Oblivious Transfer OT Zero Knowledge Proof ZKP Perfect
Oblivious Transfer (OT) Zero Knowledge Proof (ZKP) Perfect Forward Secrecy (PFS) Slides Original Source: 1. M. Stamp, “Information Security: Principles and Practice, ” John Wiley 2. Slides from Dr. Sultan Almuhammadi 3. Wikipedia: https: //en. wikipedia. org/wiki/Oblivious_transfer
Outline • Oblivious Transfer (OT) • Zero Knowledge Proof (ZKP) • Perfect Forward Secrecy (PFS) 2/92
Outline • Oblivious Transfer (OT) • Zero Knowledge Proof (ZKP) • Perfect Forward Secrecy (PFS) 3/92
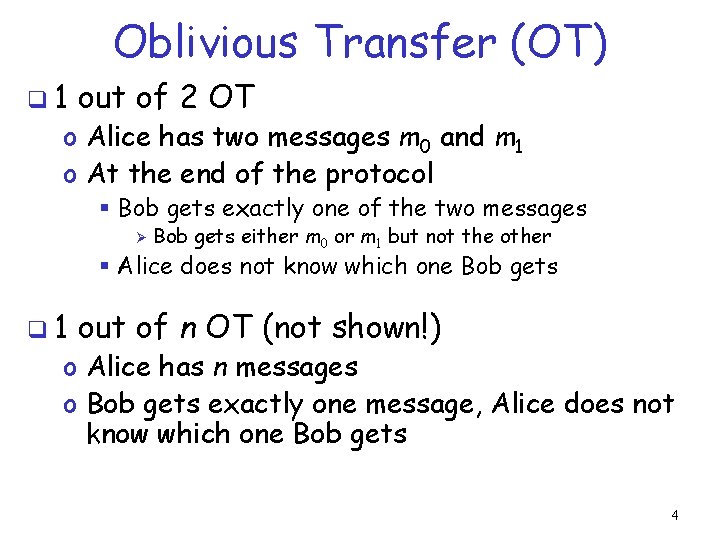
Oblivious Transfer (OT) q 1 out of 2 OT o Alice has two messages m 0 and m 1 o At the end of the protocol § Bob gets exactly one of the two messages Ø Bob gets either m 0 or m 1 but not the other § Alice does not know which one Bob gets q 1 out of n OT (not shown!) o Alice has n messages o Bob gets exactly one message, Alice does not know which one Bob gets 4
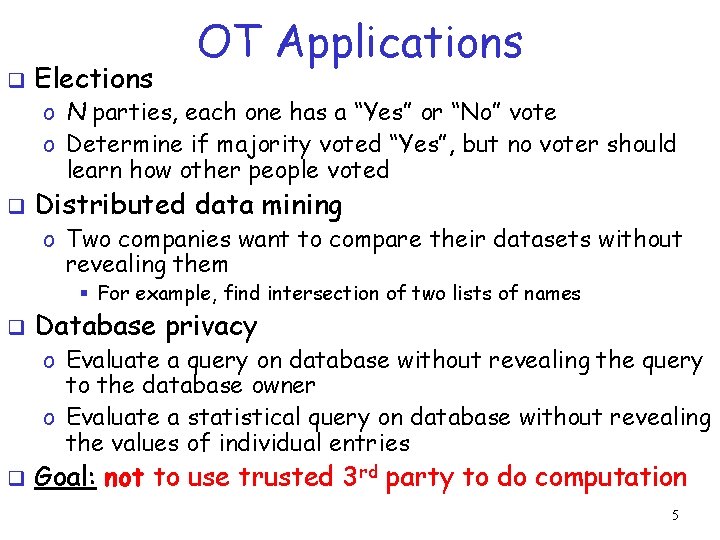
q Elections OT Applications o N parties, each one has a “Yes” or “No” vote o Determine if majority voted “Yes”, but no voter should learn how other people voted q Distributed data mining o Two companies want to compare their datasets without revealing them § For example, find intersection of two lists of names q Database privacy o Evaluate a query on database without revealing the query to the database owner o Evaluate a statistical query on database without revealing the values of individual entries q Goal: not to use trusted 3 rd party to do computation 5
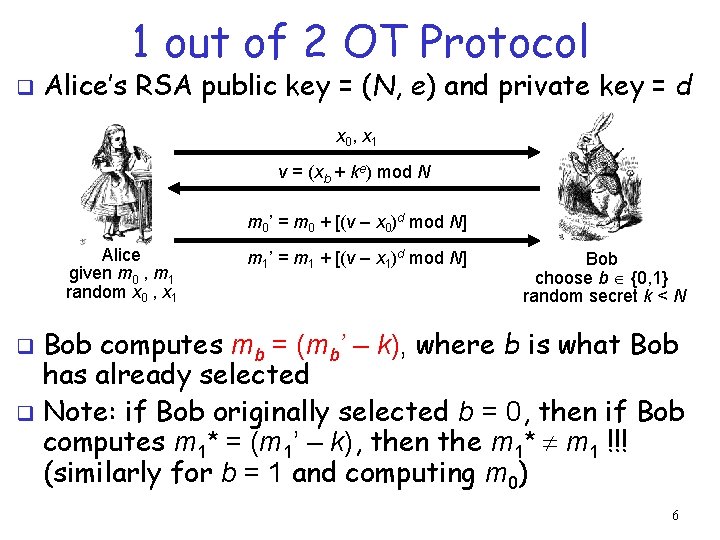
