Security Zones Intro to Cyber Security The DMZ
Security Zones Intro to Cyber Security
The DMZ The “demilitarized” zone • Ground for separating two opposing forces • Set up by agreement • For the purpose of acting as a buffer between the two sides
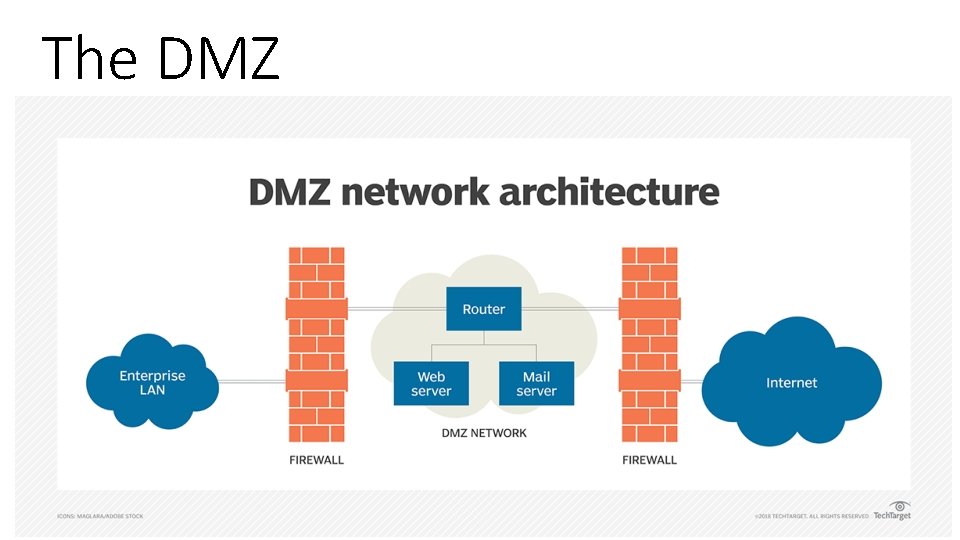
The DMZ
The DMZ Provides publicly visible services without allowing untrusted users access to your internal network
The DMZ If the outside user makes a request for a resource from the trusted network, such as a data element from an internal database that is accessed via a publicly visible page in the DMZ, the request needs to follow proper policies and procedures:
The DMZ If the outside user makes a request for a resource from the trusted network: 1. User from the untrusted network (the internet) requests data via a web page from a web server on the DMZ
The DMZ If the outside user makes a request for a resource from the trusted network: 2. Web server in the DMZ requests the data from the application server, which can be in the DMZ or in the inner, trusted network
The DMZ If the outside user makes a request for a resource from the trusted network: 3. The application server requests the data from the database server in the trusted network
The DMZ If the outside user makes a request for a resource from the trusted network: 4. The database server returns the data to the requesting application server
The DMZ If the outside user makes a request for a resource from the trusted network: 5. The application server returns the data to the requesting web server.
The DMZ If the outside user makes a request for a resource from the trusted network: 6. The web server returns the data to the requesting user from the untrusted network
The DMZ Separation accomplishes two specific, independent tasks 1. User is separated from the request for data on a secure network • Intermediaries do the requesting • Layered approach allows significant security levels to be enforced • Users do not have direct access or control over their requests
The DMZ Separation accomplishes two specific, independent tasks 2. Scalability is more easily realized • Multiple-server solutions will allow for millions of users • Will not slow down any particular layer
Internet • Yes, the Internet is its own zone • Even if your network doesn’t have direct contact with a resource, as long as a neighbor, or a neighbor’s neighbor, and so on, can get there, so can you • “Untrusted Zone”…but does not make the Internet a bad thing
Intranet • Same functionality as the Internet for users • ***Lies completely inside the trusted area of a network • Under the security control of a system and network admin
Intranet • Content not available over the Internet to untrusted users • Duplication of information onto machines in the DMZ can be made available OR an Extranet can be created to publish material to trusted partners
Extranet • Extension of a selected portion of a company’s intranet to external partners • Allows to share information to customers, suppliers, partners, and other trusted groups while using INTERNET protocols • Ensures privacy and security
Wireless • Different security perspective than physical networks • Good practice to be a separate zone • Secure User Connections v. Guest Connections • Guest connections created on the network will isolate traffic to allow inspection before allowing it to interact with more critical resources
Virtual LAN (VLAN) • “Logical implementation” • Allows computers connected to different physical networks to act and communicate as if they were on the same physical network • Uses switches and software
Virtual LAN (VLAN) • Trunking-process of spanning a single VLAN across multiple switches • See example in textbook on Page 266
VLANs and Security • Single network…multiple subnets based on functionality • Departments in example can share switch because of proximity, yet have SEPARATE traffic domains
- Slides: 21