SGXBox Enabling Visibility on Encrypted Traffic using a
SGX-Box Enabling Visibility on Encrypted Traffic using a Secure Middlebox Module Juhyeng Han, Seongmin Kim, Jaehyeong Ha, Dongsu Han
Increase of Middlebox Deployment • Middlebox : Provides many useful functionalities - Deep packet inspection (DPI), packet caching, prefetching, etc - Firewalls, IDS, proxies are widely deployed • Software-based middlebox system is prevalent - NFV gives flexibility and cost efficiency to middlebox 2
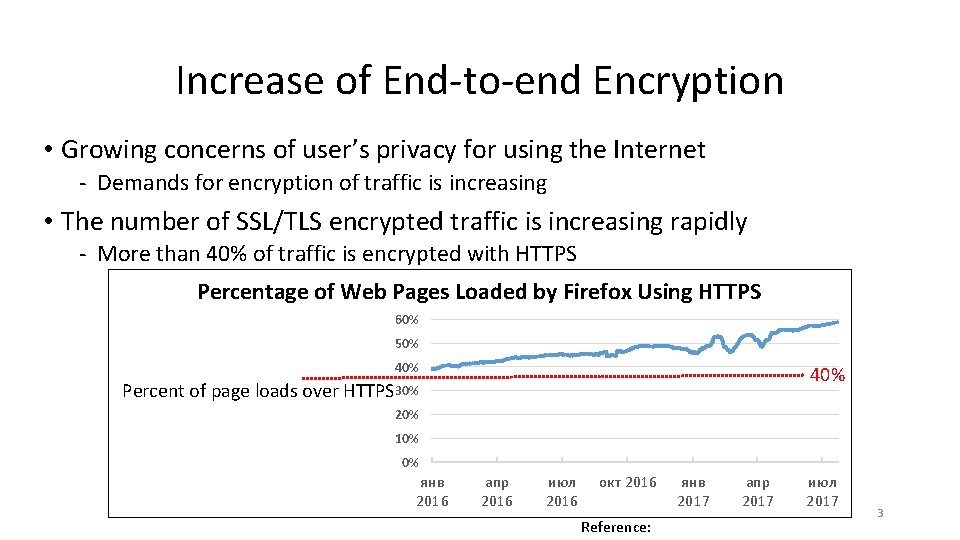
Increase of End-to-end Encryption • Growing concerns of user’s privacy for using the Internet - Demands for encryption of traffic is increasing • The number of SSL/TLS encrypted traffic is increasing rapidly - More than 40% of traffic is encrypted with HTTPS Percentage of Web Pages Loaded by Firefox Using HTTPS 60% 50% 40% Percent of page loads over 40% HTTPS 30% 20% 10% 0% янв 2016 апр 2016 июл 2016 окт 2016 Reference: янв 2017 апр 2017 июл 2017 3
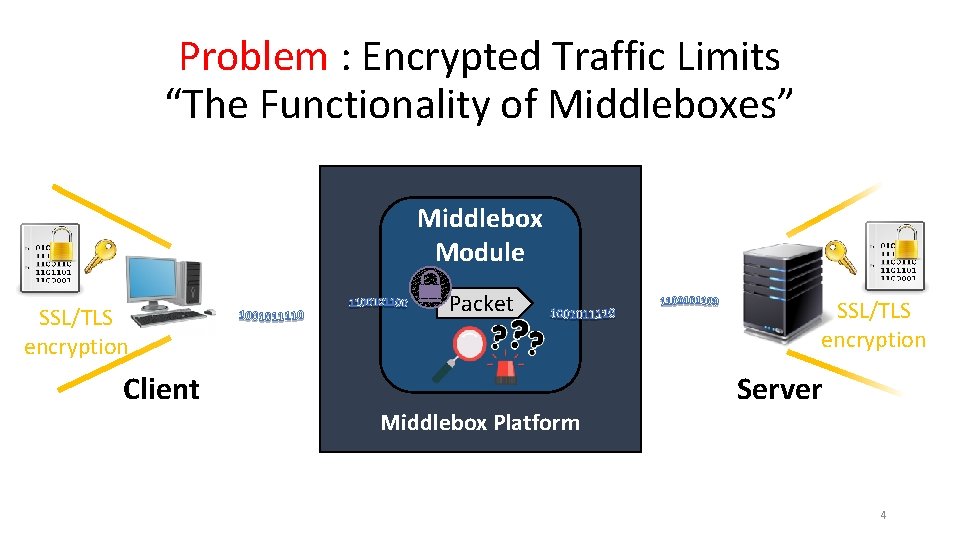
Problem : Encrypted Traffic Limits “The Functionality of Middleboxes” Middlebox Module SSL/TLS encryption Client Packet Middlebox Platform SSL/TLS encryption Server 4
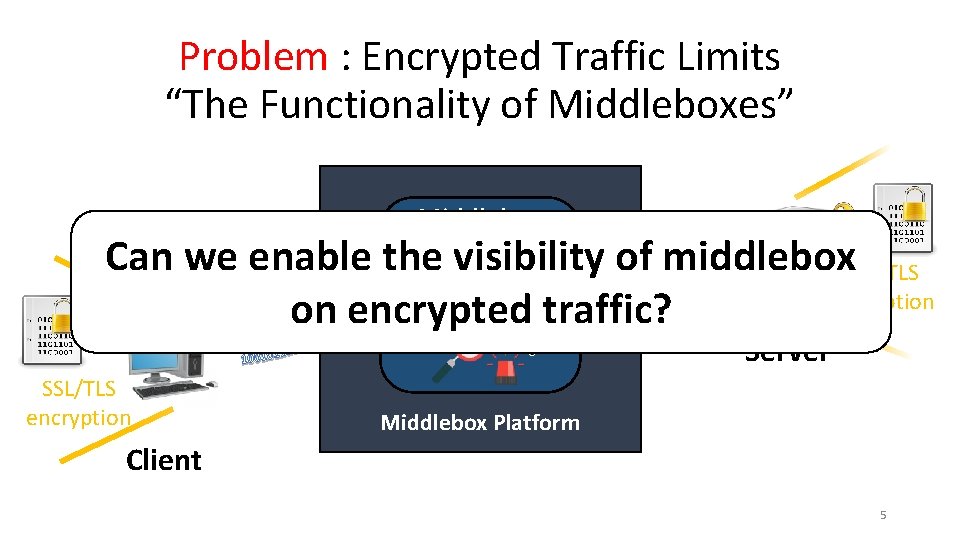
Problem : Encrypted Traffic Limits “The Functionality of Middleboxes” Middlebox the. Module visibility Can we enable of middlebox. SSL/TLS encryption Packet traffic? on encrypted Server SSL/TLS encryption Middlebox Platform Client 5
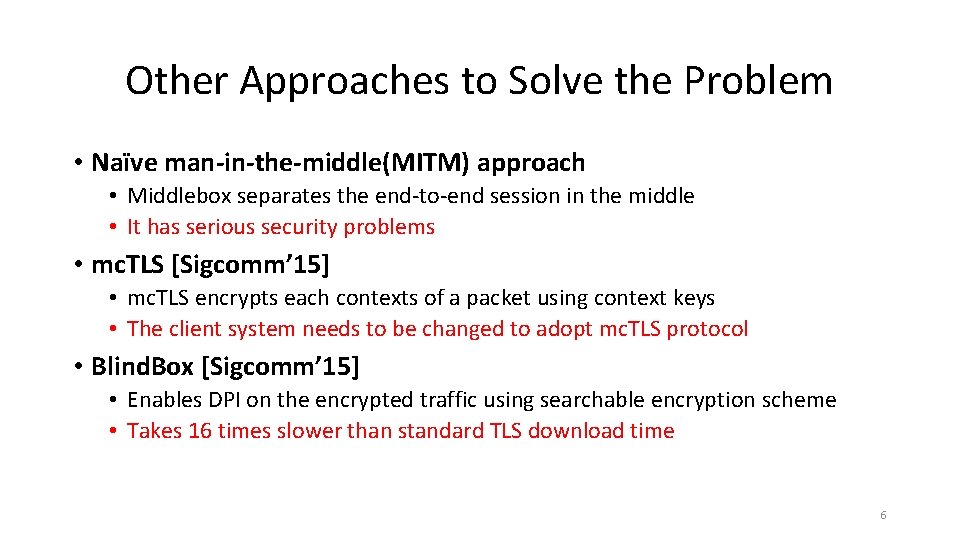
