Taint Scope Presented by Hector M LugoCordero MS
Taint. Scope Presented by: Hector M Lugo-Cordero, MS CAP 6135 April 12, 2011
Acknowledgements • Authors: Tielei Wang, Tao Wei, Guofei Gu, Wei Zou • Paper Title: Taint. Scope: A Checksum. Aware Directed Fuzzing Tool for Automatic Software Vulnerability Detection • In Proceedings of the 31 st IEEE Symposium on Security & Privacy, Oakland, CA, May 2010. • Awarded Best Student Paper 2
Outline • • Fuzz Testing Taint. Scope Performance Conclusions 3
Outline • • Fuzz Testing Taint. Scope Performance Conclusions 4
Fuzz Testing • Attempt to crash or hang a program by feeding it malformed inputs • Blackbox fuzzing – Generational – Mutation 5
Fuzz Testing: Motivation • Nobody is perfect • Programs may be very large and dificult to test • Find bugs to fix • Exploit programs for malware 6
Fuzz Testing: Challenges • Random fuzzing has to cover a huge sample space – E. g. audio signal of 4 s, 32 k bytes • 2256, 000 possible values • Symbolic fuzzing can’t bypass checksum instructions 7
Outline • • Fuzz Testing Taint. Scope Performance Conclusions 8
Taint. Scope • Fuzzer that can bypass checksum – independent of the algorithm • Concentrates on data flow dependence • Uses IDA Pro Disassembler • Works like a classifier 9
