1 Digital Data Communications Techniques Data and Computer
- Slides: 39
1 Digital Data Communications Techniques Data and Computer Communications by William Stallings Eighth Edition Networks and Communication Department Click to 6 edit Master subtitle style Chapter
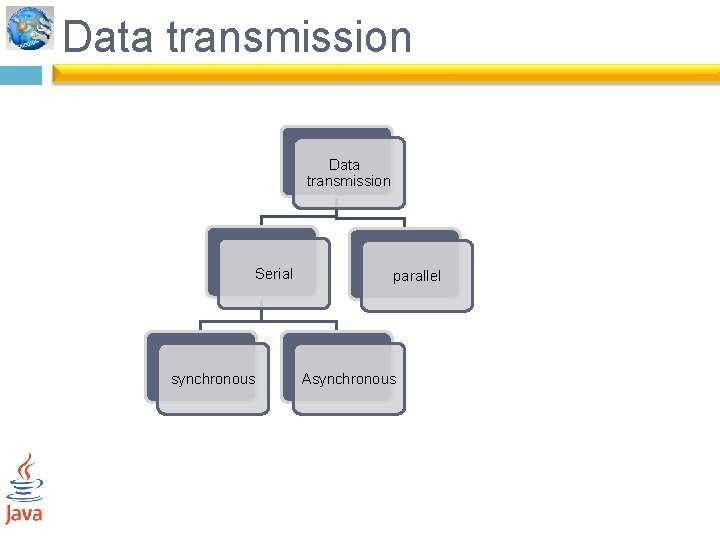
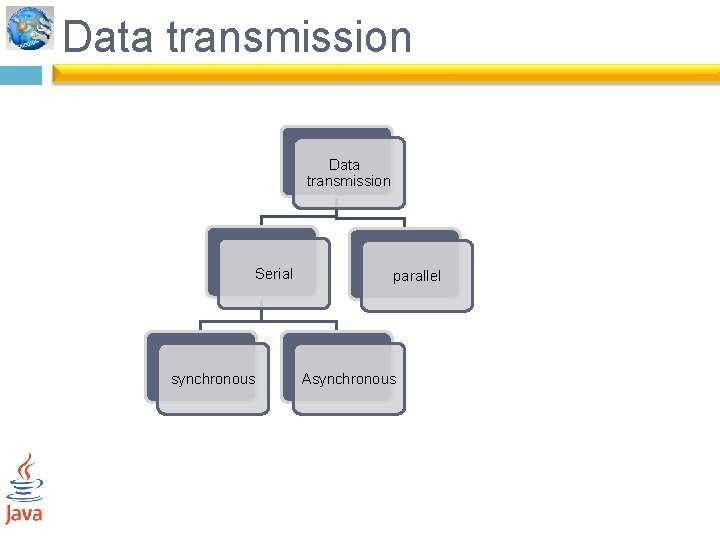
Data transmission Serial synchronous parallel Asynchronous
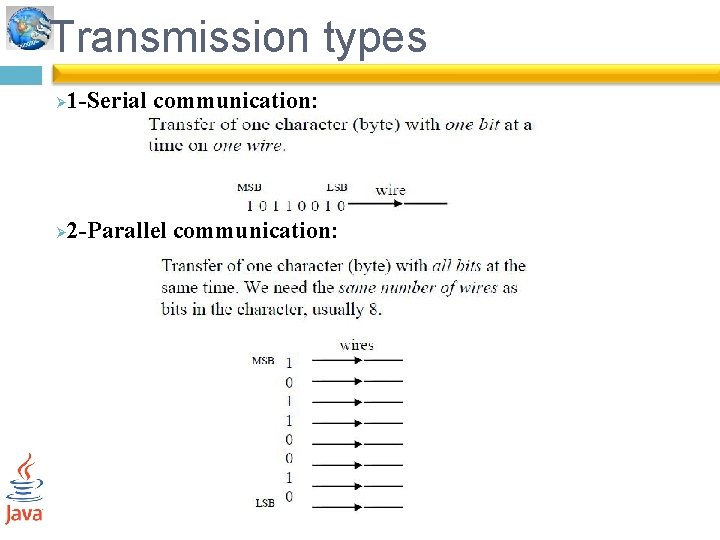
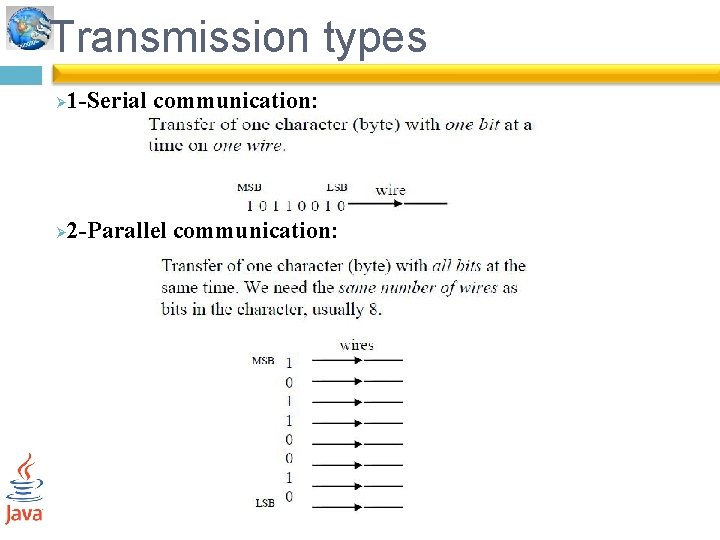
Transmission types Ø 1 -Serial communication: Ø 2 -Parallel communication:
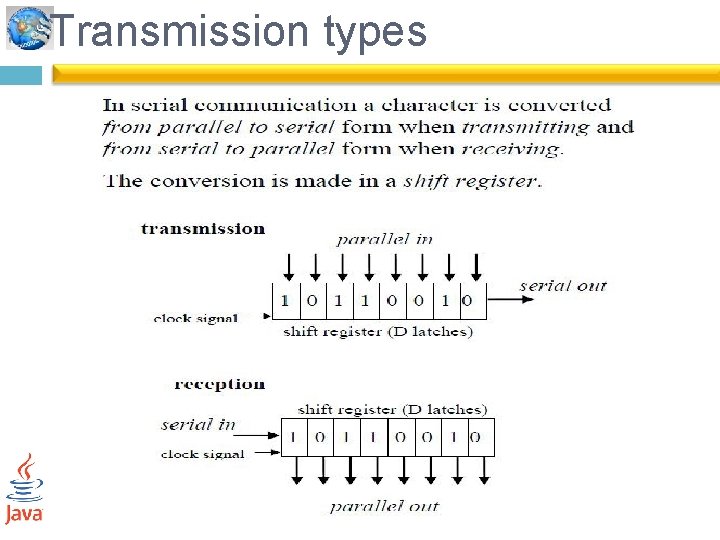
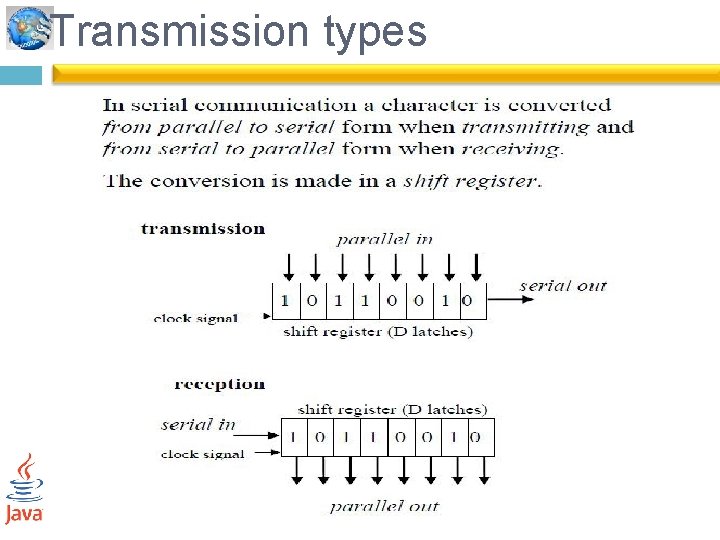
Transmission types
• One of the most fundamental requirements is synchronization. • The receiver must know the rate at which bits are being received so that it can sample the line at appropriate intervals to determine the value of each received bit. • Two techniques are in common use for this purpose : asynchronous and synchronous transmission.