1 out of 2 OT Protocol q Alice’s RSA public key = (N, e) and private key = d x 0, x 1 v = (xb + ke) mod N m 0’ = m 0 + [(v – x 0)d mod N] Alice given m 0 , m 1 random x 0 , x 1 m 1’ = m 1 + [(v – x 1)d mod N] Bob choose b {0, 1} random secret k < N Bob computes mb = (mb’ – k), where b is what Bob has already selected q Note: if Bob originally selected b = 0, then if Bob computes m 1* = (m 1’ – k), then the m 1* m 1 !!! (similarly for b = 1 and computing m 0) q 6
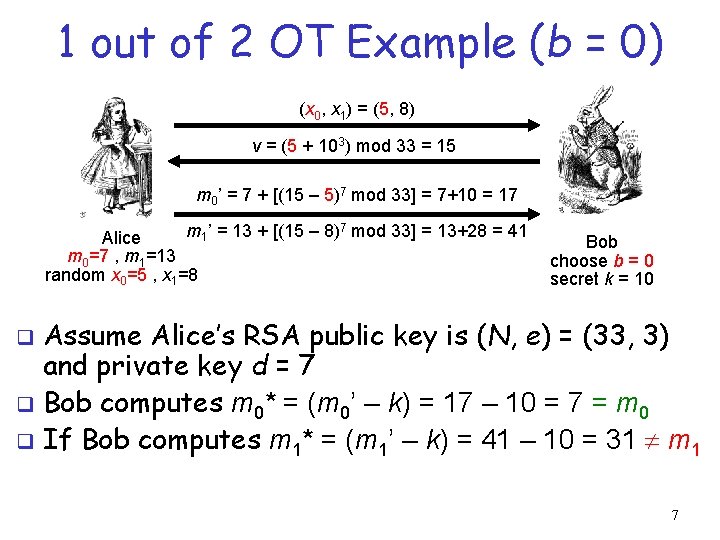
1 out of 2 OT Example (b = 0) (x 0, x 1) = (5, 8) v = (5 + 103) mod 33 = 15 m 0’ = 7 + [(15 – 5)7 mod 33] = 7+10 = 17 m 1’ = 13 + [(15 – 8)7 mod 33] = 13+28 = 41 Alice m 0=7 , m 1=13 random x 0=5 , x 1=8 Bob choose b = 0 secret k = 10 Assume Alice’s RSA public key is (N, e) = (33, 3) and private key d = 7 q Bob computes m 0* = (m 0’ – k) = 17 – 10 = 7 = m 0 q If Bob computes m 1* = (m 1’ – k) = 41 – 10 = 31 m 1 q 7
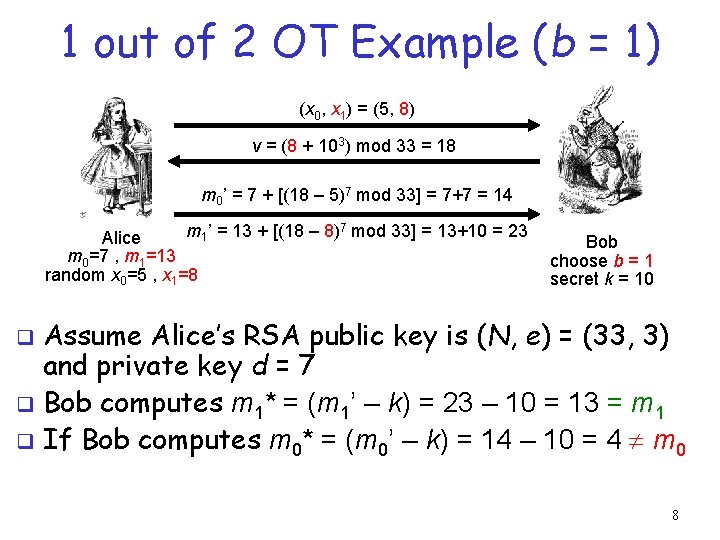
1 out of 2 OT Example (b = 1) (x 0, x 1) = (5, 8) v = (8 + 103) mod 33 = 18 m 0’ = 7 + [(18 – 5)7 mod 33] = 7+7 = 14 m 1’ = 13 + [(18 – 8)7 mod 33] = 13+10 = 23 Alice m 0=7 , m 1=13 random x 0=5 , x 1=8 Bob choose b = 1 secret k = 10 Assume Alice’s RSA public key is (N, e) = (33, 3) and private key d = 7 q Bob computes m 1* = (m 1’ – k) = 23 – 10 = 13 = m 1 q If Bob computes m 0* = (m 0’ – k) = 14 – 10 = 4 m 0 q 8
Outline • Oblivious Transfer (OT) • Zero Knowledge Proof (ZKP) • Perfect Forward Secrecy (PFS) 9/92
Zero Knowledge Proof (ZKP) q q Alice wants to prove that she knows a secret without revealing any info about it Bob must verify that Alice knows secret o But, Bob gains no info about the secret q Process is probabilistic o Bob can verify that Alice knows the secret to an arbitrarily high probability q q An “interactive proof system” Has wide range of applications in modern crypto systems 10
