Invisibly Sanitizable Signature without Pairings IEICE TRANS FUNDAMENTALSM
Invisibly Sanitizable Signature without Pairings IEICE TRANS. FUNDAMENTALSM VOL. E 92 -A, NO. 6 JUNE 2009 Dae Hyun YUN, Pil Joong LEE Adviser: 鄭錦楸 , 郭文中 教授 Reporter: 林彥宏 1
Outline Introduction Proposed Scheme Security Analysis Conclusions 2
Introduction subdocument (m 1||m 2) hi=hash(mi||ri) σ=Sign(h 1||h 2) (σ, r 1, r 2) → (σ, h 1, r 2) Digitally Signed Document Sanitizing Scheme Based on Bilinear Maps propose a new invisible sanitizable signature scheme based on the RSA signature 3
Proposed Scheme document M={M 1, …, Mn} disclosure condition Ci have one of three values: SANI: sanitized DASP: disclosed and additional sanitizing is prohibited DASA: disclosed and additional sanitizing is allowed Key generation: N=P ×Q, P and Q are primes e ×d=1 mod ψ(N) Public key (N, e) Private key (N, d) 4
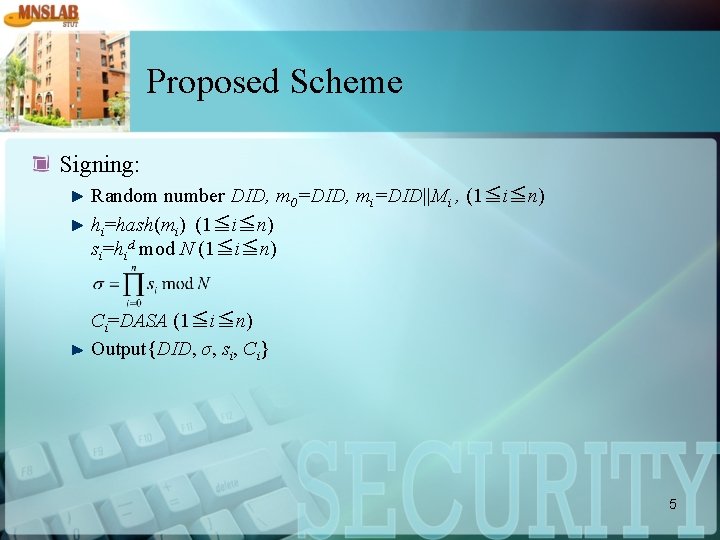
Proposed Scheme Signing: Random number DID, m 0=DID, mi=DID||Mi , (1≦i≦n) hi=hash(mi) (1≦i≦n) si=hid mod N (1≦i≦n) Ci=DASA (1≦i≦n) Output{DID, σ, si, Ci} 5
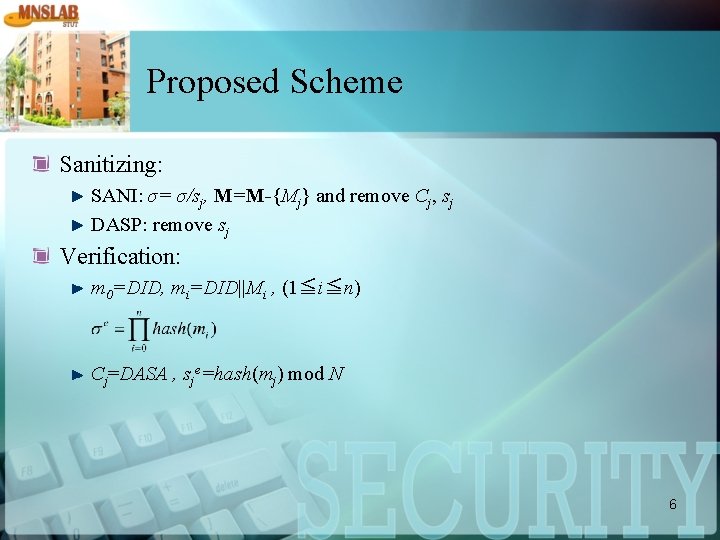
Proposed Scheme Sanitizing: SANI: σ= σ/sj, M=M-{Mj} and remove Cj, sj DASP: remove sj Verification: m 0=DID, mi=DID||Mi , (1≦i≦n) Cj=DASA , sje=hash(mj) mod N 6

Security Analysis Privacy: infeasible to retrieve any information on sanitized subdocument Invisibility: infeasible to find out, weather or not the signed document has been sanitized Unforgeability: infeasible to generate a signed document that has not been signed before or to delete a subdocument of signed documents without signer’s private key 7