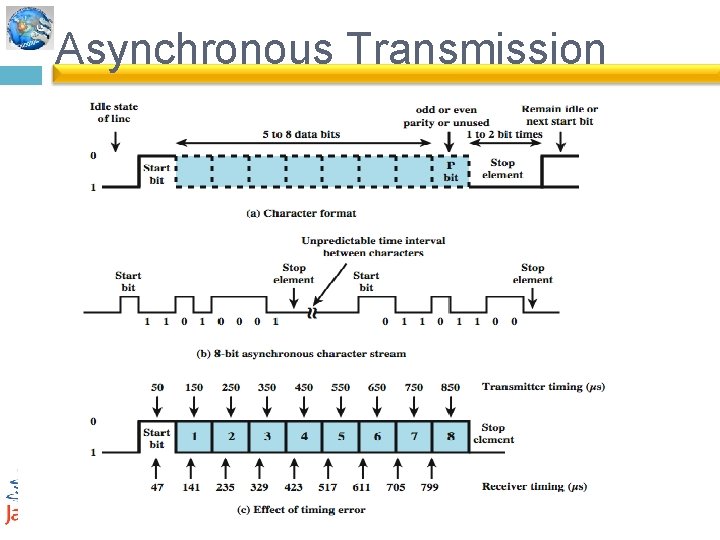
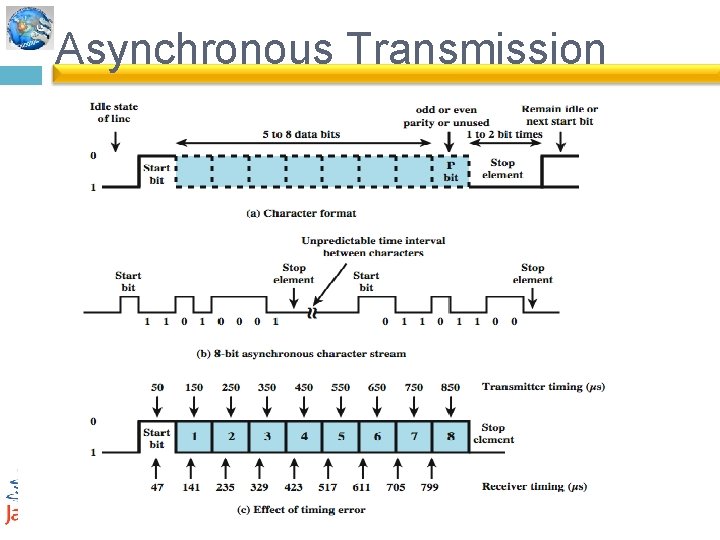
Asynchronous Transmission • data are transmitted one character at a time. • When no character is being transmitted, the line between transmitter and receiver is in an idle state (binary 1 level). • The beginning of a character is signaled by a start bit with a value of binary 0. • followed by the 5 to 8 bits that actually make up the character. • The bits of the character are transmitted beginning with the least significant bit. • Then the data bits are usually followed by a parity bit, set by the transmitter , The receiver uses this bit for error detection. • The final element is a stop element, which is a binary 1.
Asynchronous Transmission
Asynchronous - Behavior simple Øcheap Øgood for data with large gaps ( overhead could be reduced by sending larger blocks of bits between the start bit and stop element) Ø
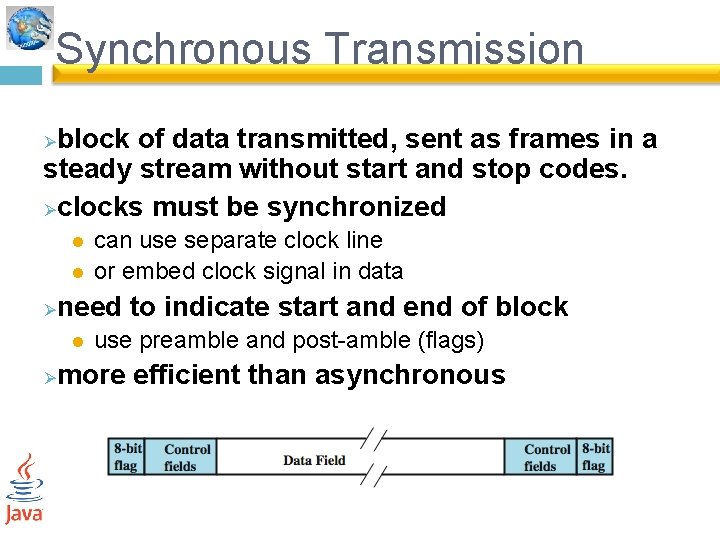
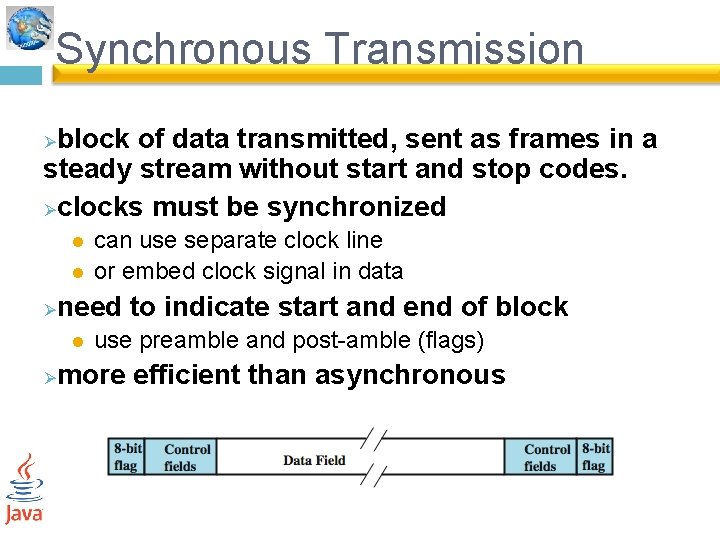
Synchronous Transmission block of data transmitted, sent as frames in a steady stream without start and stop codes. Øclocks must be synchronized Ø l l Ø need to indicate start and end of block l Ø can use separate clock line or embed clock signal in data use preamble and post-amble (flags) more efficient than asynchronous