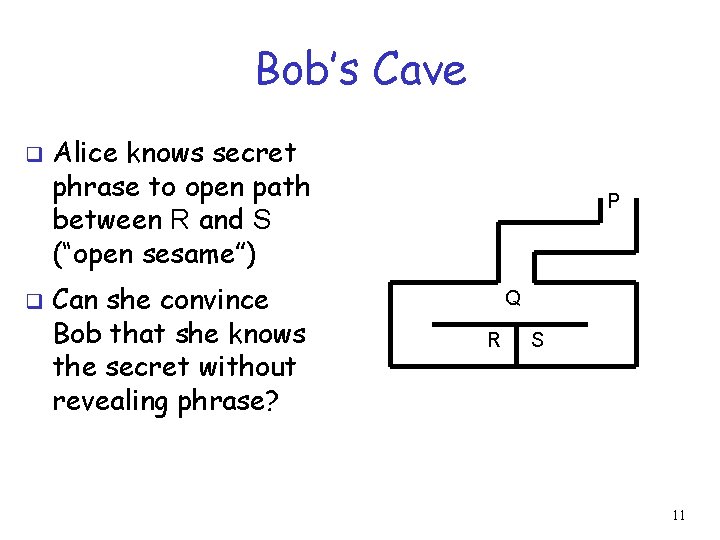
Bob’s Cave q q Alice knows secret phrase to open path between R and S (“open sesame”) Can she convince Bob that she knows the secret without revealing phrase? P Q R S 11
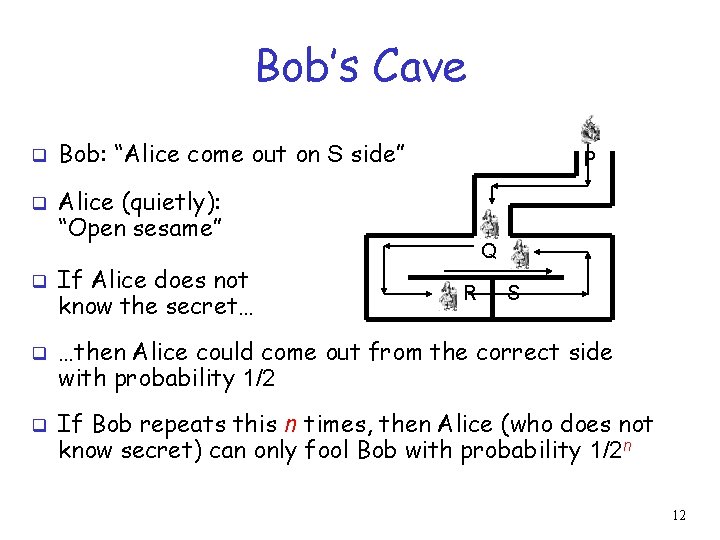
Bob’s Cave q q q Bob: “Alice come out on S side” P Alice (quietly): “Open sesame” If Alice does not know the secret… Q R S …then Alice could come out from the correct side with probability 1/2 If Bob repeats this n times, then Alice (who does not know secret) can only fool Bob with probability 1/2 n 12
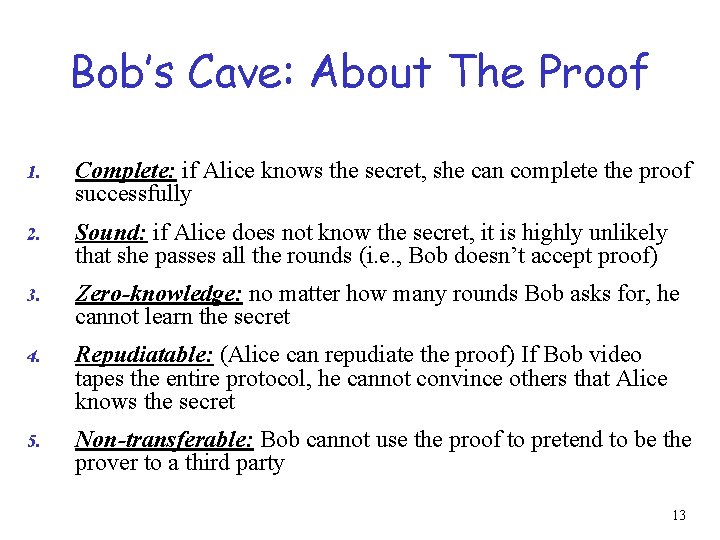
Bob’s Cave: About The Proof 1. Complete: if Alice knows the secret, she can complete the proof successfully 2. Sound: if Alice does not know the secret, it is highly unlikely that she passes all the rounds (i. e. , Bob doesn’t accept proof) 3. Zero-knowledge: no matter how many rounds Bob asks for, he cannot learn the secret 4. Repudiatable: (Alice can repudiate the proof) If Bob video tapes the entire protocol, he cannot convince others that Alice knows the secret 5. Non-transferable: Bob cannot use the proof to pretend to be the prover to a third party 13
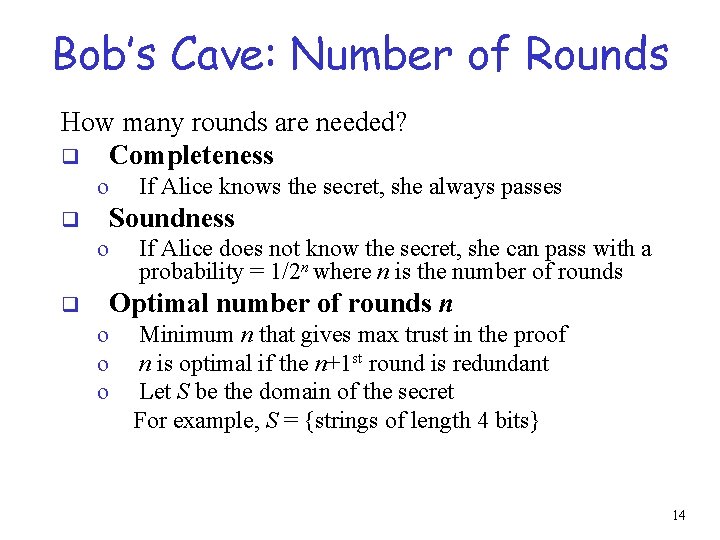
Bob’s Cave: Number of Rounds How many rounds are needed? q Completeness o If Alice knows the secret, she always passes Soundness q o If Alice does not know the secret, she can pass with a probability = 1/2 n where n is the number of rounds Optimal number of rounds n q o o o Minimum n that gives max trust in the proof n is optimal if the n+1 st round is redundant Let S be the domain of the secret For example, S = {strings of length 4 bits} 14