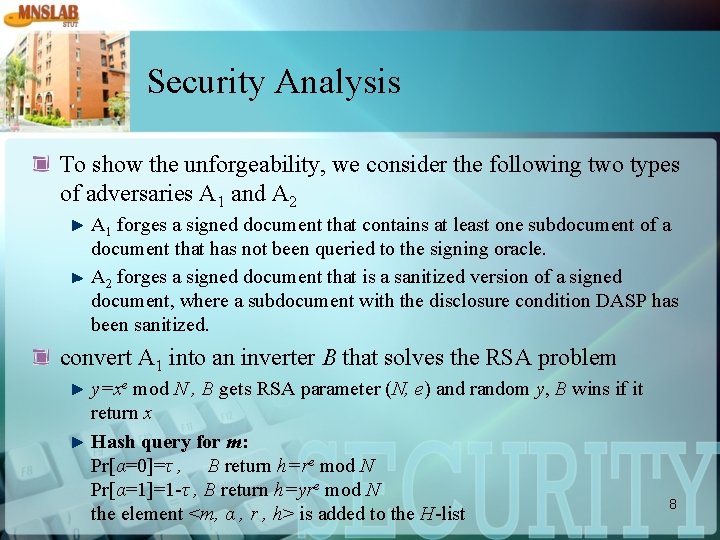
Security Analysis To show the unforgeability, we consider the following two types of adversaries A 1 and A 2 A 1 forges a signed document that contains at least one subdocument of a document that has not been queried to the signing oracle. A 2 forges a signed document that is a sanitized version of a signed document, where a subdocument with the disclosure condition DASP has been sanitized. convert A 1 into an inverter B that solves the RSA problem y=xe mod N , B gets RSA parameter (N, e) and random y, B wins if it return x Hash query for m: Pr[α=0]=τ , B return h=re mod N Pr[α=1]=1 -τ , B return h=yre mod N the element <m, α , r , h> is added to the H-list 8
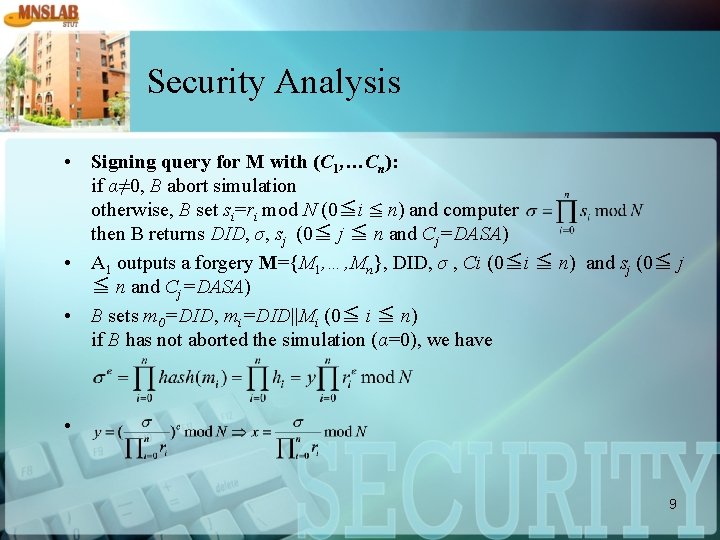
Security Analysis • Signing query for M with (C 1, …Cn): if α≠ 0, B abort simulation otherwise, B set si=ri mod N (0≦i ≦ n) and computer then B returns DID, σ, sj (0≦ j ≦ n and Cj=DASA) • A 1 outputs a forgery M={M 1, …, Mn}, DID, σ , Ci (0≦i ≦ n) and sj (0≦ j ≦ n and Cj=DASA) • B sets m 0=DID, mi=DID||Mi (0≦ i ≦ n) if B has not aborted the simulation (α=0), we have • 9

Security Analysis A 1 succeeds in forgery with a non-negligible probability ε, then B can solve the RSA problem with probability f(τ)= At f(τ) becomes 10
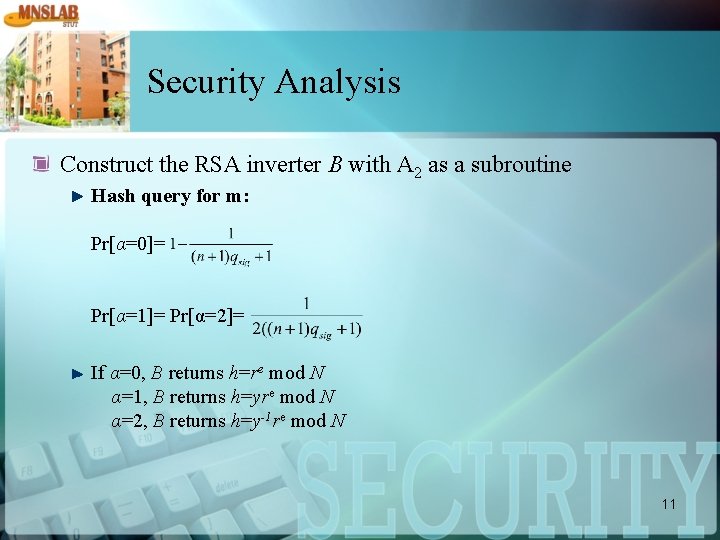