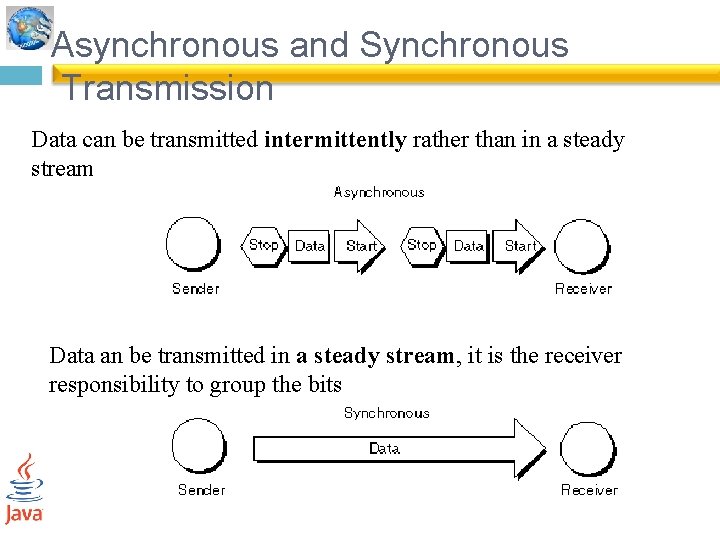
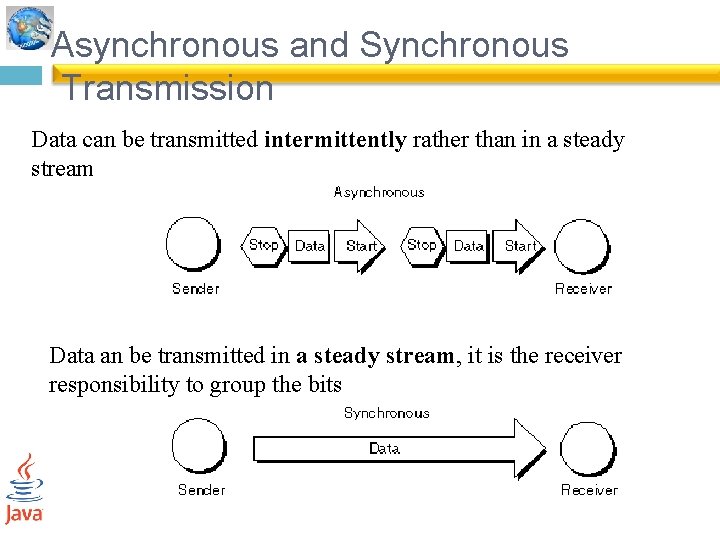
Asynchronous and Synchronous Transmission Data can be transmitted intermittently rather than in a steady stream Data an be transmitted in a steady stream, it is the receiver responsibility to group the bits
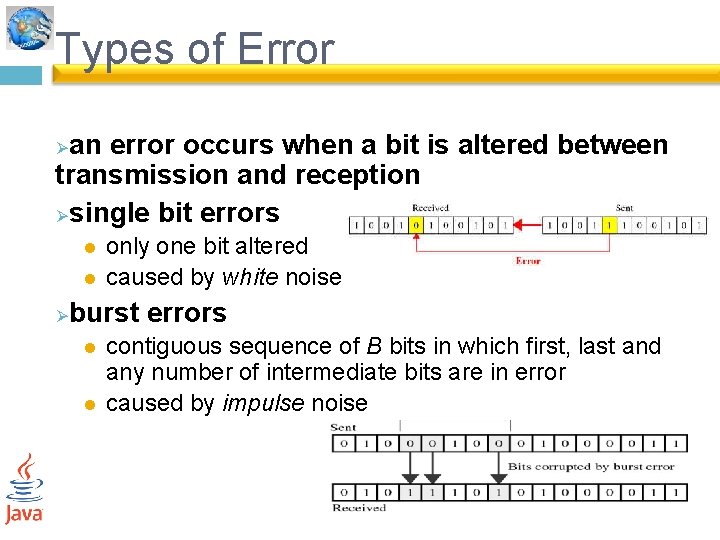
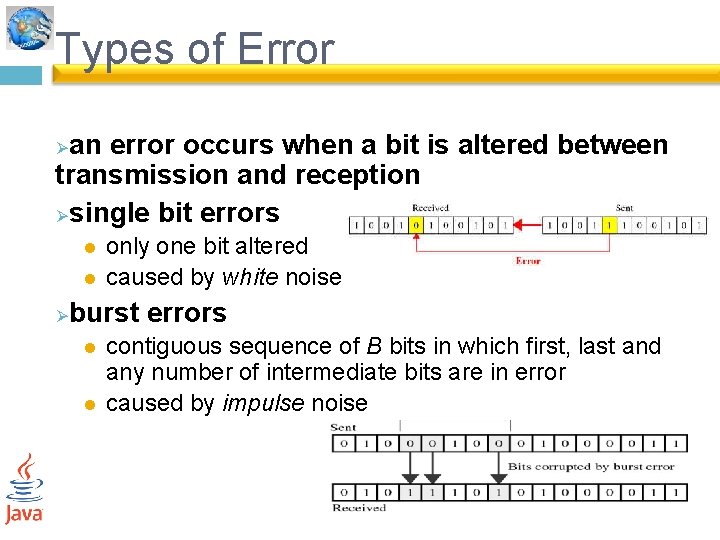
Types of Error an error occurs when a bit is altered between transmission and reception Øsingle bit errors Ø l l Ø only one bit altered caused by white noise burst errors l l contiguous sequence of B bits in which first, last and any number of intermediate bits are in error caused by impulse noise
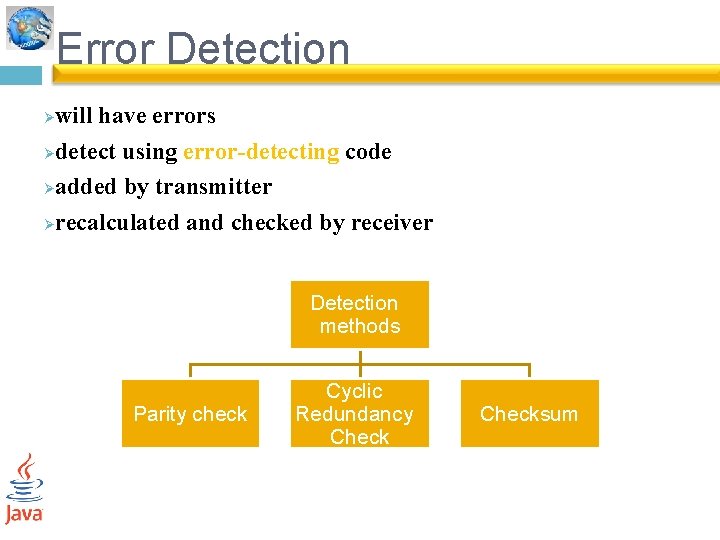
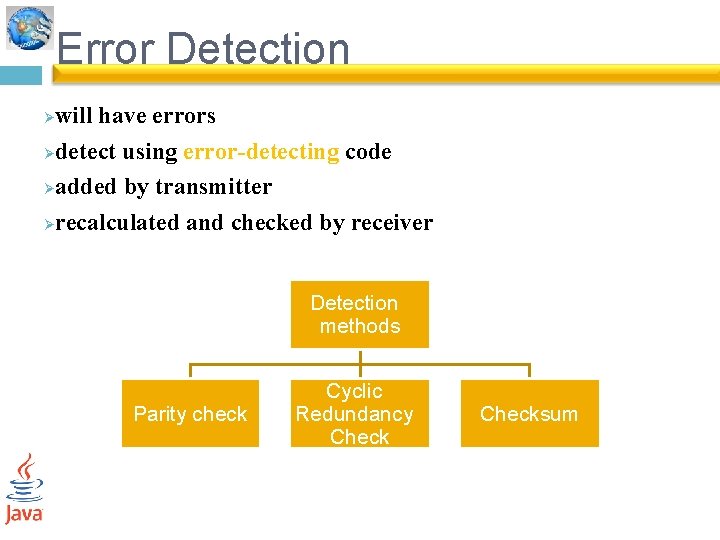
Error Detection will have errors Ødetect using error-detecting code Øadded by transmitter Ørecalculated and checked by receiver Ø Detection methods Parity check Cyclic Redundancy Checksum
Parity check 1 - Simple a parity bit (extra bit) is added to the end of a block of data so that character has an even number of 1 s (even parity) or an odd number of 1 s (odd parity).
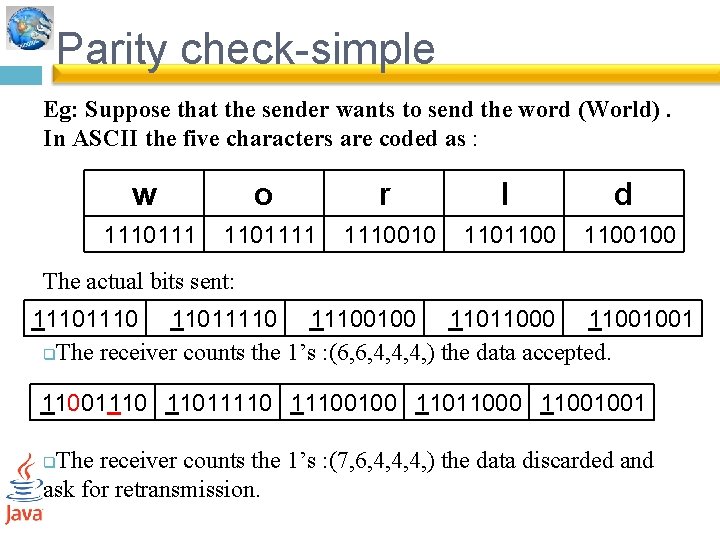
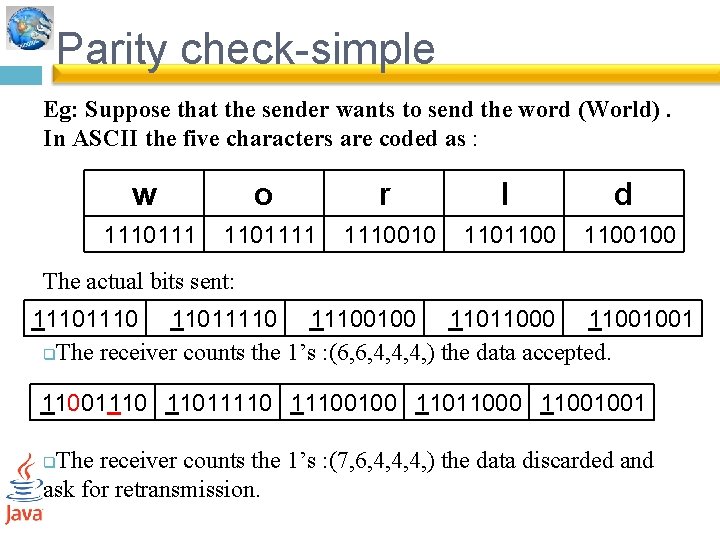