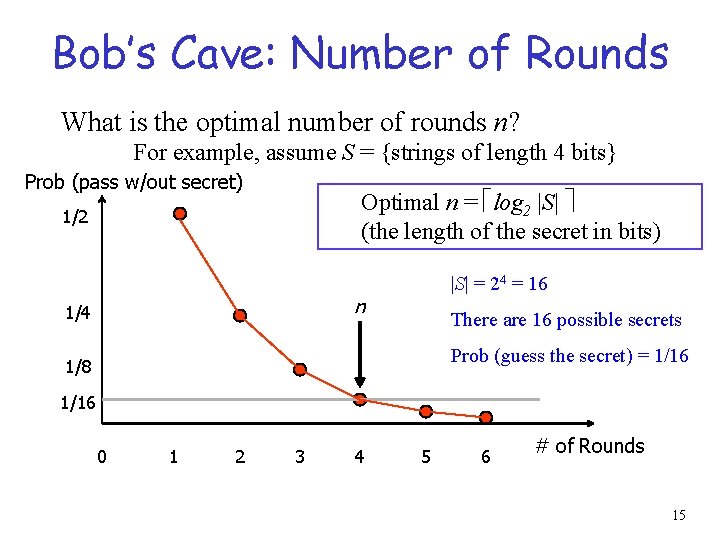
Bob’s Cave: Number of Rounds What is the optimal number of rounds n? For example, assume S = {strings of length 4 bits} Prob (pass w/out secret) Optimal n = log 2 |S| (the length of the secret in bits) 1/2 |S| = 24 = 16 n 1/4 There are 16 possible secrets Prob (guess the secret) = 1/16 1/8 1/16 0 1 2 3 4 5 6 # of Rounds 15
Applications of ZKPs Identification schemes q Multi-media security and digital watermarks q Network privacy and anonymous communication q Public-key cryptographic systems q Digital cash and off-line digital coin systems q Electronic election and e-voting q Others … q 16
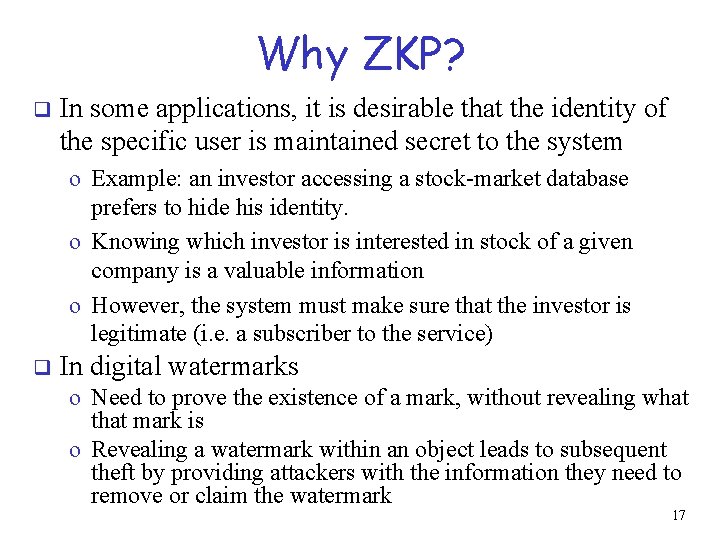
Why ZKP? q In some applications, it is desirable that the identity of the specific user is maintained secret to the system o Example: an investor accessing a stock-market database prefers to hide his identity. o Knowing which investor is interested in stock of a given company is a valuable information o However, the system must make sure that the investor is legitimate (i. e. a subscriber to the service) q In digital watermarks o Need to prove the existence of a mark, without revealing what that mark is o Revealing a watermark within an object leads to subsequent theft by providing attackers with the information they need to remove or claim the watermark 17
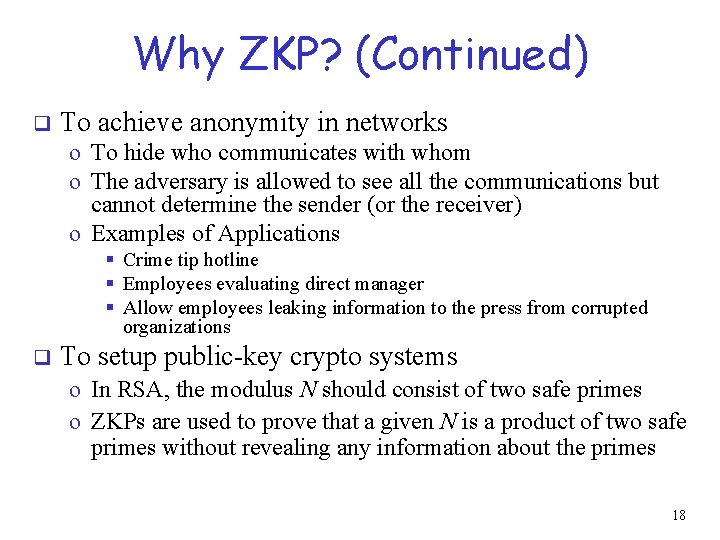
