IBM System Storage User Guide on Solaris System
IBM System Storage™ User Guide on Solaris System Managed Encryption (version 3) Jeffrey Li (September 17, 2007) IBM Confidential © 2006 IBM Corporation
IBM System Storage § Change History Version 1: 09/14/2006 Initial Version 2: 01/03/2007 The setup parameter changers Version 3: 09/17/2007 IPv 6 support 2 IBM Confidential © 2006 IBM Corporation
IBM System Storage § Data Flow in Solaris IBMtape Device Driver § Requirements & Interoperability Support § Configuration Set-up § Error Recovery & Trouble-shooting 3 IBM Confidential © 2006 IBM Corporation
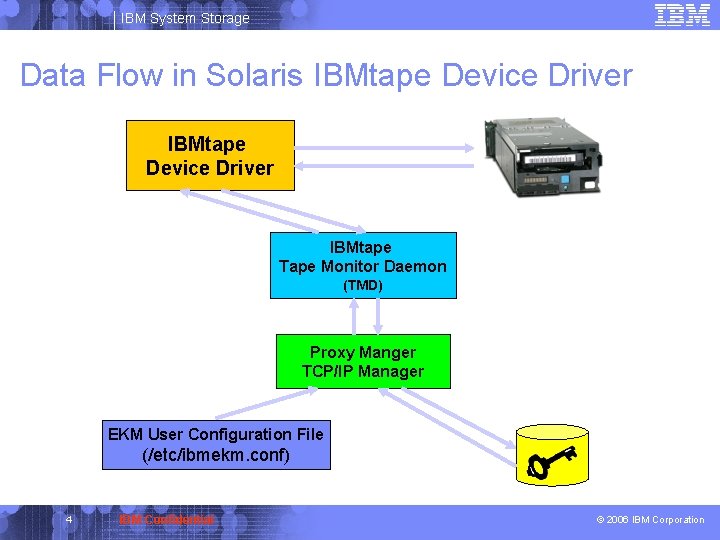
IBM System Storage Data Flow in Solaris IBMtape Device Driver IBMtape Tape Monitor Daemon (TMD) Proxy Manger TCP/IP Manager EKM User Configuration File (/etc/ibmekm. conf) 4 IBM Confidential © 2006 IBM Corporation
IBM System Storage Requirements § Tape Drive/Library 4 IBM TS 1120 Encryption Capable Tape Drive 4 IBM LTO-4 Tape Drive 4 IBM Tape Libraries with TS 1120 and LTO-4 § IBMtape Device Driver Levels 4 IBMtape 4. 1. 3. 9 or above for Sparc system 4 IBMtape 4. 1. 4. 4. x 64 or above for x 64 system 5 IBM Confidential © 2006 IBM Corporation
IBM System Storage Interoperability Support § Servers 4 Solaris Sparc Servers 4 Solaris x 64 Servers § Operating System 4 Solaris 8 or above on Sparc systems 4 Solaris 10 on x 64 systems § Storage Area Network (SAN) 4 Fibre Channel Host Bus Adapters 4 Switches 6 IBM Confidential © 2006 IBM Corporation