Parity check-simple Eg: Suppose that the sender wants to send the word (World). In ASCII the five characters are coded as : w o r l d 11101111 1110010 1101100100 The actual bits sent: 1110 110111100100 11011000 11001001 q. The receiver counts the 1’s : (6, 6, 4, 4, 4, ) the data accepted. 11001110 110111100100 11011000 11001001 The receiver counts the 1’s : (7, 6, 4, 4, 4, ) the data discarded and ask for retransmission. q
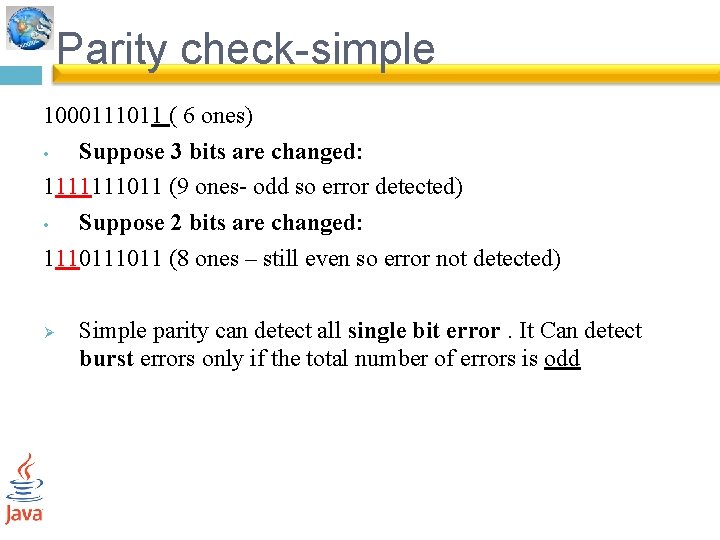
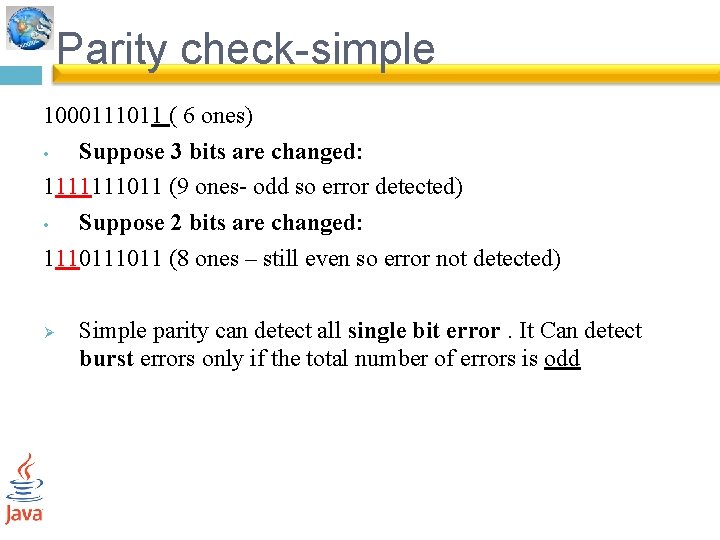
Parity check-simple 1000111011 ( 6 ones) • Suppose 3 bits are changed: 1111111011 (9 ones- odd so error detected) • Suppose 2 bits are changed: 111011 (8 ones – still even so error not detected) Ø Simple parity can detect all single bit error. It Can detect burst errors only if the total number of errors is odd
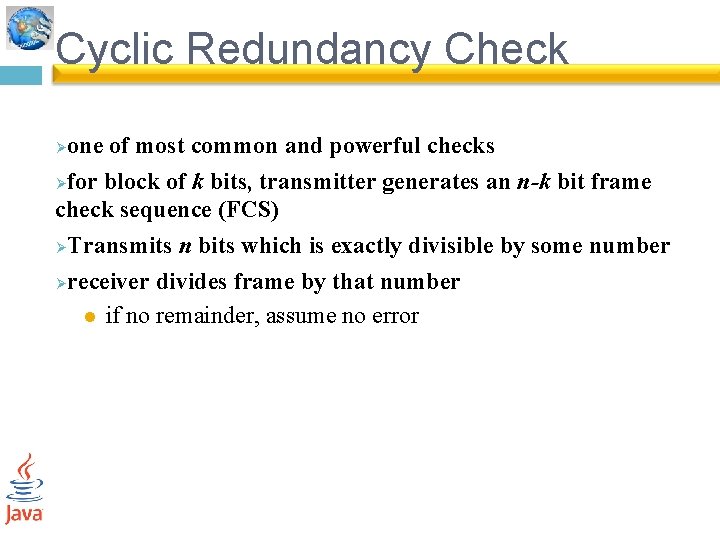
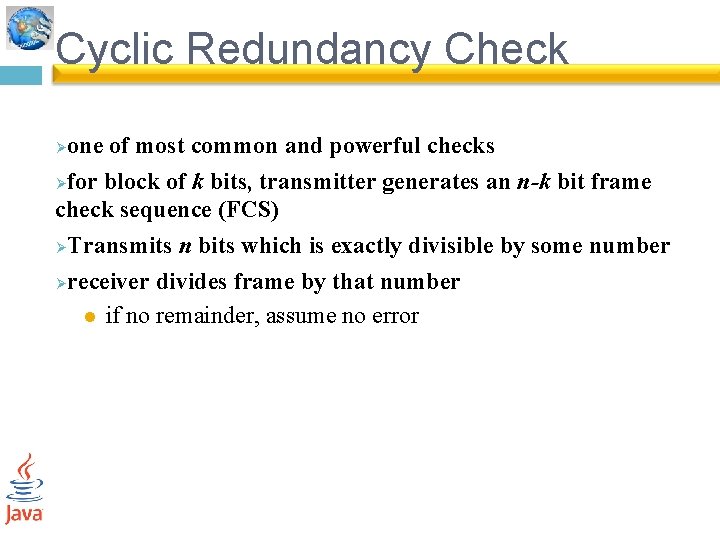
Cyclic Redundancy Check one of most common and powerful checks Øfor block of k bits, transmitter generates an n-k bit frame check sequence (FCS) ØTransmits n bits which is exactly divisible by some number Øreceiver divides frame by that number l if no remainder, assume no error Ø
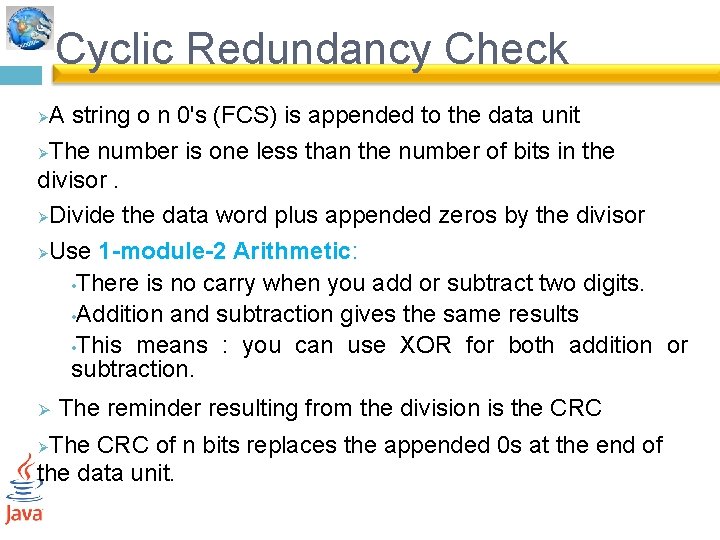
