Innovation and Collaboration with Mcard Peter Honeyman Center
Innovation and Collaboration with Mcard Peter Honeyman Center for Information Technology Integration University of Michigan Ann Arbor

A little bit about CITI u Center for Information Technology Integration – Founded in 1986 as part of Information Technology Division – Now in CIO office u Research and development “skunkworks” u Advance UMich info tech environment, transfer results to University, government, industry u Externally funded
CITI staff u Faculty and staff scientists u Researchers and programmers u Graduate and undergraduate students
CITI core competencies u Middleware lab u Enterprise-scale info tech integration – – Distributed file systems Mobile computing High-speed networking Integrated security u Proposal writing
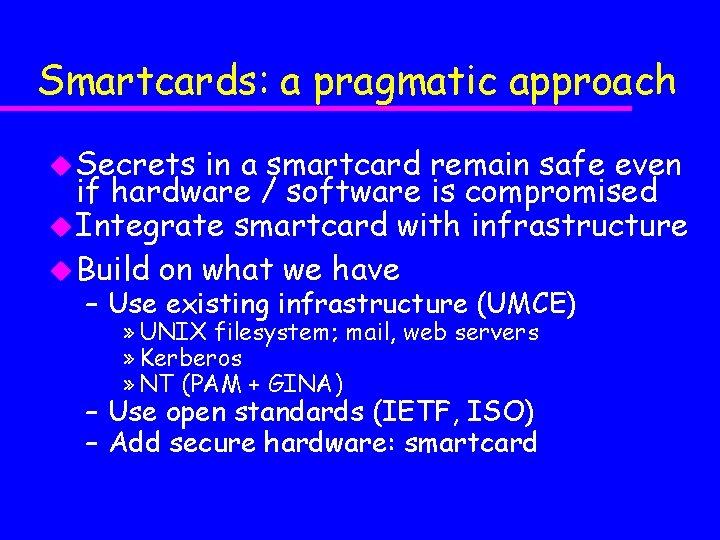
Smartcards: a pragmatic approach u Secrets in a smartcard remain safe even if hardware / software is compromised u Integrate smartcard with infrastructure u Build on what we have – Use existing infrastructure (UMCE) » UNIX filesystem; mail, web servers » Kerberos » NT (PAM + GINA) – Use open standards (IETF, ISO) – Add secure hardware: smartcard
Experimental software u Primary – – – targets: Open. BSD Linux AIX NT Palm. Pilot Java. Card u T=0, T=1
Innovation: Outline u Smartcard Filesystem u Smartcard Integration with Kerberos u Secure Bootstrap with Smartcard u IP on Smartcard
