A SelfReference Watermarking Scheme Based on Wet Paper
A Self-Reference Watermarking Scheme Based on Wet Paper Coding Chair Professor Chin-Chen Chang (張真誠) n National Tsing Hua University n National Chung Cheng University n Feng Chia University http: //msn. iecs. fcu. edu. tw/~ccc
Outline u u u Introduction Related works Self-reference watermarking scheme Experimental results Conclusions 2
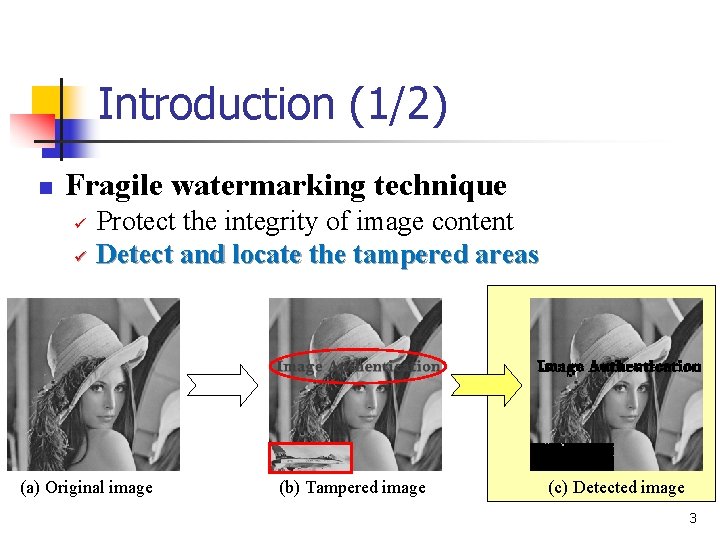
Introduction (1/2) n Fragile watermarking technique ü ü Protect the integrity of image content Detect and locate the tampered areas (a) Original image (b) Tampered image (c) Detected image 3
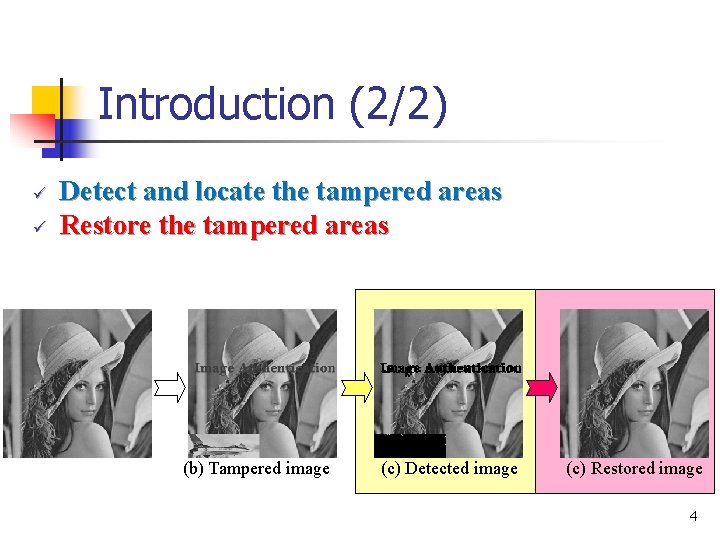
Introduction (2/2) ü ü Detect and locate the tampered areas Restore the tampered areas (b) Tampered image (c) Detected image (c) Restored image 4
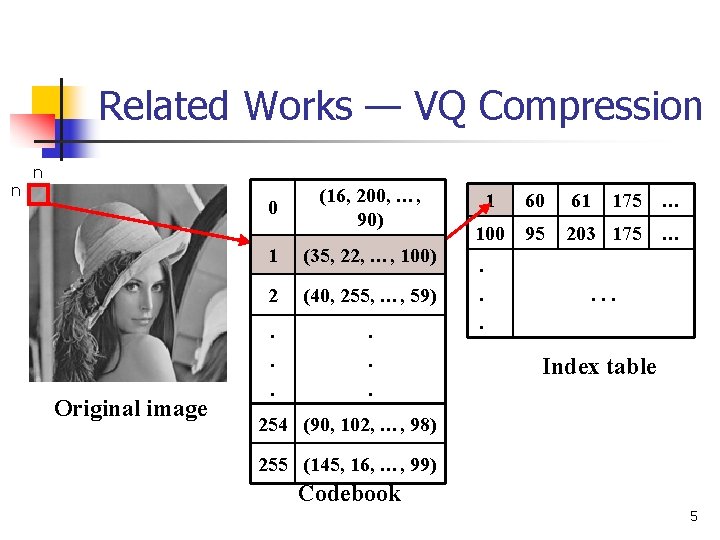
Related Works — VQ Compression n n 0 Original image (16, 200, …, 90) 1 (35, 22, …, 100) 2 (40, 255, …, 59) . . . 1 60 61 175 … 100 95 203 175 … . . . Index table 254 (90, 102, …, 98) 255 (145, 16, …, 99) Codebook 5
