Access Control Lists CSCI 283 172 Fall 2006
- Slides: 27
Access Control Lists CSCI 283 -172 Fall 2006 GWU Sources: Memon’s notes, Brooklyn Poly Bishop’s Text, Chapter 15 Bishop’s slides, Chapter 15 Text by Pfleeger and Pfleeger, Chapter 4 CS 283 -172/Fall 06/GWU/Vora Many slides from Matt Bishop's slide set
Access Control Mechanisms • • • Access Control Matrix Access Control List Capability based access control Lock and Key based access control. Rings-based access control 10/30/2021 CS 283 -172/Fall 06/GWU/Vora Many slides from Matt Bishop's slide set 2
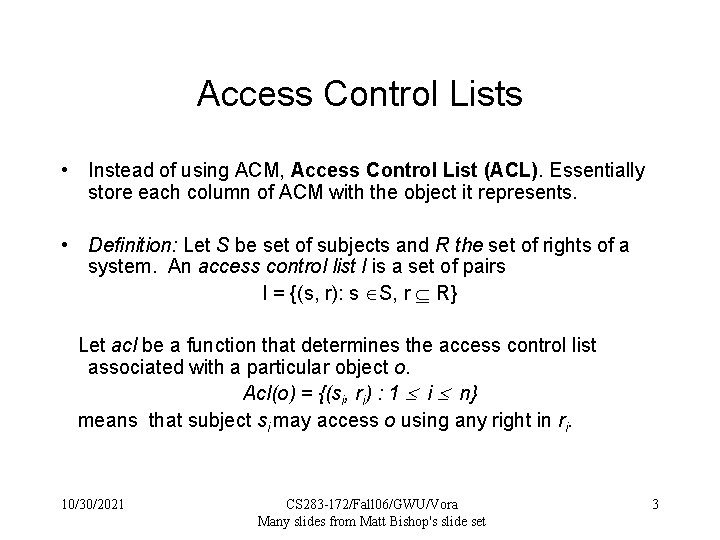
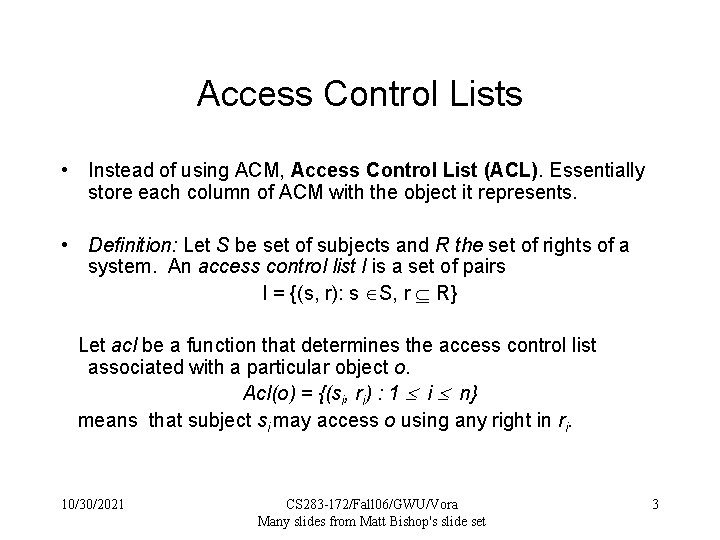
Access Control Lists • Instead of using ACM, Access Control List (ACL). Essentially store each column of ACM with the object it represents. • Definition: Let S be set of subjects and R the set of rights of a system. An access control list l is a set of pairs l = {(s, r): s S, r R} Let acl be a function that determines the access control list associated with a particular object o. Acl(o) = {(si, ri) : 1 i n} means that subject si may access o using any right in ri. 10/30/2021 CS 283 -172/Fall 06/GWU/Vora Many slides from Matt Bishop's slide set 3
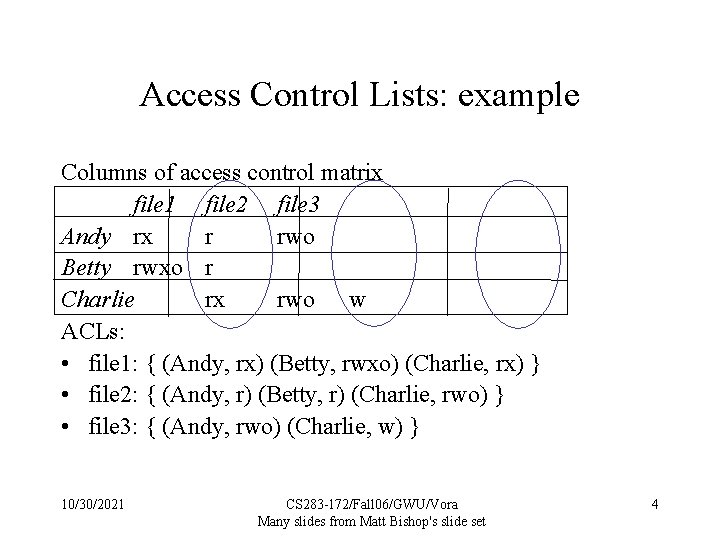
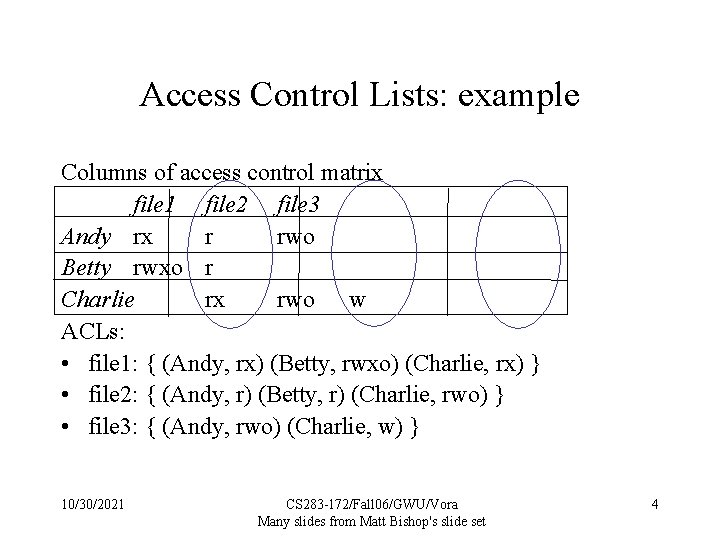
Access Control Lists: example Columns of access control matrix file 1 file 2 file 3 Andy rx r rwo Betty rwxo r Charlie rx rwo w ACLs: • file 1: { (Andy, rx) (Betty, rwxo) (Charlie, rx) } • file 2: { (Andy, r) (Betty, r) (Charlie, rwo) } • file 3: { (Andy, rwo) (Charlie, w) } 10/30/2021 CS 283 -172/Fall 06/GWU/Vora Many slides from Matt Bishop's slide set 4