Smartcard filesystem u ISO-7816 – Standard smartcard interface – Message framing protocol (too primitive to be usable) – Many vendor dependencies u Smartcard programming toolkits – IBM MFC, Microsoft PC/SC, Open. Card framework, EMV’ 96, PKCS#11, … – Smartcard-specific everything: language, API, toolkit, library, application, etc. – Hassle learning toolkit after toolkit – API dependencies
SCFS goals and policies u Integrate a smartcard with UNIX – VFS: UNIX filesystem API u Take advantage of UNIX environment – Allows sophisticated UNIX commands – Access through symlinks u Any ISO-7816 smartcard u Easy integration with applications – – Netscape cookies PGP private keyring Kerberos tickets SSH private key
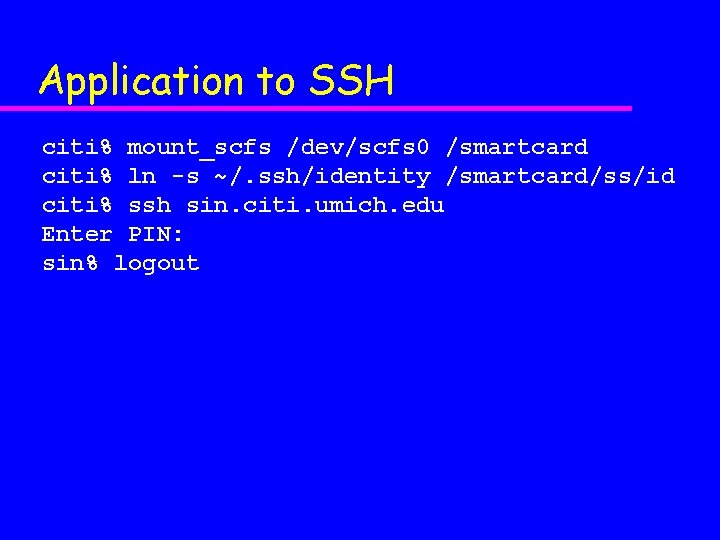
Application to SSH citi% mount_scfs /dev/scfs 0 /smartcard citi% ln -s ~/. ssh/identity /smartcard/ss/id citi% ssh sin. citi. umich. edu Enter PIN: sin% logout
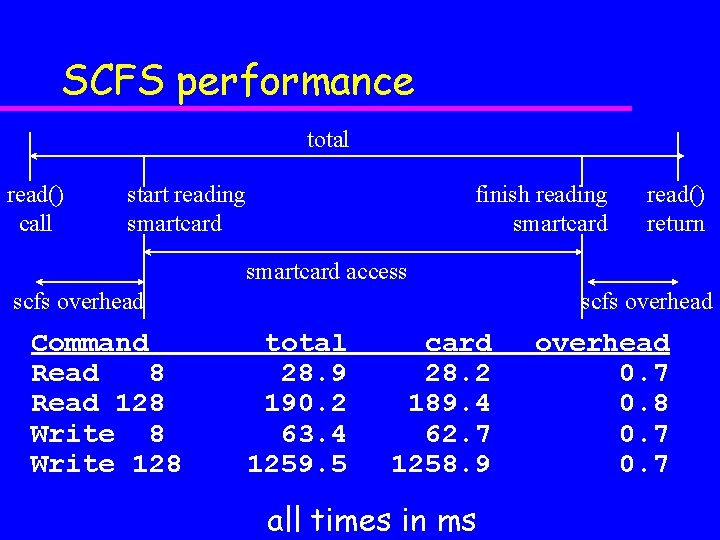
SCFS performance total read() call start reading smartcard finish reading smartcard read() return smartcard access scfs overhead Command Read 8 Read 128 Write 128 scfs overhead total 28. 9 190. 2 63. 4 1259. 5 card 28. 2 189. 4 62. 7 1258. 9 all times in ms overhead 0. 7 0. 8 0. 7
SCFS problem areas u Order of remove u Directories and metadata
Directory entry file u ISO-7816 metadata does not have the right – FID, file type, size u Required for ls, cat u Hack: “. i” in every directory