Cyclic Redundancy Check A string o n 0's (FCS) is appended to the data unit ØThe number is one less than the number of bits in the divisor. ØDivide the data word plus appended zeros by the divisor ØUse 1 -module-2 Arithmetic: • There is no carry when you add or subtract two digits. • Addition and subtraction gives the same results • This means : you can use XOR for both addition or subtraction. Ø Ø The reminder resulting from the division is the CRC The CRC of n bits replaces the appended 0 s at the end of the data unit. Ø
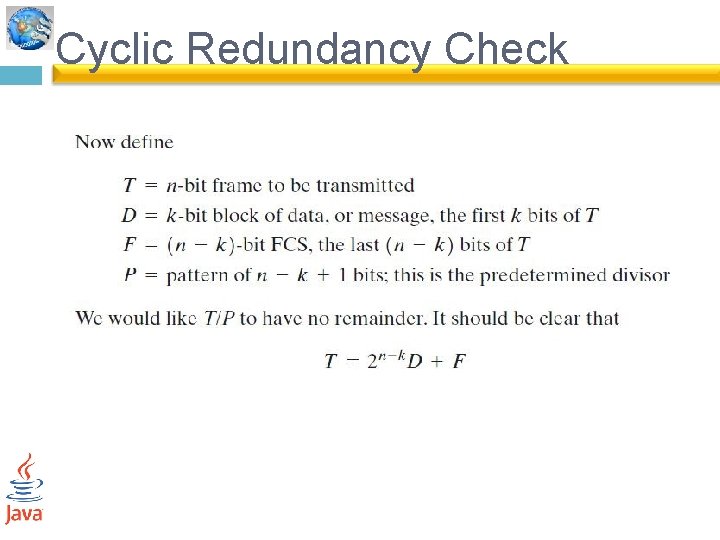
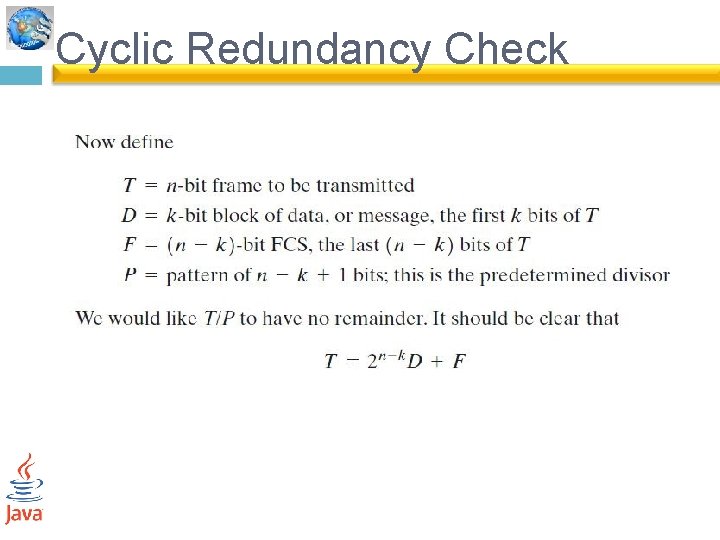
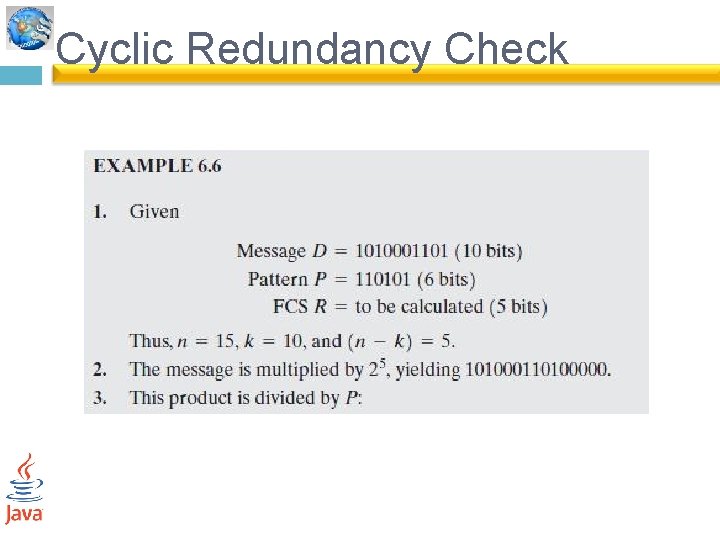
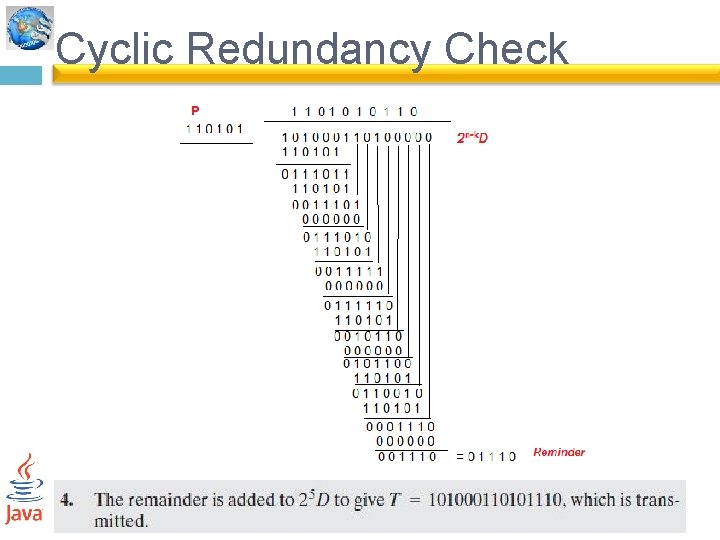
Cyclic Redundancy Check
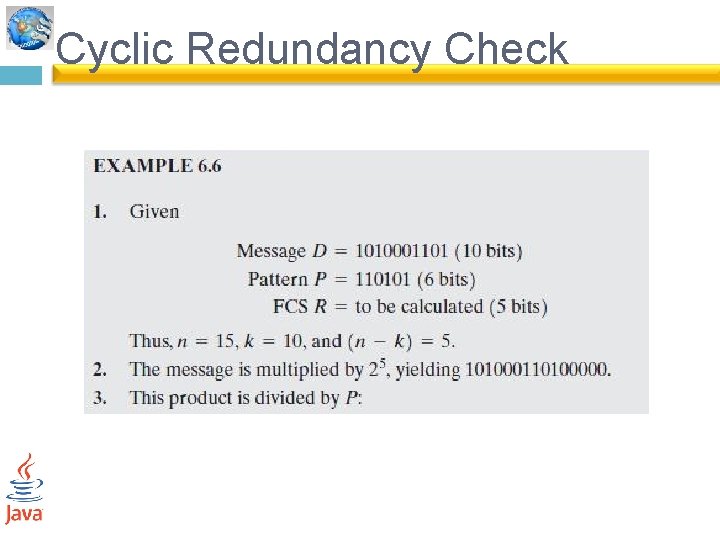
Cyclic Redundancy Check
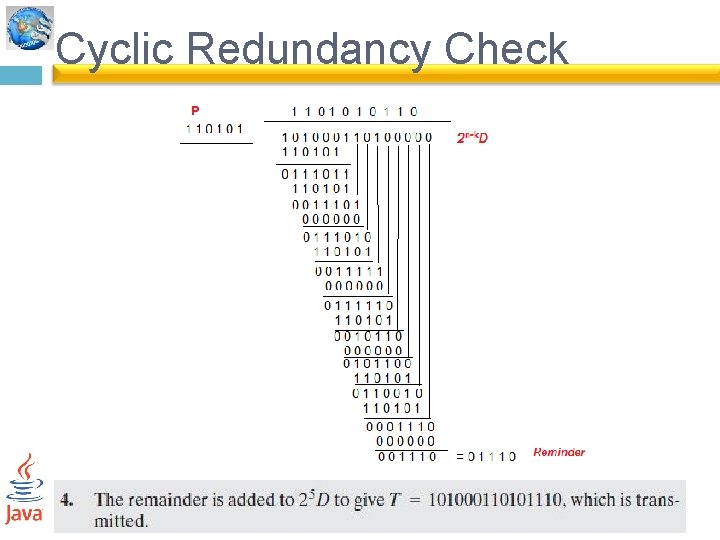
Cyclic Redundancy Check
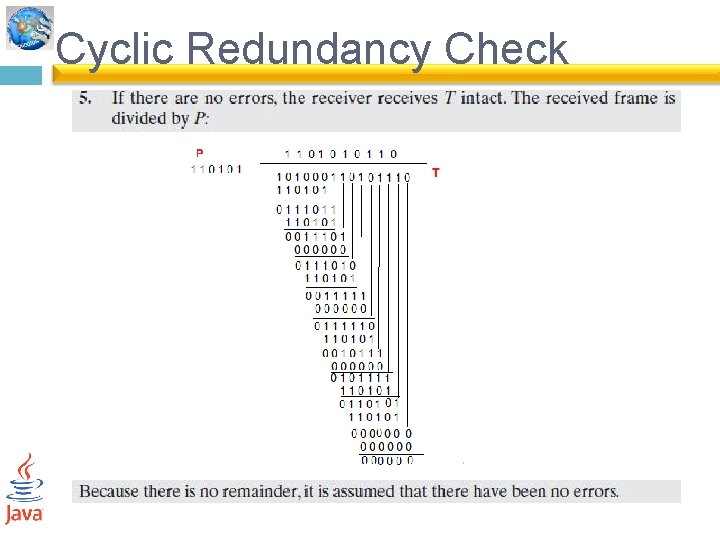
Cyclic Redundancy Check At the receiver : ØAfter receiving the data appended with the CRC , it does the same module-2 division ØIf the reminder is all 0’s , the CRC is dropped and data accepted(correct data) ØIf the reminder is not equal to zero, data discarded(wrong data)
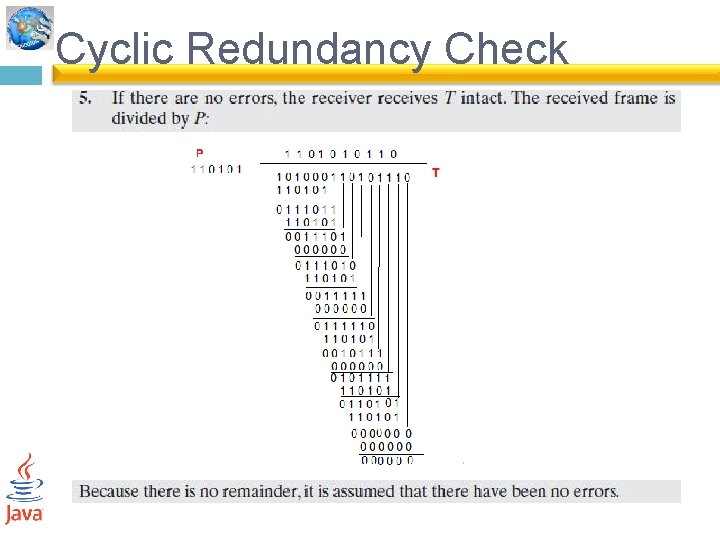
Cyclic Redundancy Check
Cyclic Redundancy Check 2 - polynomial: Express all values in variable X. ØThe divisor is represented as algebraic polynomial. Ø A polynomial should be selected to have the following : 1. It should be not divisible by x. 2. It should be divisible by x+1.
