QuadtreesBased Image Authentication Technique Source IEICE Trans Fundamentals
Quadtrees-Based Image Authentication Technique Source: IEICE Trans. Fundamentals, Vol. E 87 -A, No. 4 April 2004 pp. 946948 Author: Hong. Xia Wang, Chen He, Ke Ding Speaker: Chih Chiang Tsou Date: 2004. 4. 28 1
Outline Introduction of Image Authentication ¡ Quadtrees-Based Image Authentication Technique ¡ Experimental results ¡ Conclusion ¡ 2
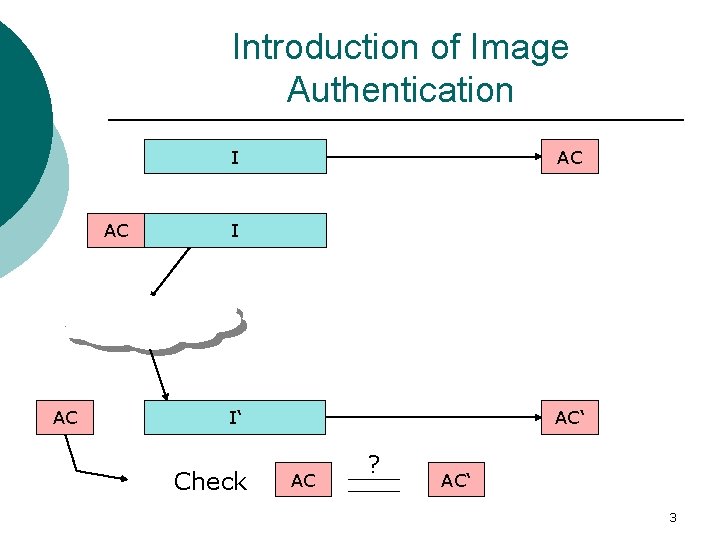
Introduction of Image Authentication I AC AC AC I I‘ Check AC‘ AC ? AC‘ 3
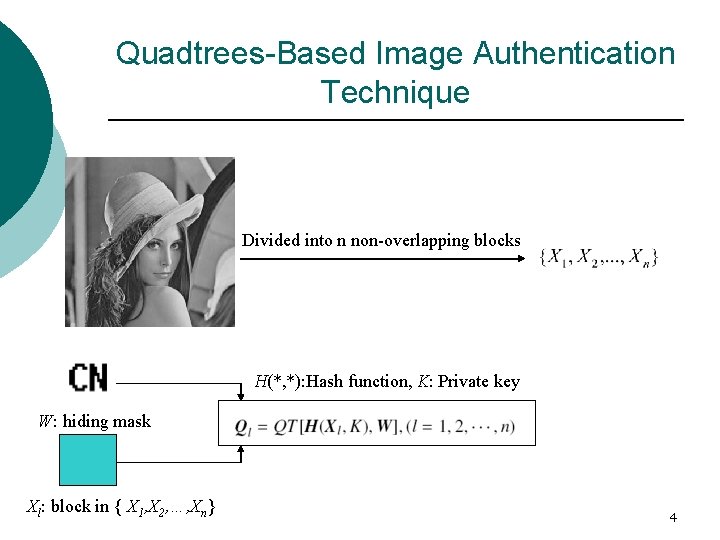