Hack: ioctl() u Some ISO-7816 -4 features do not fit the UNIX filesystem abstraction u creat(), mkdir() need size u Crypto commands (authentication, verify key, …) u Issues with application loading
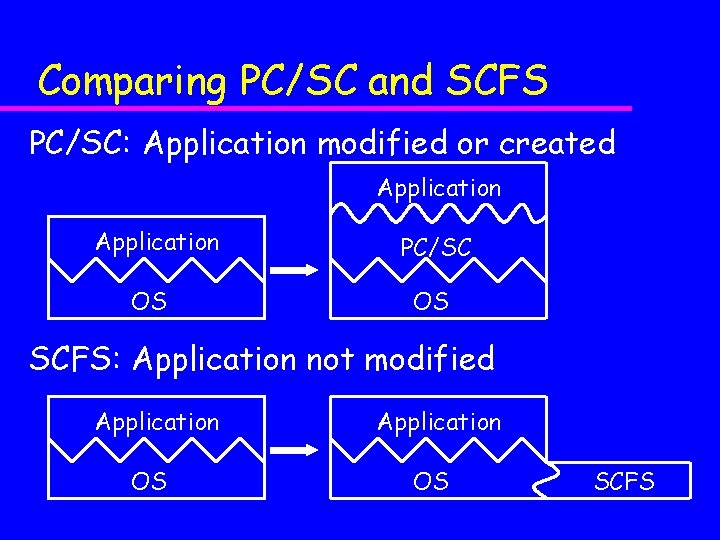
Comparing PC/SC and SCFS PC/SC: Application modified or created Application OS PC/SC OS SCFS: Application not modified Application OS SCFS
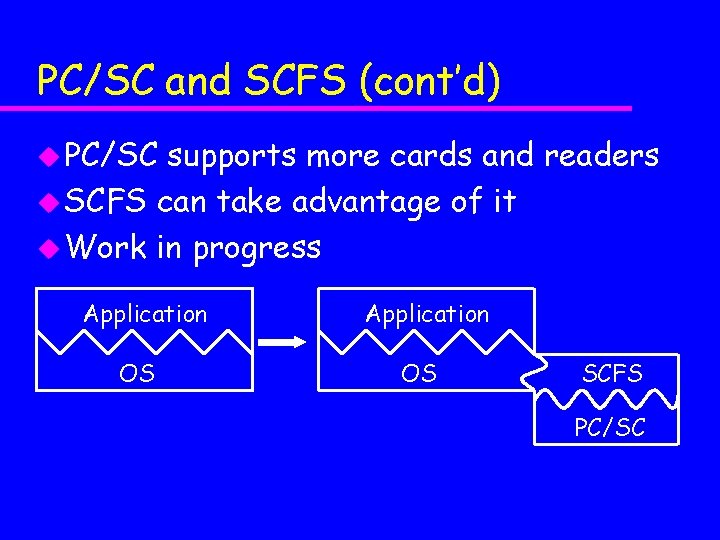
PC/SC and SCFS (cont’d) u PC/SC supports more cards and readers u SCFS can take advantage of it u Work in progress Application OS SCFS PC/SC
SCFS wrap-up u Powerful, flexible API u Overhead is small u Useful as a low-level development – ls, cd, pwd, make, etc. u Secure tool storage for user profiles, web cookies, Kerberos tickets, private keys, etc.
Smartcard/Kerberos integration u University of Michigan computing environment is protected by Kerberos – So are MIT, CMU, Stanford, Cornell, . . . u Public – (yet) key cryptography is not practical u Kerberos security limitations: – Lacks external encryption device – Lacks secure key storage – Passwords vulnerable to dictionary attack u Smartcards can solve these problems
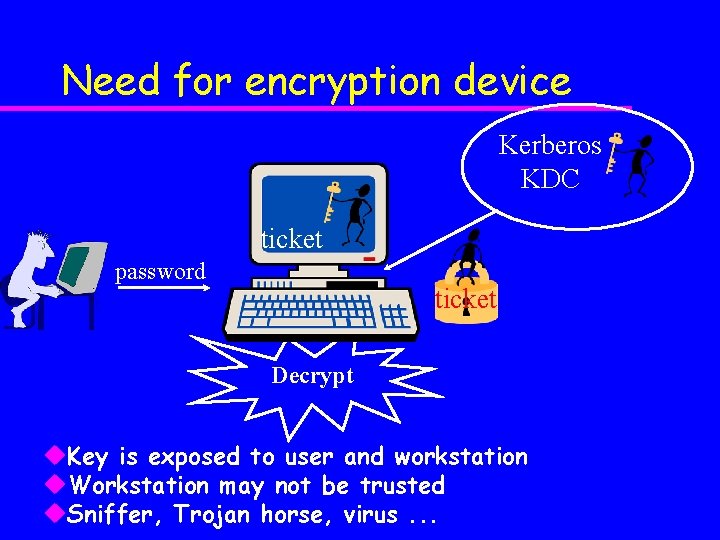
Need for encryption device Kerberos KDC ticket password ticket Decrypt u. Key is exposed to user and workstation u. Workstation may not be trusted u. Sniffer, Trojan horse, virus. . .
