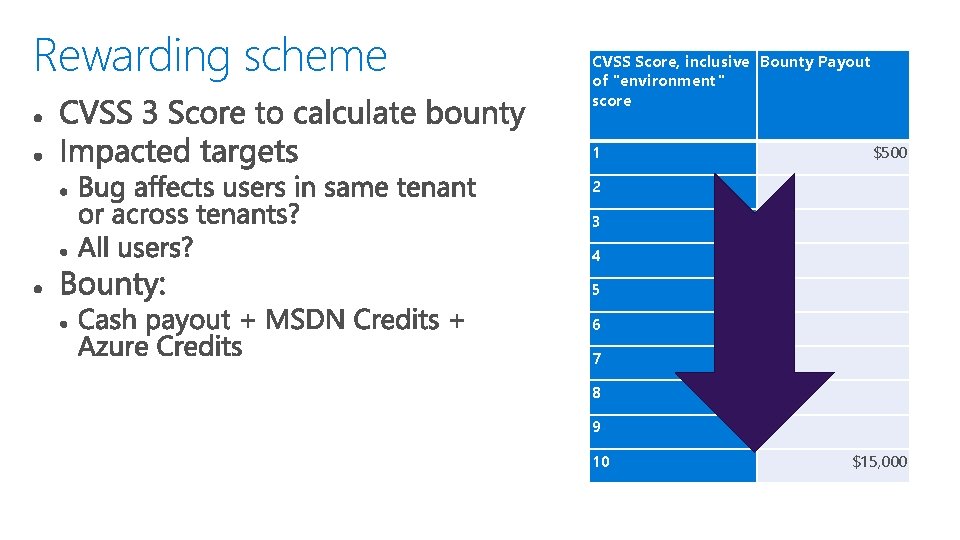
Rewarding scheme CVSS Score, inclusive Bounty Payout of "environment" score 1 $500 2 3 4 5 6 7 8 9 10 $15, 000
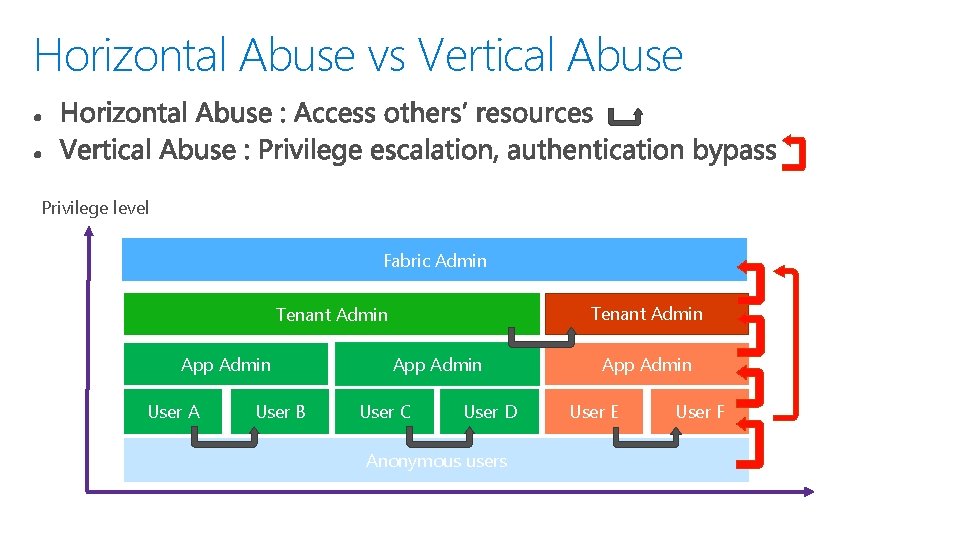