Abbreviated ACL’s • Although same amount of storage, it is now distributed. • To further reduce storage, one can abbreviate ACL’s as in UNIX. • One can also assign default access to groups of subjects as well as specific rights to individual subjects. – Two ways of doing this: 1) What is not prohibited is permitted 2) What is not permitted is prohibited. Latter always better!! 10/30/2021 CS 283 -172/Fall 06/GWU/Vora Many slides from Matt Bishop's slide set 5
Default Permissions • Normal: if not named, no rights over file – Principle of Fail-Safe Defaults • If many subjects, may use groups or wildcards in ACL – UNICOS: entries are (user, group, rights) • If user is in group, has rights over file • ‘*’ is wildcard for user, group – (holly, *, r): holly can read file regardless of her group – (*, gleep, w): anyone in group gleep can write file 10/30/2021 CS 283 -172/Fall 06/GWU/Vora Many slides from Matt Bishop's slide set 6
Accessing Files • User not in file’s ACL nor in any group named in file’s ACL: deny access • ACL entry denies user access: deny access • Take union of rights of all ACL entries giving user access: user has this set of rights over file 10/30/2021 CS 283 -172/Fall 06/GWU/Vora Many slides from Matt Bishop's slide set 7
Example - File Protection in Unix UNIX - allow read, write, execute, delete to each of the individual groups - owner, group, world. Difficult for users in different groups to share files, since each user may belong to exactly one group. rwx rwx owner group rest 10/30/2021 CS 283 -172/Fall 06/GWU/Vora Many slides from Matt Bishop's slide set 8
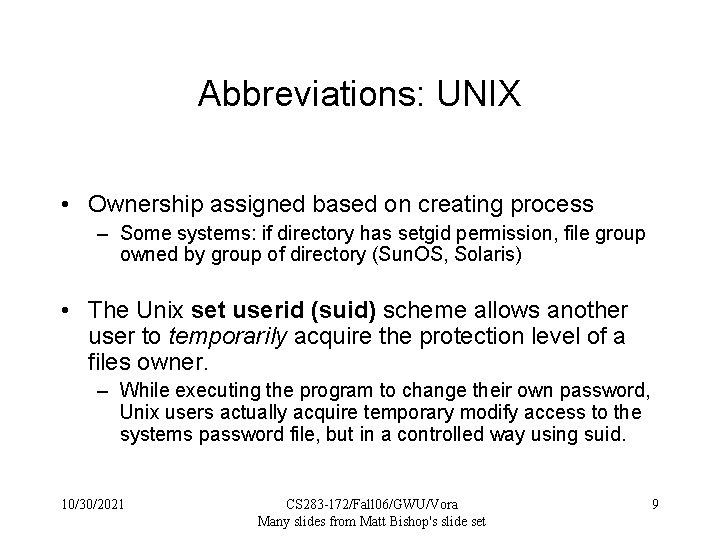
Abbreviations: UNIX • Ownership assigned based on creating process – Some systems: if directory has setgid permission, file group owned by group of directory (Sun. OS, Solaris) • The Unix set userid (suid) scheme allows another user to temporarily acquire the protection level of a files owner. – While executing the program to change their own password, Unix users actually acquire temporary modify access to the systems password file, but in a controlled way using suid. 10/30/2021 CS 283 -172/Fall 06/GWU/Vora Many slides from Matt Bishop's slide set 9
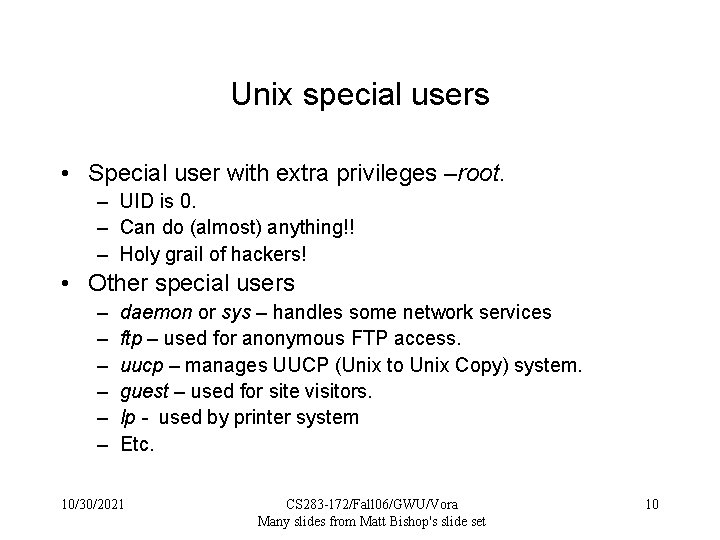
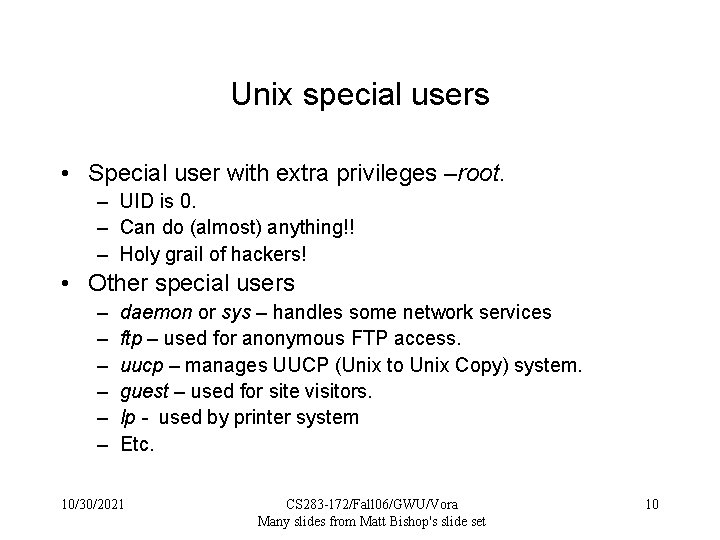
Unix special users • Special user with extra privileges –root. – UID is 0. – Can do (almost) anything!! – Holy grail of hackers! • Other special users – – – daemon or sys – handles some network services ftp – used for anonymous FTP access. uucp – manages UUCP (Unix to Unix Copy) system. guest – used for site visitors. lp - used by printer system Etc. 10/30/2021 CS 283 -172/Fall 06/GWU/Vora Many slides from Matt Bishop's slide set 10
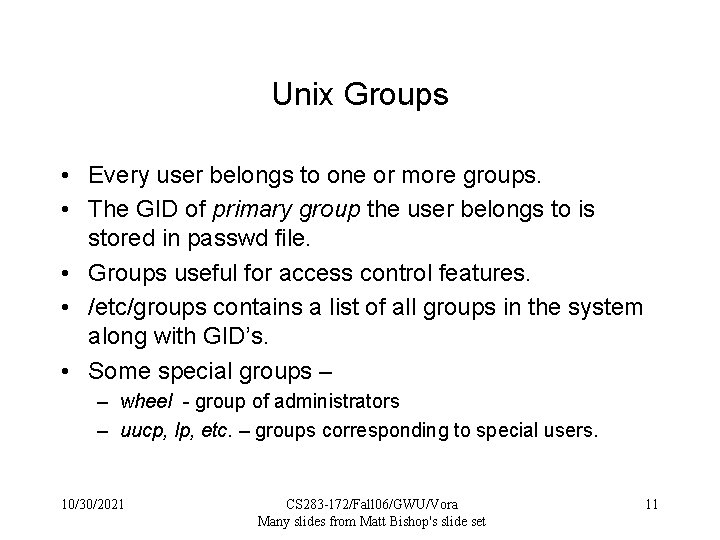
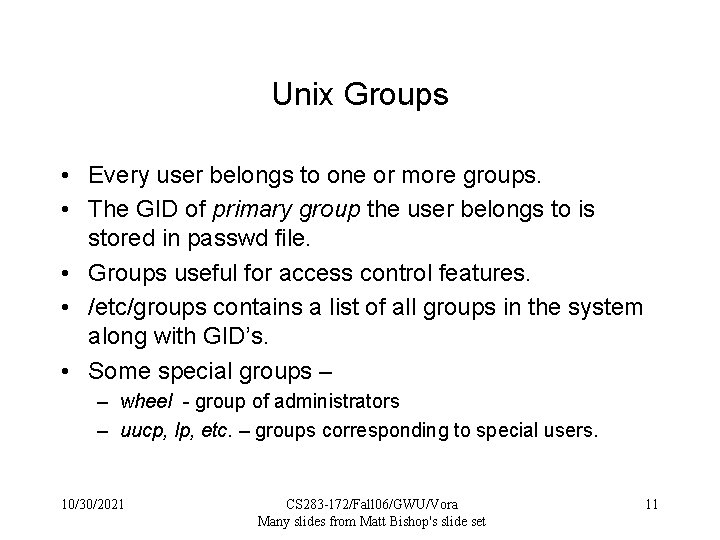