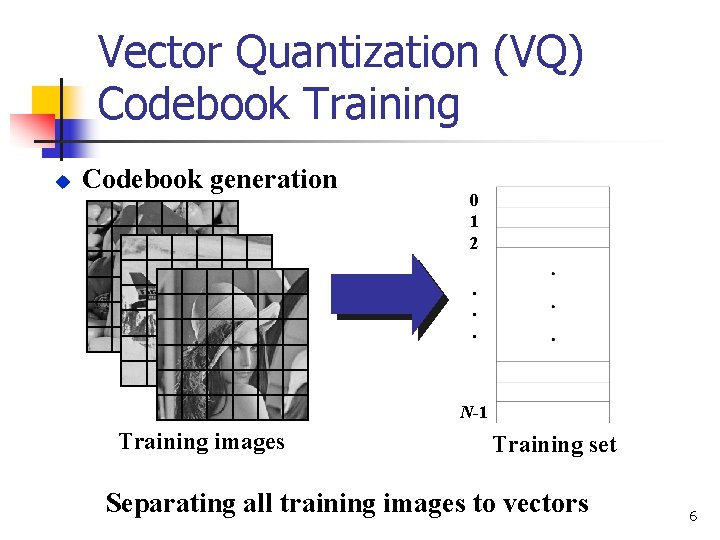
Vector Quantization (VQ) Codebook Training u Codebook generation 0 1 2. . . N-1 Training images Training set Separating all training images to vectors 6
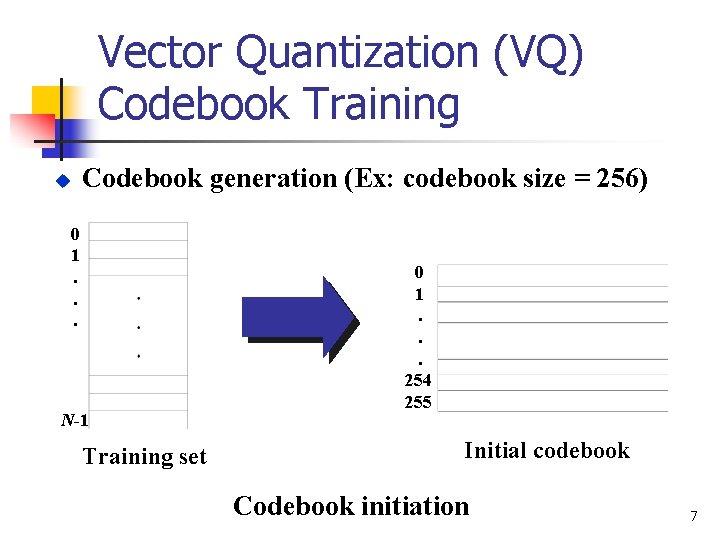
Vector Quantization (VQ) Codebook Training u Codebook generation (Ex: codebook size = 256) 0 1. . . N-1 Training set 0 1. . . 254 255 Initial codebook Codebook initiation 7
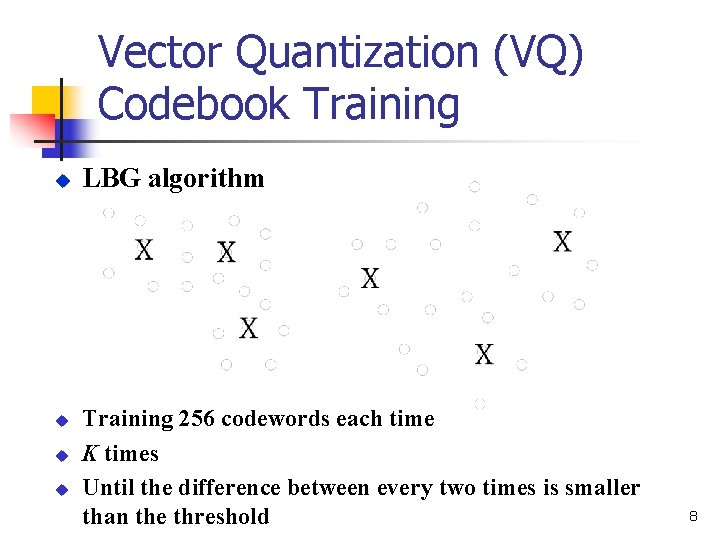
Vector Quantization (VQ) Codebook Training u u LBG algorithm Training 256 codewords each time K times Until the difference between every two times is smaller than the threshold 8
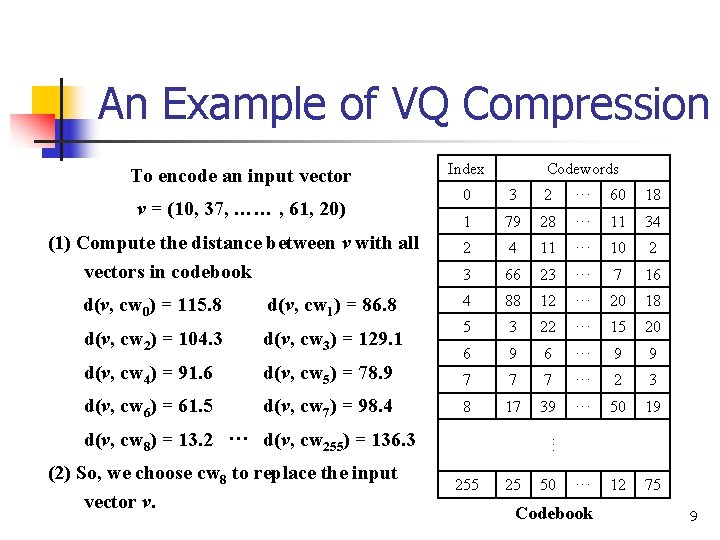
An Example of VQ Compression To encode an input vector v = (10, 37, …… , 61, 20) (1) Compute the distance between v with all vectors in codebook d(v, cw 0) = 115. 8 d(v, cw 1) = 86. 8 d(v, cw 2) = 104. 3 d(v, cw 3) = 129. 1 d(v, cw 4) = 91. 6 d(v, cw 5) = 78. 9 d(v, cw 6) = 61. 5 d(v, cw 7) = 98. 