Horizontal Abuse vs Vertical Abuse Privilege level Fabric Admin Tenant Admin App Admin User A User B App Admin User C User D Anonymous users App Admin User E User F
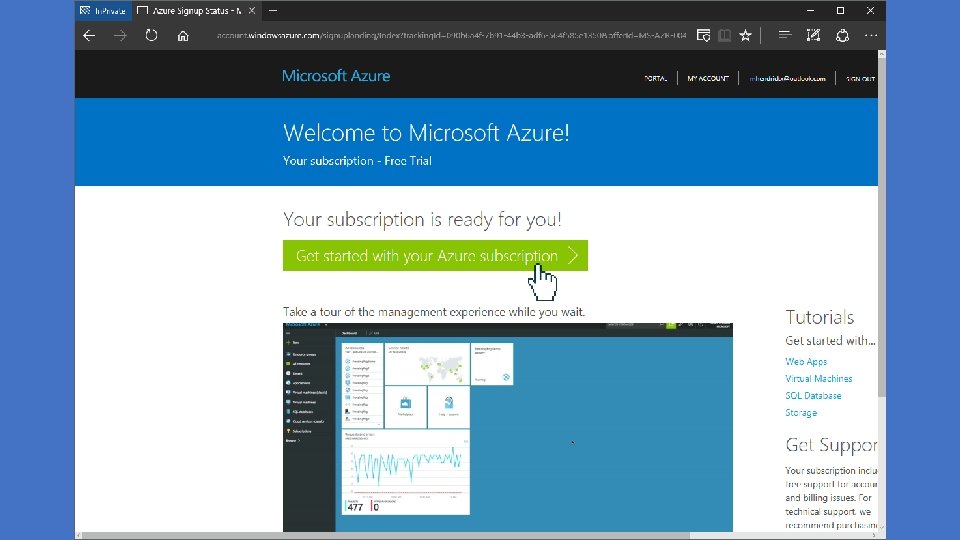
