MOBILE COMPUTING Course Code CNET 426 Chapter 3
MOBILE COMPUTING Course Code: CNET 426 Chapter 3 PHYSICAL MOBILITY
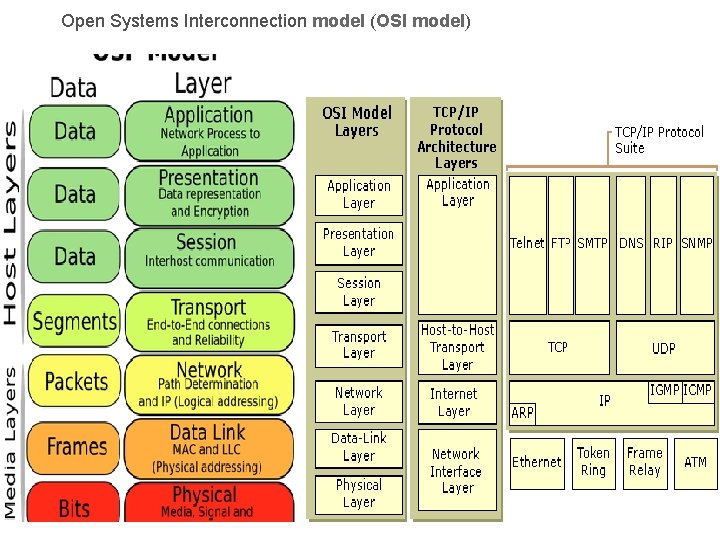
Open Systems Interconnection model (OSI model)
THE REQUIREMENTS FOR PHYSICAL MOBILITY There are three important issues related to physical mobility. 1. Wireless Communication • Mobile computers require both wireless and wired network access. • Wireless communication is more difficult to achieve than wired communication, because the environment interacts signals blocking its path and introducing noise an echoes. • Communication delays are more frequent due to retransmissions, timeouts and error control processing. • The wireless connection can also be lost or degraded by mobility if the enters high interference areas. Disconnection is a major problem for mobile computing. • Wireless networks deliver much lower bandwidth than wired ones • Network quality also changes when moving from one wireless network to another, giving rise to heterogeneous networks. 1. Meeting room has better wireless facilities than corridor.
Cont. . • multiple transceivers may be on different frequencies, and protocols on networks may be different. there may be a need to switch interfaces while moving outside from inside since infrared does not work outside. 2. MOBILITY The ability to change locations while connected to a network increases the volatility of informa tion. Data considered static for a stationary computer becomes dynamic for mobile computing; Ø Address migration: As people move, their mobile computers will have to use different network service access points(NSAPs). • Dynamically changing addresses are needed. But in the Internet protocol (IP) protocol, host names are bound with network addresses, and moving to a new location means getting a new name. To communicate with a mobile computer, messages must be sent to its most recent address.
. Ø Location dependent information: local name server, the available printer the time zone and real world information, like “where is the nearest library” are dynamically changing data that must be made available when the computer moves. • The challenge is thus to provide all these without violating privacy. Ø Migrating locality: Mobile computing gives rise to a new kind of locality that migrates as users move. For example, a server found with a great effort to the nearest one at a particular location may not be so after further movement. • Also, physical distance between two points does not necessarily reflect network distance. • Hence, communication locality becomes more important than load balancing. 3. Portability: Desktop computers are not designed to be carried, so
. Design pressures caused by portability constraints are as follows: Low power: Batteries are the largest single source of weight. But reducing battery size compromises its use, because it leads to frequent recharging, the need for spare batteries, or results in less use of the mobile computer. It has been found that P ∞ CV 2 F, Where, P is the power consumption of the device C is the interline capacitance of the VLSI processor chip in the device V is the voltage swing F is clock frequency of the processor chip. Risks to data: Portability increases the risk of physical damage, unauthorized access, loss and theft. So it is necessary to minimize the essential data on the device Small user interfaces. Current windowing techniques are not feasible when user area is One cannot have too many windows open, or too many icons buttons. Small storage capacity: Disks cannot be used in PDAs as they consume more power and are susceptible to volatility. Solutions include compressing
OVERVIEW OF IPv 4 AND IPv 6 IPv 4: IP version 4, or IP as it is better known, is the glue that holds the Internet together. Its basic func tion is to deliver from source to destination, independent of the physical location of the two. • IPv 4 addresses are 32 bit (4 bytes)long integers and are represented in a dotted decimal format (e. g. 172. 16. 19. 11) for ease of use. In CIDR (classless inter domain routing) addressing, every IPv 4 address contains the network number and the host number. • If we consider a machine with address 172. 16. 19. 11 then 176. 16 is network number and 19. 11 is the host number. • Every IP packet consists of an IP header and an IP payload. • The header contains the IP addresses of the sending node and the receiving node along with some other information. • IP executes two major steps: packet routing and packet forward ing. Packet routing involves use of protocols like border gateway protocol (BGP}, routing information protocol (RIP) and open shortest path first (OSPF) to decide the route that each packet has to travel.