Quadtrees-Based Image Authentication Technique Divided into n non-overlapping blocks H(*, *): Hash function, K: Private key W: hiding mask Xl: block in { X 1, X 2, …, Xn} 4
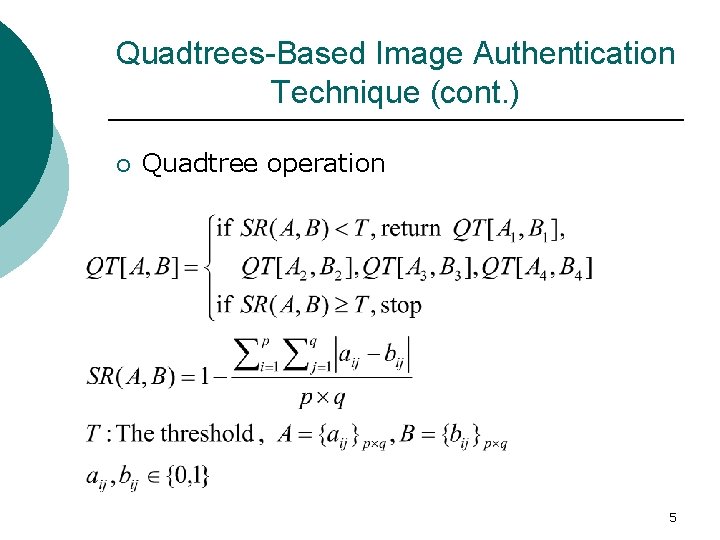
Quadtrees-Based Image Authentication Technique (cont. ) ¡ Quadtree operation 5
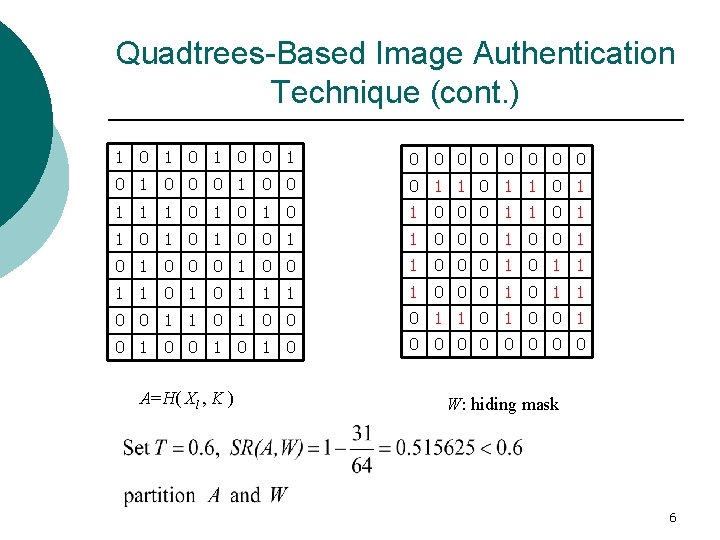
Quadtrees-Based Image Authentication Technique (cont. ) 1 0 1 0 0 0 1 0 0 0 1 1 0 1 0 1 0 0 0 1 1 0 1 0 0 1 1 0 0 0 1 0 0 0 1 0 1 1 1 1 0 0 0 1 1 0 1 0 1 0 0 0 0 0 A=H( Xl , K ) W: hiding mask 6
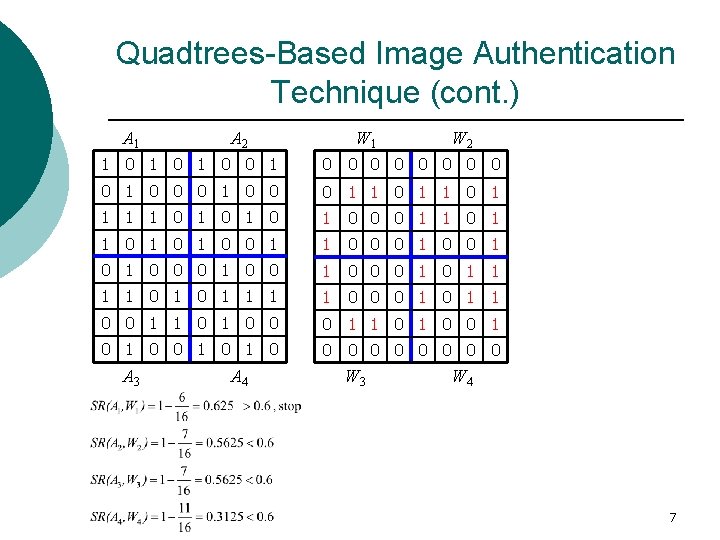