IBM System Storage Configuration Set-up § Tape Drive Configuration 4 Configure tape drive to be system-managed encryption from drive or library user interface § IBMtape Device Driver Installation § IBMtape Device Driver Configuration § Test and Verify Configuration 7 IBM Confidential © 2006 IBM Corporation
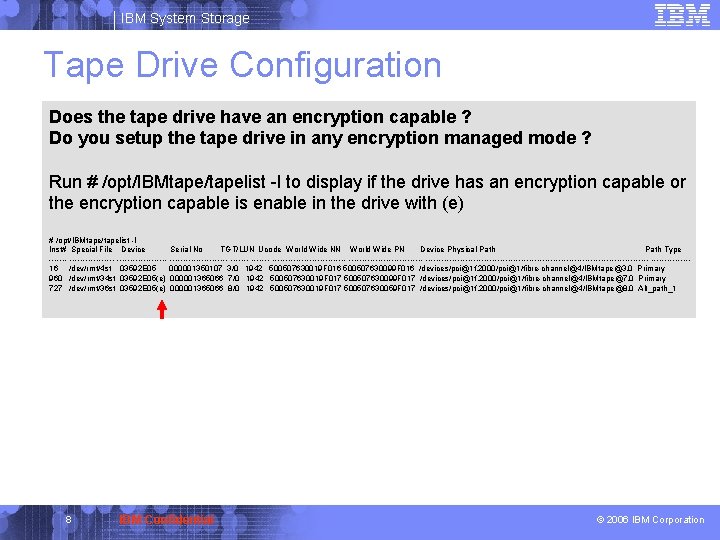
IBM System Storage Tape Drive Configuration Does the tape drive have an encryption capable ? Do you setup the tape drive in any encryption managed mode ? Run # /opt/IBMtape/tapelist -l to display if the drive has an encryption capable or the encryption capable is enable in the drive with (e) # /opt/IBMtape/tapelist -l Inst# Special File Device Serial No TGT/LUN Ucode World Wide NN World Wide PN Device Physical Path Type ----------------- -------------------------------------------------16 /dev/rmt/4 st 03592 E 05 000001350107 3/0 1942 500507630019 F 016 500507630099 F 016 /devices/pci@1 f, 2000/pci@1/fibre-channel@4/IBMtape@3, 0 Primary 960 /dev/rmt/34 st 03592 E 05(e) 000001365066 7/0 1942 500507630019 F 017 500507630099 F 017 /devices/pci@1 f, 2000/pci@1/fibre-channel@4/IBMtape@7, 0 Primary 727 /dev/rmt/36 st 03592 E 05(e) 000001365066 8/0 1942 500507630019 F 017 500507630059 F 017 /devices/pci@1 f, 2000/pci@1/fibre-channel@4/IBMtape@8, 0 Alt_path_1 8 IBM Confidential © 2006 IBM Corporation

IBM System Storage IBMtape Device Driver Installation What is new in the installation? 1. A new configuration file of ibmekm. conf in the directory of /etc 2. A new entry for new pseudo device in /usr/kernel/drv/IBMtape. conf name="IBMtape" parent="pseudo" instance=16382; 3. Remove a comment/entry in /etc/tmd. conf if the file exists #control_node_file = /devices/pseudo/IBMtape@16383: ibmcontrol 9 IBM Confidential © 2006 IBM Corporation