Other Approaches to Solve the Problem • Naïve man-in-the-middle(MITM) approach • Middlebox separates the end-to-end session in the middle • It has serious security problems • mc. TLS [Sigcomm’ 15] • mc. TLS encrypts each contexts of a packet using context keys • The client system needs to be changed to adopt mc. TLS protocol • Blind. Box [Sigcomm’ 15] • Enables DPI on the encrypted traffic using searchable encryption scheme • Takes 16 times slower than standard TLS download time 6
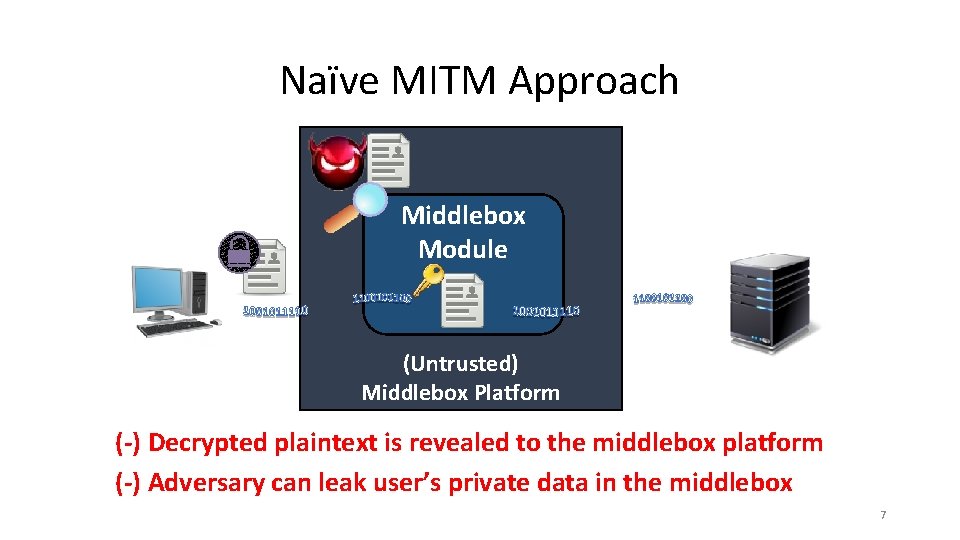
Naïve MITM Approach Middlebox Module (Untrusted) Middlebox Platform (-) Decrypted plaintext is revealed to the middlebox platform (-) Adversary can leak user’s private data in the middlebox 7
Requirements for Building a New Middlebox Module Packet Network operator (Untrusted) Middlebox Platform 8
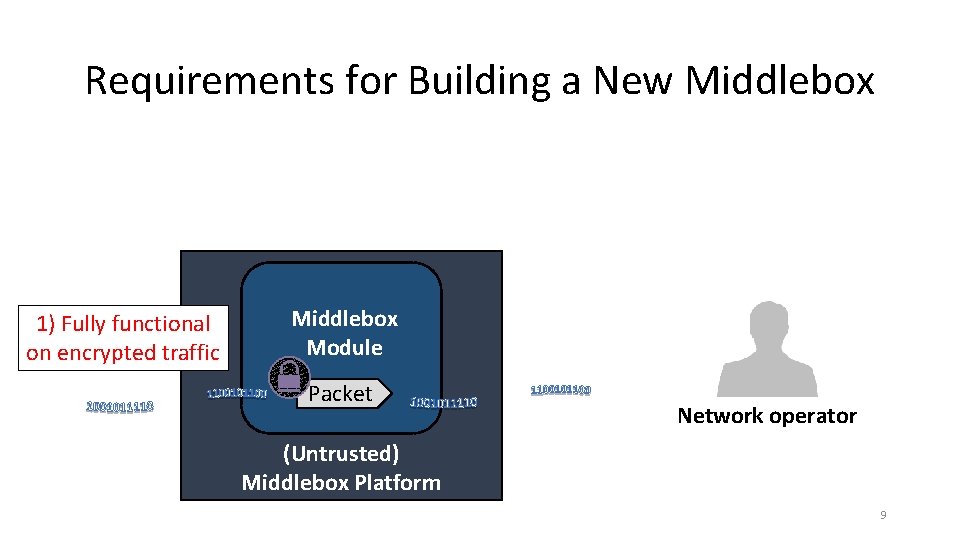
Requirements for Building a New Middlebox 1) Fully functional on encrypted traffic Middlebox Module Packet Network operator (Untrusted) Middlebox Platform 9
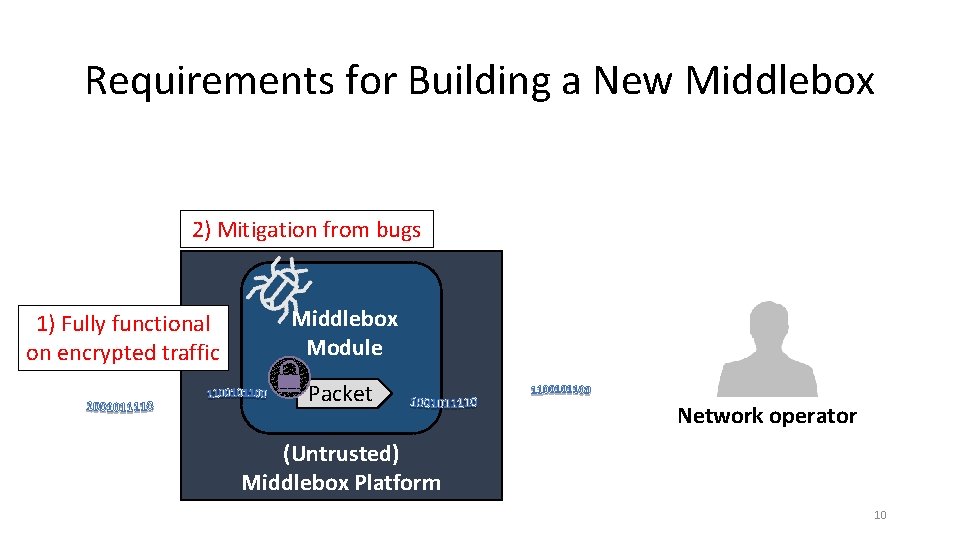
Requirements for Building a New Middlebox 2) Mitigation from bugs 1) Fully functional on encrypted traffic Middlebox Module Packet Network operator (Untrusted) Middlebox Platform 10
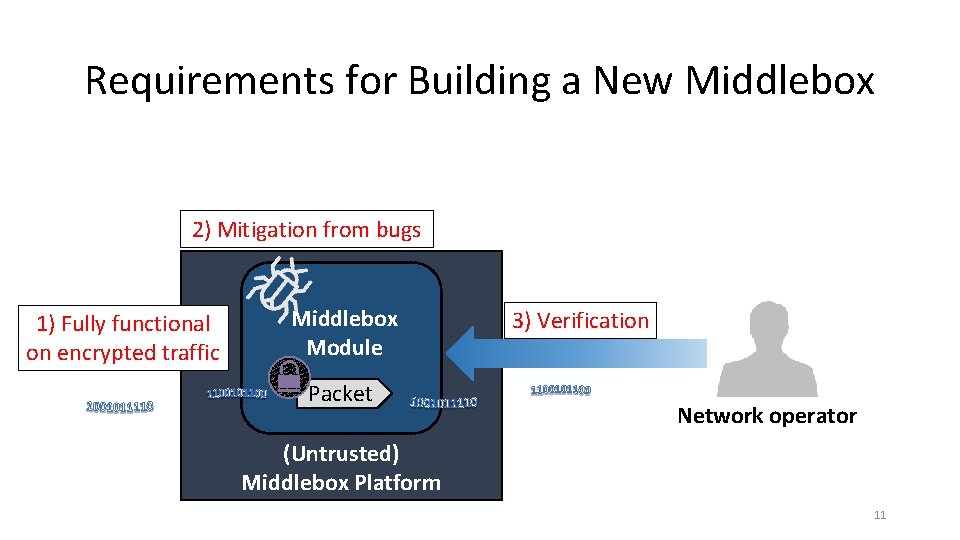
Requirements for Building a New Middlebox 2) Mitigation from bugs 1) Fully functional on encrypted traffic Middlebox Module Packet 3) Verification Network operator (Untrusted) Middlebox Platform 11
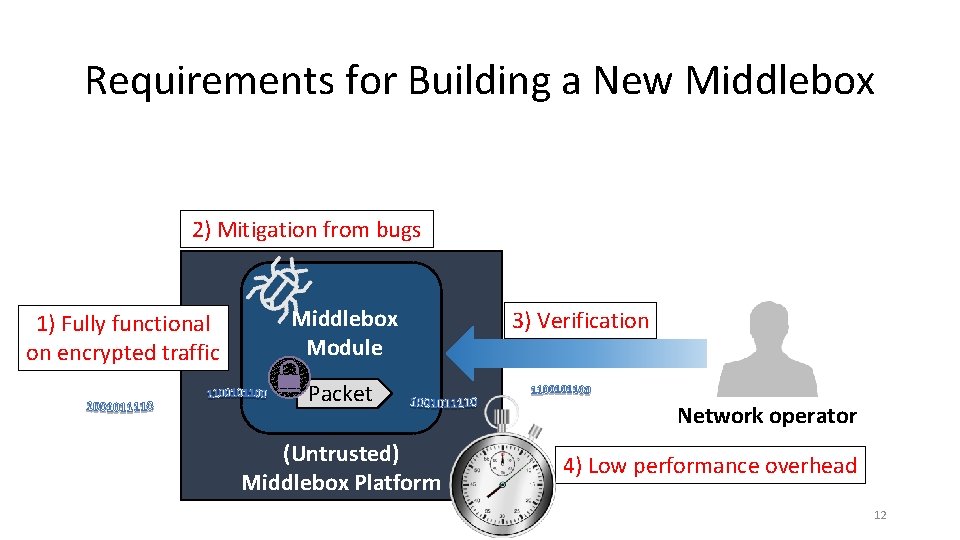
Requirements for Building a New Middlebox 2) Mitigation from bugs 1) Fully functional on encrypted traffic Middlebox Module Packet (Untrusted) Middlebox Platform 3) Verification Network operator 4) Low performance overhead 12
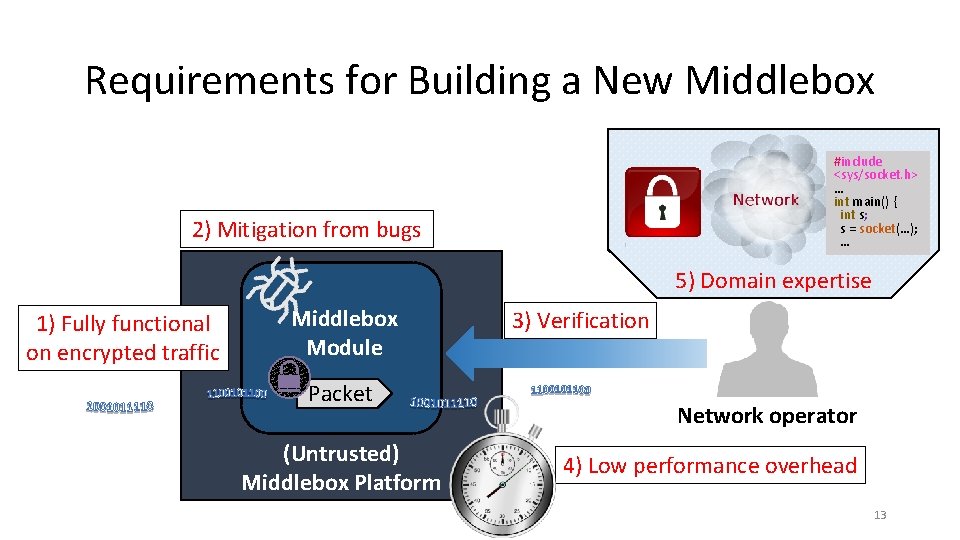