Unix Groups • Every user belongs to one or more groups. • The GID of primary group the user belongs to is stored in passwd file. • Groups useful for access control features. • /etc/groups contains a list of all groups in the system along with GID’s. • Some special groups – – wheel - group of administrators – uucp, lp, etc. – groups corresponding to special users. 10/30/2021 CS 283 -172/Fall 06/GWU/Vora Many slides from Matt Bishop's slide set 11
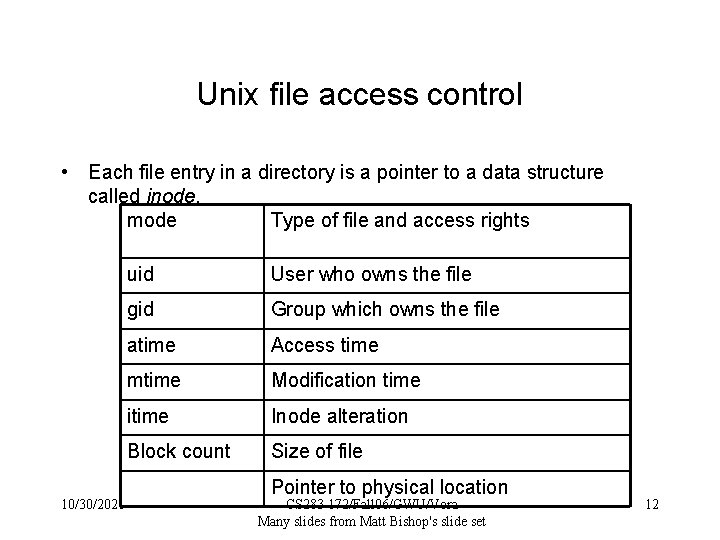
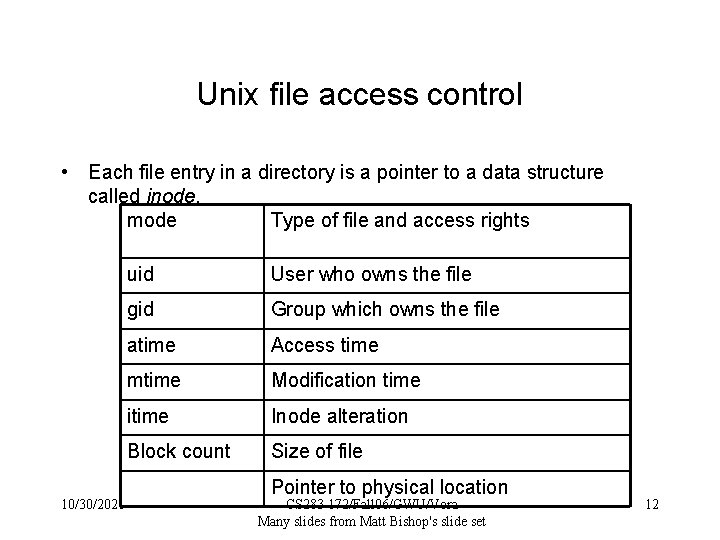
Unix file access control • Each file entry in a directory is a pointer to a data structure called inode. mode Type of file and access rights 10/30/2021 uid User who owns the file gid Group which owns the file atime Access time mtime Modification time itime Inode alteration Block count Size of file Pointer to physical location CS 283 -172/Fall 06/GWU/Vora Many slides from Matt Bishop's slide set 12
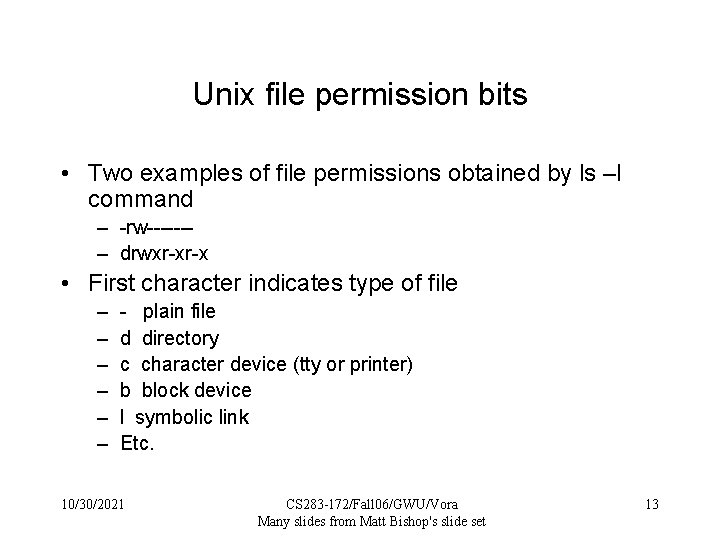
Unix file permission bits • Two examples of file permissions obtained by ls –l command – -rw------– drwxr-xr-x • First character indicates type of file – – – - plain file d directory c character device (tty or printer) b block device l symbolic link Etc. 10/30/2021 CS 283 -172/Fall 06/GWU/Vora Many slides from Matt Bishop's slide set 13
File permission bits (contd. ) • Next nine characters taken in groups of three indicate who can do what with the file – R – Permission to read – W – Permission to write – X – Permission to execute • The three classes of permission correspond respectively to – Owner – Group – Other 10/30/2021 CS 283 -172/Fall 06/GWU/Vora Many slides from Matt Bishop's slide set 14