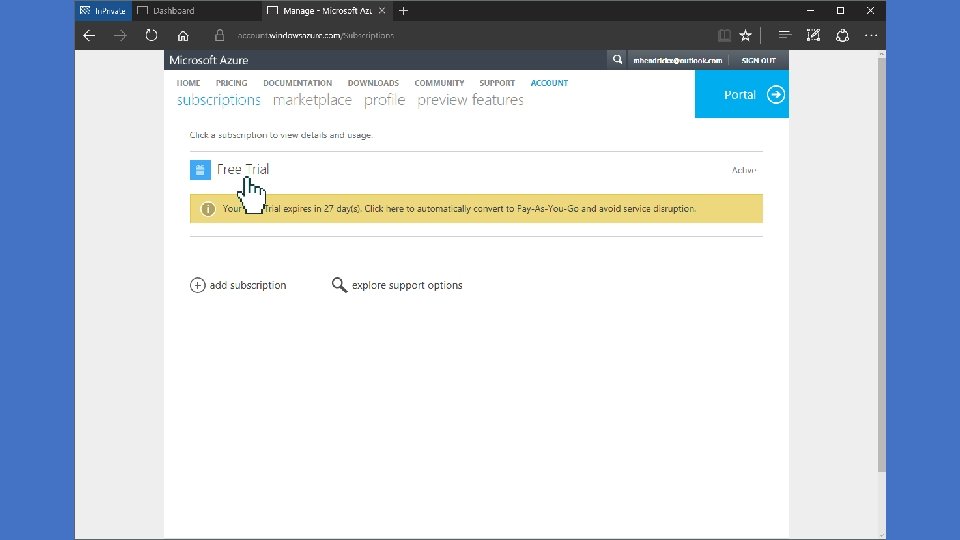
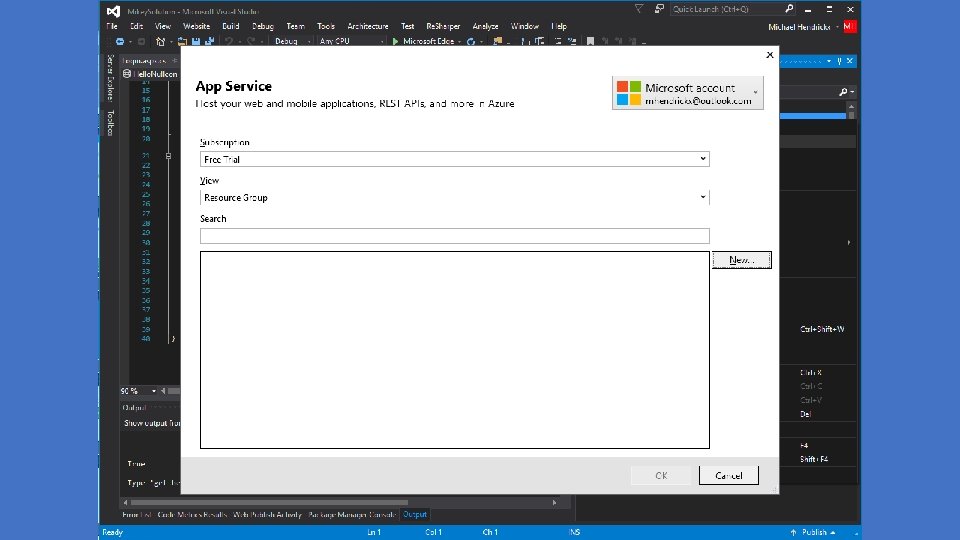
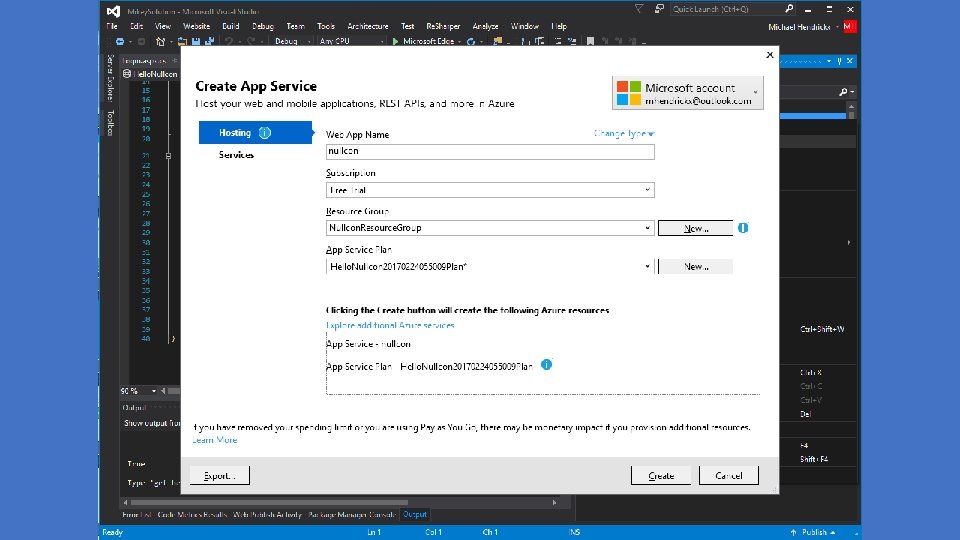
Get cracking (no pun intended) • Azure offers: https: //azure. microsoft. com/en-us/free/