4 Index Codewords 0 3 2 ··· 60 18 1 79 28 ··· 11 34 2 4 11 ··· 10 2 3 66 23 ··· 7 16 4 88 12 ··· 20 18 5 3 22 ··· 15 20 6 9 6 ··· 9 9 7 7 7 ··· 2 3 8 17 39 ··· 50 19 255 25 50 ··· 12 75 (2) So, we choose cw 8 to replace the input vector v. ··· d(v, cw 8) = 13. 2 ··· d(v, cw 255) = 136. 3 Codebook 9
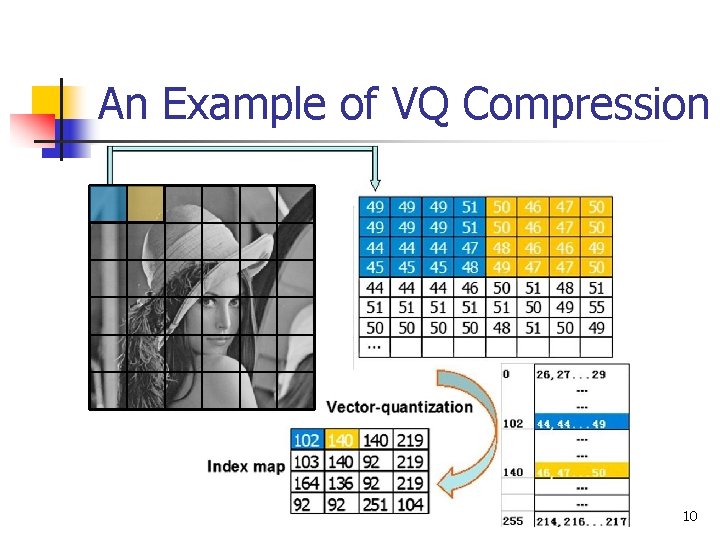
An Example of VQ Compression 10
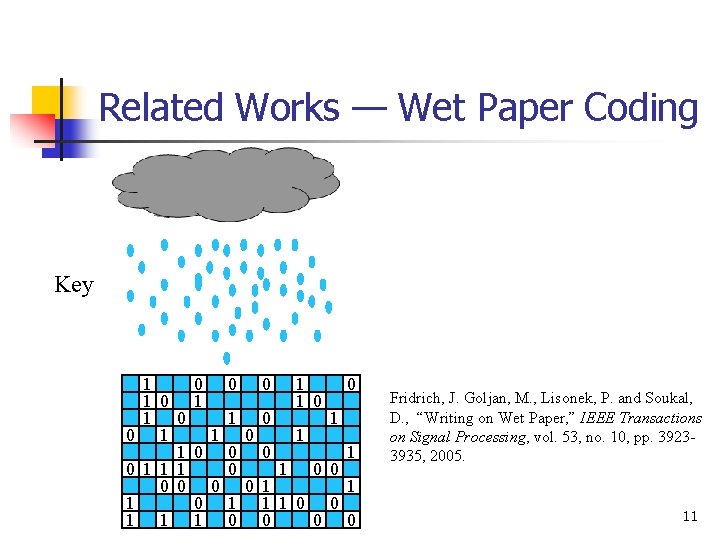
Related Works — Wet Paper Coding Key 1 0 0 1 0 1 0 0 0 1 1 1 1 0 0 0 1 1 1 0 0 0 Fridrich, J. Goljan, M. , Lisonek, P. and Soukal, D. , “Writing on Wet Paper, ” IEEE Transactions on Signal Processing, vol. 53, no. 10, pp. 39233935, 2005. 11
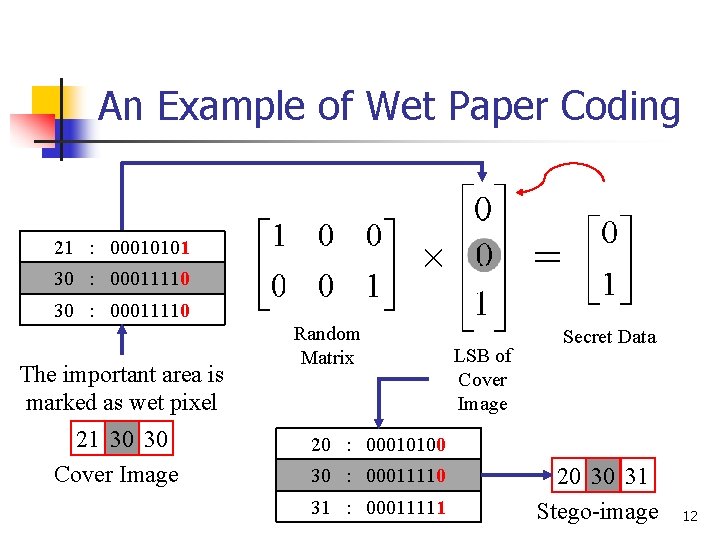
An Example of Wet Paper Coding ? × 21 : 00010101 30 : 00011110 = 30 : 00011110 The important area is marked as wet pixel 21 30 30 Cover Image Random Matrix LSB of Cover Image Secret Data 20 : 00010100 30 : 00011110 31 : 00011111 20 30 31 Stego-image 12
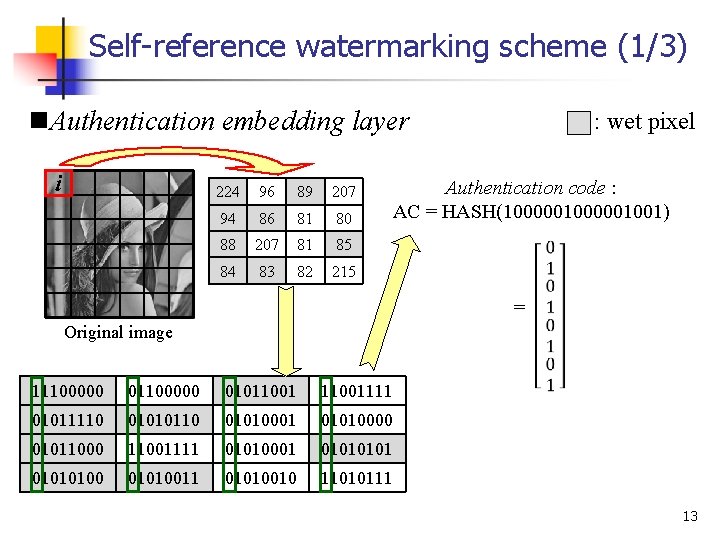