Requirements for Building a New Middlebox #include <sys/socket. h> … int main() { int s; s = socket(…); … 2) Mitigation from bugs 5) Domain expertise 1) Fully functional on encrypted traffic Middlebox Module Packet (Untrusted) Middlebox Platform 3) Verification Network operator 4) Low performance overhead 13
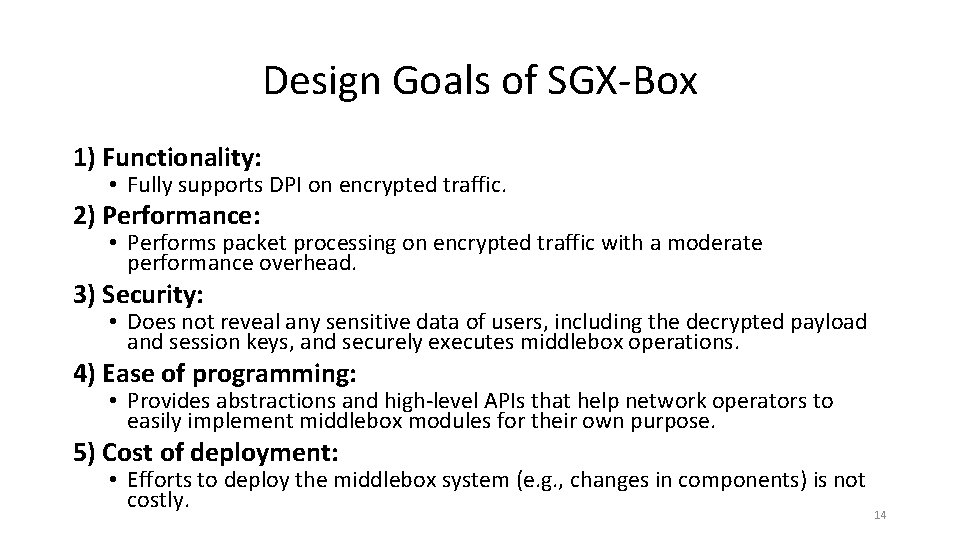
Design Goals of SGX-Box 1) Functionality: • Fully supports DPI on encrypted traffic. 2) Performance: • Performs packet processing on encrypted traffic with a moderate performance overhead. 3) Security: • Does not reveal any sensitive data of users, including the decrypted payload and session keys, and securely executes middlebox operations. 4) Ease of programming: • Provides abstractions and high-level APIs that help network operators to easily implement middlebox modules for their own purpose. 5) Cost of deployment: • Efforts to deploy the middlebox system (e. g. , changes in components) is not costly. 14
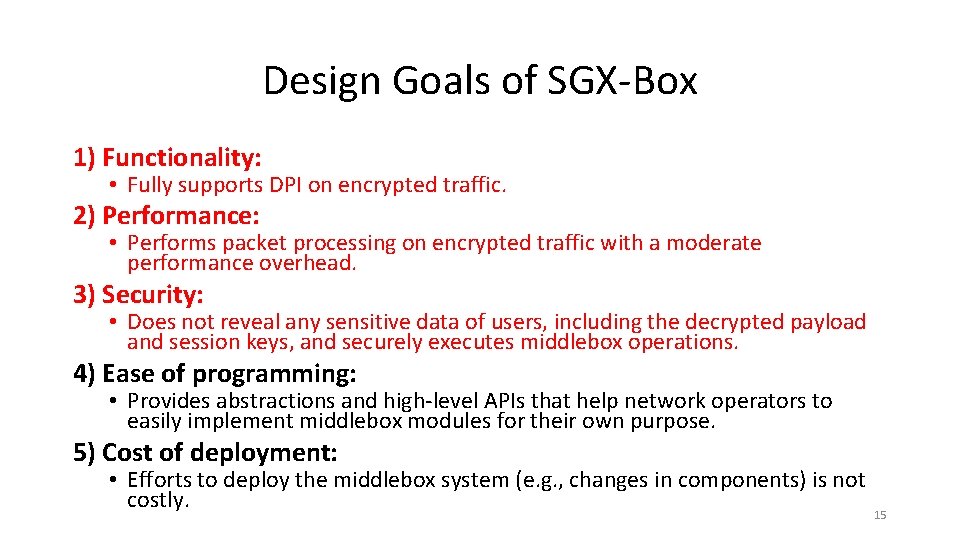
Design Goals of SGX-Box 1) Functionality: • Fully supports DPI on encrypted traffic. 2) Performance: • Performs packet processing on encrypted traffic with a moderate performance overhead. 3) Security: • Does not reveal any sensitive data of users, including the decrypted payload and session keys, and securely executes middlebox operations. 4) Ease of programming: • Provides abstractions and high-level APIs that help network operators to easily implement middlebox modules for their own purpose. 5) Cost of deployment: • Efforts to deploy the middlebox system (e. g. , changes in components) is not costly. 15
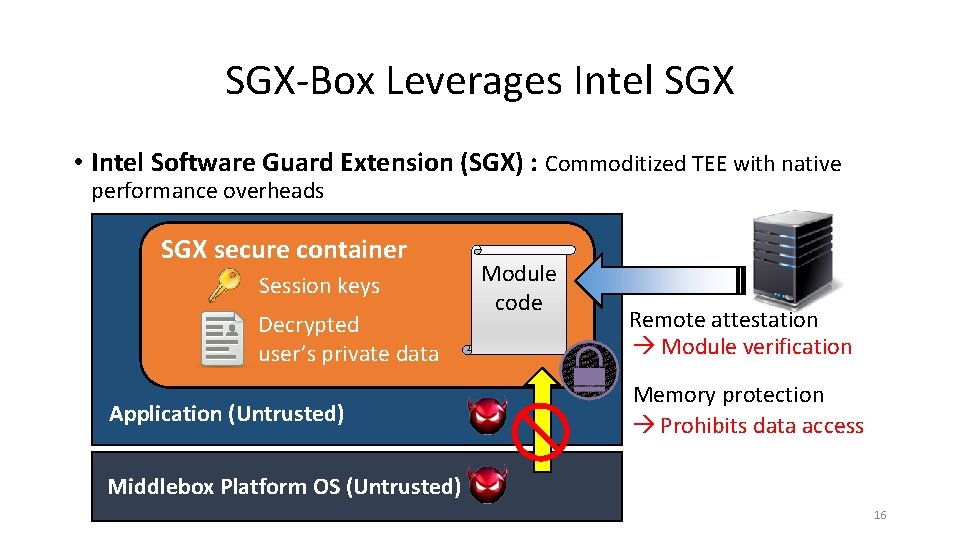
SGX-Box Leverages Intel SGX • Intel Software Guard Extension (SGX) : Commoditized TEE with native performance overheads SGX secure container Session keys Decrypted user’s private data Application (Untrusted) Module code Remote attestation Module verification Memory protection Prohibits data access Middlebox Platform OS (Untrusted) 16
