Blind Location Supporting User Location Privacy in Mobile
Blind. Location: Supporting User Location Privacy in Mobile Database Using Blind Signature Source: Journal of Computer Science and Technology, reviewing Imact Factor: 0. 632 Presenter: Yung-Chih Lu (呂勇志) Date: 2010/12/31 1
Outline Introduction Related work Proposed Scheme Security Analysis Performance Evaluation Conclusion Comment 2
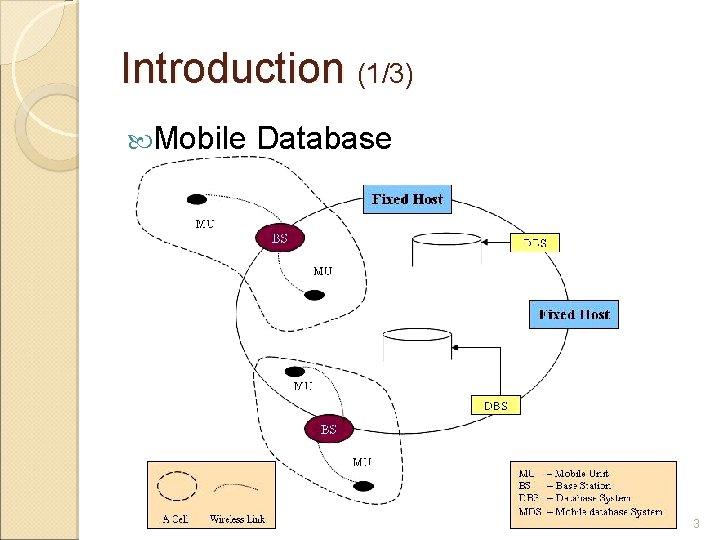
Introduction (1/3) Mobile Database 3
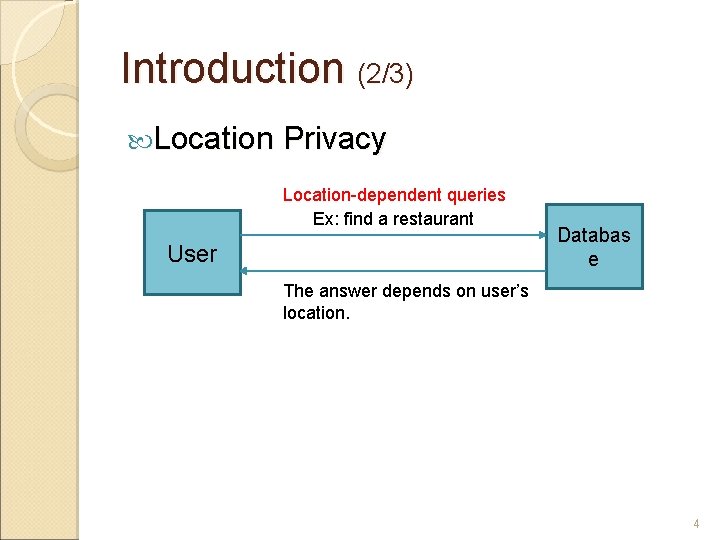
Introduction (2/3) Location Privacy Location-dependent queries Ex: find a restaurant User Databas e The answer depends on user’s location. 4
Introduction (3/3) Goal ◦ Blind. Location ◦ Mutual Authentication ◦ Prevention Insiders Attacks Outsiders Attacks ◦ Low computation time 5
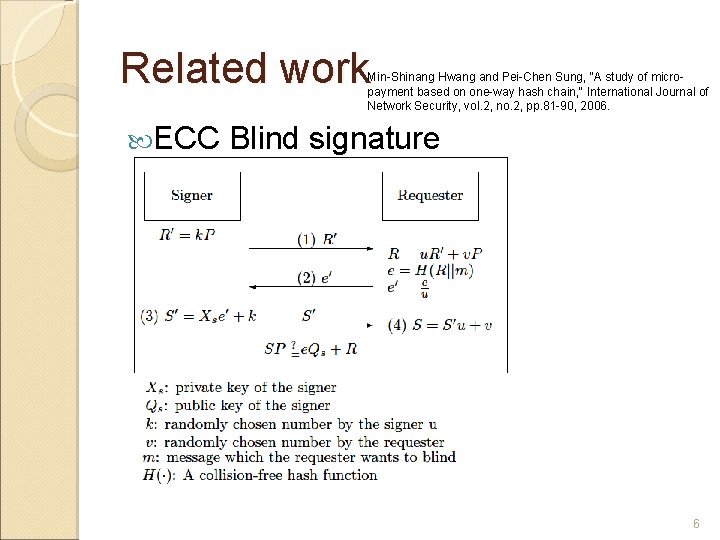