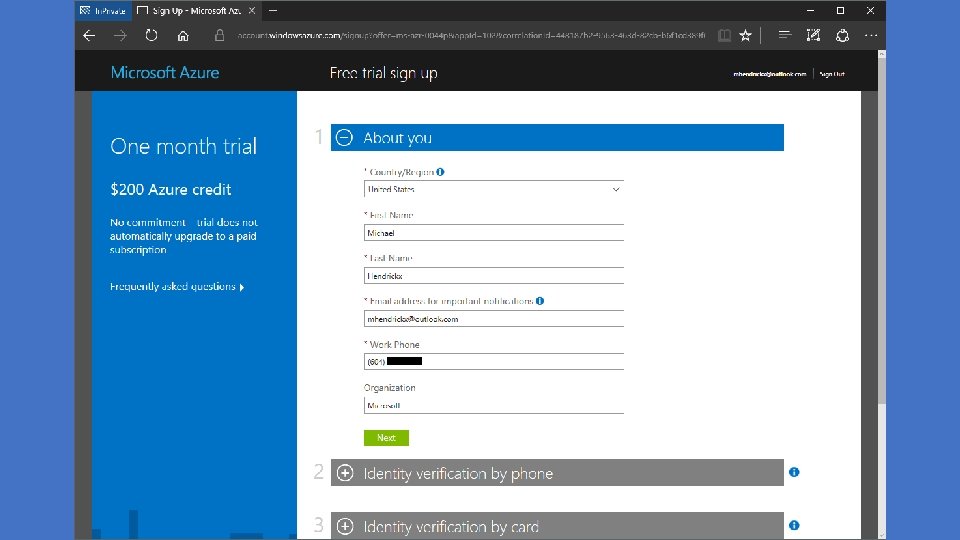
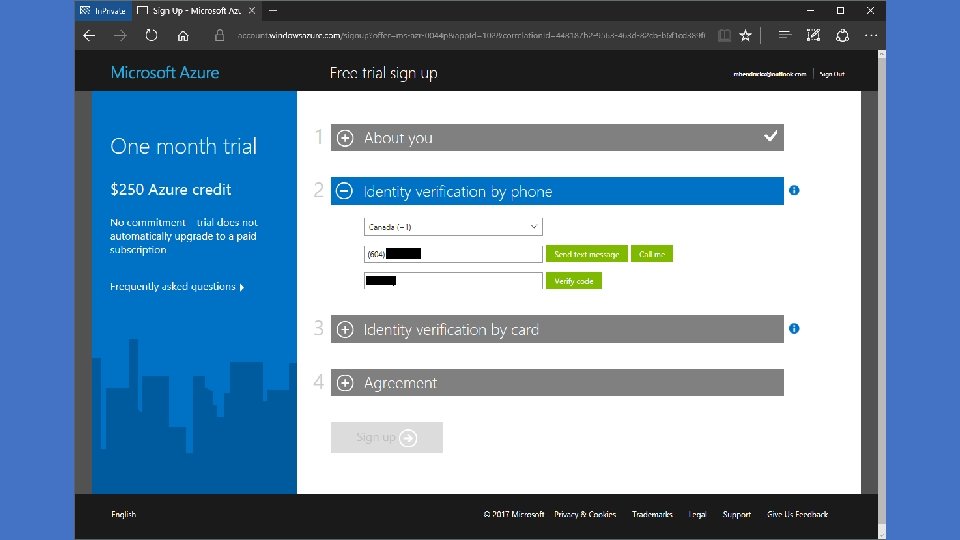
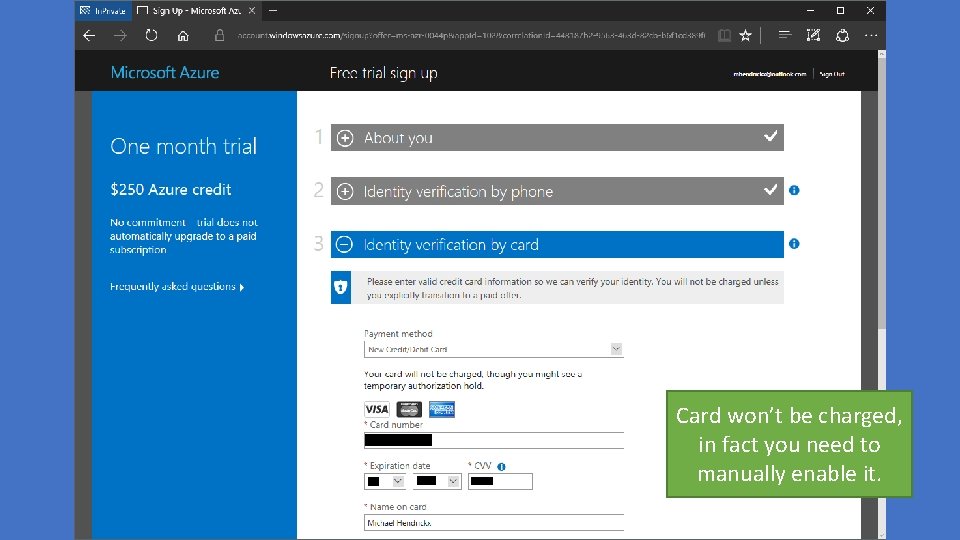
Card won’t be charged, in fact you need to manually enable it.