Self-reference watermarking scheme (1/3) n. Authentication embedding layer i 224 96 89 207 94 86 81 80 88 207 81 85 84 83 82 215 : wet pixel Authentication code : AC = HASH(1000001001) = Original image 11100000 01011001111 01011110 01010001 01010000 01011000 11001111 01010001 0101010011 01010010 11010111 13
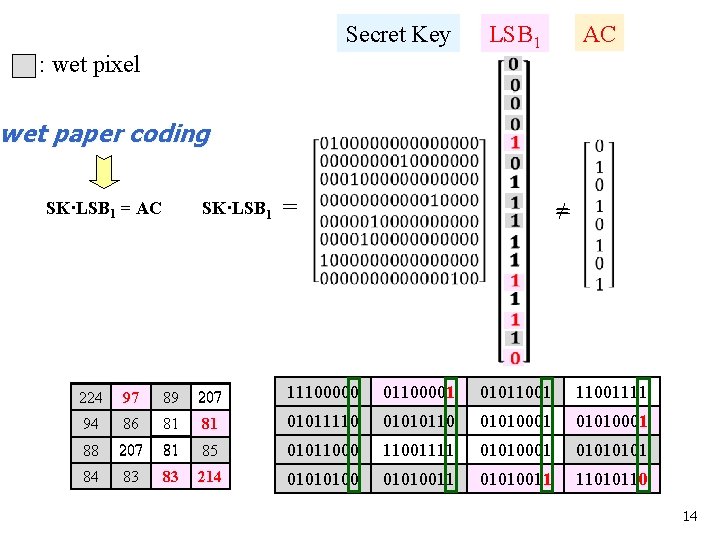
Secret Key : wet pixel LSB 1 AC wet paper coding SK·LSB 1 = AC SK·LSB 1 = ≠ = 224 96 97 89 207 11100000 01100001 01011001111 94 86 81 80 81 01011110 01010001 01010000 01010001 88 207 81 85 01011000 11001111 01010001 0101 84 83 82 83 215 214 0101010011 01010010 01010011 11010110 14
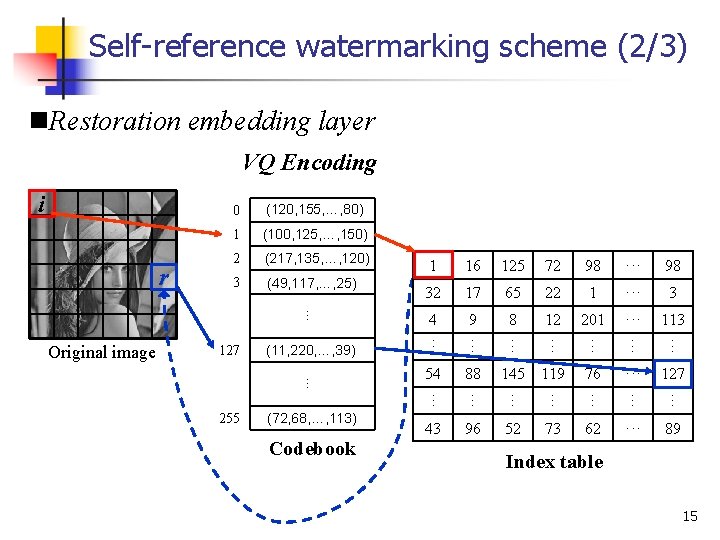
Self-reference watermarking scheme (2/3) n. Restoration embedding layer VQ Encoding i 1 (100, 125, …, 150) 2 (217, 135, …, 120) 3 (49, 117, …, 25) 3 4 9 8 12 201 ··· 113 (11, 220, …, 39) … 255 (72, 68, …, 113) Codebook 54 88 145 119 76 ··· 127 ··· ··· 1 ··· 22 ··· 65 ··· 17 ··· 32 ··· 98 ··· 72 ··· 125 ··· 16 ··· 127 1 ··· Original image (120, 155, …, 80) … r 0 43 96 52 73 62 ··· 89 Index table 15