Related work Min-Shinang Hwang and Pei-Chen Sung, "A study of micropayment based on one-way hash chain, " International Journal of Network Security, vol. 2, no. 2, pp. 81 -90, 2006. ECC Blind signature 6
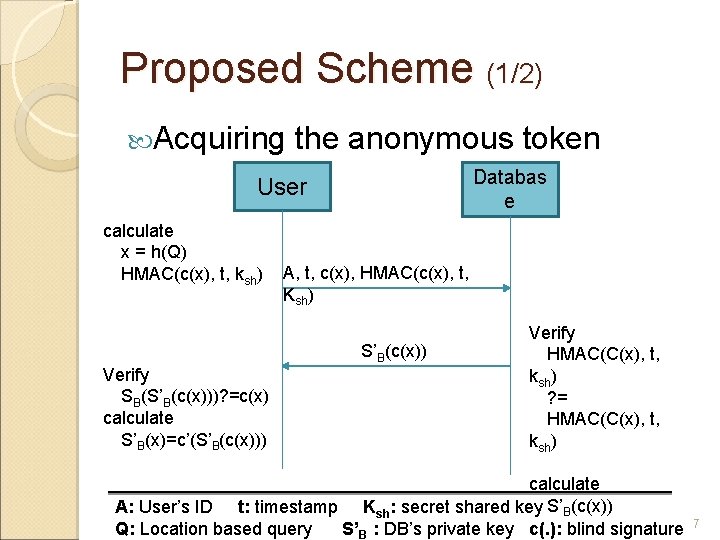
Proposed Scheme (1/2) Acquiring the anonymous token Databas e User calculate x = h(Q) HMAC(c(x), t, ksh) A, t, c(x), HMAC(c(x), t, Ksh) S’B(c(x)) Verify SB(S’B(c(x)))? =c(x) calculate S’B(x)=c’(S’B(c(x))) Verify HMAC(C(x), t, ksh) ? = HMAC(C(x), t, ksh) calculate S’B(c(x)) A: User’s ID t: timestamp Ksh: secret shared key Q: Location based query S’B : DB’s private key c(. ): blind signature 7
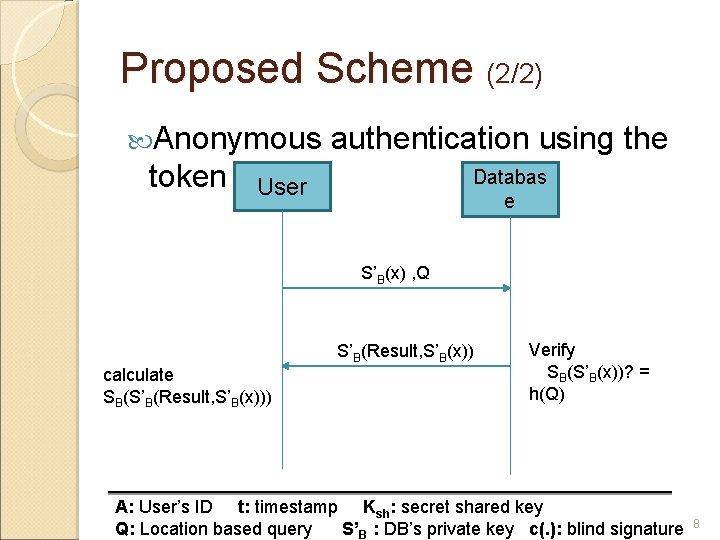
Proposed Scheme (2/2) Anonymous token authentication using the Databas e User S’B(x) , Q S’B(Result, S’B(x)) calculate SB(S’B(Result, S’B(x))) Verify SB(S’B(x))? = h(Q) A: User’s ID t: timestamp Ksh: secret shared key Q: Location based query S’B : DB’s private key c(. ): blind signature 8