Need for secure storage u Keys stored on hard disk or in memory are vulnerable u Hard disks are not secure – Adversary with administrative rights can access keys – Data in a hard disk may be backed up in an unprotected mass storage device u Memory is not secure – Adversary can scan memory – Data in memory can be paged out to a hard disk
Dictionary attack u Create a list of English words, names, etc. – Also Star Wars, German, Shakespeare, … – thx 1138 is a vulnerable password! : -( u Derive keys from the words in the list u Obtain a <plaintext, ciphertext> pair – Kerberos gives up <plaintext, ciphertext> easily u Decrypt ciphertext with the derived key – If plaintext recovered, password is exposed u UMich: 1997 > 4, 000 vulnerable accounts in
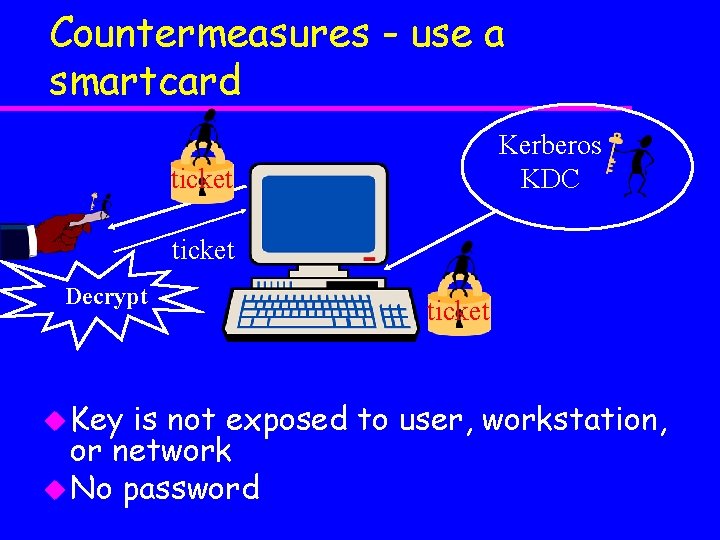
Countermeasures - use a smartcard Kerberos KDC ticket Decrypt u Key ticket is not exposed to user, workstation, or network u No password
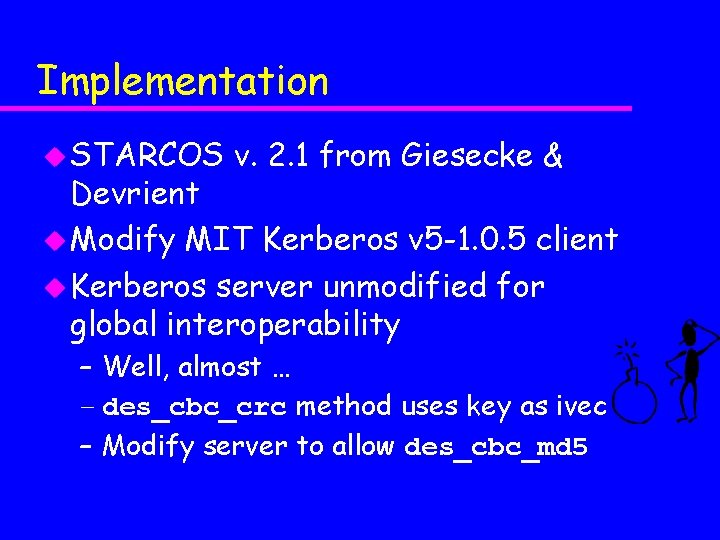