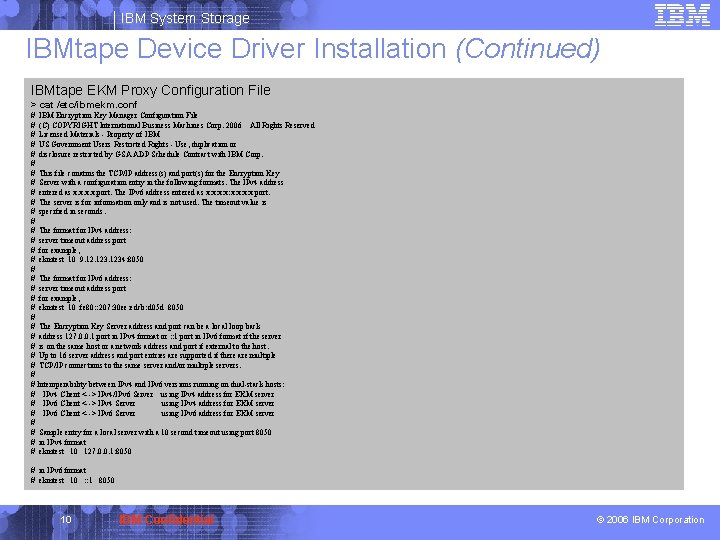
IBM System Storage IBMtape Device Driver Installation (Continued) IBMtape EKM Proxy Configuration File > cat /etc/ibmekm. conf # IBM Encryption Key Manager Configuration File # (C) COPYRIGHT International Business Machines Corp. 2006 All Rights Reserved # Licensed Materials - Property of IBM # US Government Users Restricted Rights - Use, duplication or # disclosure restricted by GSA ADP Schedule Contract with IBM Corp. # # This file conatins the TCP/IP address(s) and port(s) for the Encryption Key # Server with a configuration entry in the following formats. The IPv 4 address # entered as x. x: port. The IPv 6 address entered as x: x: x port. # The server is for information only and is not used. The timeout value is # specified in seconds. # # The format for IPv 4 address: # server timeout address: port # for example, # ekmtest 10 9. 1234: 8050 # # The format for IPv 6 address: # server timeout address port # for example, # ekmtest 10 fe 80: : 207: 30 ee: edcb: d 05 d 8050 # # The Encryption Key Server address and port can be a local loop back # address 127. 0. 0. 1: port in IPv 4 format or : : 1 port in IPv 6 format if the server # is on the same host or a network address and port if external to the host. # Up to 16 server address and port entries are supported if there are multiple # TCP/IP connections to the same server and/or multiple servers. # # Interoperability between IPv 4 and IPv 6 versions running on dual-stack hosts: # IPv 4 Client <--> IPv 4/IPv 6 Server using IPv 4 address for EKM server # IPv 6 Client <--> IPv 4 Server using IPv 4 address for EKM server # IPv 6 Client <--> IPv 6 Server using IPv 6 address for EKM server # # Sample entry for a local server with a 10 second timeout using port 8050 # in IPv 4 format # ekmtest 10 127. 0. 0. 1: 8050 # in IPv 6 format # ekmtest 10 : : 1 8050 10 IBM Confidential © 2006 IBM Corporation
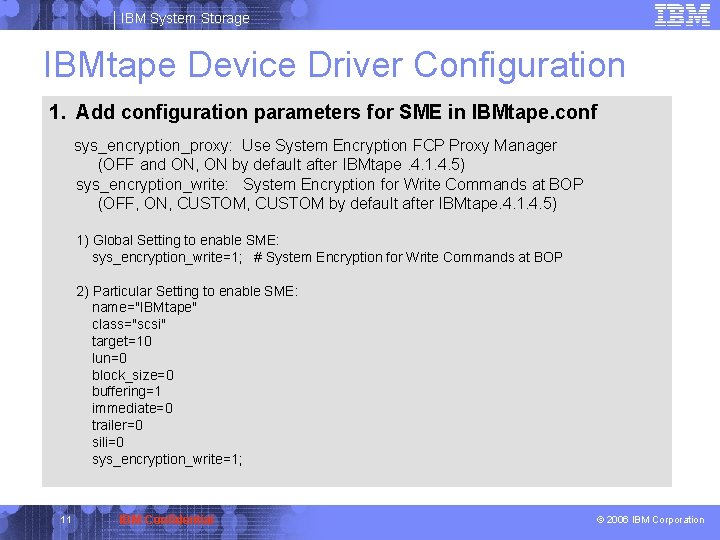
IBM System Storage IBMtape Device Driver Configuration 1. Add configuration parameters for SME in IBMtape. conf sys_encryption_proxy: Use System Encryption FCP Proxy Manager (OFF and ON, ON by default after IBMtape. 4. 1. 4. 5) sys_encryption_write: System Encryption for Write Commands at BOP (OFF, ON, CUSTOM by default after IBMtape. 4. 1. 4. 5) 1) Global Setting to enable SME: sys_encryption_write=1; # System Encryption for Write Commands at BOP 2) Particular Setting to enable SME: name="IBMtape" class="scsi" target=10 lun=0 block_size=0 buffering=1 immediate=0 trailer=0 sili=0 sys_encryption_write=1; 11 IBM Confidential © 2006 IBM Corporation
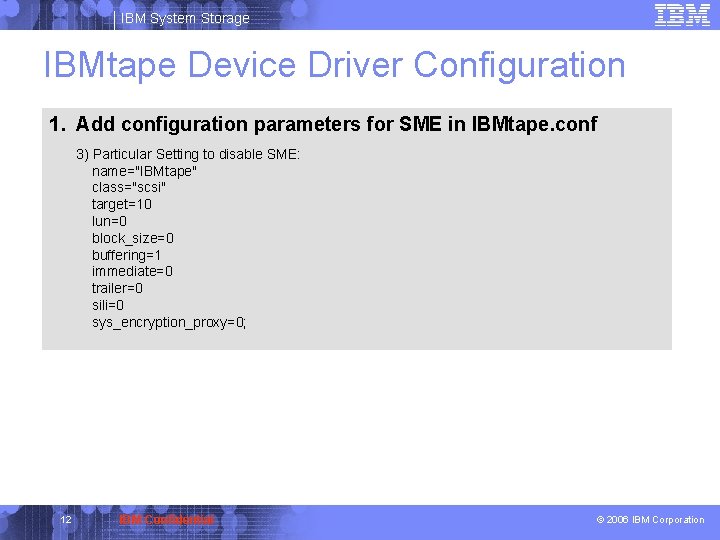
IBM System Storage IBMtape Device Driver Configuration 1. Add configuration parameters for SME in IBMtape. conf 3) Particular Setting to disable SME: name="IBMtape" class="scsi" target=10 lun=0 block_size=0 buffering=1 immediate=0 trailer=0 sili=0 sys_encryption_proxy=0; 12 IBM Confidential © 2006 IBM Corporation
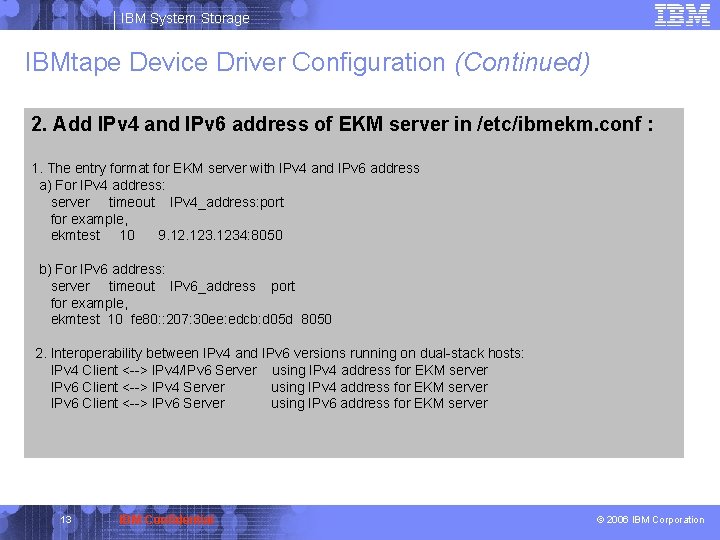