File permission bits – special cases • File permission bits do not apply to symbolic links. • If you have x access but no r access you can execute the program without reading it (not on linux). • Execute permission in a directory means you can change to the directory. Secret Files! • File permission bits also commonly specified in octal notation. 0777 mean -rwxrwxrwx, 0600 means -r_x-----, etc. 10/30/2021 CS 283 -172/Fall 06/GWU/Vora Many slides from Matt Bishop's slide set 15
Umask and default permissions • umask (User file creation mode mask) is a four digit octal number used to determine file permissions for newly created files. • It defines permission you do not want to be given (the bit-wise complement of the permission you want a file to have by default). • 0666 – default mode means 0222 umask. • 0077 umask means … 0022 means … • Set up at log in time in environment variables. 10/30/2021 CS 283 -172/Fall 06/GWU/Vora Many slides from Matt Bishop's slide set 16
The suid bit • Sometimes unprivileged users must perform tasks that are privileged. – Change password thereby modify /etc/passwd. • UNIX allows certain programs to change UID to their owner when executed. – SUID programs – change UID to owner. – SGID programs – change GID to owners group. • ls –l command indicates if SUID or SGID – -rwsr-xr-x indicates SUID – -rwxr-sr-x indicates SGID 10/30/2021 CS 283 -172/Fall 06/GWU/Vora Many slides from Matt Bishop's slide set 17