Quadtrees-Based Image Authentication Technique (cont. ) A 1 A 2 W 1 W 2 1 0 1 0 0 0 1 0 0 0 1 1 0 1 0 1 0 0 0 1 1 0 1 0 0 1 1 0 0 0 1 0 0 0 1 0 1 1 1 1 0 0 0 1 1 0 1 0 1 0 0 0 0 0 A 3 A 4 W 3 W 4 7
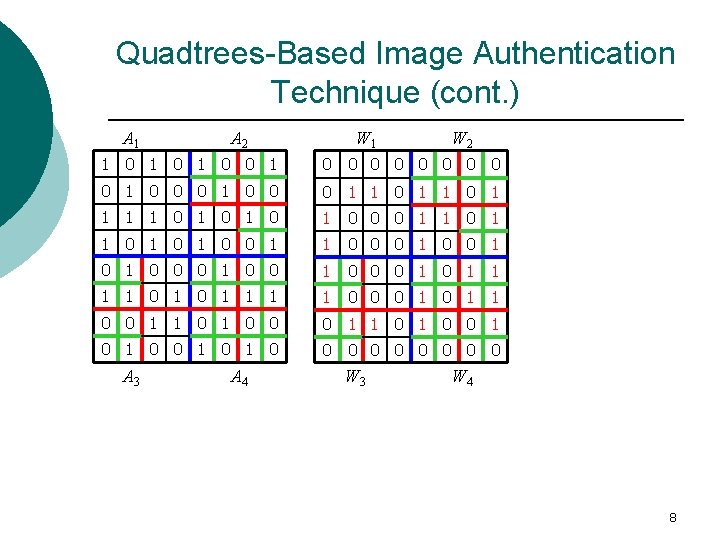
Quadtrees-Based Image Authentication Technique (cont. ) A 1 A 2 W 1 W 2 1 0 1 0 0 0 1 0 0 0 1 1 0 1 0 1 0 0 0 1 1 0 1 0 0 1 1 0 0 0 1 0 0 0 1 0 1 1 1 1 0 0 0 1 1 0 1 0 1 0 0 0 0 0 A 3 A 4 W 3 W 4 8
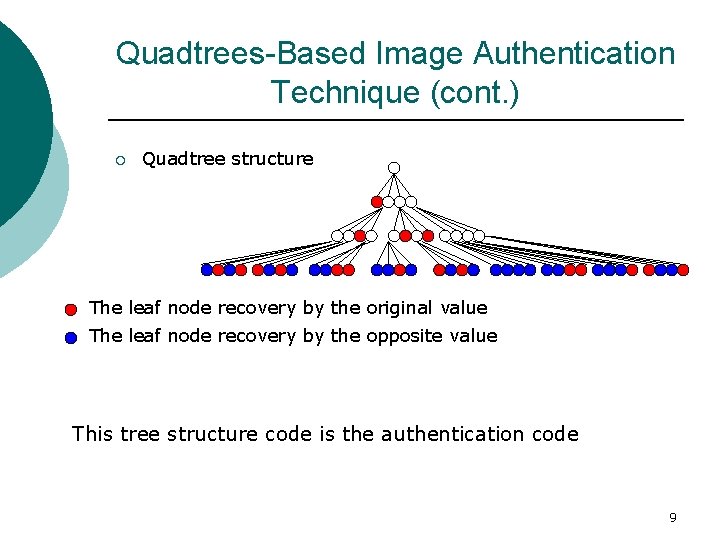
Quadtrees-Based Image Authentication Technique (cont. ) ¡ Quadtree structure The leaf node recovery by the original value The leaf node recovery by the opposite value This tree structure code is the authentication code 9
