Location Privacy Location privacy in mobile systems A
Location Privacy Location privacy in mobile systems: A personalized Anonymization Model Burga Gedik, Ling Liu
Location privacy threats An adversary learns the locations that a subjected visited as well as the times of visit. Can receive clues about private information such as political affiliations, medical problems. If a subject is identified at any point, her complete movement can be exposed.
K-anonymity Originally introduced in the context of relational data privacy research. In context of LBS, refers to k-anonymous usage of location information A subject is considered k-anonymous with respect to location information if this location information is indistinguishable from the location information of at least k-1 other subjects. The adversary will have uncertainty in matching the mobile node to a location-identity association The uncertainty increases with increasing value of k.
Overview To ensure that a subject is k-anonymous one can perturb the location information by replacing relatively large spatial region or by delaying the message long enough. May result in poor quality of service. Allow personalization: Enable each node to specify I. minimum level of anonymity it desires II. maximum temporal and spatial resolutions Efficient message perturbation engine Cliquecloak: spatio-temporal cloaking
Personalized location k-anonymity Assumptions Ø LBS system consists of mobile nodes, wireless networks, anonymity servers and LBS servers. Ø Source of location information : GPS receiver in vehicle (includes time information as well) Ø Nodes communicate with third party LBS servers through anonymity servers. Ø Each node specifies anonymity level (k value), spatial tolerance and temporal tolerance.
Spatial cloaking: Degree of location anonymity maintained by decreasing the location accuracy through enlarging the exposed spatial area such that there are k-1 mobile nodes present in the area. Temporal cloaking: Location anonymity achieved by delaying the message until k nodes have visited the area located by message sender.
Set up S: a Set of messages received from the mobile nodes. message in set S is denoted by ms = <uid , rno , {t, x, y}, k, {dt , dx , dy}> (uid , rno) sender's identifier and message reference number pair L(ms) → {t, x, y} (spatio-temporal location point) K → anonymity level. (k=1 anonymity not required) {dt , dx , dy} → tolerances