Security Analysis Construct the RSA inverter B with A 2 as a subroutine Hash query for m: Pr[α=0]= Pr[α=1]= Pr[α=2]= If α=0, B returns h=re mod N α=1, B returns h=yre mod N α=2, B returns h=y-1 re mod N 11

Security Analysis Signing query for M with(C 1, …, Cn): assume C 1=DASP if αi=0, B sets si=ri mod N (0≦ i ≦ n) and computes if α 0=1, α 1=2, and αi=0 (i ≠ 0, 1), B sets si=ri mod N (i ≠ 0, 1) and computes otherwise B aborts the simulation B returns DID, σ, sj (1≦ j ≦ n and Cj=DASA) A 2 output a forgery M={M 1, …, Mn}, DID, σ, Ci (0≦ i ≦ n) and sj (1≦j≦n and Cj=DASA) B sets m 0=DID, mi=DID||Mi (1≦ i ≦ n) B proceeds only if α 0=1 and αi=0 for (1≦ i ≦ n) , which means that A 2 sanitized a subdocument with the disclosure condition DASP 12

Security Analysis If B has not aborted the simulation, we have Thus B can return x (1) in the signing queries, either αi=0 (0≦i≦n) or α 0=1, α 1=2, αi=0 (2≦i≦n), which happens with probability at least 13
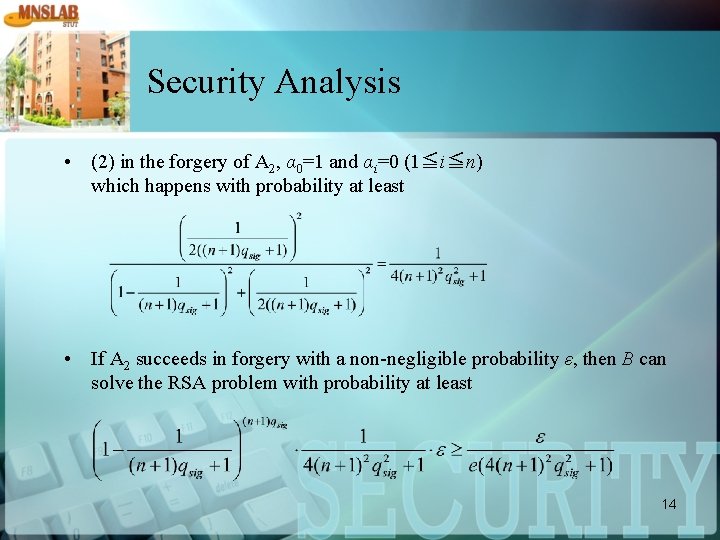
Security Analysis • (2) in the forgery of A 2, α 0=1 and αi=0 (1≦i≦n) which happens with probability at least • If A 2 succeeds in forgery with a non-negligible probability ε, then B can solve the RSA problem with probability at least 14
Conclusions We proposed an invisibly sanitizable signature scheme without paring and proved its security under the RSA assumption. Our result also shows that aggregate signature is not necessary for the construction of invisibly sanitizable signatures. 15
- Slides: 15