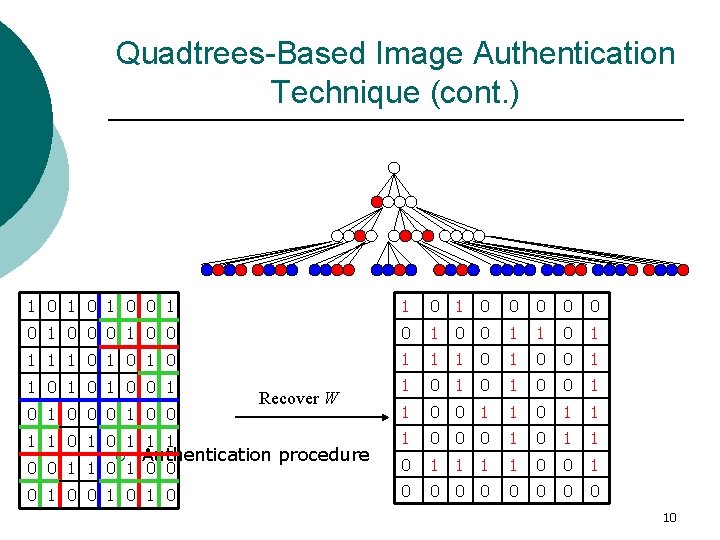
Quadtrees-Based Image Authentication Technique (cont. ) 1 0 1 0 0 1 1 0 0 0 0 1 0 0 1 1 1 1 0 1 0 0 1 1 0 1 0 0 1 1 0 1 1 1 1 0 0 0 1 1 0 0 1 0 1 0 0 0 0 0 1 0 0 ¡ Recover W Authentication procedure 10
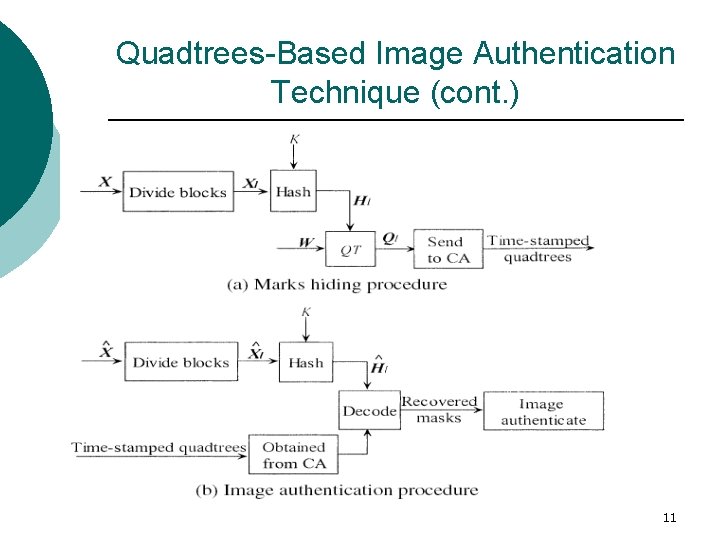
Quadtrees-Based Image Authentication Technique (cont. ) 11
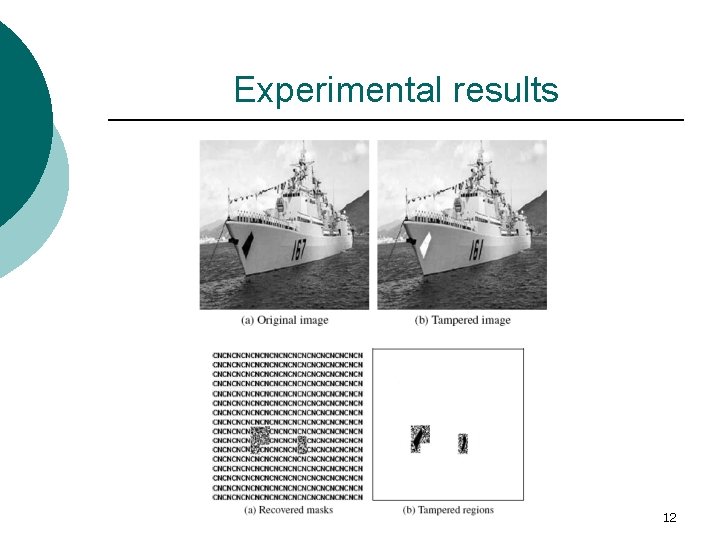
Experimental results 12
Conclusion This method can’t distinguish between modification and tampering. ¡ The quadtrees authentication codes aren’t small enough (Because of the hash function) ¡ 13
- Slides: 13