Implementation u STARCOS v. 2. 1 from Giesecke & Devrient u Modify MIT Kerberos v 5 -1. 0. 5 client u Kerberos server unmodified for global interoperability – Well, almost … – des_cbc_crc method uses key as ivec – Modify server to allow des_cbc_md 5
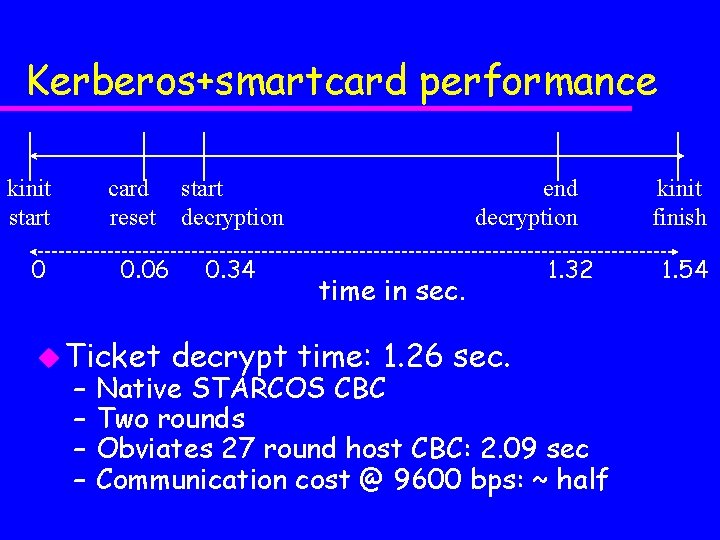
Kerberos+smartcard performance kinit start card reset 0 0. 06 u Ticket – – start decryption 0. 34 end decryption time in sec. decrypt time: 1. 26 sec. 1. 32 Native STARCOS CBC Two rounds Obviates 27 round host CBC: 2. 09 sec Communication cost @ 9600 bps: ~ half kinit finish 1. 54
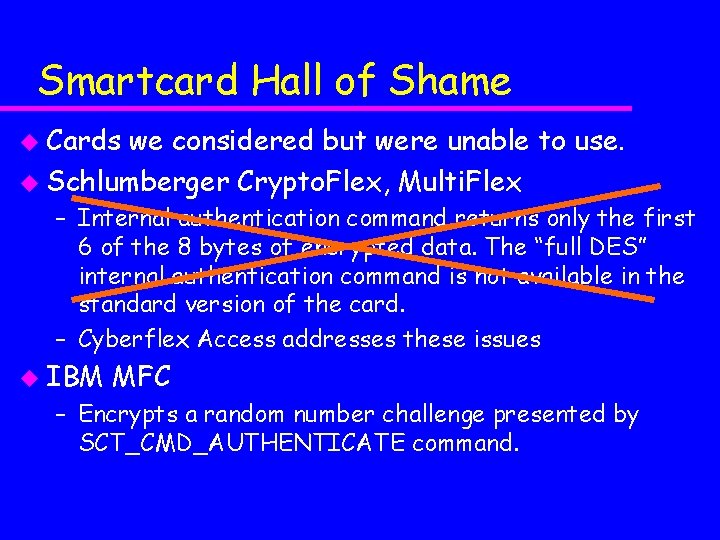
Smartcard Hall of Shame u Cards we considered but were unable to use. u Schlumberger Crypto. Flex, Multi. Flex – Internal authentication command returns only the first 6 of the 8 bytes of encrypted data. The “full DES” internal authentication command is not available in the standard version of the card. – Cyberflex Access addresses these issues u IBM MFC – Encrypts a random number challenge presented by SCT_CMD_AUTHENTICATE command.