. • The route is decided using a routing table having the 2 tuple pairs (destination address, next hop) • Packet forwarding involves use of protocols like address resolution protocol (ARP), proxy ARP. • To deliver the packet to the end node once it has arrived at the destination. IPv 6: IPv 6 version, mainly to take care of the rapidly increasing number of machines connecting to the Internet. § It provides for 16 byte (128 bits) addresses, in place of the 4 byte addresses of 1 Pv 4. • It is a simpler protocol that allows routers to process packets faster by reducing the size of routing tables. • It provides better security through two 'extension headers'. ü The ‘authentication header pro videsa mechanism by which the receiver of a packet can be sure who sent the packet. ü The 'encrypted security payload' header makes it possible to encrypt the packet so that only the intended recipient can read it. • Most important, IPv 6 supports mobility.
MOBILE IP • Mobile IP protocols provide mobility support for IP network. • It allows transparent routing of IP datagrams to mobile nodes in the Internet. • In mobileeach mobile always IPnode identified is, home address, itsby regardless of 'its current point of attachment to the Internet. • Every mobile node is associated with a care of address, which provides information about its current point of attachment to the Internet. GOALS The major goals envisaged for mobile IP were as follows: • To continue to work with the existing TCP/IP protocol suite. • To provide Internet wide mobility, allowing a host the same IP address, called 'home address'. • To optimize local area mobility without sacrificing performance or functionality of the general case. • To leave the transport layer and higher protocols untouched.
. • To ensure that no application needs. . to change in order to run on or to be used from mobile hosts (MHs). • To ensure that the infrastructure, that is, non MHs, routers, routing protocols, etc. are not changed either. • To see that mobility is handled at the network layer. • To ensure minimum power consumption, since mobile nodes are likely to be battery powered. Mobility support in IPv 4 Mobile IP introduces the following new functional entities which are required for both IPv 4 and IPv 6. ü Mobile node: This is a host or router that changes its point of attachment from one network or sub network to another. A mobile node (or host) may change its location without changing its address.
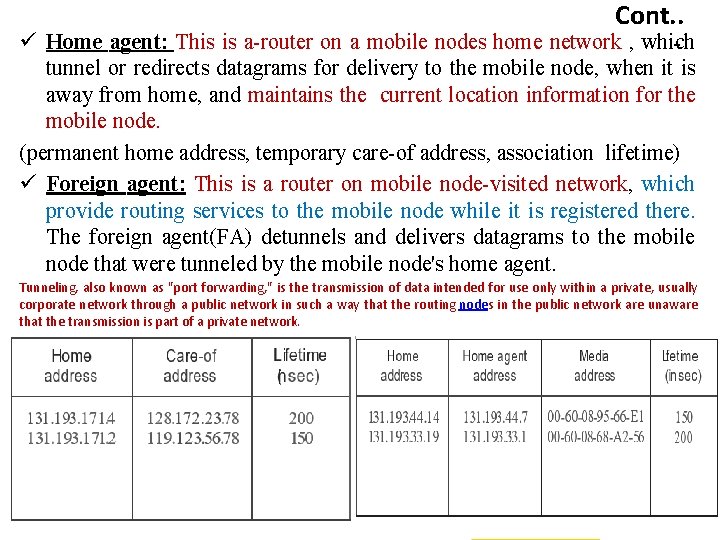
Cont. . ü Home agent: This is a router on a mobile nodes home network , which tunnel or redirects datagrams for delivery to the mobile node, when it is away from home, and maintains the current location information for the mobile node. (permanent home address, temporary care of address, association lifetime) ü Foreign agent: This is a router on mobile node visited network, which provide routing services to the mobile node while it is registered there. The foreign agent(FA) detunnels and delivers datagrams to the mobile node that were tunneled by the mobile node's home agent. Tunneling, also known as "port forwarding, " is the transmission of data intended for use only within a private, usually corporate network through a public network in such a way that the routing nodes in the public network are unaware that the transmission is part of a private network.
