COEN 351 Authentication Authentication n Authentication is based
COEN 351 Authentication
Authentication n Authentication is based on n What you know n n What you have n n Biometrics: fingerprints, Iris, voice, … Where you are n n (Physical) keys, tokens, smart-card What you are n n Passwords, Pins, Answers to questions, … IP-address (not very secure), … Who else trusts you n Certification by trusted third party, …
Authentication n Passwords, Pins, … threatened by n External disclosure n n Guessing n n n Brute forcing, dictionary attack, … Snooping n n Looking over the shoulder, social engineering Finds unencrypted passwords Circumvention through replay Host compromise n That hands out password file.
Authentication n Password protection mechanisms n Transformation: Password presented by user to client is hashed, hash is sent to server. Server compares with hash of password. n n Challenge-response n n n Protects against replay attacks. Time stamps n n UNIX Salting: Each hash is different. Authentication request from client to server depends on time. Protects against replays. One-time passwords Digital Signature with every request. Zero-Knowledge techniques
Authentication Kerberos: n Authentication system based on symmetric cryptography n For patent reasons
Kerberos n n Every user / client / server shares a key with the authentication server. Authentication server hands out tickets to all other servers.
Kerberos n First exchange between user and Authentication Server establishes a session key. n This way, the same key is used only sparingly.
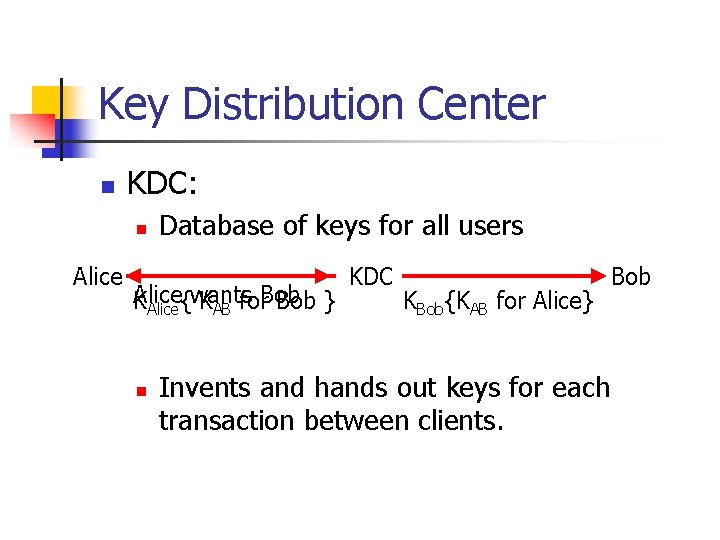
Key Distribution Center n KDC: n Alice Database of keys for all users Alice KAlice{wants KAB for. Bob } n KDC KBob{KAB for Alice} Invents and hands out keys for each transaction between clients. Bob
Personal Tokens n Small hardware devices that use a pin to unlock. n n Storage Token: contains a secret value. Synchronous one-time password generator n n Challenge Response: n n Generates a new password once a minute. Implements the calculation of the response from a challenge according to a secret algorithm. Digital Signature Token: n Calculates digital signature from message MAC.
Personal Tokens n Human Interface Token. n n Smartcard n n n Handheld with digital display (and keyboard). Dimensions and contacts standardized by ISO/IEC. PCMCIA card USB token
Biometrics n n n Fingerprint recognition Voice recognition Handwriting recognition Face recognition Retinal scan Hand geometry recognition
- Slides: 11