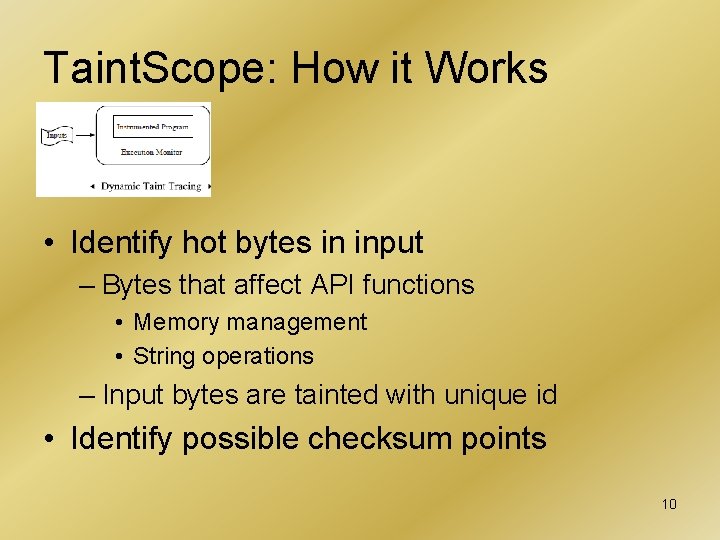
Taint. Scope: How it Works • Identify hot bytes in input – Bytes that affect API functions • Memory management • String operations – Input bytes are tainted with unique id • Identify possible checksum points 10
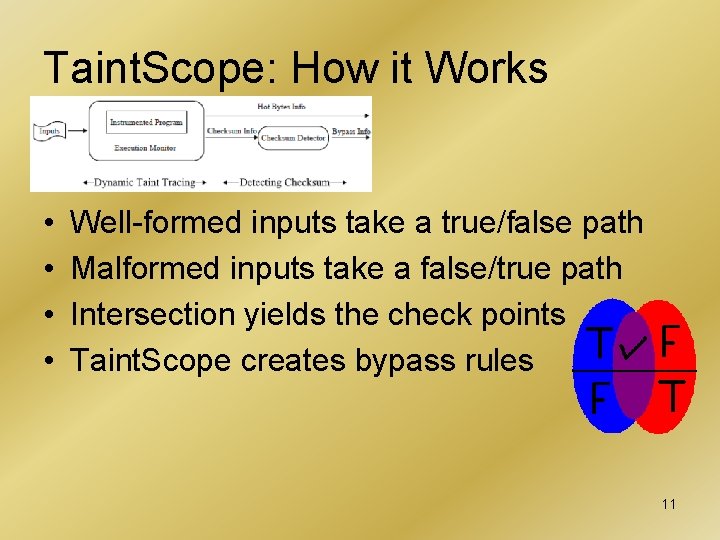
Taint. Scope: How it Works • • Well-formed inputs take a true/false path Malformed inputs take a false/true path Intersection yields the check points Taint. Scope creates bypass rules 11
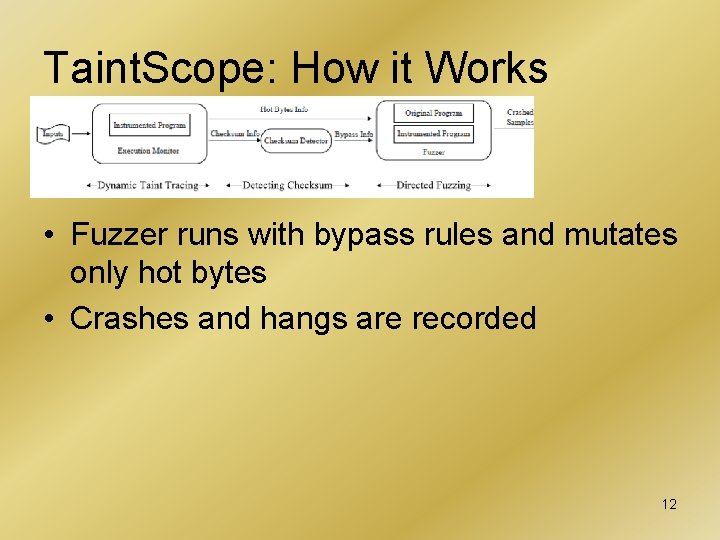
Taint. Scope: How it Works • Fuzzer runs with bypass rules and mutates only hot bytes • Crashes and hangs are recorded 12
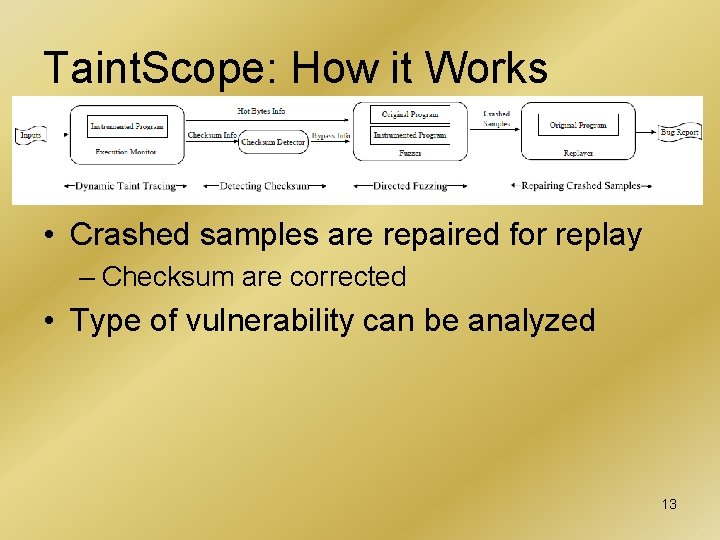
Taint. Scope: How it Works • Crashed samples are repaired for replay – Checksum are corrected • Type of vulnerability can be analyzed 13
Outline • • Fuzz Testing Taint. Scope Performance Conclusions 14
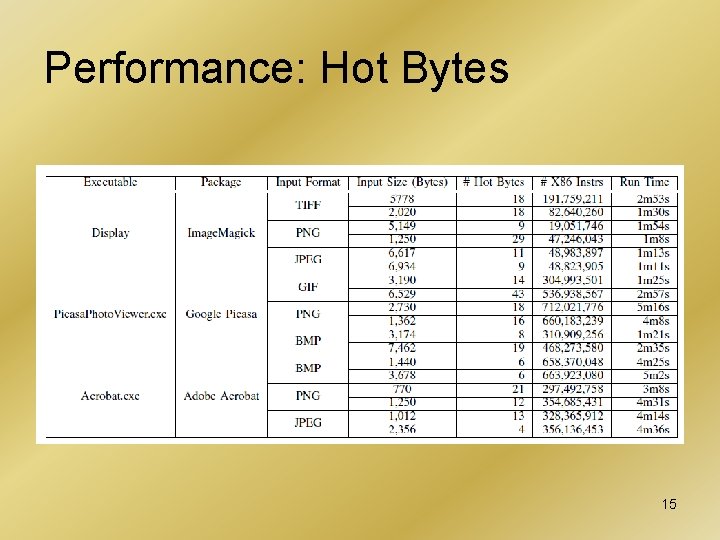
Performance: Hot Bytes 15
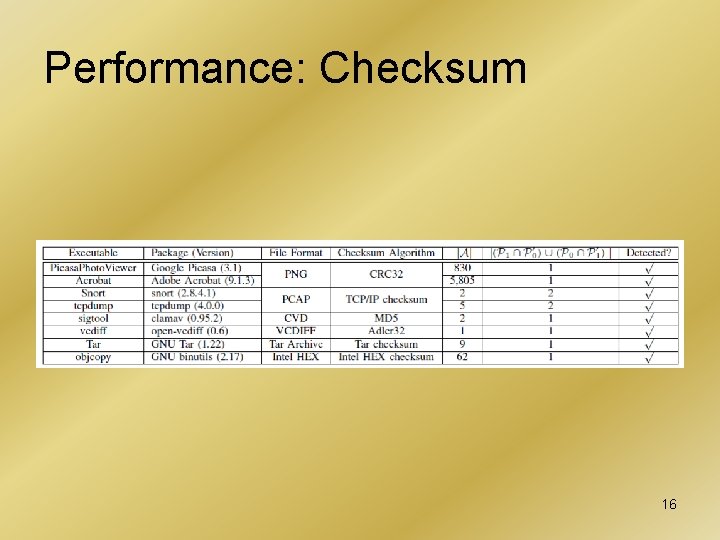
Performance: Checksum 16
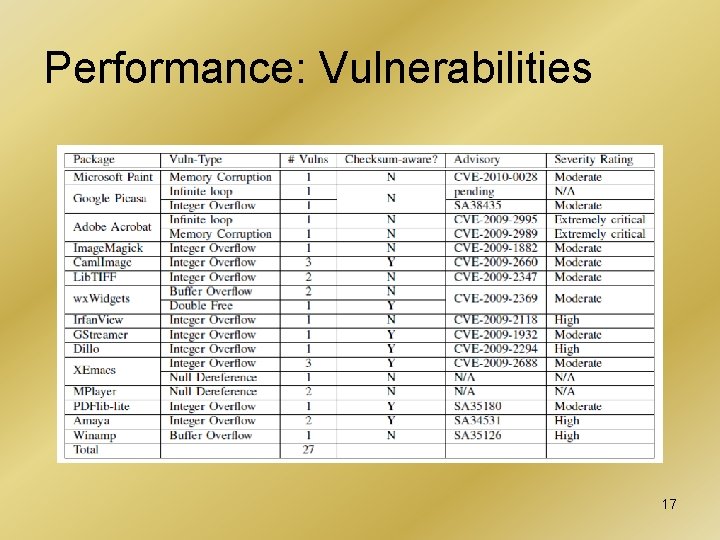
Performance: Vulnerabilities 17
What is accomplished? • Taint. Scope has found vulnerabilities in popular programs (e. g. MS Paint, Adobe Acrobat, and more) • Vendors have patched the software • Vulnerabilities have been published in – Secunia – Common Vulnerabilities and Exposure 18
MW Paint Search 19
Adobe Acrobat Search 20
Outline • • Fuzz Testing Taint. Scope Performance Conclusions 21
Conclusions • • • Fuzzer able to bypass checksum Works with Linux/Windows binaries 100% inputs cause crash or hang Low input samples Tested on many well-known applications and formats 22
Weakness • Doesn’t talk about code coverage • Needs to run the program several times to find information of interest • Can’t detect correctly checksums where data is encrypted with key-based algorithm 23
Improvements • Consider incorporating a tool like Hyper. NEAT – can learn search space patterns – work with encryption (e. g. DES S-Boxes) • Dynamic update to reduce number of runs needed to build hot bytes/checksum information 24
References 1. 2. 3. 4. 5. 6. 7. Tielei Wang’s website: http: //sites. google. com/site/tieleiwang/ Month of Kernel Bugs: http: //projects. infopull. com/mokb/ Month Browsers Bug: http: //browserfun. blogspot. com/ Secunia: http: //secunia. com/ Comon Vulnerabilities and Exposure: http: //cve. mitre. org/ IDA Disassembler: http: //www. hex-rays. com/idapro/ Google Images: http: //images. google. com 25
QUESTIONS 26
- Slides: 26