IBM System Storage IBMtape Device Driver Configuration (Continued) 2. Add IPv 4 and IPv 6 address of EKM server in /etc/ibmekm. conf : 1. The entry format for EKM server with IPv 4 and IPv 6 address a) For IPv 4 address: server timeout IPv 4_address: port for example, ekmtest 10 9. 1234: 8050 b) For IPv 6 address: server timeout IPv 6_address port for example, ekmtest 10 fe 80: : 207: 30 ee: edcb: d 05 d 8050 2. Interoperability between IPv 4 and IPv 6 versions running on dual-stack hosts: IPv 4 Client <--> IPv 4/IPv 6 Server using IPv 4 address for EKM server IPv 6 Client <--> IPv 4 Server using IPv 4 address for EKM server IPv 6 Client <--> IPv 6 Server using IPv 6 address for EKM server 13 IBM Confidential © 2006 IBM Corporation
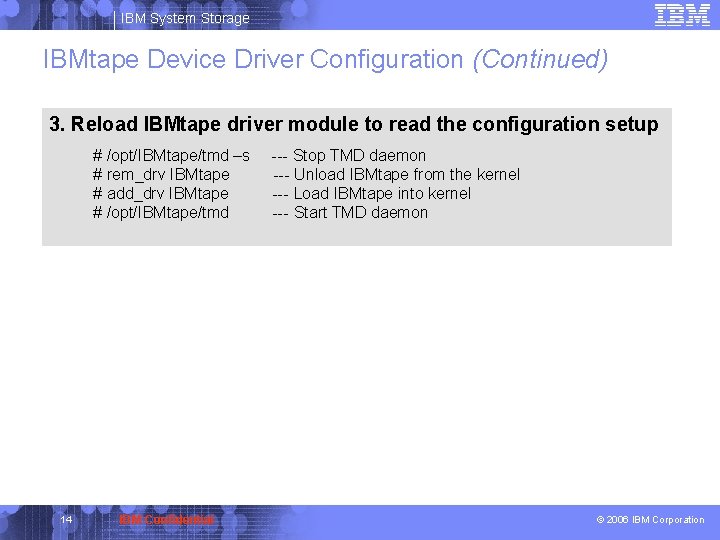
IBM System Storage IBMtape Device Driver Configuration (Continued) 3. Reload IBMtape driver module to read the configuration setup # /opt/IBMtape/tmd –s # rem_drv IBMtape # add_drv IBMtape # /opt/IBMtape/tmd 14 IBM Confidential --- Stop TMD daemon --- Unload IBMtape from the kernel --- Load IBMtape into kernel --- Start TMD daemon © 2006 IBM Corporation
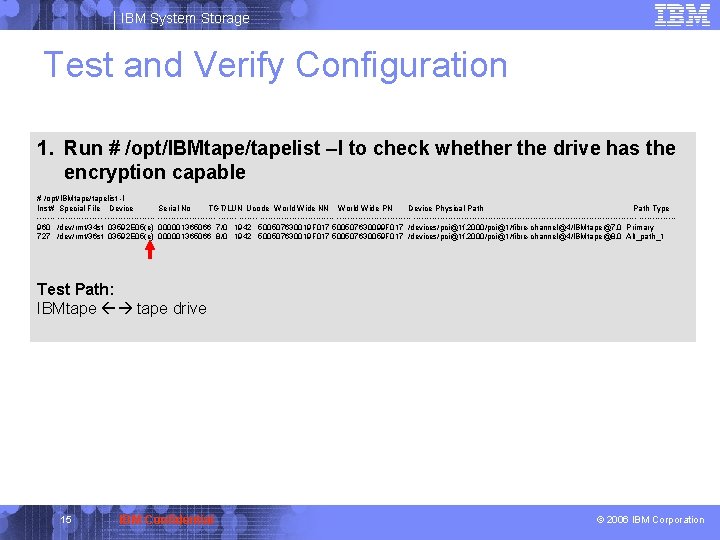
IBM System Storage Test and Verify Configuration 1. Run # /opt/IBMtape/tapelist –l to check whether the drive has the encryption capable # /opt/IBMtape/tapelist -l Inst# Special File Device Serial No TGT/LUN Ucode World Wide NN World Wide PN Device Physical Path Type ----------------- -------------------------------------------------960 /dev/rmt/34 st 03592 E 05(e) 000001365066 7/0 1942 500507630019 F 017 500507630099 F 017 /devices/pci@1 f, 2000/pci@1/fibre-channel@4/IBMtape@7, 0 Primary 727 /dev/rmt/36 st 03592 E 05(e) 000001365066 8/0 1942 500507630019 F 017 500507630059 F 017 /devices/pci@1 f, 2000/pci@1/fibre-channel@4/IBMtape@8, 0 Alt_path_1 Test Path: IBMtape drive 15 IBM Confidential © 2006 IBM Corporation