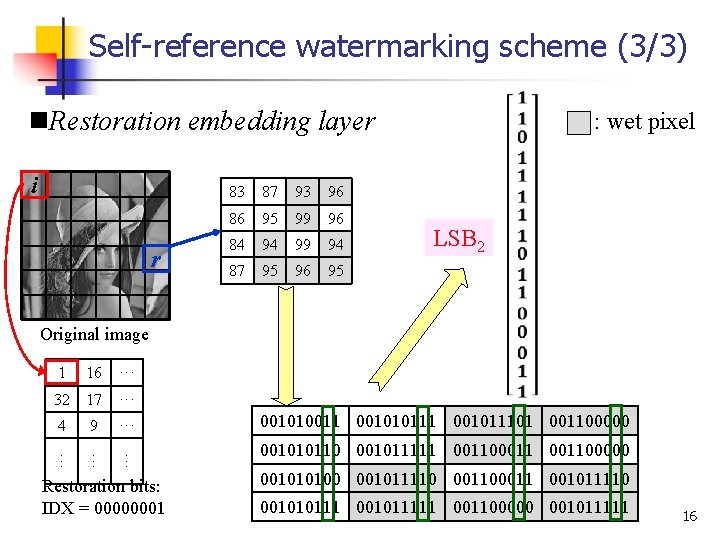
Self-reference watermarking scheme (3/3) n. Restoration embedding layer i r 83 87 93 96 86 95 99 96 84 94 99 94 87 95 96 95 : wet pixel LSB 2 Original image 1 16 ··· 32 17 ··· 4 9 ··· ··· Restoration bits: IDX = 00000001 001010011 001010111 001011101 001100000 001010110 001011111 001100000 001010100 001011110 001100011 001011110 001010111 001011111 001100000 001011111 16
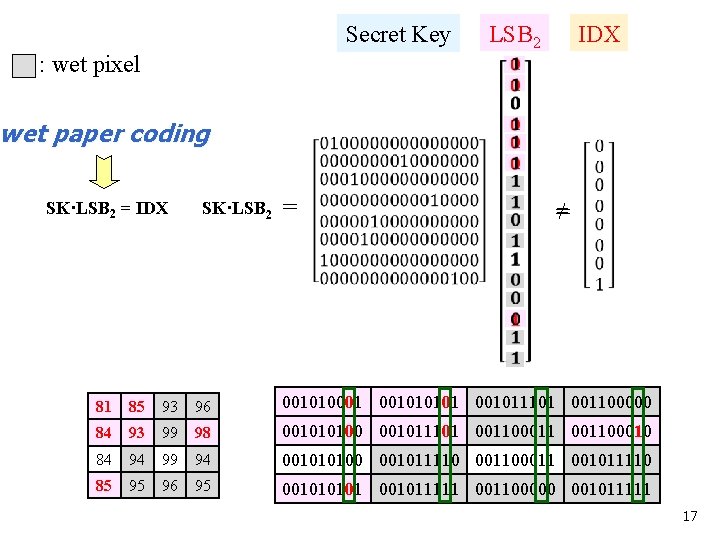
Secret Key : wet pixel LSB 2 IDX wet paper coding SK·LSB 2 = IDX SK·LSB 2 = ≠ = 83 81 87 85 93 96 001010011 001010111 001011101 001100000 001010001 86 84 95 93 99 96 98 001010110 001011101 001011111 001100010 001100000 001010100 84 94 99 94 001010100 001011110 001100011 001011110 87 85 95 96 95 001010111 001011111 001100000 001011111 00101 17
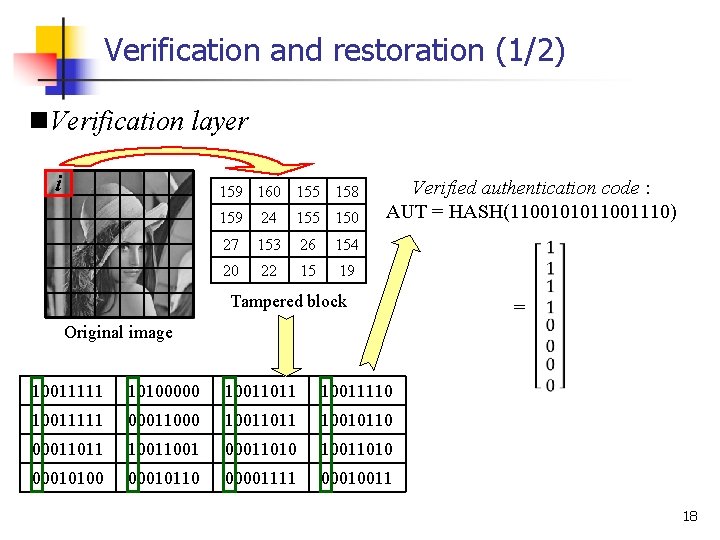
