Motivation and Problem Statement 1 Key Idea Initial
Motivation and Problem Statement 1
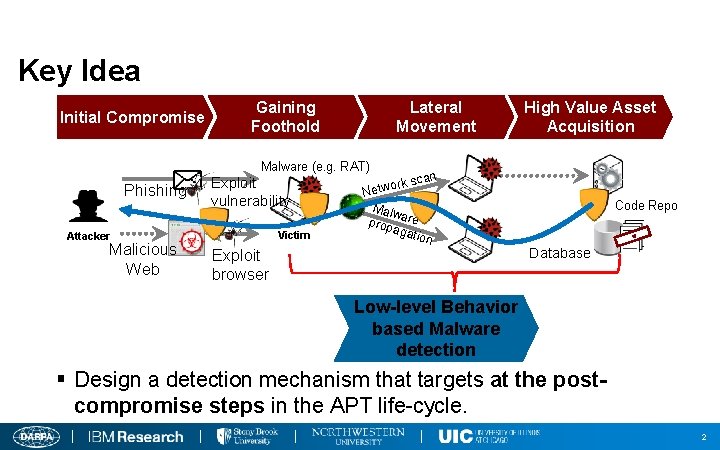
Key Idea Initial Compromise Gaining Foothold Lateral Movement High Value Asset Acquisition Malware (e. g. RAT) Phishing Exploit vulnerability Victim Attacker Malicious Web an ork sc w t e N Malw prop are agat ion Exploit browser Code Repo I F T N E L O D A C Database Low-level Behavior based Malware detection § Design a detection mechanism that targets at the postcompromise steps in the APT life-cycle. 2
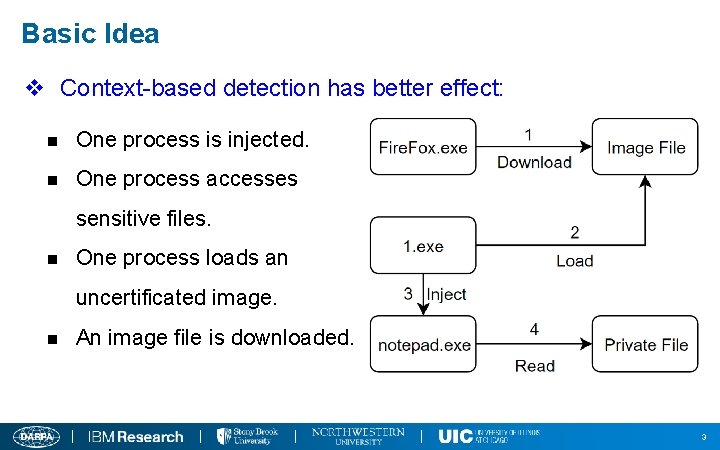
Basic Idea v Context-based detection has better effect: n One process is injected. n One process accesses sensitive files. n One process loads an uncertificated image. n An image file is downloaded. 3
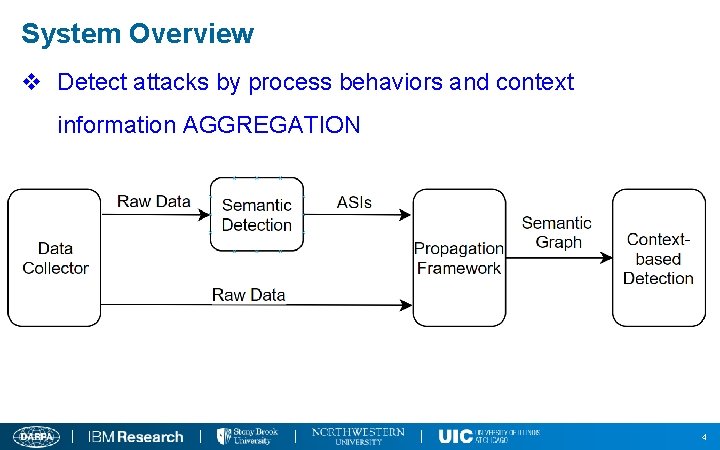
System Overview v Detect attacks by process behaviors and context information AGGREGATION 4
Basic Idea v Detect attacks by suspicious indicators and process context information: n Suspicious behaviors with high-level semantics n Context Information: n Process Features n Code Source n Data Flow 5
Main Idea v A Context-Based Semantic-Aware Attack Detection and Reconstruction System v Atomic suspicious indicators (ASI) v Aggregation Framework v Detection Policies 6
System Design -- ASI v ASIs are used to represent the current status (its own and context information) of one process and one file, including: v Process ASIs: v Behaviors: Screengrab, Keylogger and Execute sensitive commands, etc. ; v Features: Have Visible Windows, Have Human Interactions, its ancestor process has network connections etc. v Code source: Injected and Load a downloaded image, etc. ; v Data flow: Access Data from Network, etc. 7
ASI Design and Selection 8
System Design v File ASIs: v Data flow: Access Data from Network and Contains Sensitive Information, etc. v Features: Uncertificated and Contains Macros, etc. 9
System Design – Aggregation Framework v Problem statement v Solution comparison (forward, backward, bidirectional) v Rules are used to propagate labels from one subject/object to another, in other words, the context information. v For example, 10
System Design v Policies (clearly define it) v Four Main Components: v 1. Execute codes/scripts from attacker(or insider attack) v 2. Suspicious Behaviors: The target of the attack; v 3. Network Connections: To communicate with attacker and steal data v 4. Other features: For example, unrealized by users. v Fast Policy Matching 11
System Details and Implementation v Problem 1: semantic behavior detection 12
System Details and Implementation v Problem 2 : Customized labels/rules/polices. n The framework is designed to be customizable to cover more attacks and adjust to different situation n n Labels(Identifier, Confidence Score, Type, Description): n PT 2, 1, PHF, Access sensitive information n FT 5, 1, Data, The file contains sensitive information Rules(Subject, Event, Object/Subject, Direction): n n PT 2, 2, FT 5, R Policies: 13
System Details and Implementation v Problem 3 : Attack Reconstruction n We’ve designed a label-based attack graph reconstruction approach. n If process A is found to be suspicious, our approach would show the source path of the labels in A. n Advantages: 1. Don’t use additional memory; 2. Fast; 3. Accurate in most scenarios. 14
System Details and Implementation v Problem 4 : Data Storage in Memory n Instead of a graph, we prefer a process tree with a file list. n Process Tree n Each node is a process with its creation information and labels n n File List n n Nodes are connected by creation relationships. Each element is a file with its attributes and labels We don’t store events in memory, but status. 15
Challenges & Solutions v Challenge 5: Cross-machine Detection v TODO 16
- Slides: 16