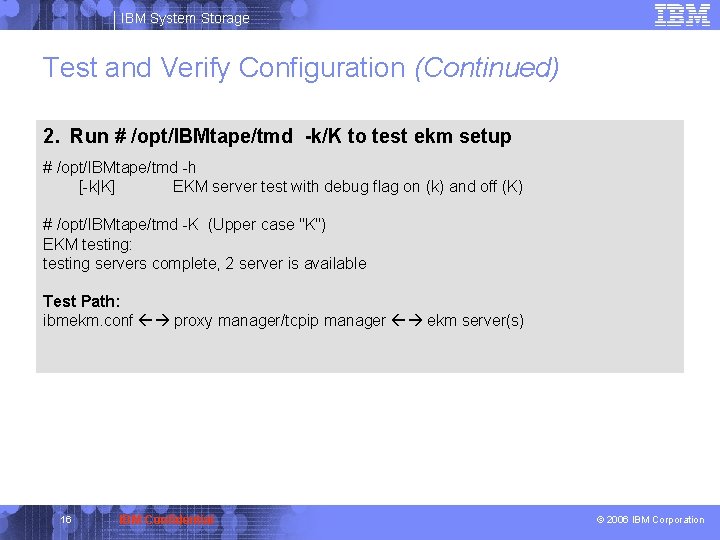
IBM System Storage Test and Verify Configuration (Continued) 2. Run # /opt/IBMtape/tmd -k/K to test ekm setup # /opt/IBMtape/tmd -h [-k|K] EKM server test with debug flag on (k) and off (K) # /opt/IBMtape/tmd -K (Upper case "K") EKM testing: testing servers complete, 2 server is available Test Path: ibmekm. conf proxy manager/tcpip manager ekm server(s) 16 IBM Confidential © 2006 IBM Corporation
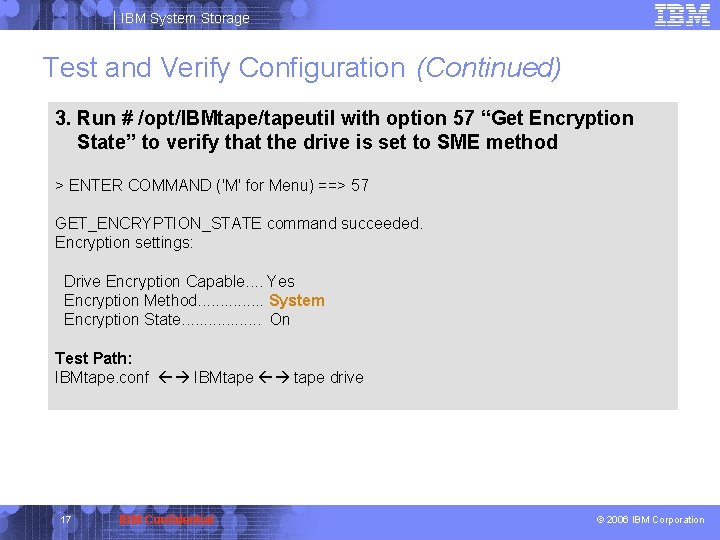
IBM System Storage Test and Verify Configuration (Continued) 3. Run # /opt/IBMtape/tapeutil with option 57 “Get Encryption State” to verify that the drive is set to SME method > ENTER COMMAND ('M' for Menu) ==> 57 GET_ENCRYPTION_STATE command succeeded. Encryption settings: Drive Encryption Capable. . Yes Encryption Method. . . . System Encryption State. . . . On Test Path: IBMtape. conf IBMtape drive 17 IBM Confidential © 2006 IBM Corporation
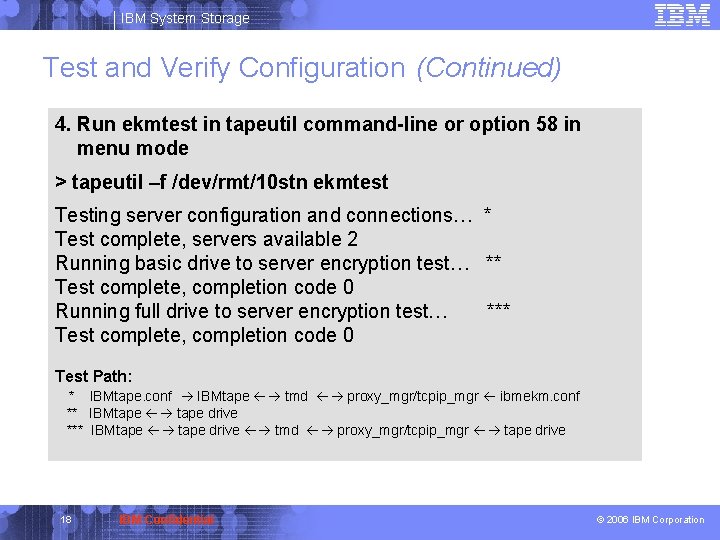
IBM System Storage Test and Verify Configuration (Continued) 4. Run ekmtest in tapeutil command-line or option 58 in menu mode > tapeutil –f /dev/rmt/10 stn ekmtest Testing server configuration and connections… * Test complete, servers available 2 Running basic drive to server encryption test… ** Test complete, completion code 0 Running full drive to server encryption test… *** Test complete, completion code 0 Test Path: * IBMtape. conf IBMtape tmd proxy_mgr/tcpip_mgr ibmekm. conf ** IBMtape drive *** IBMtape drive tmd proxy_mgr/tcpip_mgr tape drive 18 IBM Confidential © 2006 IBM Corporation
