COEN 351 ECommerce Security Public Key Infrastructure Assessment
COEN 351: E-Commerce Security Public Key Infrastructure Assessment and Accreditation
Assessment for PKI n Assessment: n Prescribed procedure for determining whether a system or one of its components satisfies defined criteria for trustworthiness and quality.
Assessment for PKI n Assessment: n Creates favorable legal presumptions. n n Necessary for licensing and accreditation. Potential formal requirement for PKI interoperation. n n n Legal status. Stronger presumptions for non-repudiation. This is the motivating example. Creates public relations bonus and generates acceptance. Helps in risk assessment and management. n Might be required for insurance purposes.
Assessment for PKI n Assessment is used by: n n n Service subscribers. Relying parties. Policy management authorities. Certification and registration authorities. Licensing and regulatory authorities.
Assessment for PKI n Formal qualification of Assessors n n n Some laws require assessors to be Certified Public Accountants. Others specify required years of work in the security profession. Material qualifications of Assessors n n n Independence. Quality assurance for assessment work. Educational and training qualifications.
Assessment for PKI n Assessment targets: n (System-level) n n n The overall PKI environment. Systems and Subsystems. Discrete Components. PKI cryptomodules. (Entity) n n n Primary certification authority controls. Key and device management console. Certificate life-cycle controls.
Assessment for PKI n Attributes of successful assessment criteria n Appropriateness. n n Objectivity. Clarity. Ubiquity. n n Develop threat model first. general acceptance. Extensibility. n Criteria can be updated for future developments. )
Assessment for PKI n n n Self-assessment. Internal audit. External audit.
System Assessment Criteria n Formal criteria have evolved: n U. S. Trusted Computer System Evaluation Criteria (TCSEC) 1985. n Orange Book. n n Focused on confidentiality to protect national security secrets. European Information Technology Security Evaluation Criteria (ITSEC) 1991.
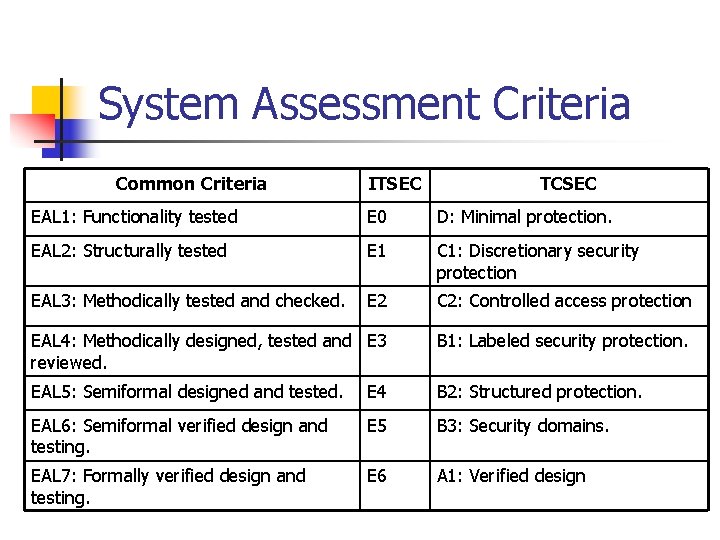
System Assessment Criteria Common Criteria ITSEC TCSEC EAL 1: Functionality tested E 0 D: Minimal protection. EAL 2: Structurally tested E 1 C 1: Discretionary security protection EAL 3: Methodically tested and checked. E 2 C 2: Controlled access protection EAL 4: Methodically designed, tested and E 3 reviewed. B 1: Labeled security protection. EAL 5: Semiformal designed and tested. E 4 B 2: Structured protection. EAL 6: Semiformal verified design and testing. E 5 B 3: Security domains. EAL 7: Formally verified design and testing. E 6 A 1: Verified design
Assessment & Accreditation Schemes n Australia, Gatekeeper: n n Australian government effort to enhance secure service delivery, streamline secure intragovernmental transactions, establish a “rational voluntary mechanism for the implementation of PKI by government agencies. ” Gatekeeper is also used to provide interoperationality among PKI providers. Mandatory for vendors of PKI services for government. Gatekeeper has two levels of authentication: n n Entry-level Full accreditation
System Assessment Criteria n Canada: Government of Canada PKI n n Allows links via cross-certification. Expert teams establish tables of concordance between requester’s Certificate Policy (CP) and Go. C PKI.
System Assessment Criteria n US: Light Touch n n State legislation influenced by Utah and Washington. Reciprocity agreements (e. g. Minnesota, Utah, Washington)
System Assessment Criteria n HIPAA n Requires security controls to ensure the integrity and confidentiality of Internet communications.
- Slides: 14