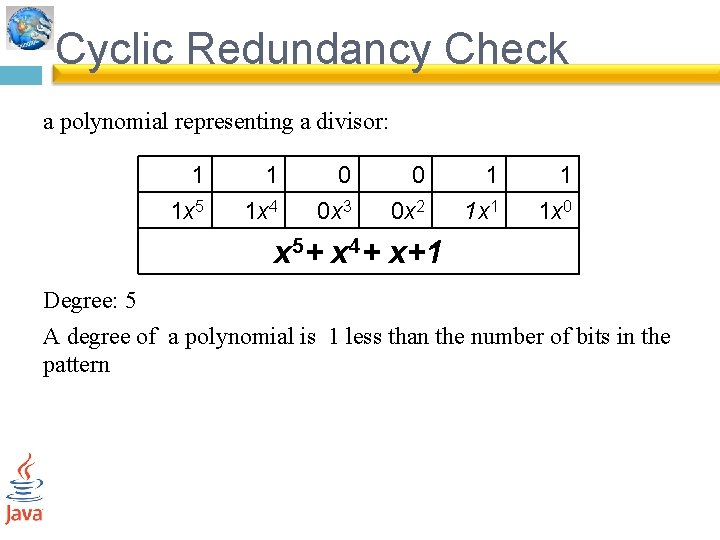
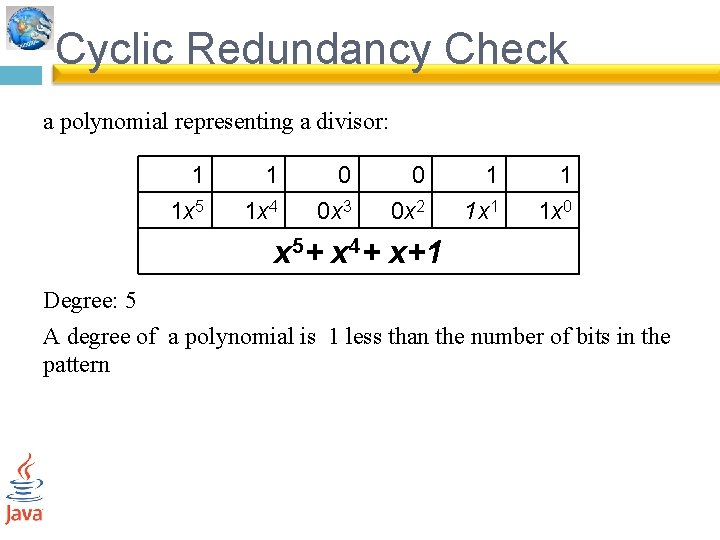
Cyclic Redundancy Check a polynomial representing a divisor: 1 1 x 5 1 1 x 4 0 0 x 3 0 0 x 2 1 1 x 1 1 1 x 0 x 5+ x 4+ x+1 Degree: 5 A degree of a polynomial is 1 less than the number of bits in the pattern
Cyclic Redundancy Check Examples : We cannot choose: 1. X(binary 10) 2. X 2 +X (binary 110) because both are divisible by X We can choose: 1. X+1 (binary 11) because it is not divisible by X , but divisible by X+1
Cyclic Redundancy Check CRC performance: ØCRC an detects all burst errors that affects odd number of bits, ØDetects all burst errors of length less than or equal to the degree of the polynomial Ø Detects all burst errors of length greater than the degree of the polynomial
Cyclic Redundancy Check # CRC-12 (X 12+ X 11+X 3+X+1) Degree: 12 CRC performance: ØCRC an detects all burst errors that affects odd number of bits, ØDetects all burst errors of length less than or equal to 12. Ø Detects all burst errors of length greater than 12
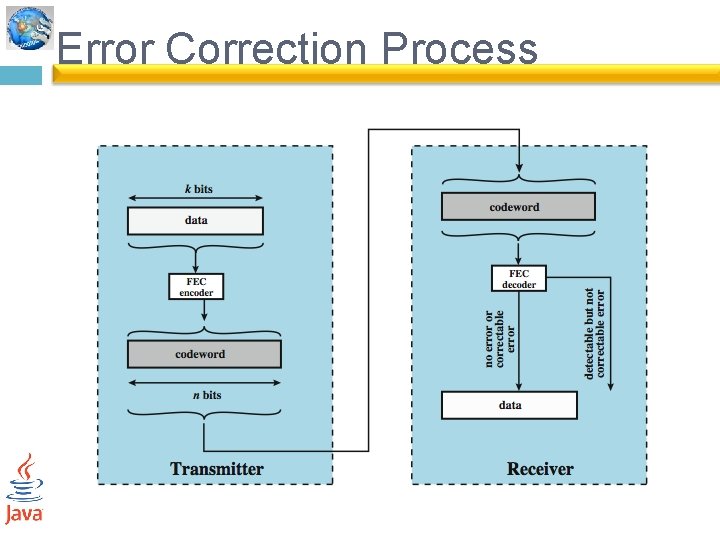
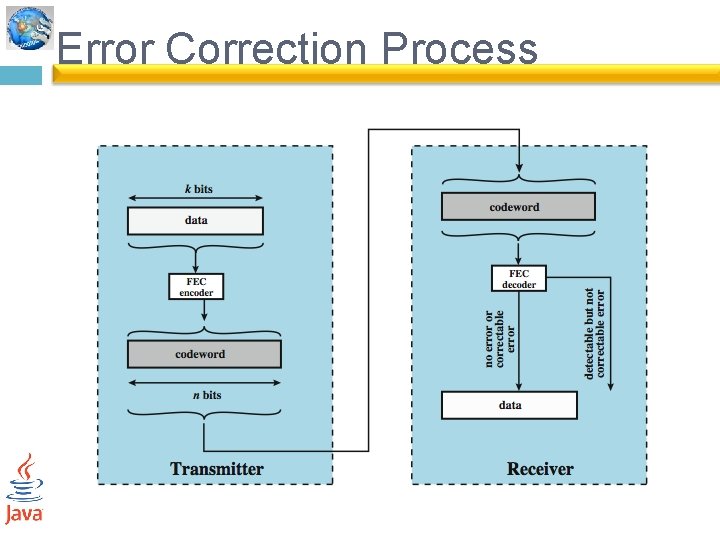
Error Correction Process
Error Correction figure 6. 7. On the transmission end, each k-bit block of data is mapped into an n-bit block (n > k) called a codeword, using an FEC (forward error correction) encoder. The codeword is then transmitted. At the receiver, the incoming signal is demodulated to produce codeword but may contain errors. This block is passed through an FEC decoder, with one of four possible outcomes: 1. If there are no bit errors, the input to the FEC decoder is identical to the original codeword, and the decoder produces the original data block as output. 2. For certain error patterns, it is possible for the decoder to detect and correct those errors, the FEC decoder is able to map this block into the original data block. 