Why ZKP? (Continued) q To achieve anonymity in networks o To hide who communicates with whom o The adversary is allowed to see all the communications but cannot determine the sender (or the receiver) o Examples of Applications § Crime tip hotline § Employees evaluating direct manager § Allow employees leaking information to the press from corrupted organizations q To setup public-key crypto systems o In RSA, the modulus N should consist of two safe primes o ZKPs are used to prove that a given N is a product of two safe primes without revealing any information about the primes 18
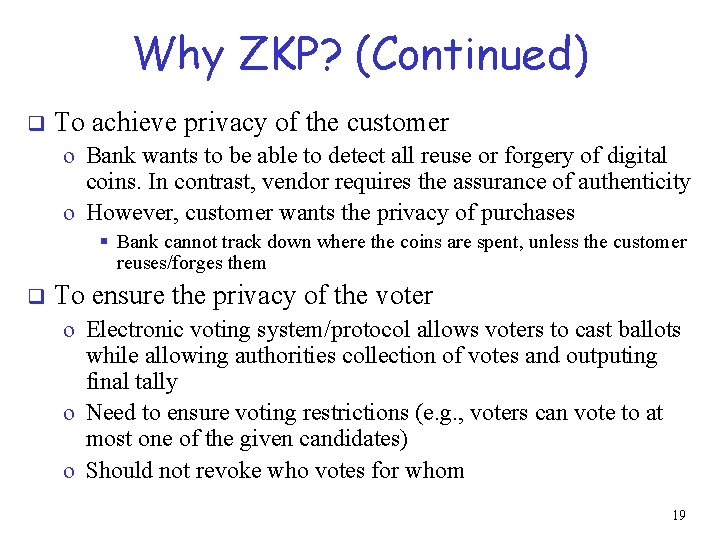
Why ZKP? (Continued) q To achieve privacy of the customer o Bank wants to be able to detect all reuse or forgery of digital coins. In contrast, vendor requires the assurance of authenticity o However, customer wants the privacy of purchases § Bank cannot track down where the coins are spent, unless the customer reuses/forges them q To ensure the privacy of the voter o Electronic voting system/protocol allows voters to cast ballots while allowing authorities collection of votes and outputing final tally o Need to ensure voting restrictions (e. g. , voters can vote to at most one of the given candidates) o Should not revoke who votes for whom 19
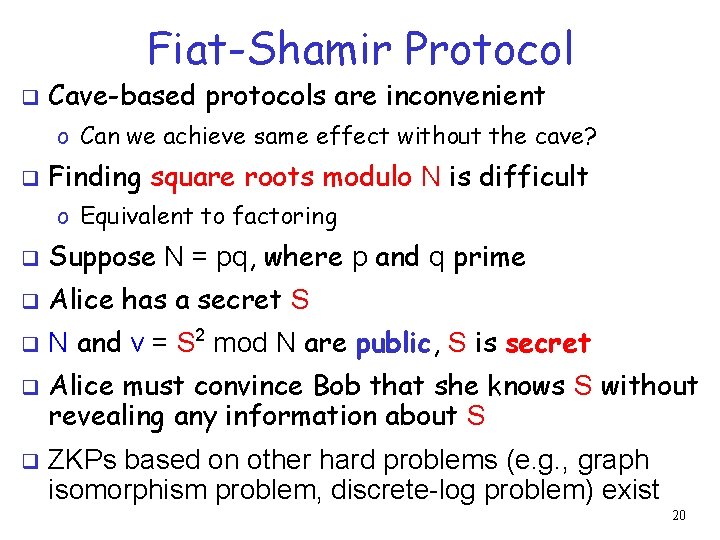
Fiat-Shamir Protocol q Cave-based protocols are inconvenient o Can we achieve same effect without the cave? q Finding square roots modulo N is difficult o Equivalent to factoring q Suppose N = pq, where p and q prime q Alice has a secret S q N and v = S 2 mod N are public, S is secret q q Alice must convince Bob that she knows S without revealing any information about S ZKPs based on other hard problems (e. g. , graph isomorphism problem, discrete-log problem) exist 20
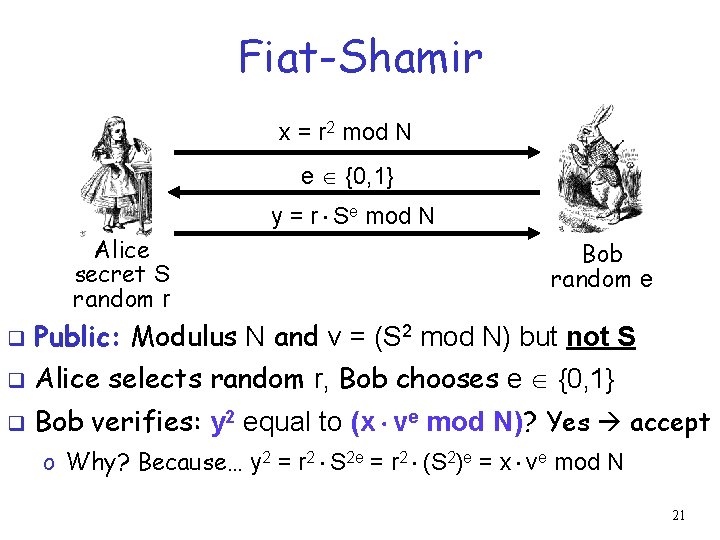