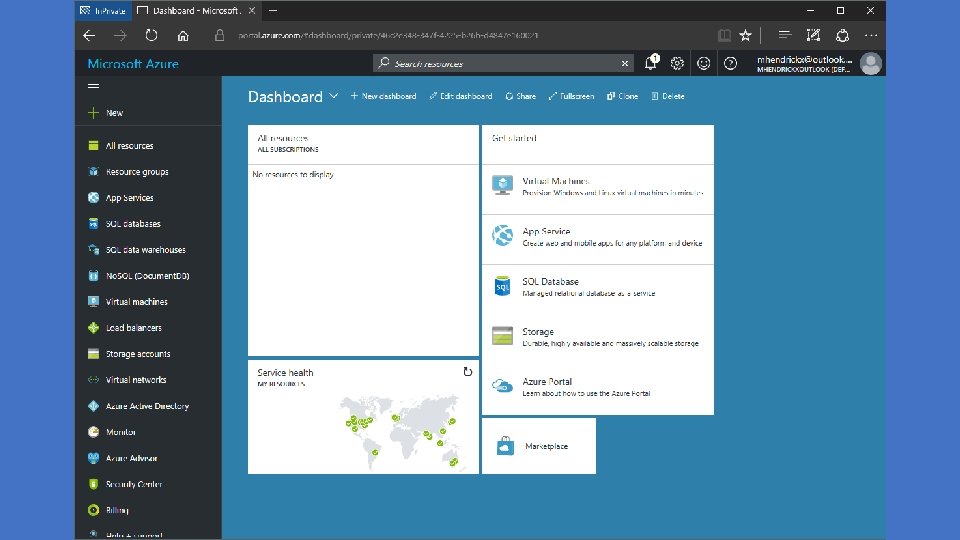
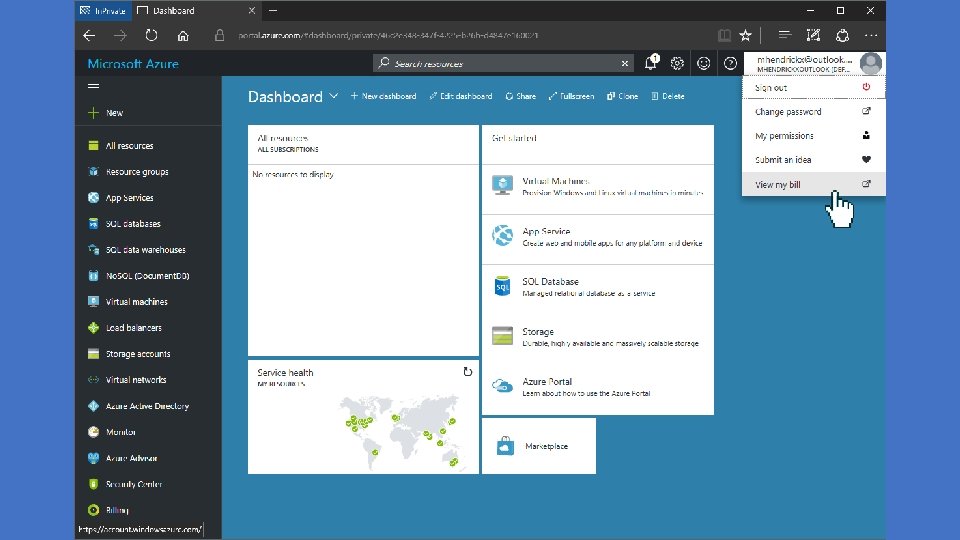
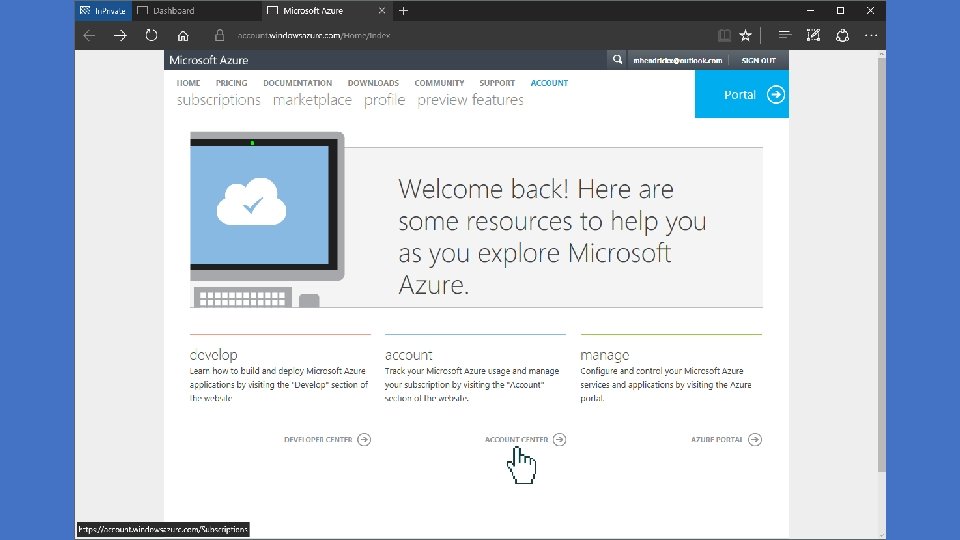