3. For certain error patterns, the decoder can detect but not correct the errors, the decoder simply reports an uncorrectable error. 4. For certain, typically rare, error patterns, the decoder does not detect that any errors have occurred and maps the incoming data block into a block different from the original.
Error correcting codes 1 -Block Code Principles Ø 2 -Hamming Code Ø
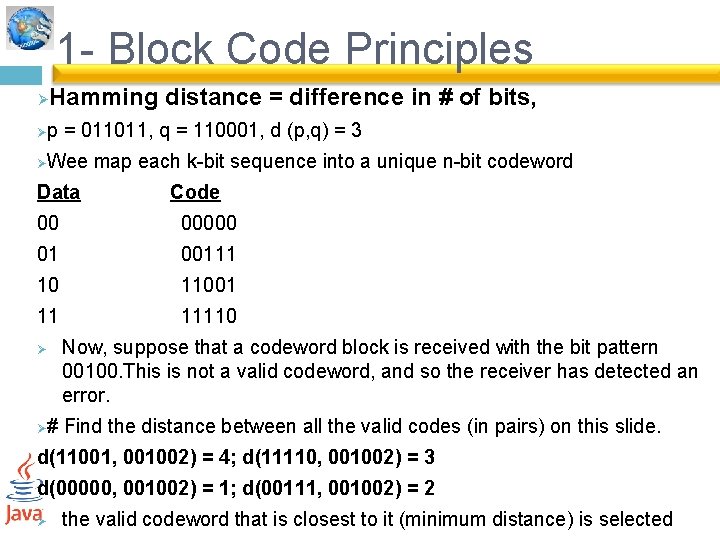
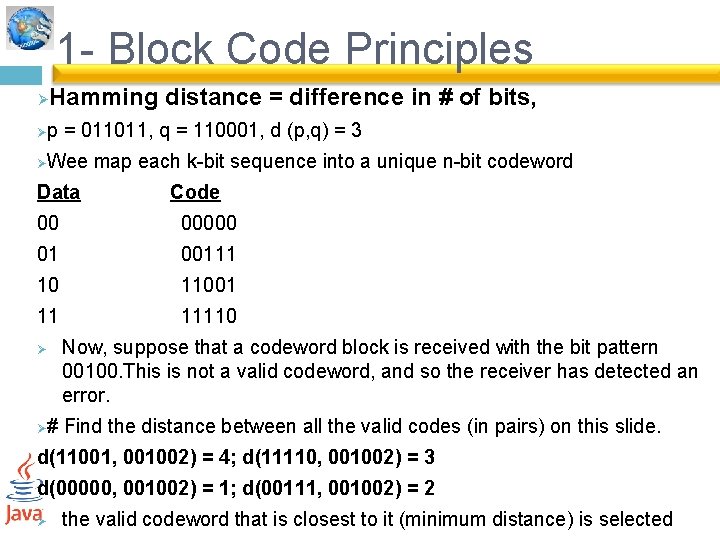
1 - Block Code Principles Ø Hamming distance = difference in # of bits, p = 011011, q = 110001, d (p, q) = 3 Ø Wee map each k-bit sequence into a unique n-bit codeword Ø Data Code 00 00000 01 00111 10 11001 11 11110 Ø Now, suppose that a codeword block is received with the bit pattern 00100. This is not a valid codeword, and so the receiver has detected an error. # Find the distance between all the valid codes (in pairs) on this slide. Ø d(11001, 001002) = 4; d(11110, 001002) = 3 d(00000, 001002) = 1; d(00111, 001002) = 2 Ø the valid codeword that is closest to it (minimum distance) is selected
Block Code Principles Example : if we have 01010 (Invalid) valid 00000 and 11110 Ø(‘Equidistance of 2’) , More than one minimum distance!!! ØReceiver has no way to choose between two alternatives. ØCan always correct a single bit error. but cannot correct double bit error. Ø
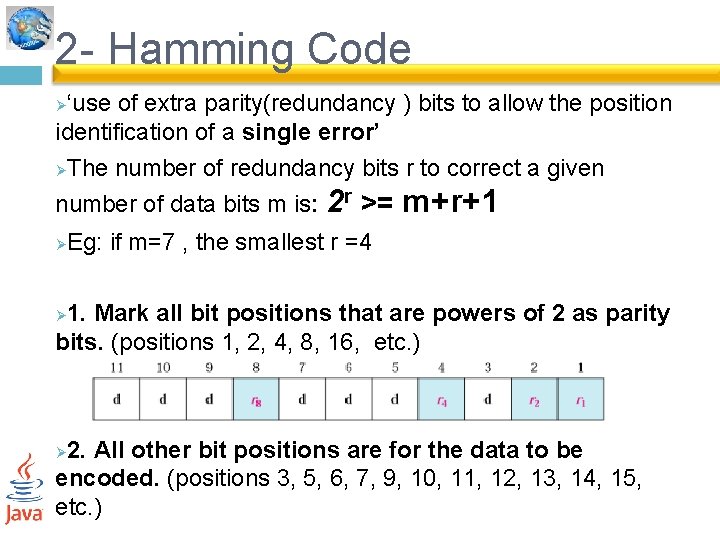
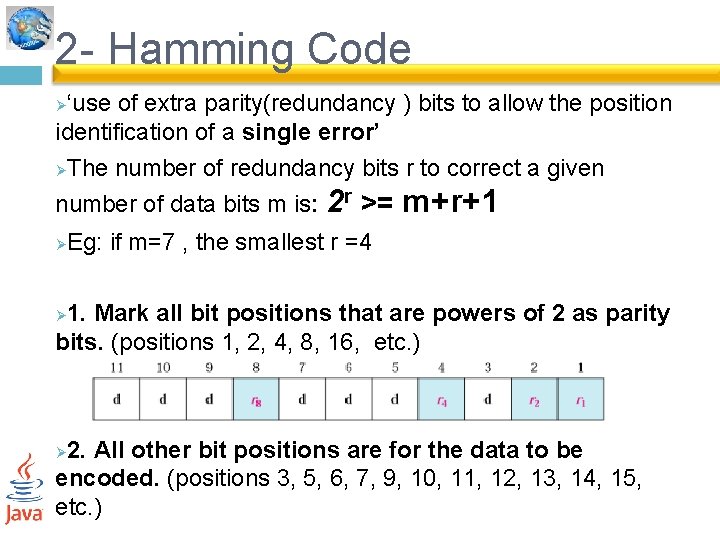
2 - Hamming Code ‘use of extra parity(redundancy ) bits to allow the position identification of a single error’ ØThe number of redundancy bits r to correct a given Ø number of data bits m is: 2 r >= Ø m+r+1 Eg: if m=7 , the smallest r =4 1. Mark all bit positions that are powers of 2 as parity bits. (positions 1, 2, 4, 8, 16, etc. ) Ø 2. All other bit positions are for the data to be encoded. (positions 3, 5, 6, 7, 9, 10, 11, 12, 13, 14, 15, etc. ) Ø