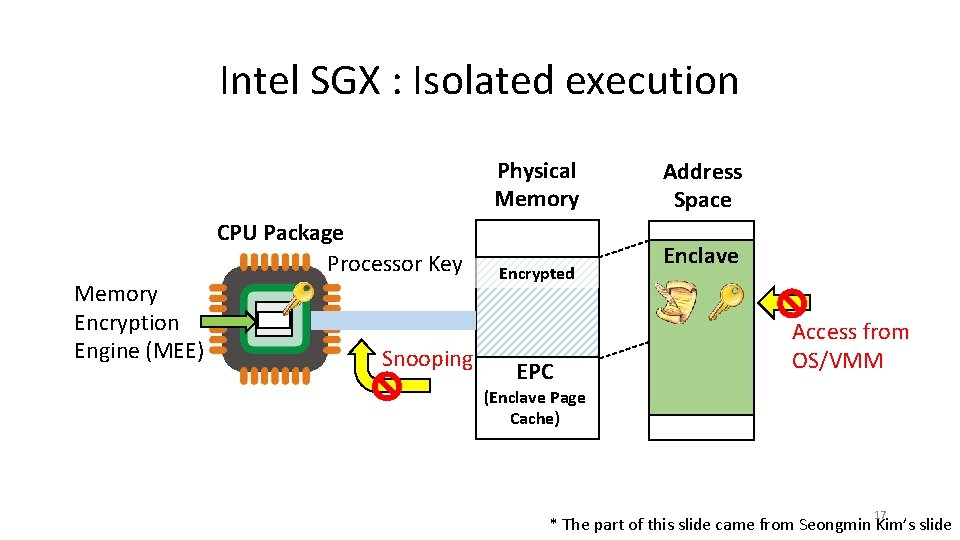
Intel SGX : Isolated execution Physical Memory CPU Package Processor Key Memory Encryption Engine (MEE) Snooping Encrypted EPC Address Space Enclave Access from OS/VMM (Enclave Page Cache) 17 * The part of this slide came from Seongmin Kim’s slide
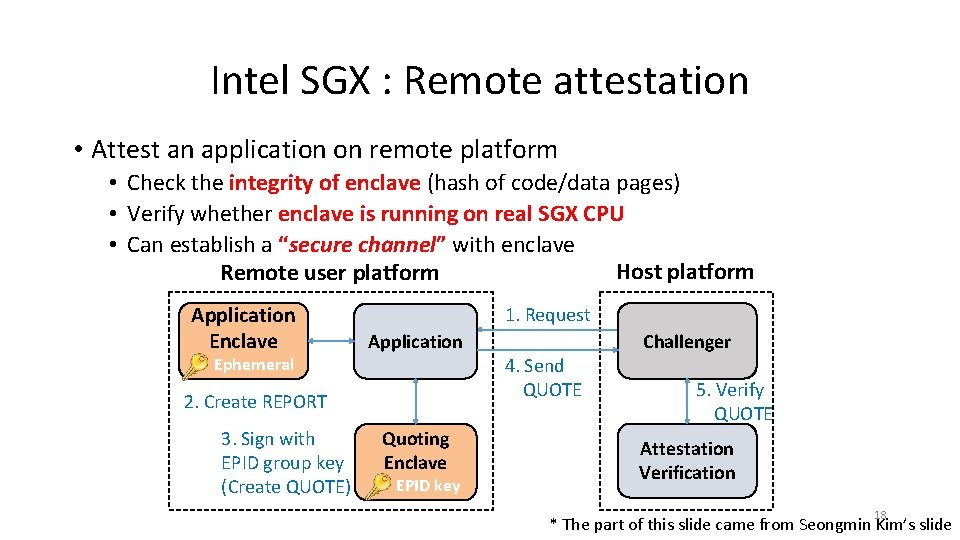
Intel SGX : Remote attestation • Attest an application on remote platform • Check the integrity of enclave (hash of code/data pages) • Verify whether enclave is running on real SGX CPU • Can establish a “secure channel” with enclave Host platform Remote user platform Application Enclave Ephemeral 1. Request 4. Send QUOTE 2. Create REPORT 3. Sign with EPID group key (Create QUOTE) Challenger Application Quoting Enclave EPID key 5. Verify QUOTE Attestation Verification 18 * The part of this slide came from Seongmin Kim’s slide
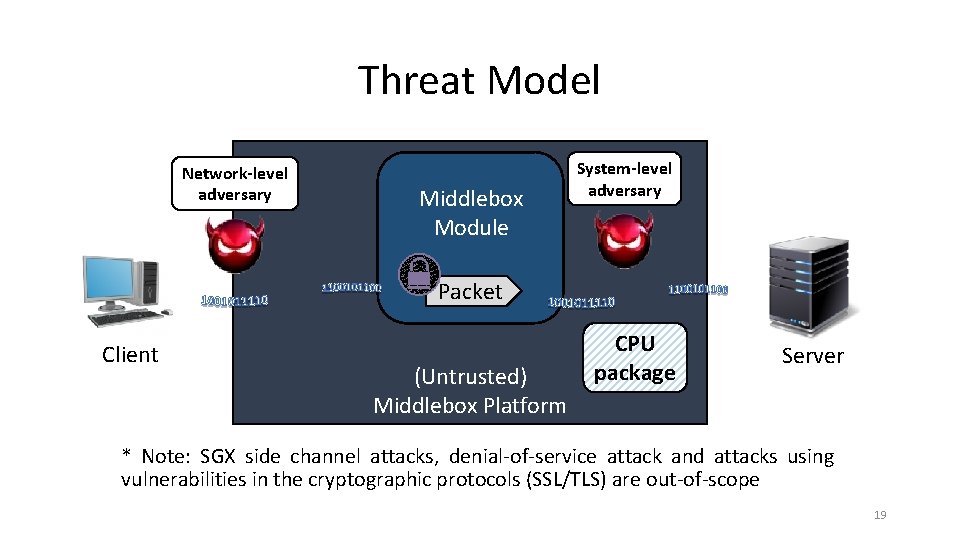
Threat Model Network-level adversary Middlebox Module System-level adversary Packet Client (Untrusted) Middlebox Platform CPU package Server * Note: SGX side channel attacks, denial-of-service attack and attacks using vulnerabilities in the cryptographic protocols (SSL/TLS) are out-of-scope 19
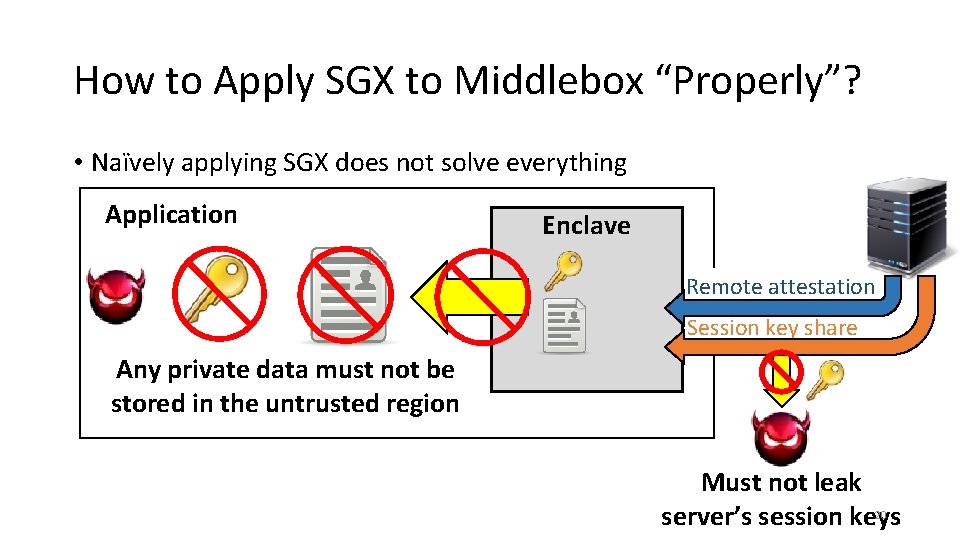
How to Apply SGX to Middlebox “Properly”? • Naïvely applying SGX does not solve everything Application Enclave Remote attestation Session key share Any private data must not be stored in the untrusted region Must not leak 20 server’s session keys
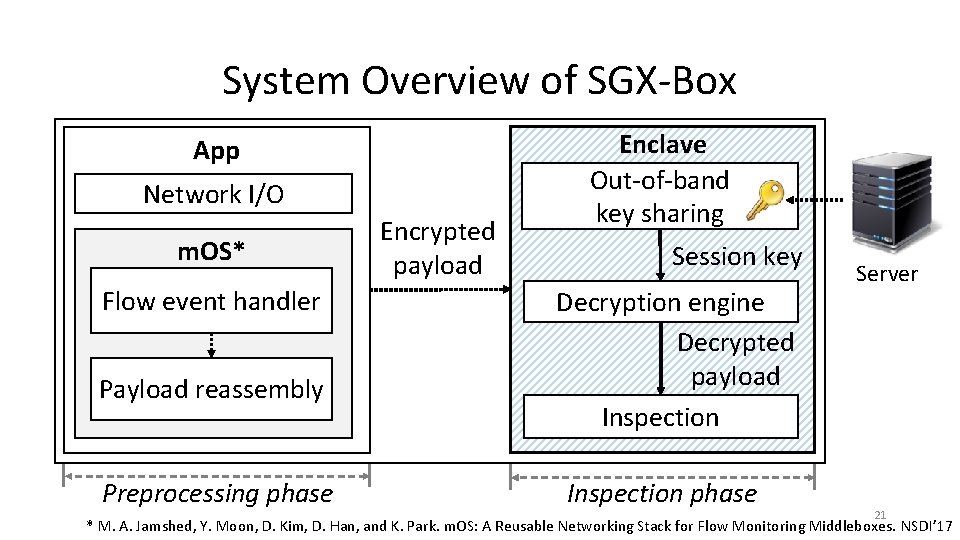