![Set up Let Φ(v, d)= [v-d, v+d] � Spatio-temporal Constraint box of message ms Set up Let Φ(v, d)= [v-d, v+d] � Spatio-temporal Constraint box of message ms](http://slidetodoc.com/presentation_image_h/279717eedff6df14e3c1bf5a0dd30b8e/image-8.jpg)
Set up Let Φ(v, d)= [v-d, v+d] � Spatio-temporal Constraint box of message ms denoted by Bcn(ms) � Φ(ms. x , ms. dx), Φ(ms. y , ms. dy) , Φ(ms. t , ms. dt) � Denote the set of perturbed (anonymized) messages as T � message in T denoted by � mt <uid , rno , {X: [xs , xe ], Y: [ys , ye ], T: [ts , te]}, C> � Spatio-temporal cloaking box of a perturbed message �B (m ) -> (m. X: [x , x ], m. Y: [y , y ], m. I: [t , t ]) cl t t s e �
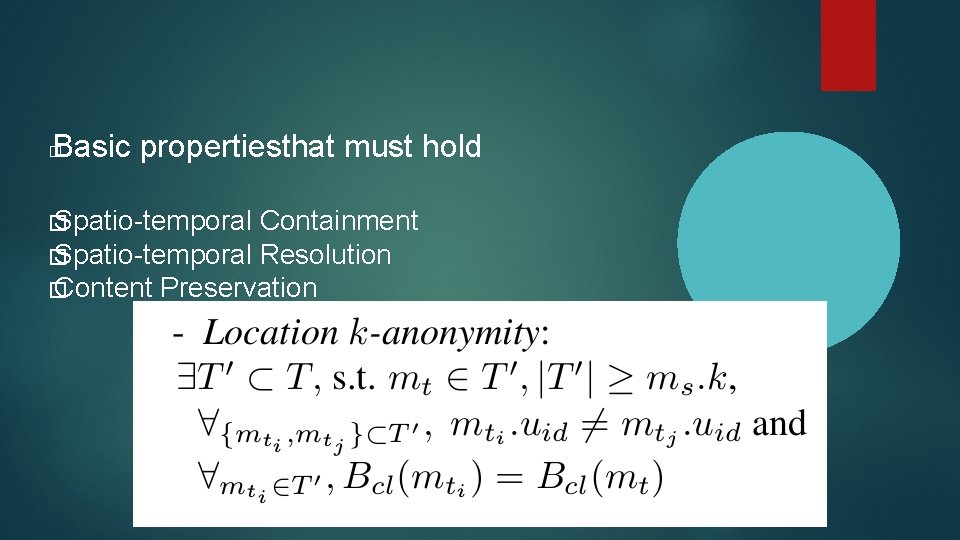
Basic propertiesthat must hold � � Spatio-temporal Containment � Spatio-temporal Resolution � Content Preservation
Message perturbation engine Zoom-in � Detection � Perturbation � Expiration �
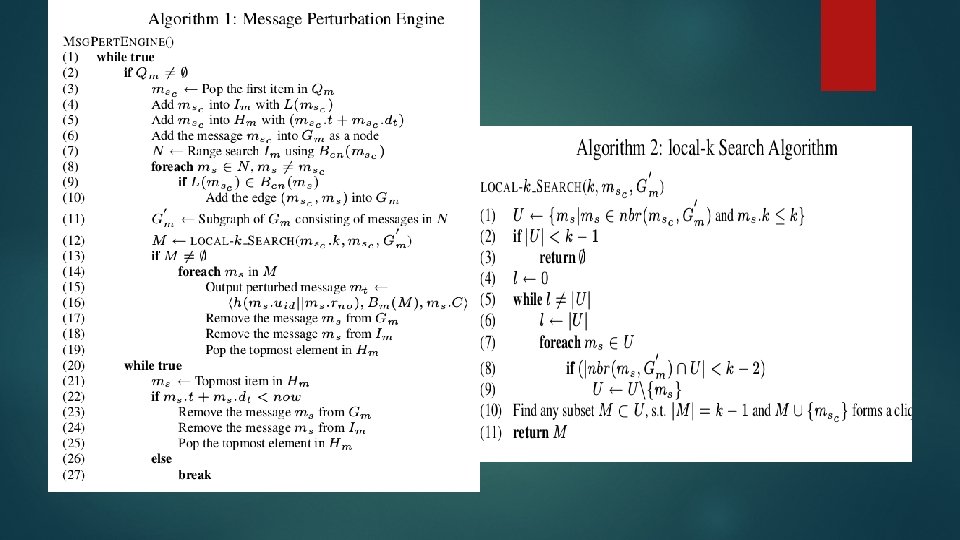
Data structures Message Queue (FIFO): collects messages sent from � the mobile node Multi-dimensional index: contains a 3 D point L(ms) as � key and ms as data. Expiration heap: A mean heap sorted based on the � deadline of the messages
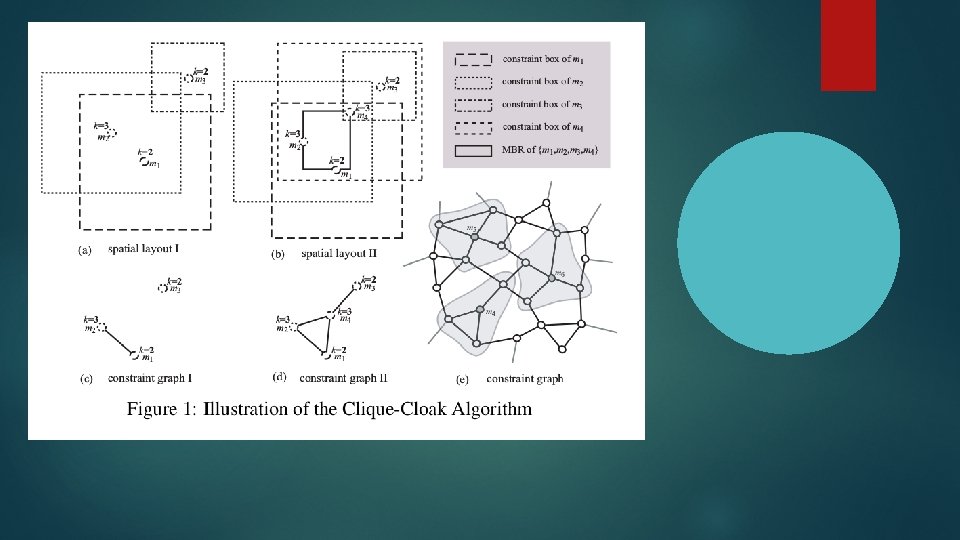