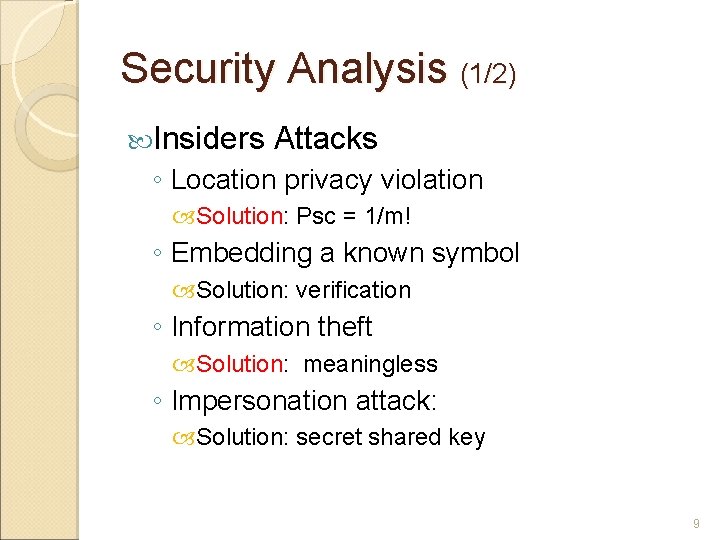
Security Analysis (1/2) Insiders Attacks ◦ Location privacy violation Solution: Psc = 1/m! ◦ Embedding a known symbol Solution: verification ◦ Information theft Solution: meaningless ◦ Impersonation attack: Solution: secret shared key 9
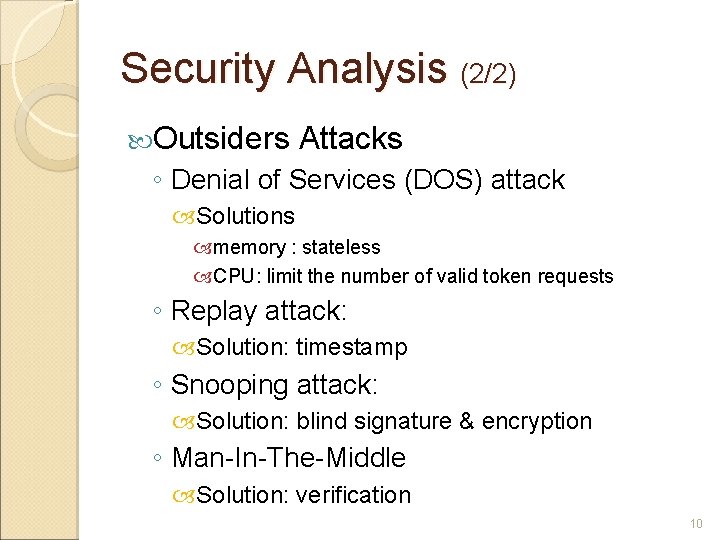
Security Analysis (2/2) Outsiders Attacks ◦ Denial of Services (DOS) attack Solutions memory : stateless CPU: limit the number of valid token requests ◦ Replay attack: Solution: timestamp ◦ Snooping attack: Solution: blind signature & encryption ◦ Man-In-The-Middle Solution: verification 10
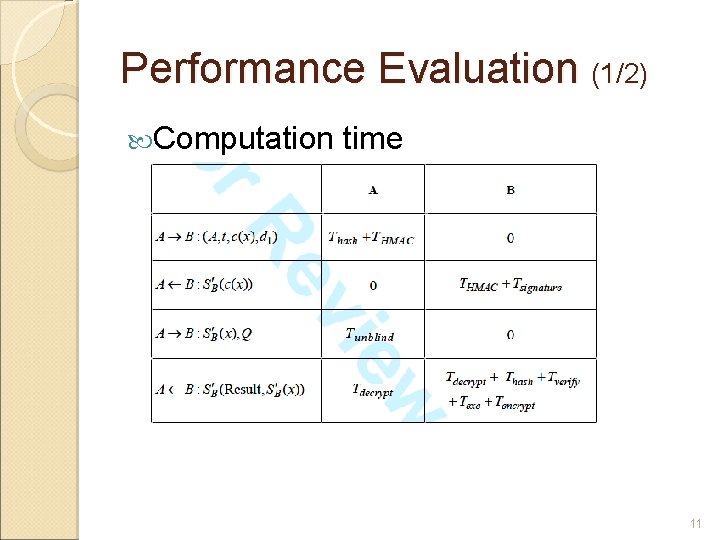
Performance Evaluation (1/2) Computation time 11
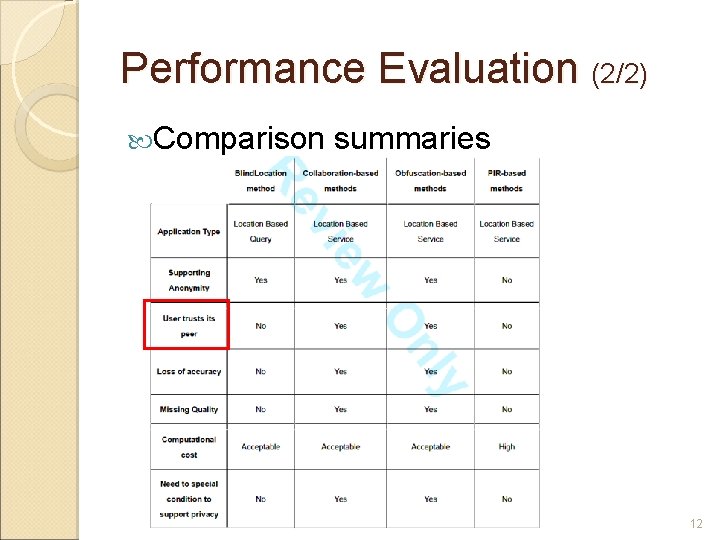
Performance Evaluation (2/2) Comparison summaries 12
Conclusion Solve the location privacy problem The quality of service is not forfeited 13

- Slides: 15