Mobility support in IPv 6 mobility support is like that of mobile IPv 4, using the concepts of home networks, home gents and encapsulation. • Route optimization is built as a fundamental part of mobile IPv 6 unlike in mobile IPv 4, Where it is an optional extension that may not be supported by all nodes. • Foreign agents are not needed in mobile IPv 6. This is because IPv 6 uses the concept of neighbor discovery by the mobile node. • Address auto configuration is another feature used by the mobile nodes to function in any location without the services of any special router in that location. • In mobile IPv 4, when a mobile node communicates with a CN, it puts its home address as the source address of the packet. 'Ingress filtering' routers present in the network will filter out such a packet, since it finds that the source address of the packet is different from the network from which the packet actually originated.
. • This problem is tackled in mobile IPv 6 by putting the care of address as the source address, not the home address. There is also a home address destination option, which allows the use of the care of address to be transparent over the IP layer • Security is automatically provided in 1 Pv 6 nodes since they are expected to implement cryptographic and strong authentication and encryption features.
CELLULAR IP The cellular IP access network ü It consists of access routers or base stations (BS) interconnection by wired linked and connected to internet by a gateway router (R). ü Mobile between gateways (i. e. cellular IP access networks) is managed by mobile, while mobility within access networks is handled by cellular IP. ü All packets coming from mobile terminals are routed from BS they are connected to, towards R, no matter what the destination of the packet is. ü The Gateway R periodically broad casts a beacon packet that is flooded through the cellular IP network to make sure that all nodes have a correct routing entry towards it. ü Nodes in the net work record the neighbour they last received this beacon from and use it to route packets towards the Gateway R.
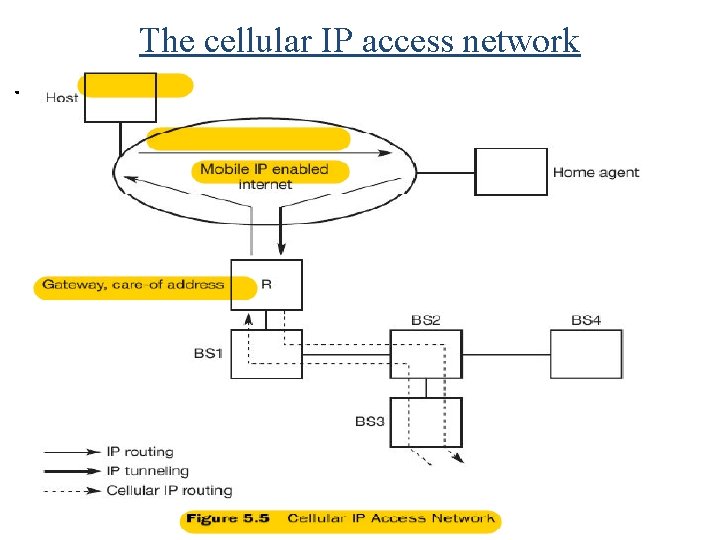
The cellular IP access network.
Routing and paging cache • To send packets towards a mobile device, the nodes use two different caches, a routing cache and a paging cache. • Routing caches are used to route packets towards a mobile terminal. When a data packet from a mobile node enters a node, it puts a mapping into its routing cache for the mobile node's IP address and the neighbour node from which the packet came. • To keep be caches valid; the mobile node must keep sending route update packets even if it has no data to send. • Paging caches are similar to routing caches but are used to find an idle mobile if a packet has to be sent to it but there is no entry for it in the routing cache. • Idle mobiles must keep sending paging updates at regular time intervals to the gateway to refresh the paging cache entries. • If there is no entry or a mobile in either for routing or the paging caches, any node in the network, the packet is for wardedto all downlinks by that node
TCP for mobility Transport protocols like TCP have been typically designed for fixed end systems and fixed, wired networks. Indirect TCP ü TCP performs poorly with wireless link , and that it cannot be changed for the fixed network. These facts led to the development of indirect TCP ( I TCP). ü I TCP segments a TCP connection into a fixed part and a wireless part. There are no changes to the TCP protocol for hosts connected to the wire internet; millions of computer will continue to use this protocol. ü Standard TCP is used between the correspondent node CN and the access point AP. Its connection now ends at the AP, which acts as a proxy. Between the AP and the MH, a special TCP, adapted and optimized to wireless links, is used.