Constraint graph • An undirected graph represented by G(S, E) • S is the set of vertices, each representing a message received at the message perturbation engine • edge e = (msi , msj ) ∈ E between two vertices msi and msj , if and only if the following conditions hold: • (i) L(msi) ∈ Bcn (msj ), • (ii) L(msj) ∈ Bcn (msi ), • (iii) msi. uid = msj. uid • mt is a valid perturbed message of ms if there exists an l-clique in the constraint grapg such that l>=ms. k
Cliquecloak theorem • Let M = {m s 1 , ms 2 , . . . , msl } be a set of messages in S. For each message msi in M , we define mti = msi. uid , msi. rno , Bm(M ), msi. C. Then mti , 1 ≤ i ≤ l, is a valid perturbed format of m s i if and only if the set M of messages form an l-clique in the constraint graph G(S, E) with the additional condition that for any message msi in S, we have msi. k ≤ l (i. e. msi ’s user specified k value is not larger than the cardinality of the set M )
Optimizations • Neighbor_k instead of local_k • Deferred Cliquecloak vs Immediate Cliquecloak
Evaluation metrics • Success rate : defined over a set S' ⊂ S of messages as the percentage of messages that are successfully anonymized. • Relative anonymity level : measure of the level of anonymity provided by the cloaking algorithm, normalized by the