Verification and restoration (1/2) n. Verification layer i 159 160 155 158 159 24 155 150 27 153 26 154 20 22 15 19 Verified authentication code : AUT = HASH(1100101011001110) Tampered block = Original image 10011111 10100000 10011011 10011110 10011111 00011000 10011011 10010110 00011011 1001 00011010 10011010 00010100 00010110 00001111 00010011 18
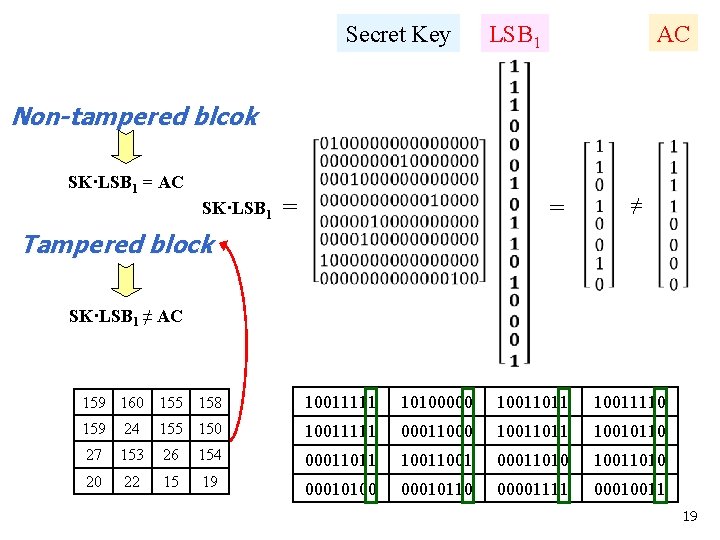
Secret Key LSB 1 AC Non-tampered blcok SK·LSB 1 = AC SK·LSB 1 = = ≠ Tampered block SK·LSB 1 ≠ AC 159 160 155 158 10011111 10100000 10011011 10011110 159 24 155 150 10011111 00011000 10011011 10010110 27 153 26 154 00011011 1001 00011010 10011010 20 22 15 19 00010100 00010110 00001111 00010011 19
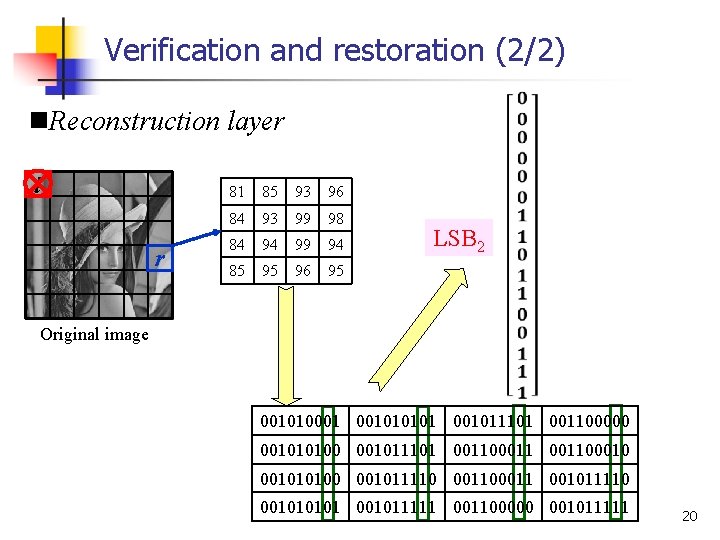
Verification and restoration (2/2) n. Reconstruction layer i r 81 85 93 96 84 93 99 98 84 94 99 94 85 95 96 95 LSB 2 Original image 001010001 001011101 001100000 001010100 001011101 00110001010100 001011110 001100011 001011110 001011111 001100000 001011111 20
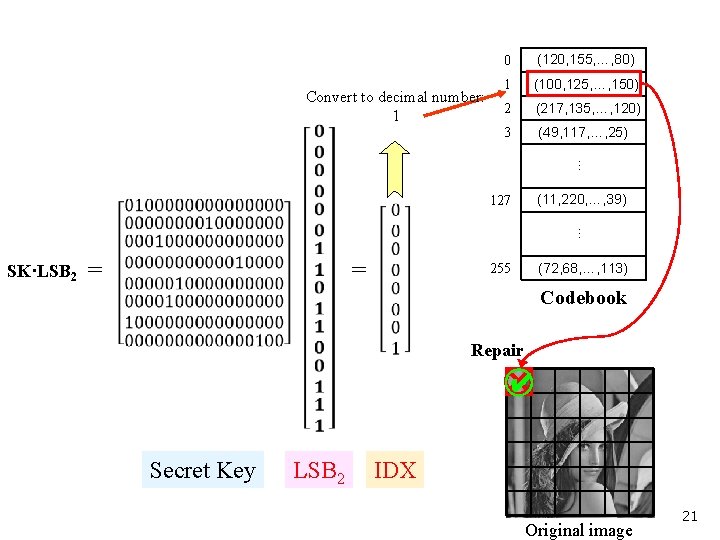
Convert to decimal number: 1 (120, 155, …, 80) 1 (100, 125, …, 150) 2 (217, 135, …, 120) 3 (49, 117, …, 25) 127 (11, 220, …, 39) 255 (72, 68, …, 113) … 0 … SK·LSB 2 = = Codebook Repair ○ ✔ Secret Key LSB 2 IDX Original image 21