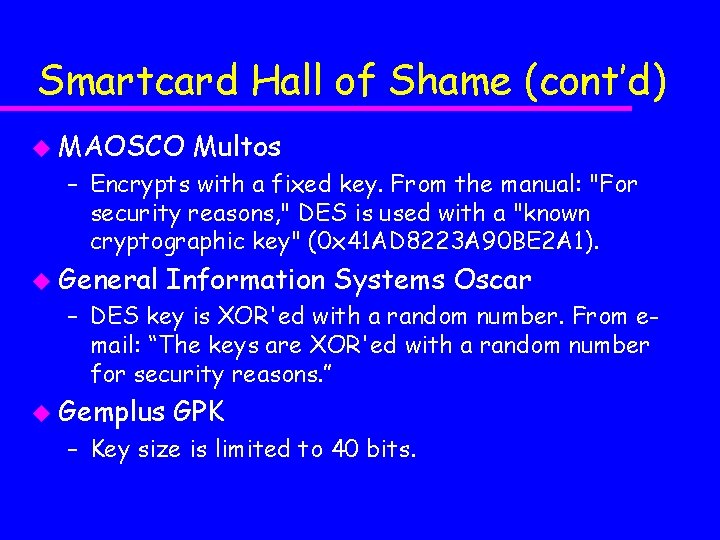
Smartcard Hall of Shame (cont’d) u MAOSCO Multos – Encrypts with a fixed key. From the manual: "For security reasons, " DES is used with a "known cryptographic key" (0 x 41 AD 8223 A 90 BE 2 A 1). u General Information Systems Oscar – DES key is XOR'ed with a random number. From email: “The keys are XOR'ed with a random number for security reasons. ” u Gemplus GPK – Key size is limited to 40 bits.
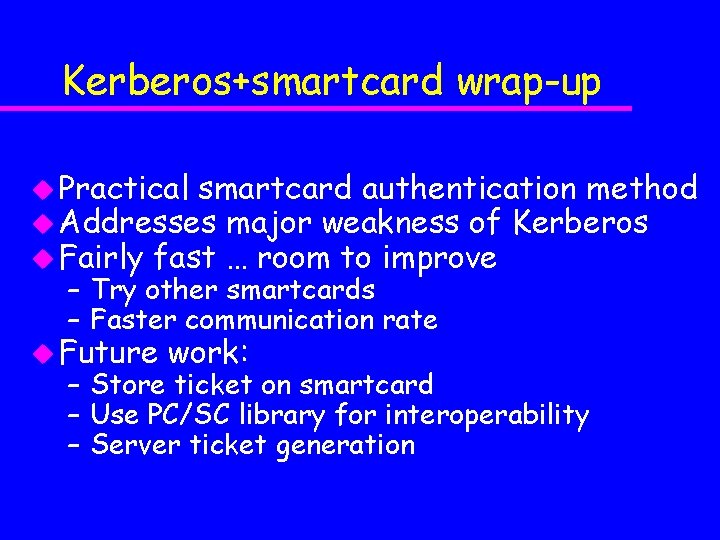
Kerberos+smartcard wrap-up u Practical smartcard authentication method u Addresses major weakness of Kerberos u Fairly fast … room to improve – Try other smartcards – Faster communication rate u Future work: – Store ticket on smartcard – Use PC/SC library for interoperability – Server ticket generation
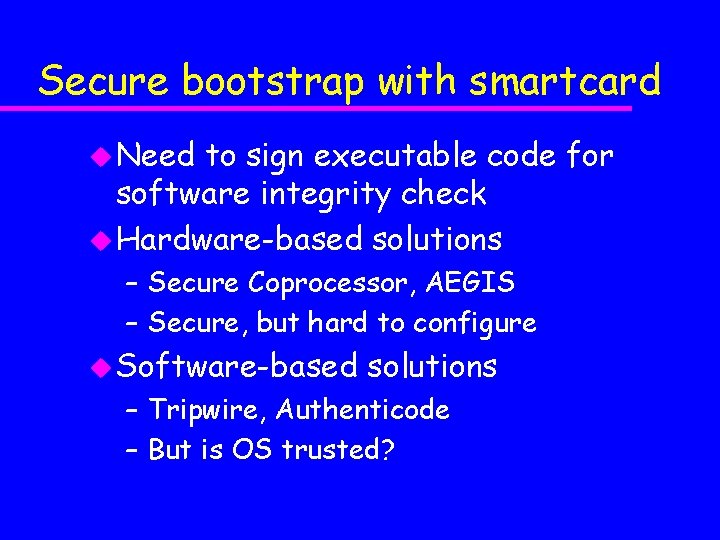
Secure bootstrap with smartcard u Need to sign executable code for software integrity check u Hardware-based solutions – Secure Coprocessor, AEGIS – Secure, but hard to configure u Software-based solutions – Tripwire, Authenticode – But is OS trusted?