Limitations of UNIX file permission system • Abbreviated ACL’s in general and UNIX in particular may not be flexible enough for many circumstances. • Consider the following example: – 5 users, Anne, Beth, Caroline, Della and Elizabeth. – Anne wants Beth to read her file and nothing else. – She wants Caroline to write – Della to only read and write – Elizabeth to only execute Above not possible with Unix file permission bits!! 10/30/2021 CS 283 -172/Fall 06/GWU/Vora Many slides from Matt Bishop's slide set 18
ACLs + Abbreviations • Augment abbreviated lists with ACLs – Intent is to shorten ACL • ACLs override abbreviations – Exact method varies • Example: IBM AIX – Base permissions are abbreviations, extended permissions are ACLs with user, group – ACL entries can add rights, but on deny, access is denied 10/30/2021 CS 283 -172/Fall 06/GWU/Vora Many slides from Matt Bishop's slide set 19
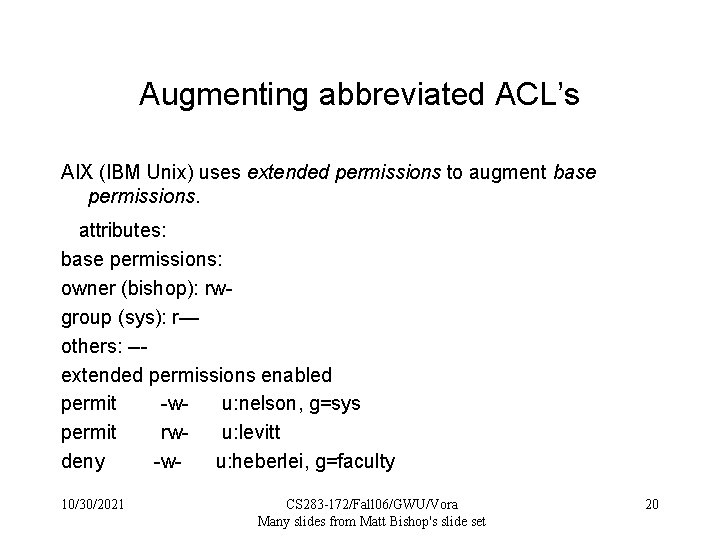
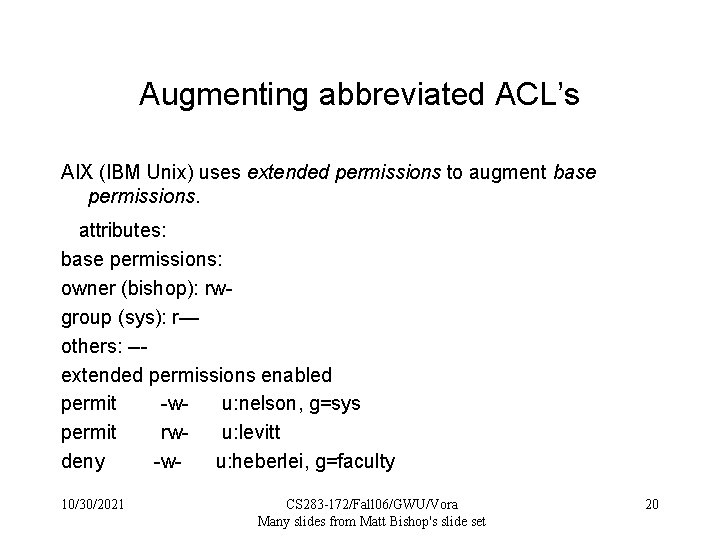
Augmenting abbreviated ACL’s AIX (IBM Unix) uses extended permissions to augment base permissions. attributes: base permissions: owner (bishop): rwgroup (sys): r— others: --extended permissions enabled permit -wu: nelson, g=sys permit rwu: levitt deny -wu: heberlei, g=faculty 10/30/2021 CS 283 -172/Fall 06/GWU/Vora Many slides from Matt Bishop's slide set 20