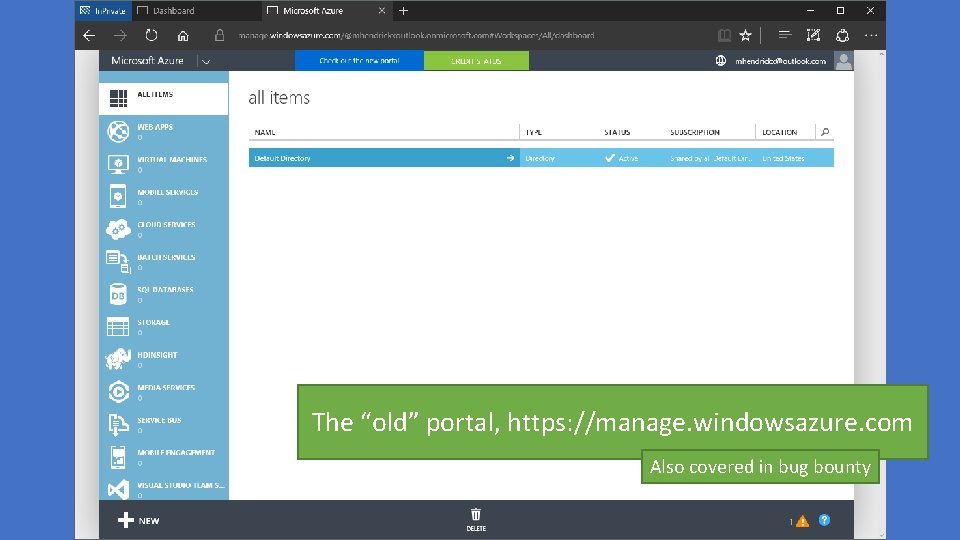
The “old” portal, https: //manage. windowsazure. com Also covered in bug bounty

Adding users to your tenant.