System Overview of SGX-Box App Network I/O m. OS* Flow event handler Payload reassembly Preprocessing phase Encrypted payload Enclave Out-of-band key sharing Session key Decryption engine Decrypted payload Inspection phase Server 21 * M. A. Jamshed, Y. Moon, D. Kim, D. Han, and K. Park. m. OS: A Reusable Networking Stack for Flow Monitoring Middleboxes. NSDI’ 17
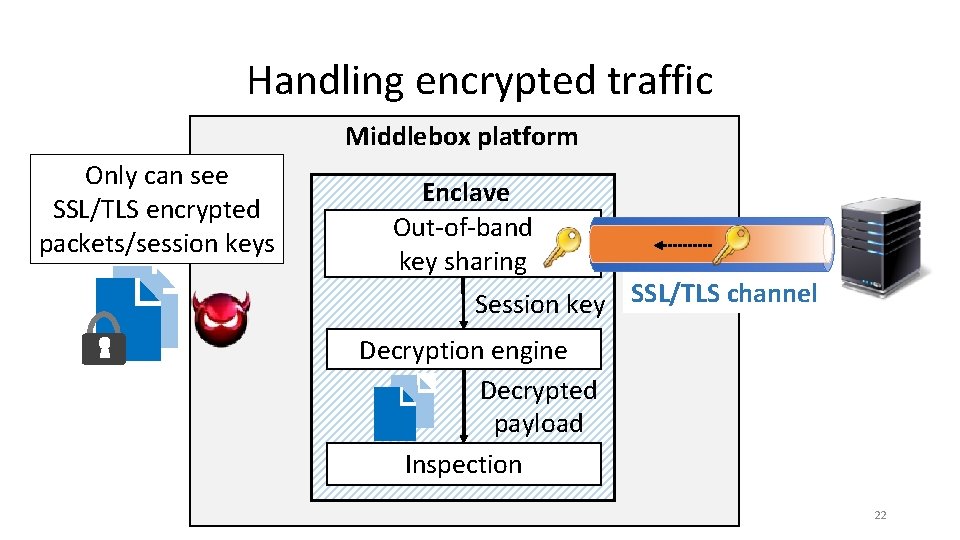
Handling encrypted traffic Middlebox platform Only can see SSL/TLS encrypted packets/session keys Enclave Out-of-band key sharing Session key SSL/TLS channel Decryption engine Decrypted payload Inspection 22
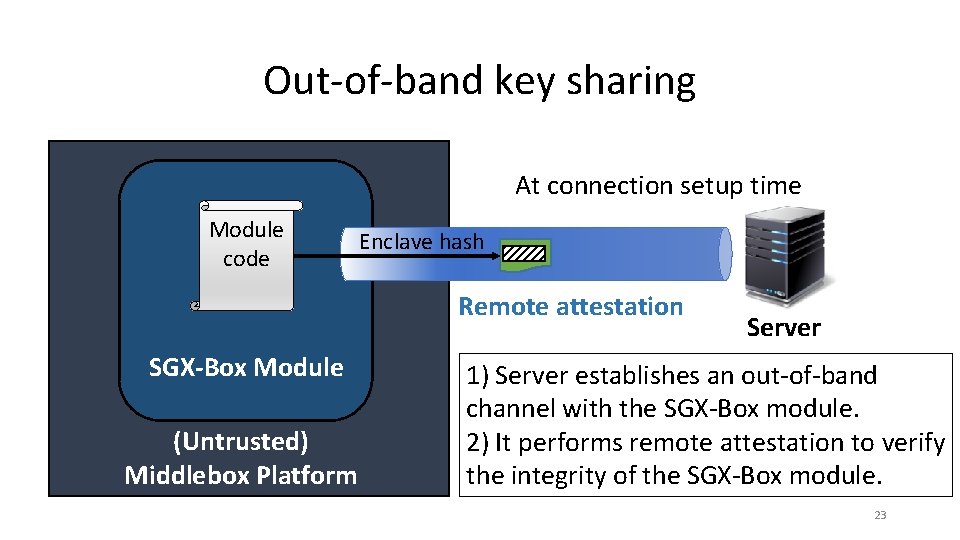
Out-of-band key sharing At connection setup time Module code Enclave hash Remote attestation SGX-Box Module (Untrusted) Middlebox Platform Server 1) Server establishes an out-of-band channel with the SGX-Box module. 2) It performs remote attestation to verify the integrity of the SGX-Box module. 23
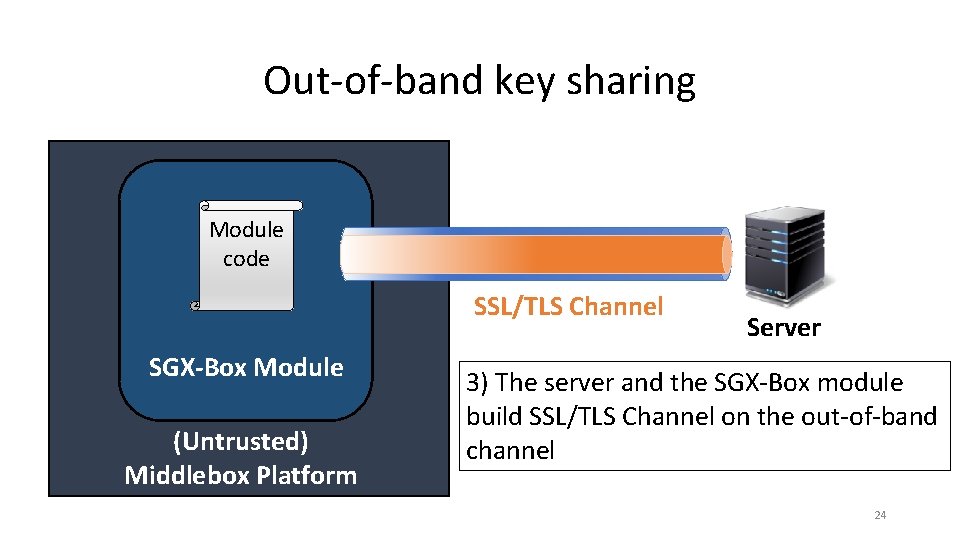
Out-of-band key sharing Module code SSL/TLS Channel SGX-Box Module (Untrusted) Middlebox Platform Server 3) The server and the SGX-Box module build SSL/TLS Channel on the out-of-band channel 24
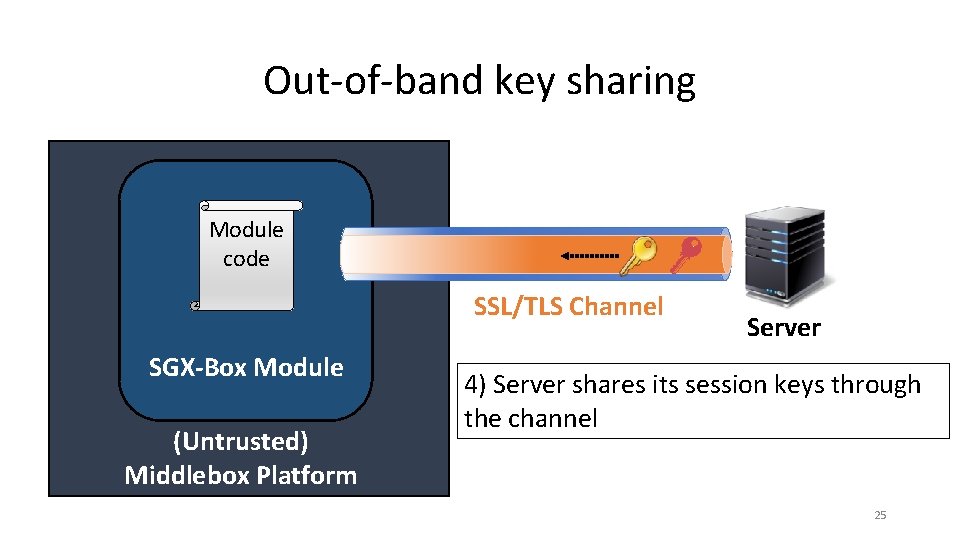
Out-of-band key sharing Module code SSL/TLS Channel SGX-Box Module (Untrusted) Middlebox Platform Server 4) Server shares its session keys through the channel 25
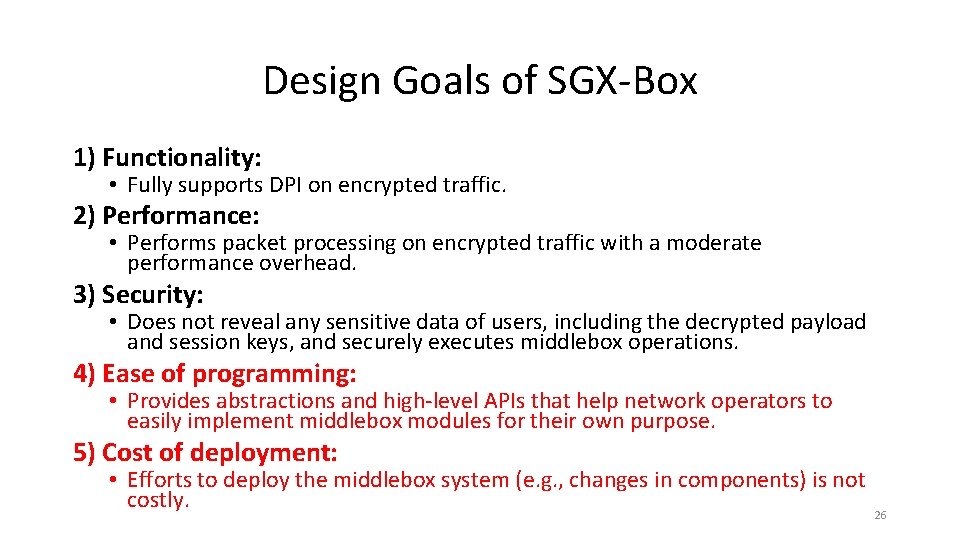
Design Goals of SGX-Box 1) Functionality: • Fully supports DPI on encrypted traffic. 2) Performance: • Performs packet processing on encrypted traffic with a moderate performance overhead. 3) Security: • Does not reveal any sensitive data of users, including the decrypted payload and session keys, and securely executes middlebox operations. 