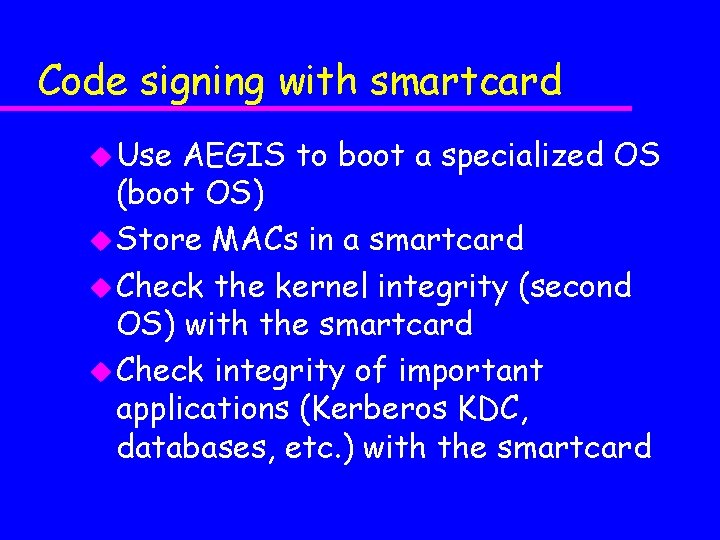
Code signing with smartcard u Use AEGIS to boot a specialized OS (boot OS) u Store MACs in a smartcard u Check the kernel integrity (second OS) with the smartcard u Check integrity of important applications (Kerberos KDC, databases, etc. ) with the smartcard
IP on smartcard u Expand smartcard accessibility to the Internet u Network protocols on smartcard – Network service used unmodified - same idea with SCFS – FTP, HTTP, E-mail, etc. u Smartcard as a mobile computer – Bring IP address with you
IP on smartcard plans u Phase 1 : IP on ISO-7816 – Will be implemented on Schlumberger Cyber. Flex – Limit communication style to host request - smartcard reply u Phase 2 : IP on bidirectional link layer – Waiting for bare smartcard
Future directions u SCFS – Porting to other operating systems (Linux, NT) – Support more cards and readers (PC/SC? ) u Kerberos – Store tickets in a smartcard – Support more cards and readers (PC/SC? ) – Smartcard-based ticket generation on server u Just started – IP on smartcard – Code signing
Innovation wrap-up u For secure operating system – Authentication: Kerberos + smartcard – Integrity check: code signing with smartcard u For convenient use of smartcard – Host - smartcard access: SCFS – Internet access: IP on smartcard
Collaboration u Partnerships with industry, government u Identify common objectives u Develop near- and intermediate-term solutions u University is a “living laboratory” of enterprise-scale issues
CITI/Schlumberger Program in Smartcard Technology u File system transparency u Secure token storage u Kerberos authentication u Internet protocol u Experimental fault analysis u Java. Card formal verification u Java. Card performance analysis u SEM attack and defense
Mcard opportunities u CITI, ITD, Fin. Ops, Medical u Public key infrastructure u Engage the creativity and energy of the student body
Any questions? http: //www. citi. umich. edu/
- Slides: 37