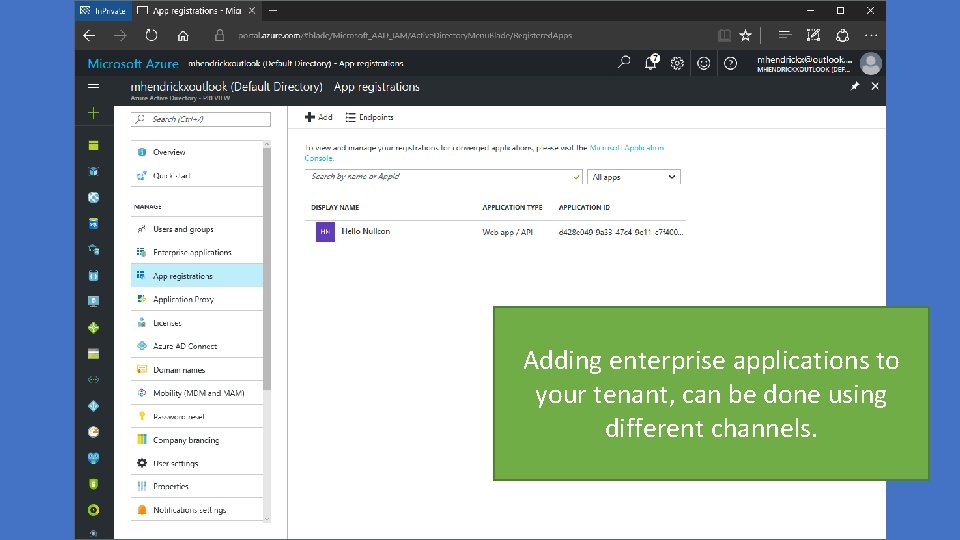
Adding enterprise applications to your tenant, can be done using different channels.


Bounties Paid To Date • Mitigation Bypass, Bounty for Defense and Blue. Hat Prize > $600, 000 USD • Online Services Bug Bounty > $400, 000 USD • Software Bounties > $200, 000 USD
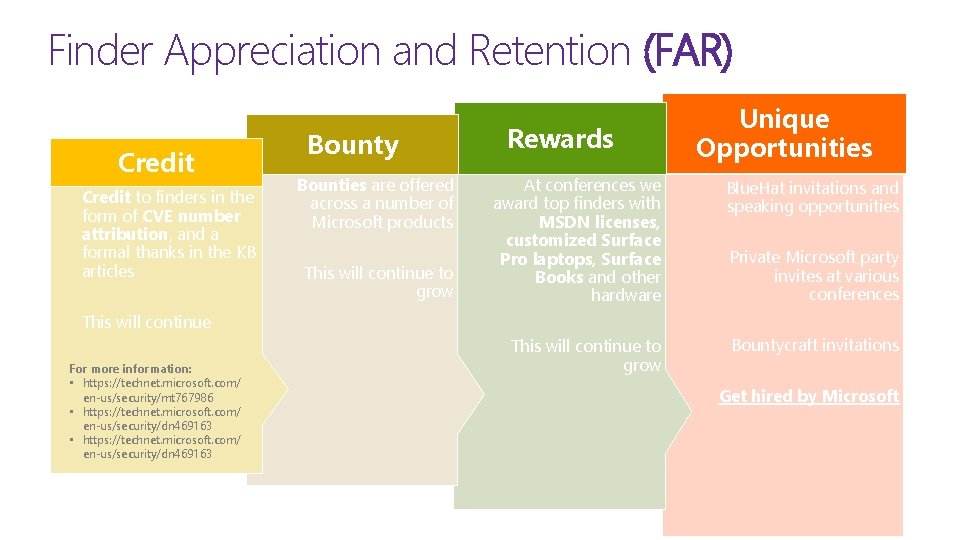
Finder Appreciation and Retention (FAR) Credit to finders in the form of CVE number attribution, and a formal thanks in the KB articles Bounty Bounties are offered across a number of Microsoft products This will continue to grow Rewards Unique Opportunities At conferences we award top finders with MSDN licenses, customized Surface Pro laptops, Surface Books and other hardware Blue. Hat invitations and speaking opportunities This will continue to grow Bountycraft invitations Private Microsoft party invites at various conferences This will continue For more information: • https: //technet. microsoft. com/ en-us/security/mt 767986 • https: //technet. microsoft. com/ en-us/security/dn 469163 Get hired by Microsoft
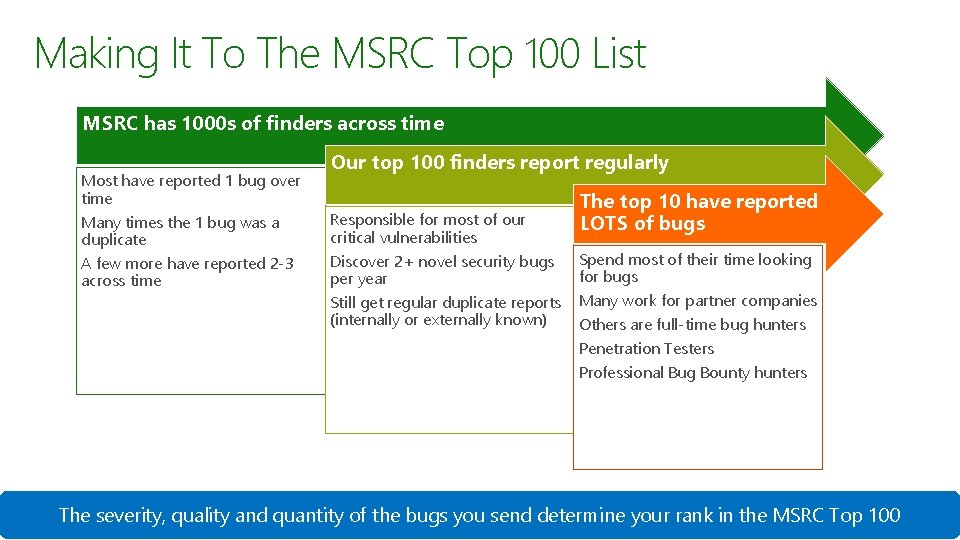
Making It To The MSRC Top 100 List MSRC has 1000 s of finders across time Our top 100 finders report regularly Most have reported 1 bug over time Many times the 1 bug was a duplicate Responsible for most of our critical vulnerabilities A few more have reported 2 -3 across time Discover 2+ novel security bugs per year Still get regular duplicate reports (internally or externally known) The top 10 have reported LOTS of bugs Spend most of their time looking for bugs Many work for partner companies Others are full-time bug hunters Penetration Testers Professional Bug Bounty hunters The severity, quality and quantity of the bugs you send determine your rank in the MSRC Top 100

Now we’re running, what are the rules of the game? • CVD : Coordinated Vulnerability Disclosure • Keep customers secure by maintaining the confidentiality of the vulnerability report to MSRC. • You can submit exploits to us up to 90 days after sending us the vulnerability and can still claim the full reward • If you wish to discuss the vulnerability publically or blog about it, please wait till it has been fixed and patches have been released to customers. • Preferably, 30 days after it has been patched. This gives customers enough time to take the patch • Never publish any exploit code (please ) • We are happy to provide technically review to any talks, white papers or blogs you are publishing
Take Action 1. Visit https: //aka. ms/Bug. Bounty for a current list of active bounties 2. Identify the bounty you want to go after and start hacking away at it 3. Report your findings to secure@microsoft. com • Describe the bug and how you exploit it • Provide a Proof of Concept (Po. C) • For complicated bugs (software) provide a white paper or detailed write up • If it’s a high quality report, you get larger bounties • If it has greater impact to Microsoft, you get larger bounties 4. Give us your name and a good email to reach you at 5. Encrypt with our public key (if it’s a Po. C or working exploit) 6. For eligible bounty cases, GET PAID!
Recap
- Slides: 53