4) Ease of programming: • Provides abstractions and high-level APIs that help network operators to easily implement middlebox modules for their own purpose. 5) Cost of deployment: • Efforts to deploy the middlebox system (e. g. , changes in components) is not costly. 26
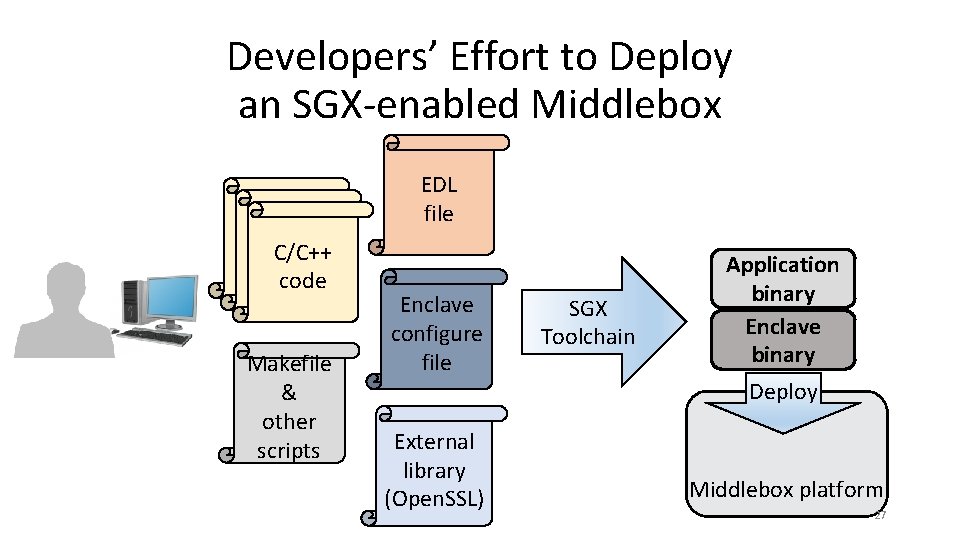
Developers’ Effort to Deploy an SGX-enabled Middlebox C/C++ code Makefile & other scripts EDL file Enclave configure file External library (Open. SSL) SGX Toolchain Application binary Enclave binary Deploy Middlebox platform 27
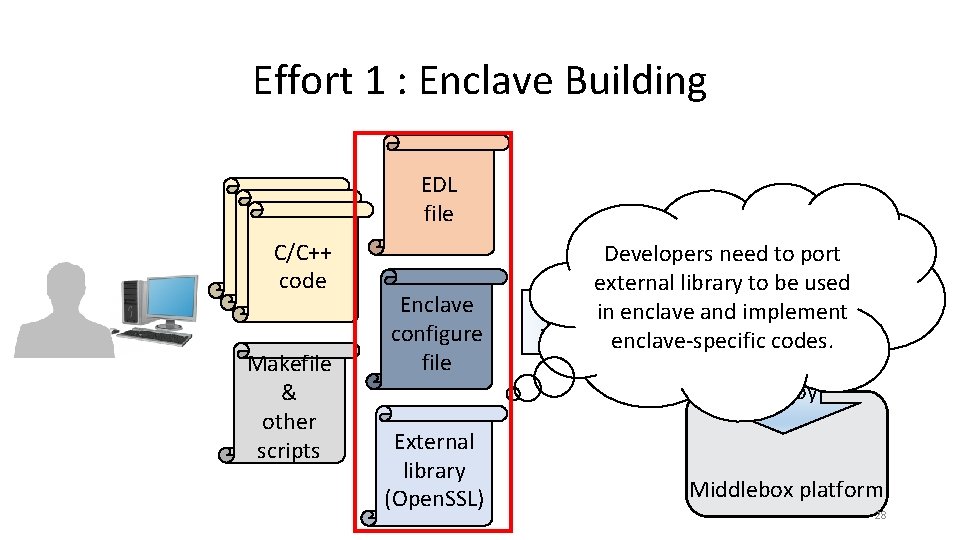
Effort 1 : Enclave Building C/C++ code Makefile & other scripts EDL file Enclave configure file External library (Open. SSL) Developers need to port Application external library to be used binary SGXin enclave and implement Enclave Toolchain enclave-specific codes. binary Deploy Middlebox platform 28
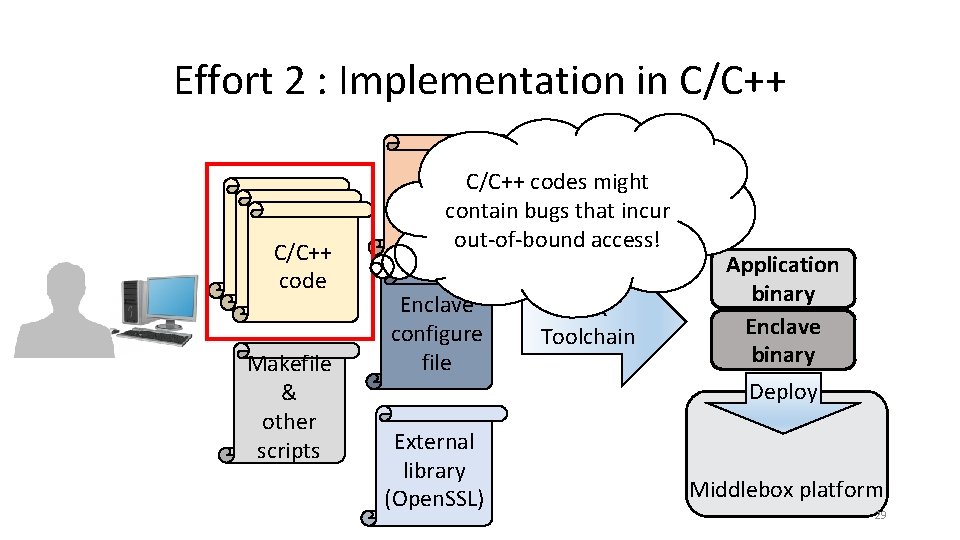
Effort 2 : Implementation in C/C++ code C/C++ code Makefile & other scripts EDL C/C++ codes might filecontain bugs that incur out-of-bound access! Enclave configure file External library (Open. SSL) SGX Toolchain Application binary Enclave binary Deploy Middlebox platform 29
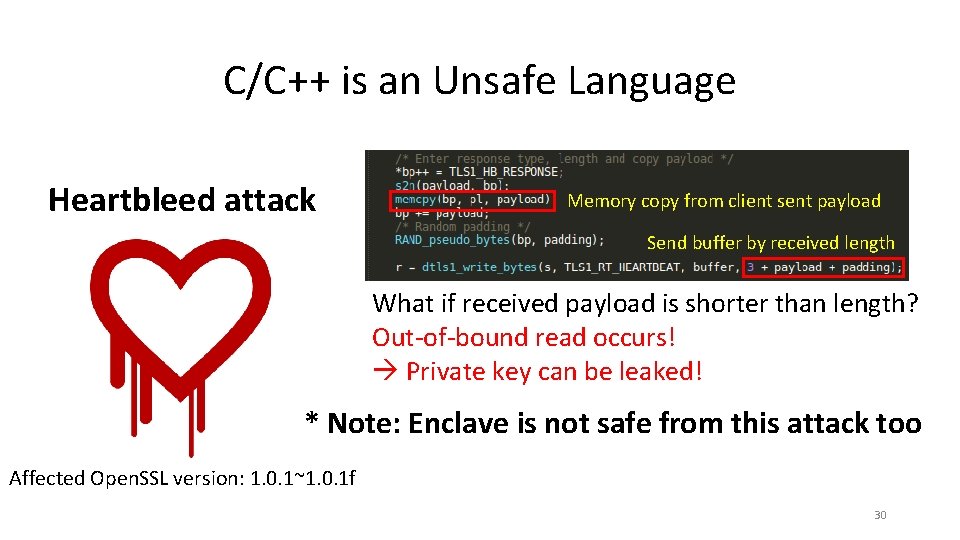
C/C++ is an Unsafe Language Heartbleed attack Memory copy from client sent payload Send buffer by received length What if received payload is shorter than length? Out-of-bound read occurs! Private key can be leaked! * Note: Enclave is not safe from this attack too Affected Open. SSL version: 1. 0. 1~1. 0. 1 f 30
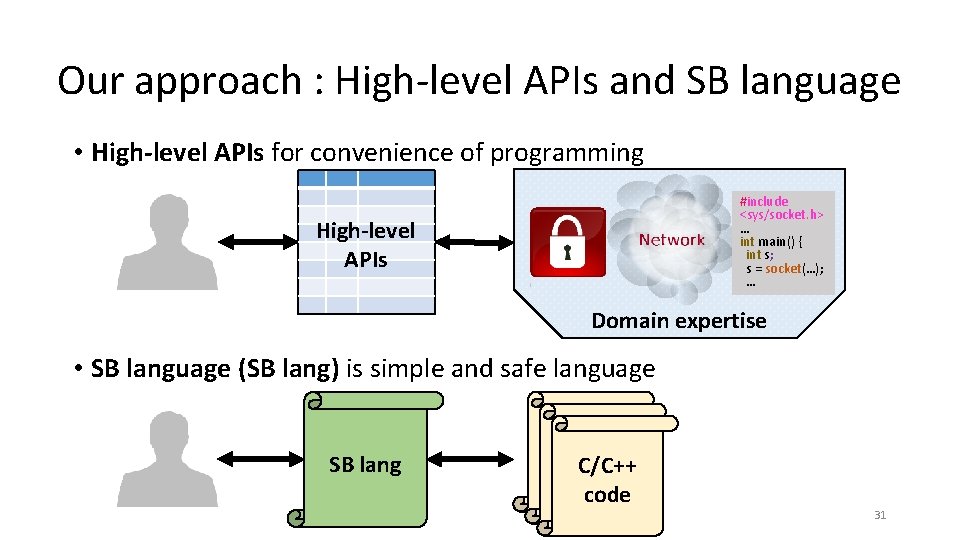