Fiat-Shamir x = r 2 mod N e {0, 1} y = r Se mod N Alice secret S random r Bob random e q Public: Modulus N and v = (S 2 mod N) but not S q Alice selects random r, Bob chooses e {0, 1} q Bob verifies: y 2 equal to (x ve mod N)? Yes accept o Why? Because… y 2 = r 2 S 2 e = r 2 (S 2)e = x ve mod N 21
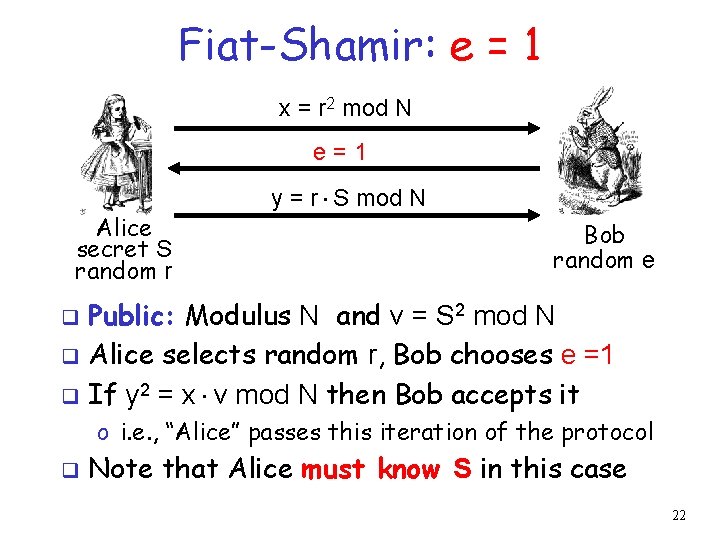
Fiat-Shamir: e = 1 x = r 2 mod N e=1 Alice secret S random r y = r S mod N Bob random e Public: Modulus N and v = S 2 mod N q Alice selects random r, Bob chooses e =1 q If y 2 = x v mod N then Bob accepts it q o i. e. , “Alice” passes this iteration of the protocol q Note that Alice must know S in this case 22
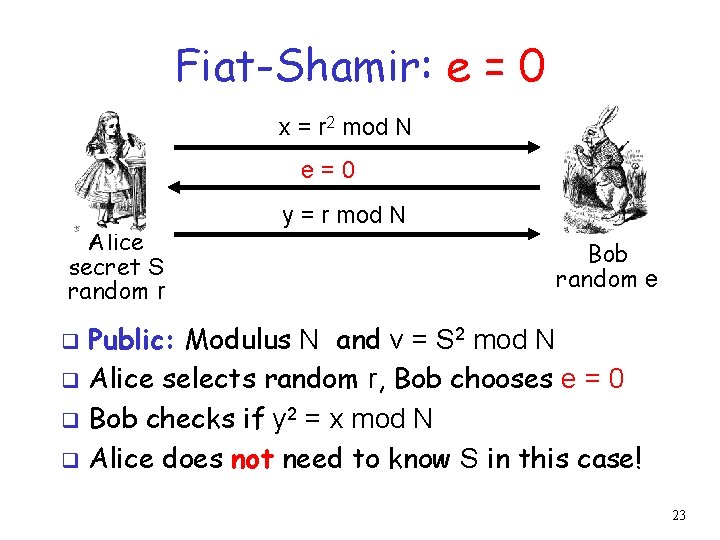
Fiat-Shamir: e = 0 x = r 2 mod N e=0 Alice secret S random r y = r mod N Bob random e Public: Modulus N and v = S 2 mod N q Alice selects random r, Bob chooses e = 0 q Bob checks if y 2 = x mod N q Alice does not need to know S in this case! q 23
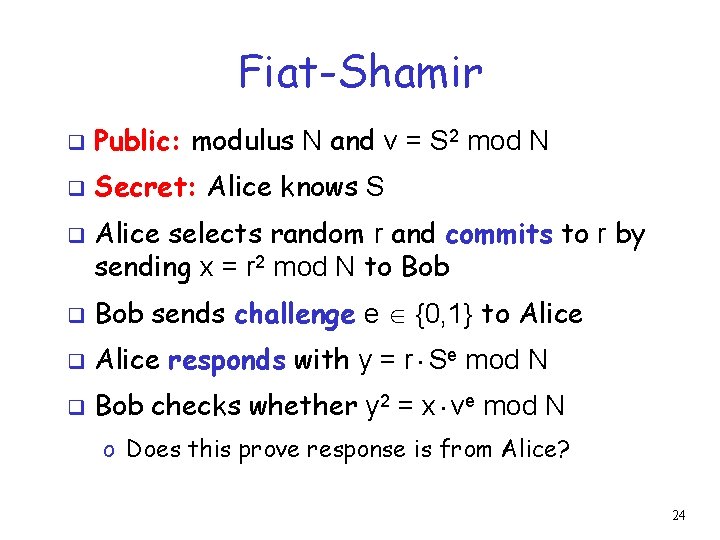
Fiat-Shamir q Public: modulus N and v = S 2 mod N q Secret: Alice knows S q Alice selects random r and commits to r by sending x = r 2 mod N to Bob q Bob sends challenge e {0, 1} to Alice q Alice responds with y = r Se mod N q Bob checks whether y 2 = x ve mod N o Does this prove response is from Alice? 24
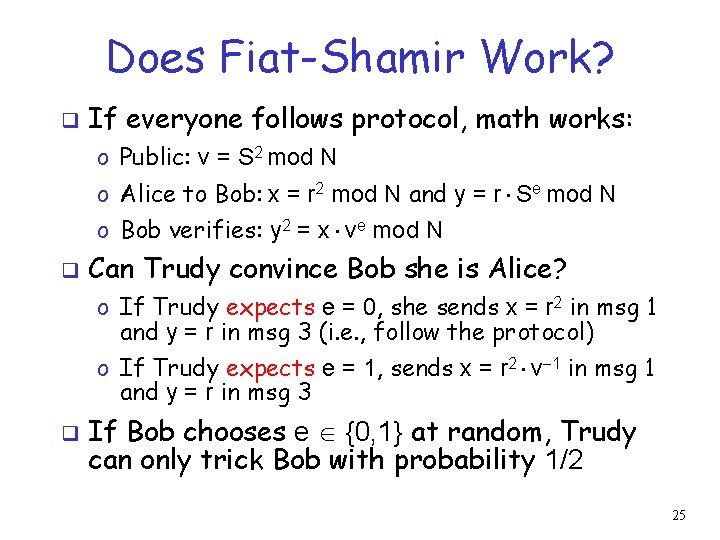
Does Fiat-Shamir Work? q If everyone follows protocol, math works: o Public: v = S 2 mod N o Alice to Bob: x = r 2 mod N and y = r Se mod N o Bob verifies: y 2 = x ve mod N q Can Trudy convince Bob she is Alice? o If Trudy expects e = 0, she sends x = r 2 in msg 1 and y = r in msg 3 (i. e. , follow the protocol) o If Trudy expects e = 1, sends x = r 2 v 1 in msg 1 and y = r in msg 3 q If Bob chooses e {0, 1} at random, Trudy can only trick Bob with probability 1/2 25