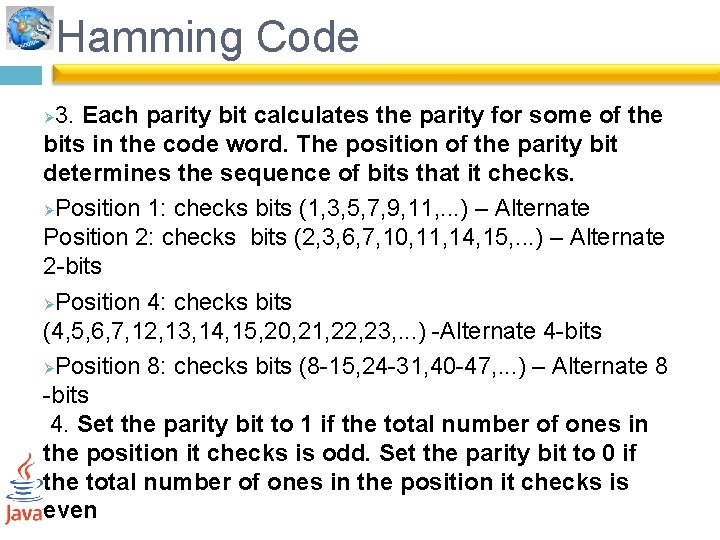
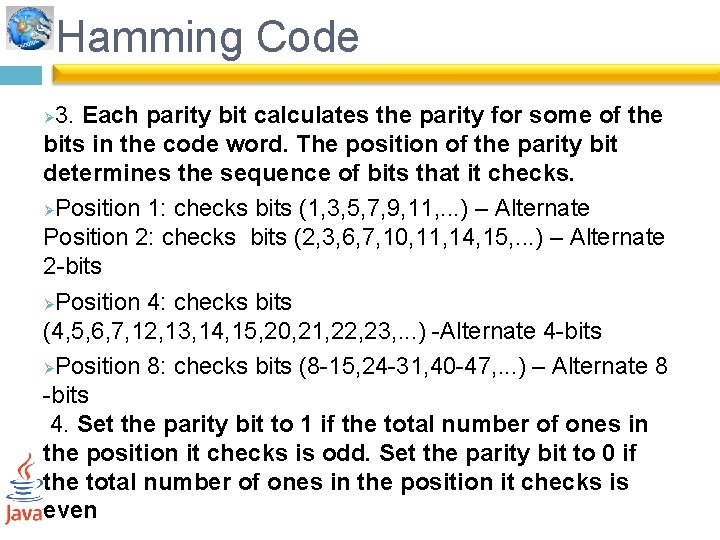
Hamming Code 3. Each parity bit calculates the parity for some of the bits in the code word. The position of the parity bit determines the sequence of bits that it checks. ØPosition 1: checks bits (1, 3, 5, 7, 9, 11, . . . ) – Alternate Position 2: checks bits (2, 3, 6, 7, 10, 11, 14, 15, . . . ) – Alternate 2 -bits ØPosition 4: checks bits (4, 5, 6, 7, 12, 13, 14, 15, 20, 21, 22, 23, . . . ) -Alternate 4 -bits ØPosition 8: checks bits (8 -15, 24 -31, 40 -47, . . . ) – Alternate 8 -bits 4. Set the parity bit to 1 if the total number of ones in the position it checks is odd. Set the parity bit to 0 if the total number of ones in the position it checks is even Ø
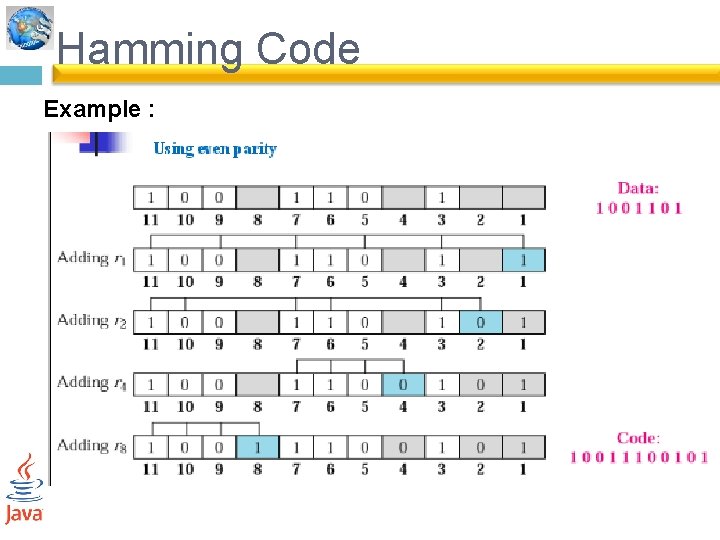
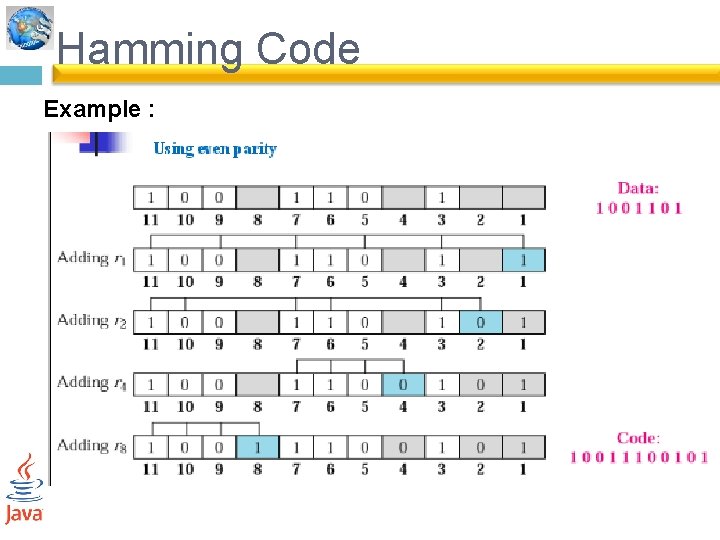
Hamming Code Example :
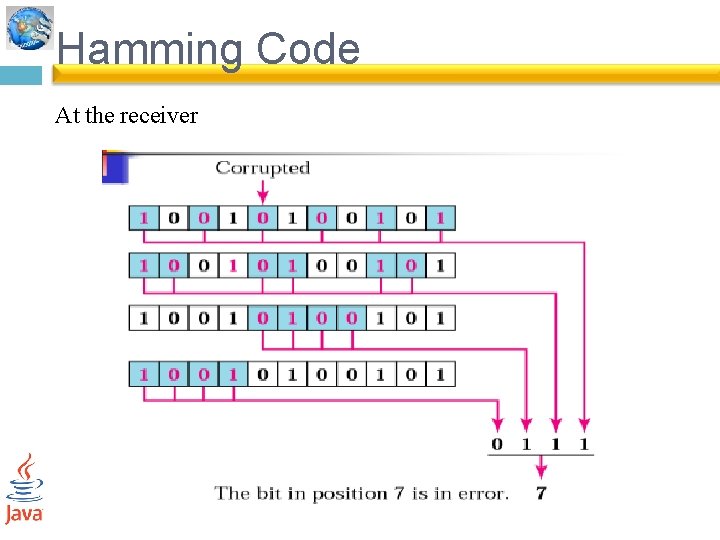
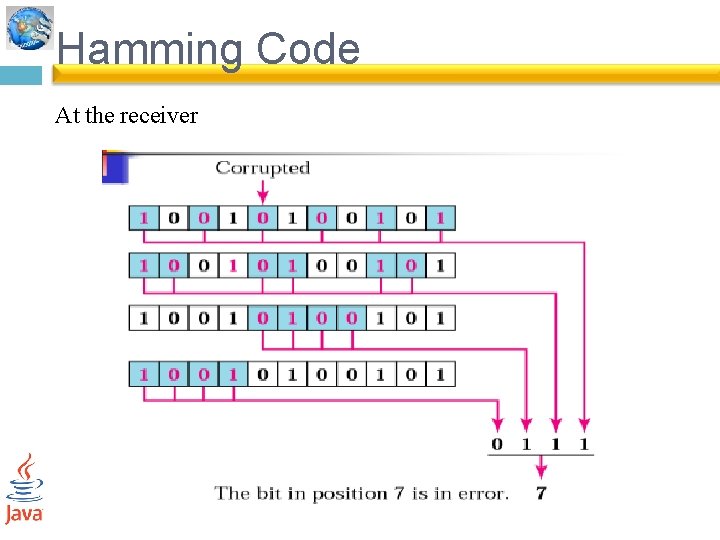
Hamming Code At the receiver
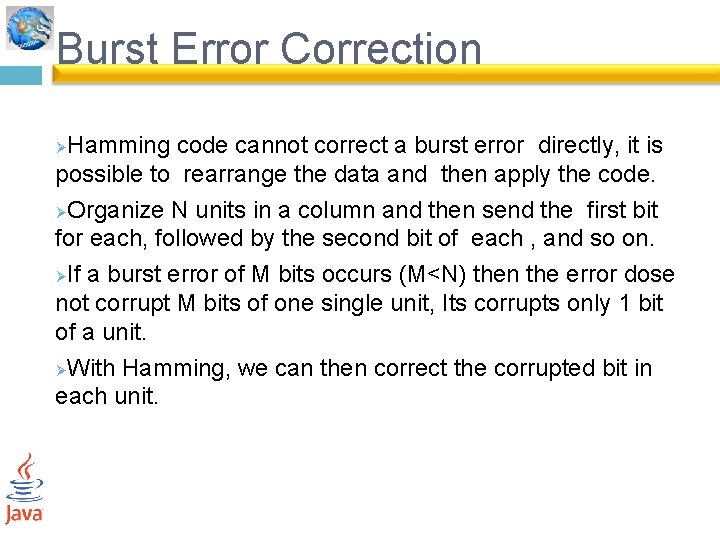
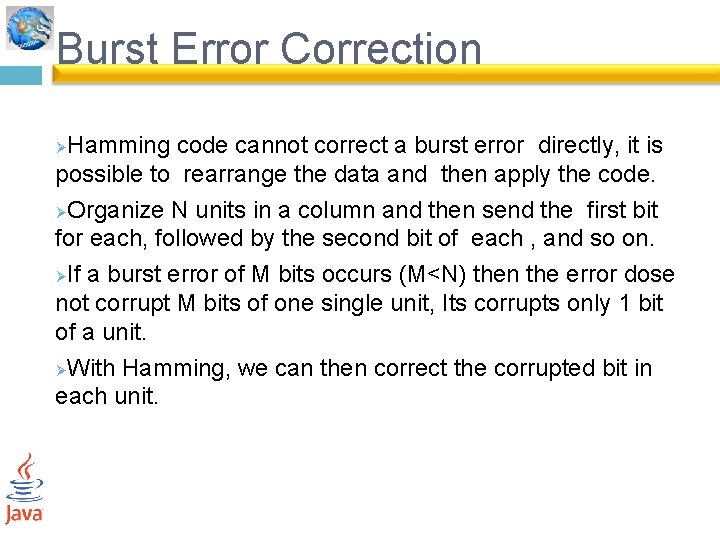
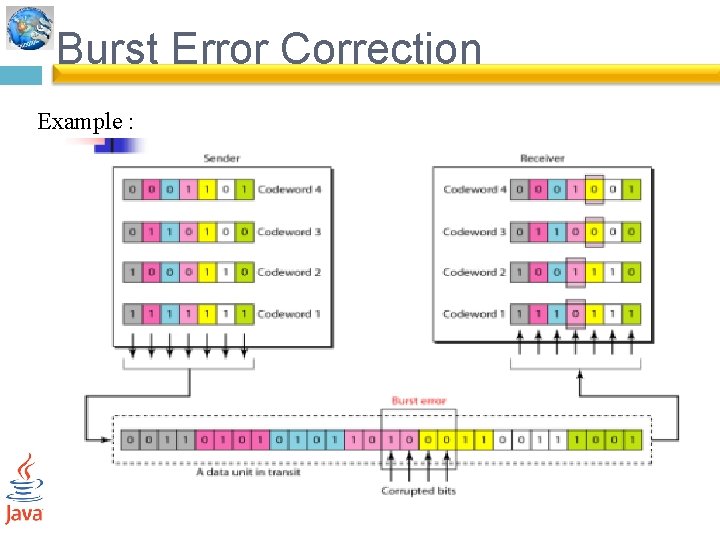
Burst Error Correction Hamming code cannot correct a burst error directly, it is possible to rearrange the data and then apply the code. ØOrganize N units in a column and then send the first bit for each, followed by the second bit of each , and so on. ØIf a burst error of M bits occurs (M<N) then the error dose not corrupt M bits of one single unit, Its corrupts only 1 bit of a unit. ØWith Hamming, we can then correct the corrupted bit in each unit. Ø
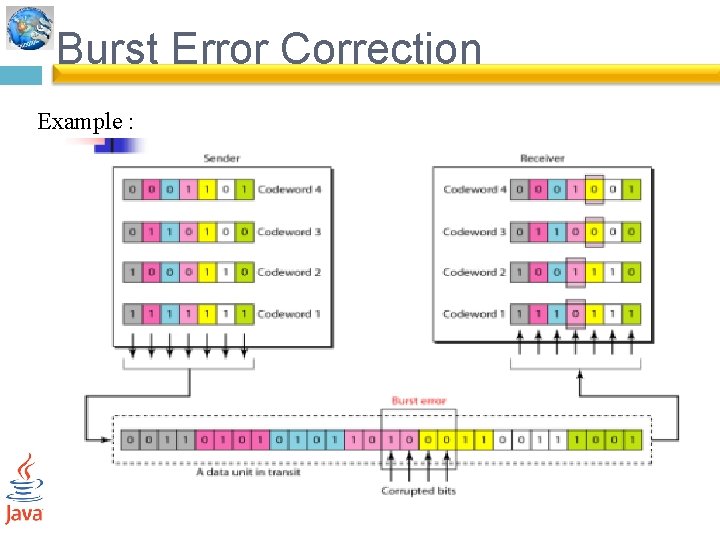
Burst Error Correction Example :
Summary asynchronous verses synchronous transmission Øerror detection and correction Ø