level of anonymity required by the messages. • Relative spatial resolution : measure of the spatial resolution provided by the cloaking algorithm, normalized by the minimum acceptable spatial resolution de-fined by the spatial tolerances • Relative temporal resolution : measure of the temporal resolution provided by the cloaking algorithm, normalized by the minimum acceptable temporal resolution defined by the temporal tolerances
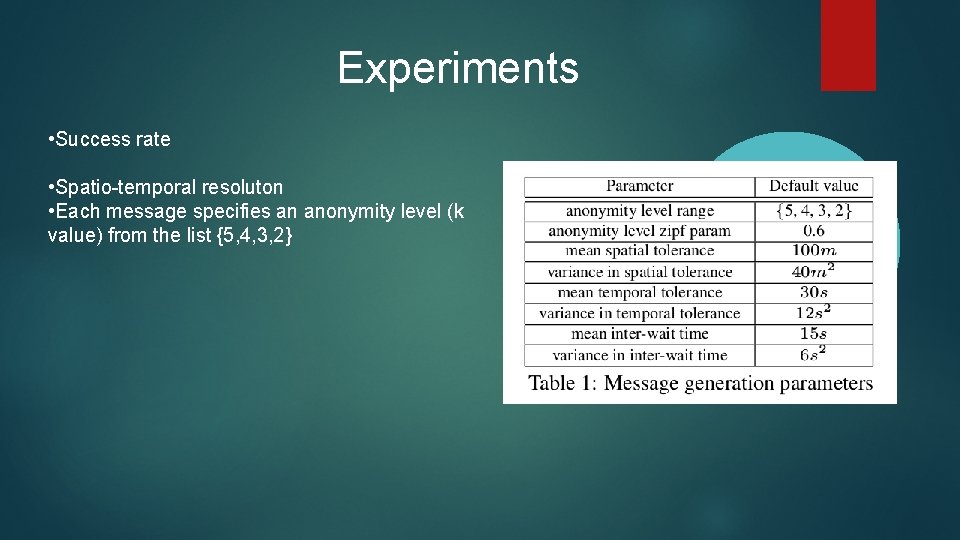
Experiments • Success rate • Spatio-temporal resoluton • Each message specifies an anonymity level (k value) from the list {5, 4, 3, 2}
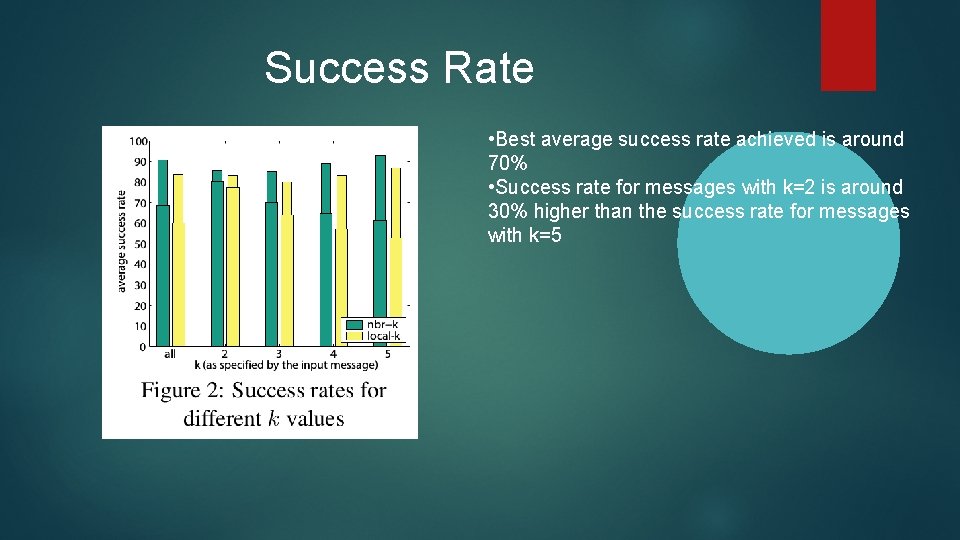
Success Rate • Best average success rate achieved is around 70% • Success rate for messages with k=2 is around 30% higher than the success rate for messages with k=5
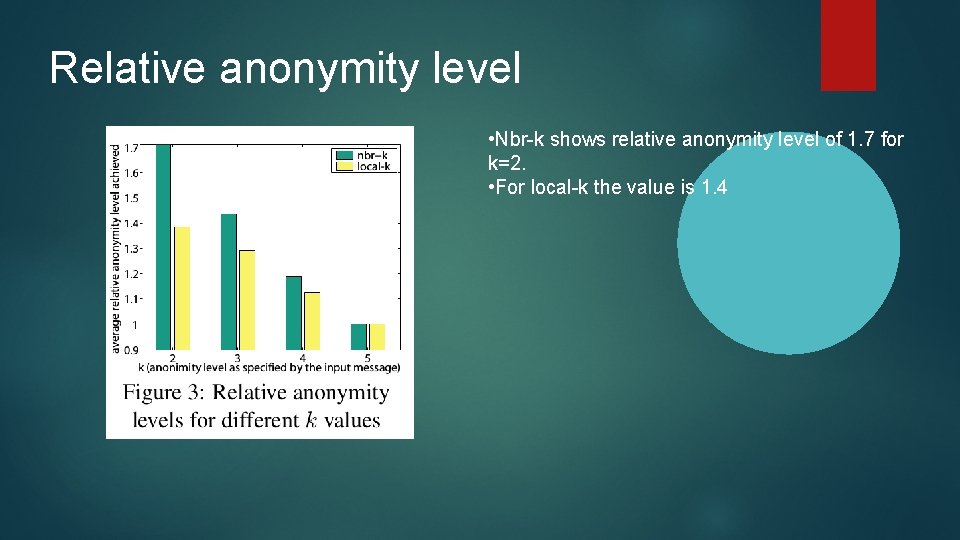
Relative anonymity level • Nbr-k shows relative anonymity level of 1. 7 for k=2. • For local-k the value is 1. 4
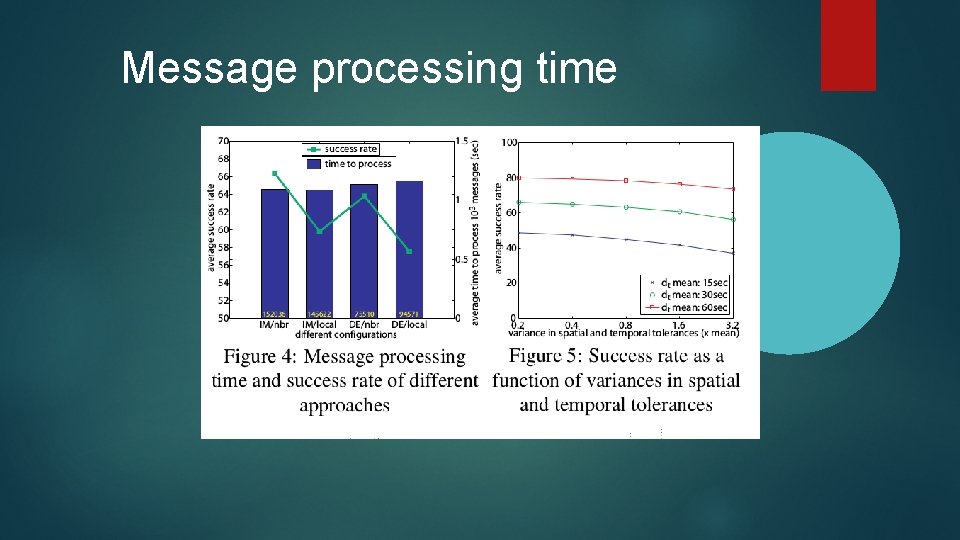
Message processing time
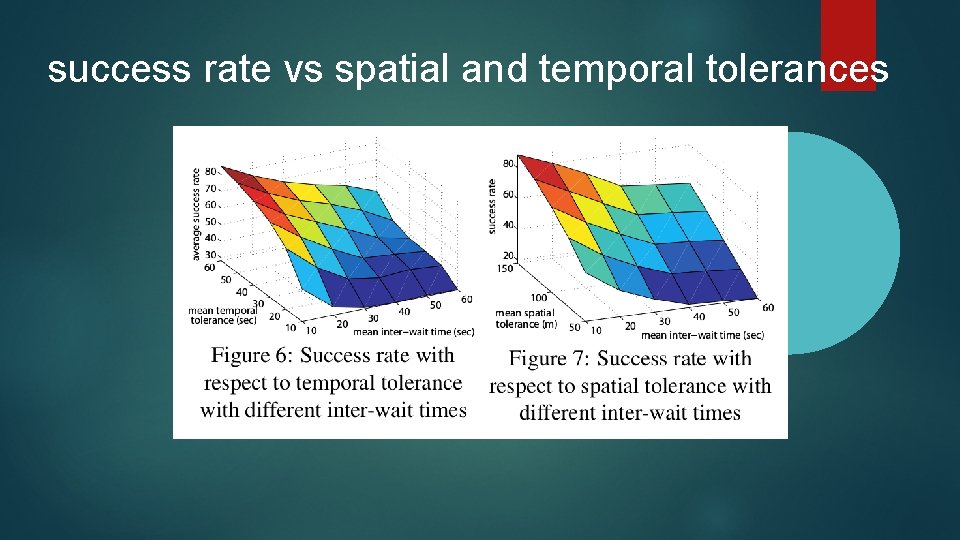
success rate vs spatial and temporal tolerances
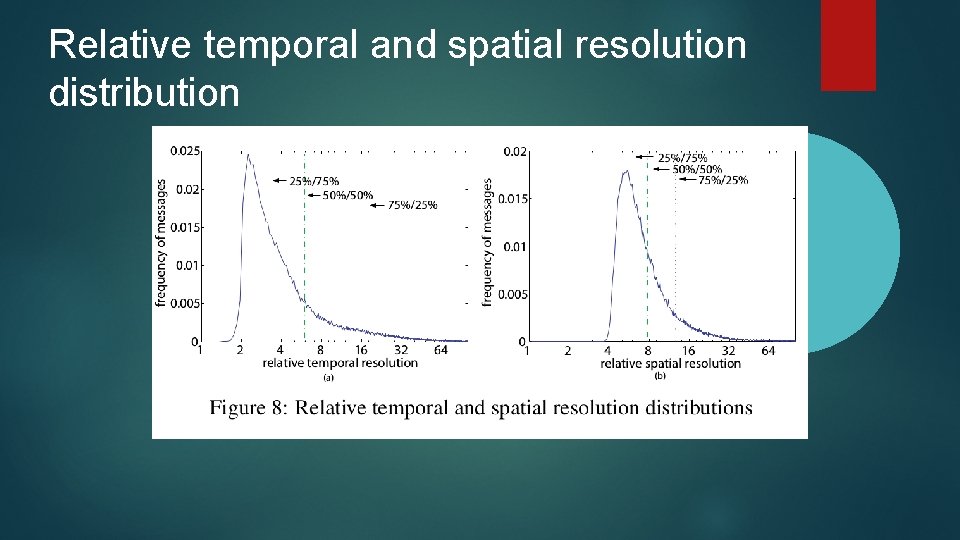
Relative temporal and spatial resolution distribution
THANK YOU
- Slides: 24