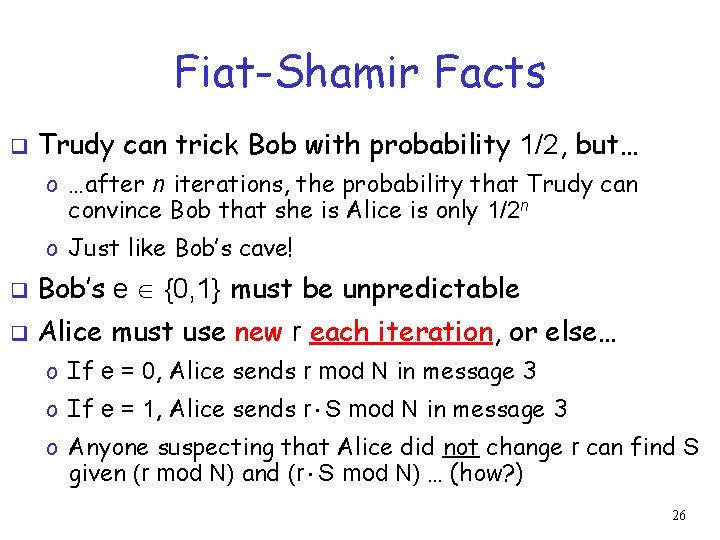
Fiat-Shamir Facts q Trudy can trick Bob with probability 1/2, but… o …after n iterations, the probability that Trudy can convince Bob that she is Alice is only 1/2 n o Just like Bob’s cave! q Bob’s e {0, 1} must be unpredictable q Alice must use new r each iteration, or else… o If e = 0, Alice sends r mod N in message 3 o If e = 1, Alice sends r S mod N in message 3 o Anyone suspecting that Alice did not change r can find S given (r mod N) and (r S mod N) … (how? ) 26
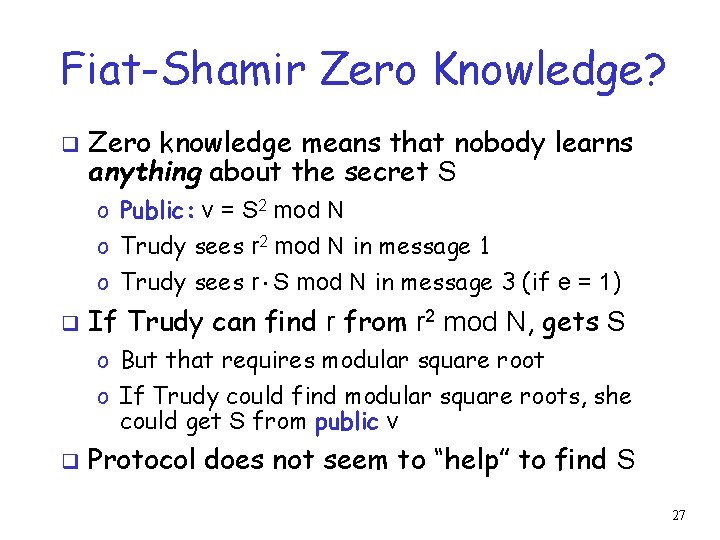
Fiat-Shamir Zero Knowledge? q Zero knowledge means that nobody learns anything about the secret S o Public: v = S 2 mod N o Trudy sees r 2 mod N in message 1 o Trudy sees r S mod N in message 3 (if e = 1) q If Trudy can find r from r 2 mod N, gets S o But that requires modular square root o If Trudy could find modular square roots, she could get S from public v q Protocol does not seem to “help” to find S 27
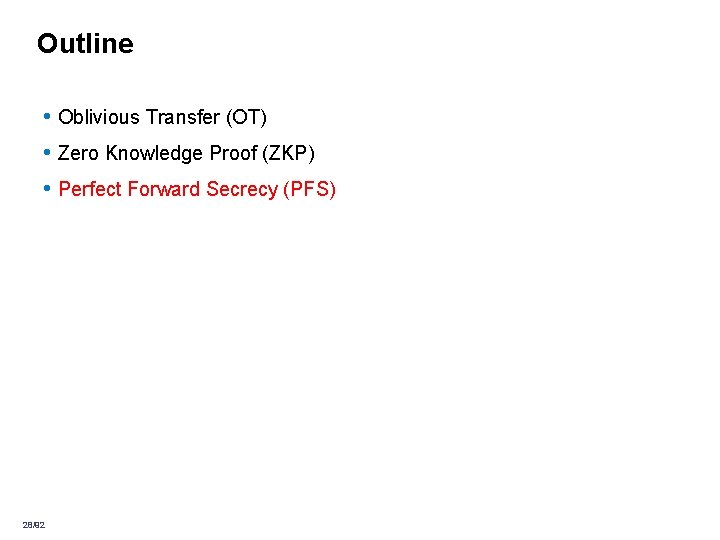
Outline • Oblivious Transfer (OT) • Zero Knowledge Proof (ZKP) • Perfect Forward Secrecy (PFS) 28/92
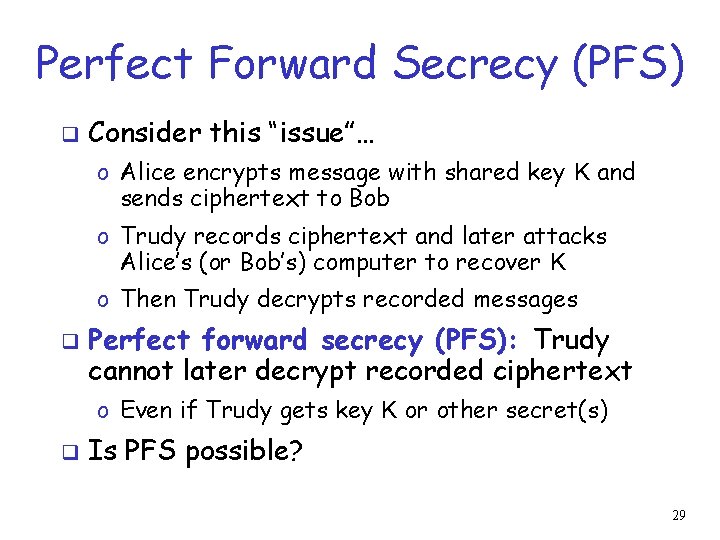
Perfect Forward Secrecy (PFS) q Consider this “issue”… o Alice encrypts message with shared key K and sends ciphertext to Bob o Trudy records ciphertext and later attacks Alice’s (or Bob’s) computer to recover K o Then Trudy decrypts recorded messages q Perfect forward secrecy (PFS): Trudy cannot later decrypt recorded ciphertext o Even if Trudy gets key K or other secret(s) q Is PFS possible? 29
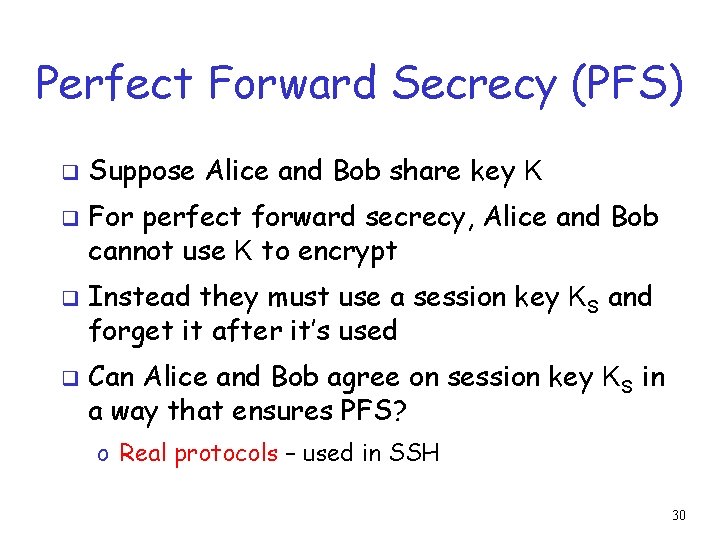