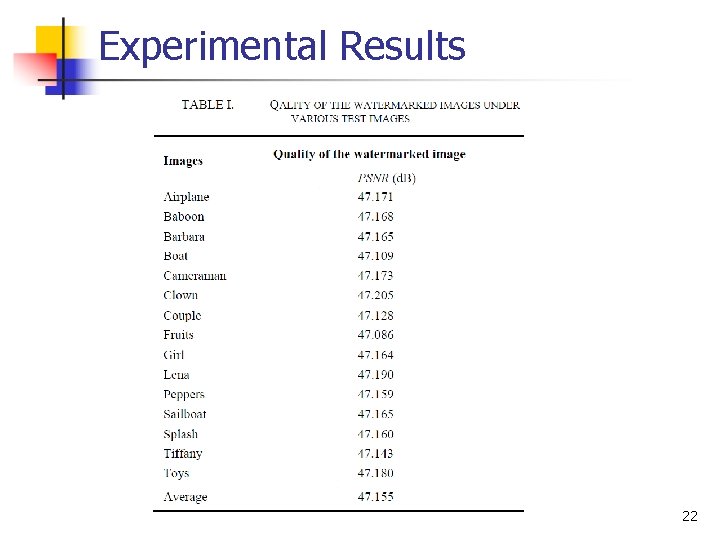
Experimental Results 22
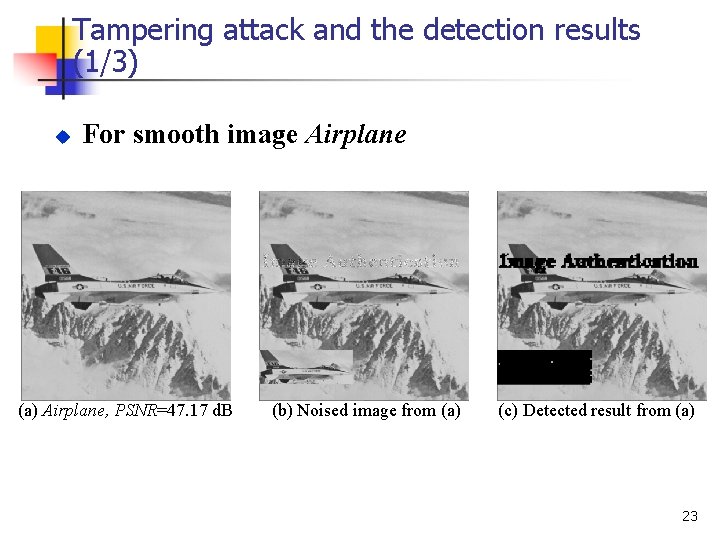
Tampering attack and the detection results (1/3) u For smooth image Airplane (a) Airplane, PSNR=47. 17 d. B (b) Noised image from (a) (c) Detected result from (a) 23
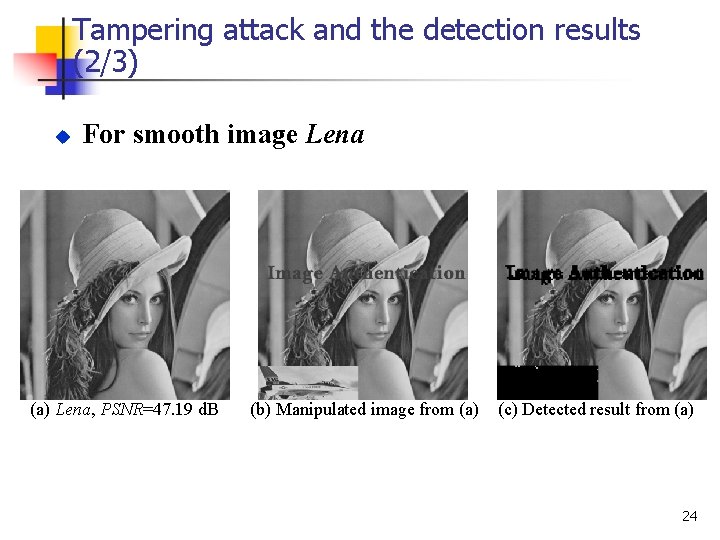
Tampering attack and the detection results (2/3) u For smooth image Lena (a) Lena, PSNR=47. 19 d. B (b) Manipulated image from (a) (c) Detected result from (a) 24
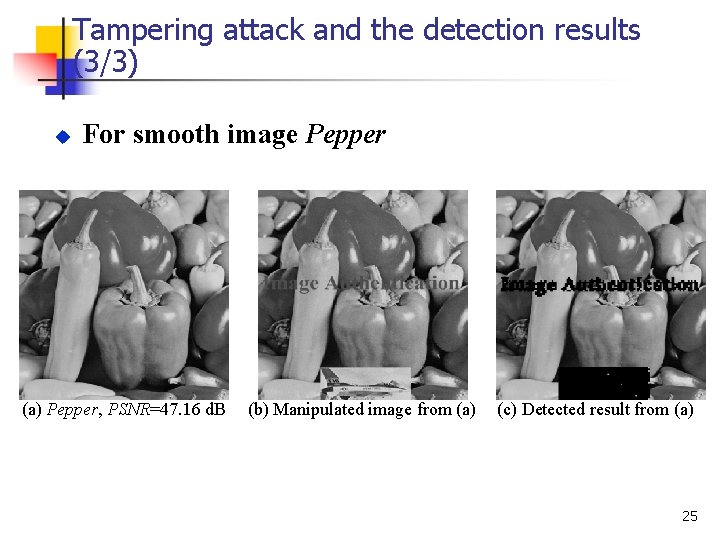
Tampering attack and the detection results (3/3) u For smooth image Pepper (a) Pepper, PSNR=47. 16 d. B (b) Manipulated image from (a) (c) Detected result from (a) 25
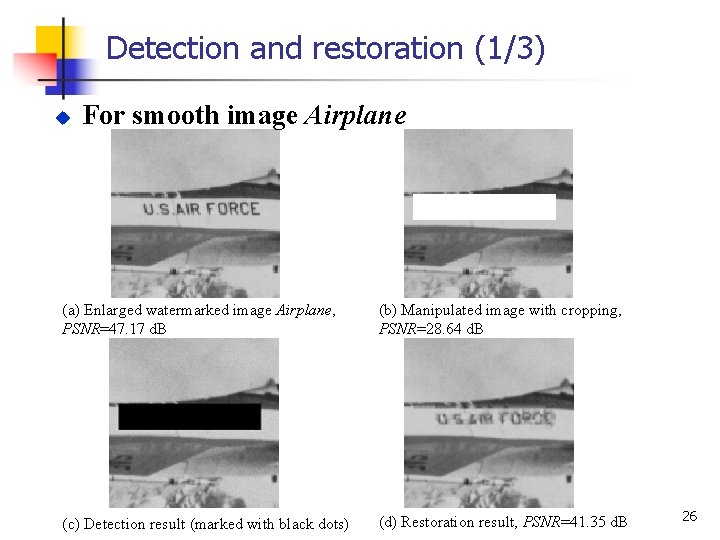
Detection and restoration (1/3) u For smooth image Airplane (a) Enlarged watermarked image Airplane, PSNR=47. 17 d. B (b) Manipulated image with cropping, PSNR=28. 64 d. B (c) Detection result (marked with black dots) (d) Restoration result, PSNR=41. 35 d. B 26