Issues to consider while designing an ACL based system • • • Which subject can modify an object in ACL? Does ACL apply to privileged user (root), if any? Does ACL support groups or wildcards? How are contradictory permissions handled? If default permissions allowed, do ACL’s modify it? Or is default used only when subject not explicitly mentioned in ACL? 10/30/2021 CS 283 -172/Fall 06/GWU/Vora Many slides from Matt Bishop's slide set 21
ACL Modification • Who can do this? – Creator is given own right that allows this – System R provides a grant modifier (like a copy flag) allowing a right to be transferred, so ownership not needed • Transferring right to another modifies ACL • Do ACLs apply to privileged users (root)? – Solaris: abbreviated lists do not, but full-blown ACL entries do – Other vendors: varies 10/30/2021 CS 283 -172/Fall 06/GWU/Vora Many slides from Matt Bishop's slide set 22
Groups and Wildcards Classic form: no; in practice, usually – AIX: base perms gave group sys read only permit -w- u: heidi, g=sys line adds write permission for heidi when in that group – UNICOS: • holly : gleep : r – user holly in group gleep can read file • holly : * : r – user holly in any group can read file • * : gleep : r – any user in group gleep can read file 10/30/2021 CS 283 -172/Fall 06/GWU/Vora Many slides from Matt Bishop's slide set 23
Conflicts • Deny access if any entry would deny access – AIX: if any entry denies access, regardless or rights given so far, access is denied • Apply first entry matching subject – Cisco routers: run packet through access control rules (ACL entries) in order; on a match, stop, and forward the packet; if no matches, deny • Note default is deny so honors principle of fail-safe defaults 10/30/2021 CS 283 -172/Fall 06/GWU/Vora Many slides from Matt Bishop's slide set 24