Perfect Forward Secrecy (PFS) q q Suppose Alice and Bob share key K For perfect forward secrecy, Alice and Bob cannot use K to encrypt Instead they must use a session key KS and forget it after it’s used Can Alice and Bob agree on session key KS in a way that ensures PFS? o Real protocols – used in SSH 30
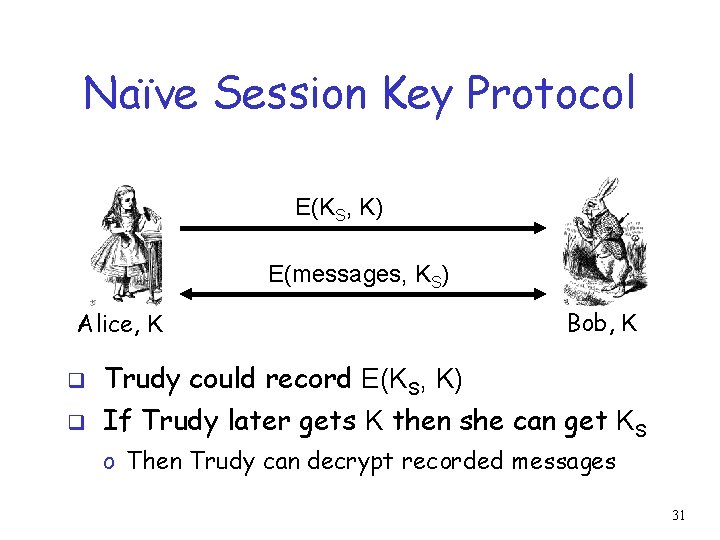
Naïve Session Key Protocol E(KS, K) E(messages, KS) Alice, K Bob, K q Trudy could record E(KS, K) q If Trudy later gets K then she can get KS o Then Trudy can decrypt recorded messages 31
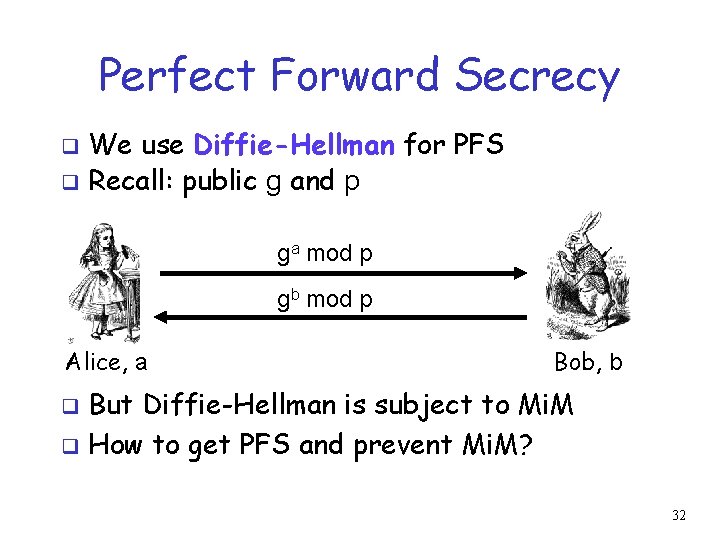
Perfect Forward Secrecy We use Diffie-Hellman for PFS q Recall: public g and p q ga mod p gb mod p Alice, a Bob, b But Diffie-Hellman is subject to Mi. M q How to get PFS and prevent Mi. M? q 32
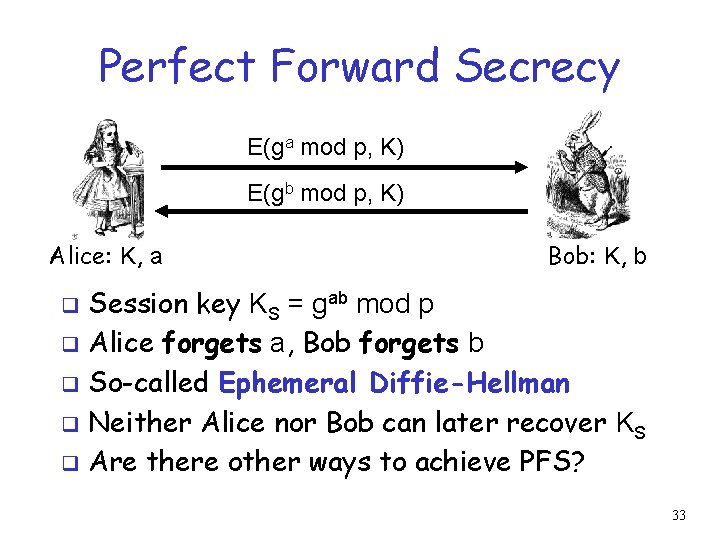
Perfect Forward Secrecy E(ga mod p, K) E(gb mod p, K) Alice: K, a Bob: K, b Session key KS = gab mod p q Alice forgets a, Bob forgets b q So-called Ephemeral Diffie-Hellman q Neither Alice nor Bob can later recover KS q Are there other ways to achieve PFS? q 33
![Mutual Authentication, Session Key and PFS “I’m Alice”, RA RB, [{RA, gb mod p}Alice]Bob Mutual Authentication, Session Key and PFS “I’m Alice”, RA RB, [{RA, gb mod p}Alice]Bob](http://slidetodoc.com/presentation_image_h2/89ccf8a34de9ec4d8e6c02c0443bda17/image-34.jpg)
Mutual Authentication, Session Key and PFS “I’m Alice”, RA RB, [{RA, gb mod p}Alice]Bob [{RB, ga mod p}Bob]Alice, a Bob, b Session key is Ks = gab mod p q Alice forgets a and Bob forgets b q If Trudy later gets Bob’s and Alice’s secrets (i. e. , RSA private keys d. B and/or d. A), she cannot recover session key Ks q 34
- Slides: 34