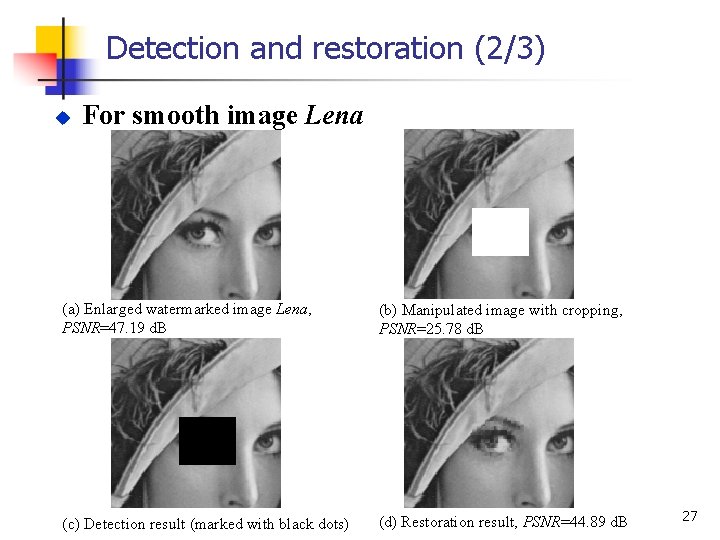
Detection and restoration (2/3) u For smooth image Lena (a) Enlarged watermarked image Lena, PSNR=47. 19 d. B (b) Manipulated image with cropping, PSNR=25. 78 d. B (c) Detection result (marked with black dots) (d) Restoration result, PSNR=44. 89 d. B 27
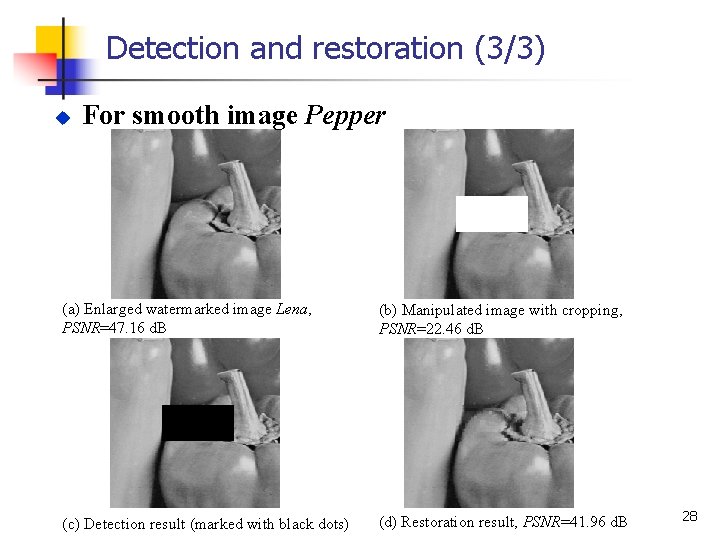
Detection and restoration (3/3) u For smooth image Pepper (a) Enlarged watermarked image Lena, PSNR=47. 16 d. B (b) Manipulated image with cropping, PSNR=22. 46 d. B (c) Detection result (marked with black dots) (d) Restoration result, PSNR=41. 96 d. B 28
Conclusions ü ü Propose a self-reference watermarking approach Utilize VQ to achieve the reconstruction data with high compression rate ü Using wet-paper coding to improve the security ü Detect and locate the tampered regions sensitively ü Reconstruct the invalid regions with satisfactory quality ü Protect the integrity of image content 29
- Slides: 29