Handling Default Permissions • Apply ACL entry, and if none use defaults – Cisco router: apply matching access control rule, if any; otherwise, use default rule (deny) • Augment defaults with those in the appropriate ACL entry – AIX: extended permissions augment base permissions 10/30/2021 CS 283 -172/Fall 06/GWU/Vora Many slides from Matt Bishop's slide set 25
Revocation Question • How do you remove subject’s rights to a file? – Owner deletes subject’s entries from ACL, or rights from subject’s entry in ACL • What if ownership not involved? – Depends on system – System R: restore protection state to what it was before right was given • May mean deleting descendent rights too … 10/30/2021 CS 283 -172/Fall 06/GWU/Vora Many slides from Matt Bishop's slide set 26
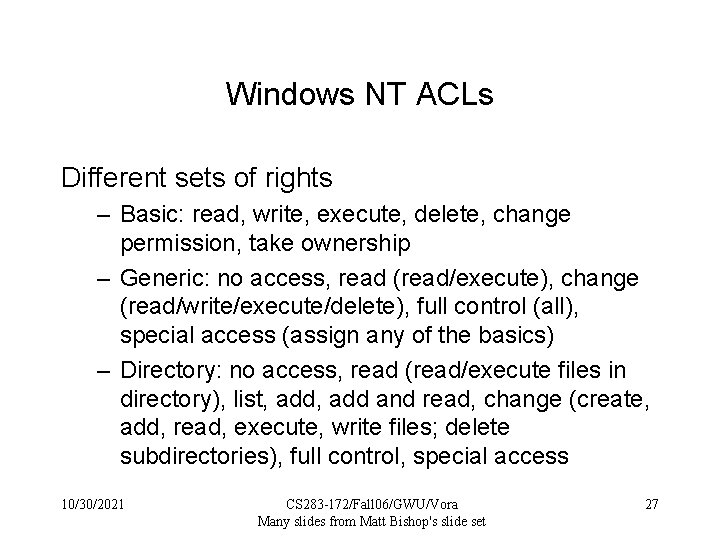
Windows NT ACLs Different sets of rights – Basic: read, write, execute, delete, change permission, take ownership – Generic: no access, read (read/execute), change (read/write/execute/delete), full control (all), special access (assign any of the basics) – Directory: no access, read (read/execute files in directory), list, add and read, change (create, add, read, execute, write files; delete subdirectories), full control, special access 10/30/2021 CS 283 -172/Fall 06/GWU/Vora Many slides from Matt Bishop's slide set 27