Our approach : High-level APIs and SB language • High-level APIs for convenience of programming #include <sys/socket. h> … int main() { int s; s = socket(…); … High-level APIs Domain expertise • SB language (SB lang) is simple and safe language SB lang C/C++ code 31
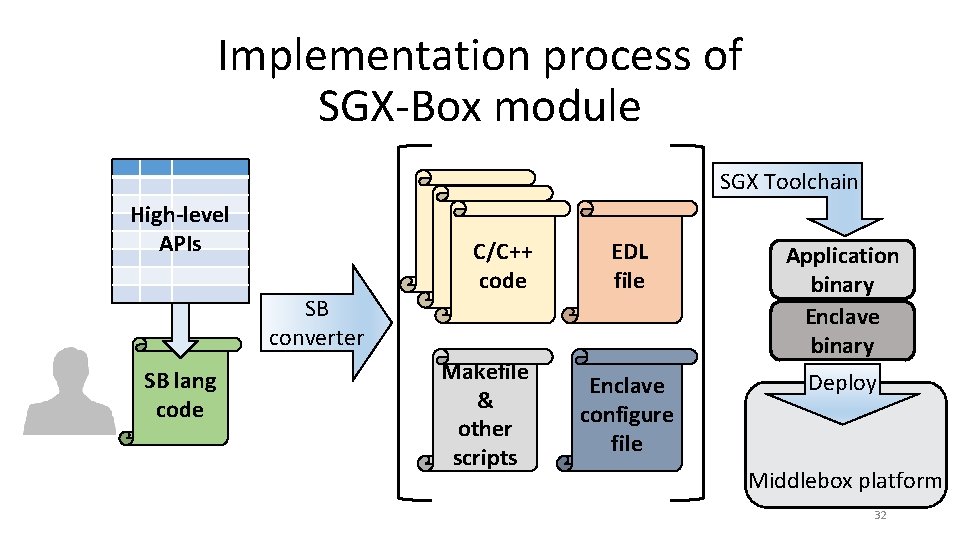
Implementation process of SGX-Box module SGX Toolchain High-level APIs SB converter SB lang code C/C++ code Makefile & other scripts EDL file Application binary Enclave configure file Deploy Middlebox platform 32
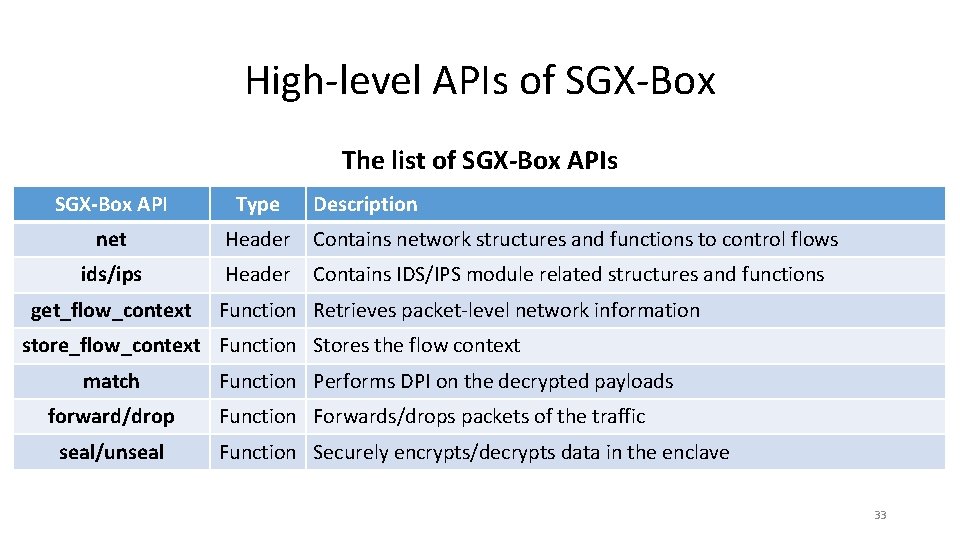
High-level APIs of SGX-Box The list of SGX-Box APIs SGX-Box API Type net Header Contains network structures and functions to control flows ids/ips Header Contains IDS/IPS module related structures and functions get_flow_context Description Function Retrieves packet-level network information store_flow_context Function Stores the flow context match forward/drop seal/unseal Function Performs DPI on the decrypted payloads Function Forwards/drops packets of the traffic Function Securely encrypts/decrypts data in the enclave 33
Preliminary Evaluation • Environment setup : • • CPU: Quad core Intel i 7 -6700 3. 4 GHz CPU OS: Ubuntu kernel 4. 4. 0. Intel SGX version: Linux SDK 1. 8 A client, a server, and an SGX-Box run in the same host • Case study : a proof-of-concept IDS • Performance overhead of SGX-Box 34
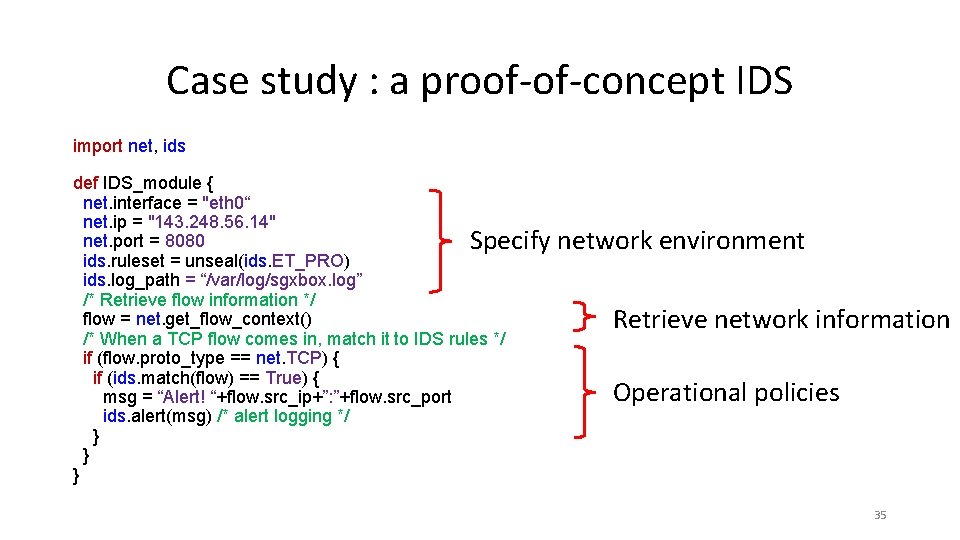
Case study : a proof-of-concept IDS import net, ids def IDS_module { net. interface = "eth 0“ net. ip = "143. 248. 56. 14" net. port = 8080 Specify ids. ruleset = unseal(ids. ET_PRO) ids. log_path = “/var/log/sgxbox. log” /* Retrieve flow information */ flow = net. get_flow_context() /* When a TCP flow comes in, match it to IDS rules */ if (flow. proto_type == net. TCP) { if (ids. match(flow) == True) { msg = “Alert! “+flow. src_ip+”: ”+flow. src_port ids. alert(msg) /* alert logging */ } } } network environment Retrieve network information Operational policies 35