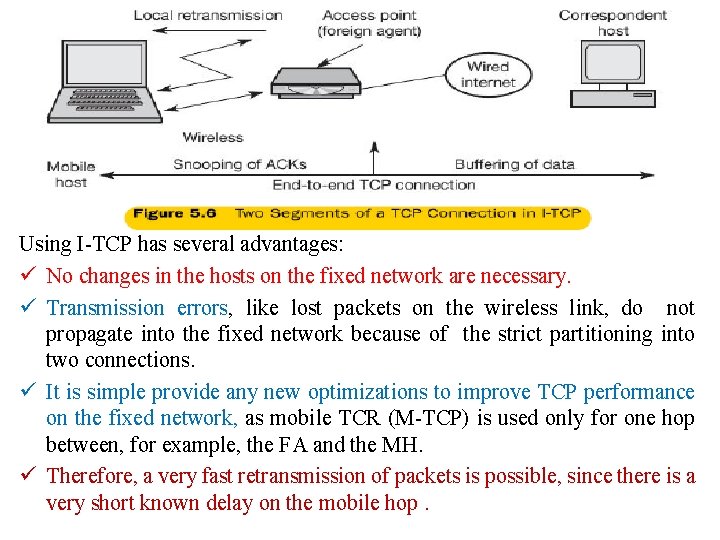
Using I TCP has several advantages: ü No changes in the hosts on the fixed network are necessary. ü Transmission errors, like lost packets on the wireless link, do not propagate into the fixed network because of the strict partitioning into two connections. ü It is simple provide any new optimizations to improve TCP performance on the fixed network, as mobile TCR (M TCP) is used only for one hop between, for example, the FA and the MH. ü Therefore, a very fast retransmission of packets is possible, since there is a very short known delay on the mobile hop.
Snooping TCP • One of the disadvantages of I TCP is that a single TCP connection is split into two, thus losing the original end to end semantic. • Snooping TCP is a transparent extension of TCP, leaving its end to end connection intact. • The main concept in snooping TCP is that packets are buffered close to the MH for fast local retransmission in case of packet loss. This buffering can be done at the FA. • All packets destined for the MH are buffered at the FA, which also snoops' the packet flow in both direction. • Lost packet on the wireless link (both directions) will be retransmitted (locally) immediately by the MH or by the FA, respectively, from the buffer, performing a much faster retransmission compared to the CN.
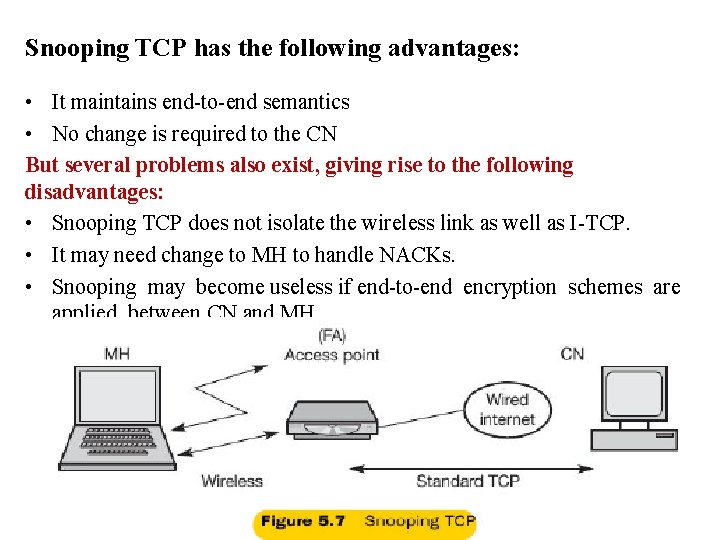
Snooping TCP has the following advantages: • It maintains end to end semantics • No change is required to the CN But several problems also exist, giving rise to the following disadvantages: • Snooping TCP does not isolate the wireless link as well as I TCP. • It may need change to MH to handle NACKs. • Snooping may become useless if end to end encryption schemes are applied between CN and MH.

Thanks Any Query ?
- Slides: 21