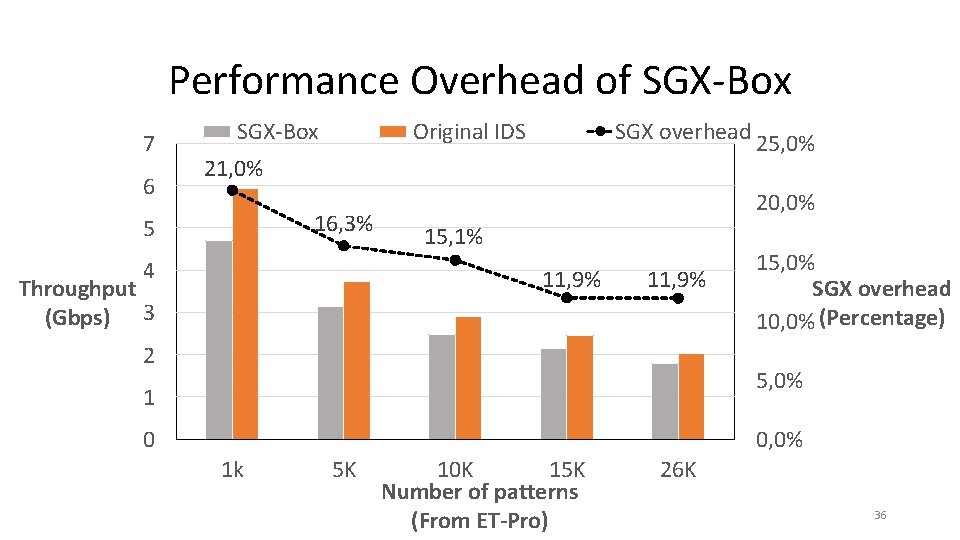
Performance Overhead of SGX-Box 7 6 SGX-Box Original IDS SGX overhead 21, 0% 16, 3% 5 4 20, 0% 15, 1% 11, 9% Throughput (Gbps) 3 25, 0% 11, 9% 2 15, 0% SGX overhead 10, 0% (Percentage) 5, 0% 1 0 0, 0% 1 k 5 K 10 K 15 K Number of patterns (From ET-Pro) 26 K 36
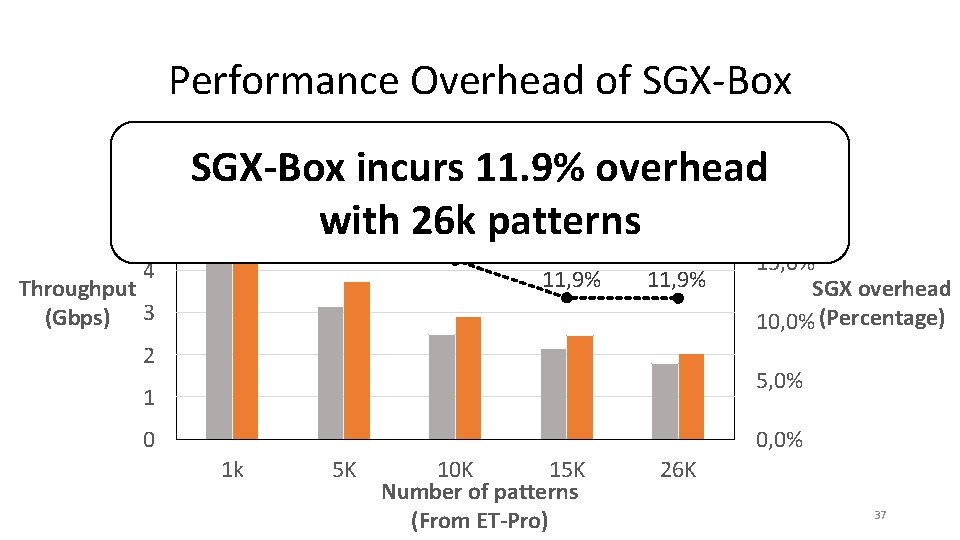
Performance Overhead of SGX-Box 7 6 5 SGX-Box Original IDS SGX overhead 25, 0% 21, 0% SGX-Box incurs 11. 9% overhead 20, 0% 16, 3% with 26 k 15, 1% patterns 4 11, 9% Throughput (Gbps) 3 11, 9% 2 15, 0% SGX overhead 10, 0% (Percentage) 5, 0% 1 0 0, 0% 1 k 5 K 10 K 15 K Number of patterns (From ET-Pro) 26 K 37
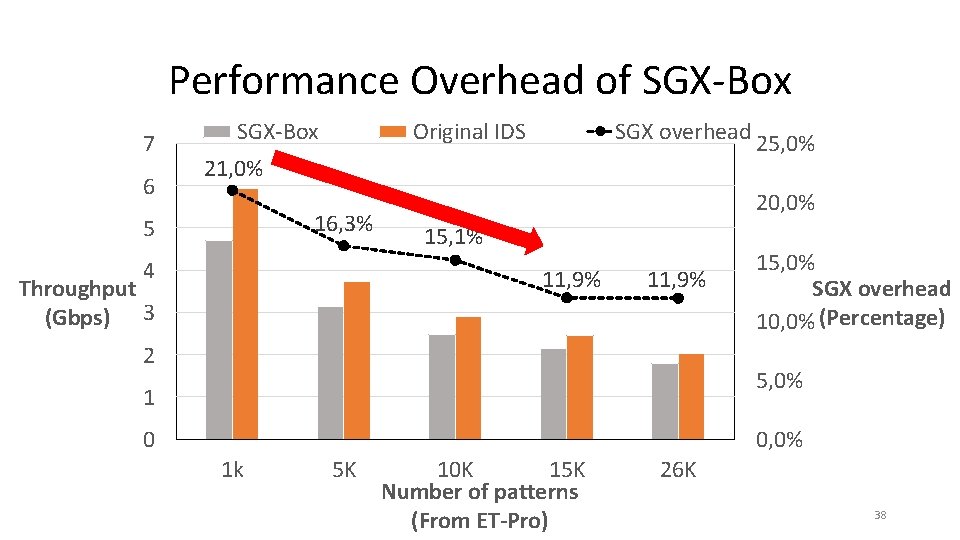
Performance Overhead of SGX-Box 7 6 SGX-Box Original IDS SGX overhead 21, 0% 16, 3% 5 4 20, 0% 15, 1% 11, 9% Throughput (Gbps) 3 25, 0% 11, 9% 2 15, 0% SGX overhead 10, 0% (Percentage) 5, 0% 1 0 0, 0% 1 k 5 K 10 K 15 K Number of patterns (From ET-Pro) 26 K 38
Conclusion • New middlebox system that enables visibility on encrypted traffic to enable deep packet inspection by leveraging SGX technology • SGX-Box does not leak user’s private data - All decryption and decrypted packet inspection performs inside of enclave - Carefully shares server’s session key through out-of-band secure channel • SGX-Box has moderate performance overhead • Case study : proof-of-concept IDS shows programming convenience - High-level APIs enables implementing SGX-Box module without in-depth knowledge of the usage of cryptographic libraries 39
- Slides: 39