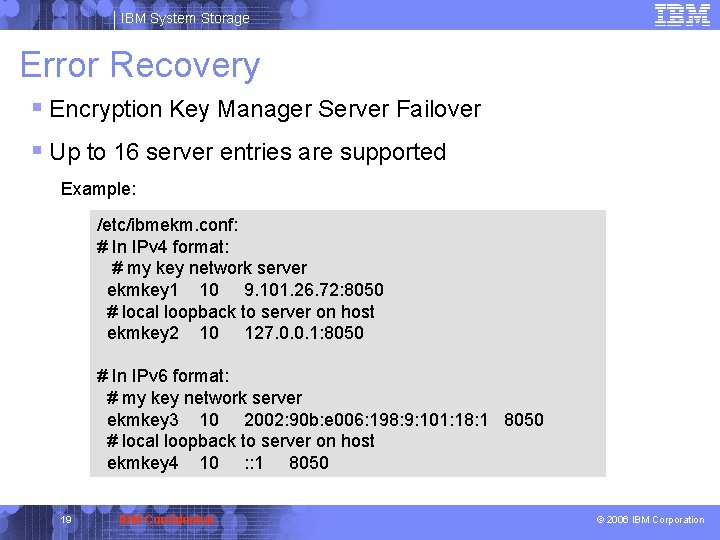
IBM System Storage Error Recovery § Encryption Key Manager Server Failover § Up to 16 server entries are supported Example: /etc/ibmekm. conf: # In IPv 4 format: # my key network server ekmkey 1 10 9. 101. 26. 72: 8050 # local loopback to server on host ekmkey 2 10 127. 0. 0. 1: 8050 # In IPv 6 format: # my key network server ekmkey 3 10 2002: 90 b: e 006: 198: 9: 101: 18: 1 8050 # local loopback to server on host ekmkey 4 10 : : 1 8050 19 IBM Confidential © 2006 IBM Corporation
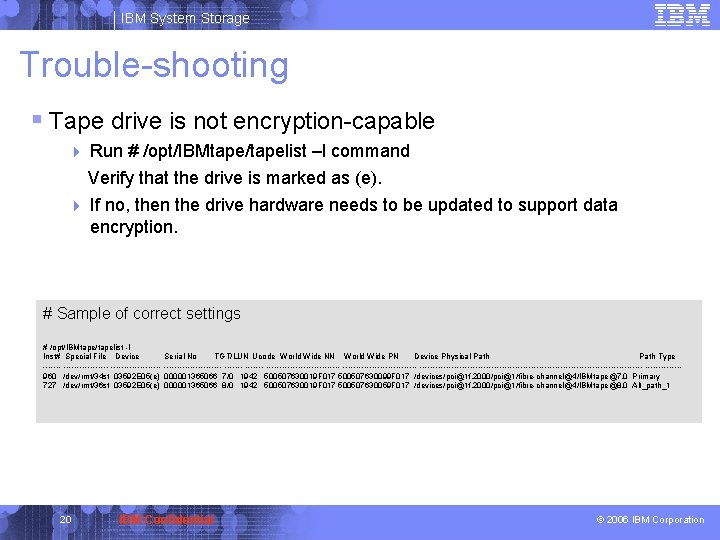
IBM System Storage Trouble-shooting § Tape drive is not encryption-capable 4 Run # /opt/IBMtape/tapelist –l command Verify that the drive is marked as (e). 4 If no, then the drive hardware needs to be updated to support data encryption. # Sample of correct settings # /opt/IBMtape/tapelist -l Inst# Special File Device Serial No TGT/LUN Ucode World Wide NN World Wide PN Device Physical Path Type ----------------- -------------------------------------------------960 /dev/rmt/34 st 03592 E 05(e) 000001365066 7/0 1942 500507630019 F 017 500507630099 F 017 /devices/pci@1 f, 2000/pci@1/fibre-channel@4/IBMtape@7, 0 Primary 727 /dev/rmt/36 st 03592 E 05(e) 000001365066 8/0 1942 500507630019 F 017 500507630059 F 017 /devices/pci@1 f, 2000/pci@1/fibre-channel@4/IBMtape@8, 0 Alt_path_1 20 IBM Confidential © 2006 IBM Corporation
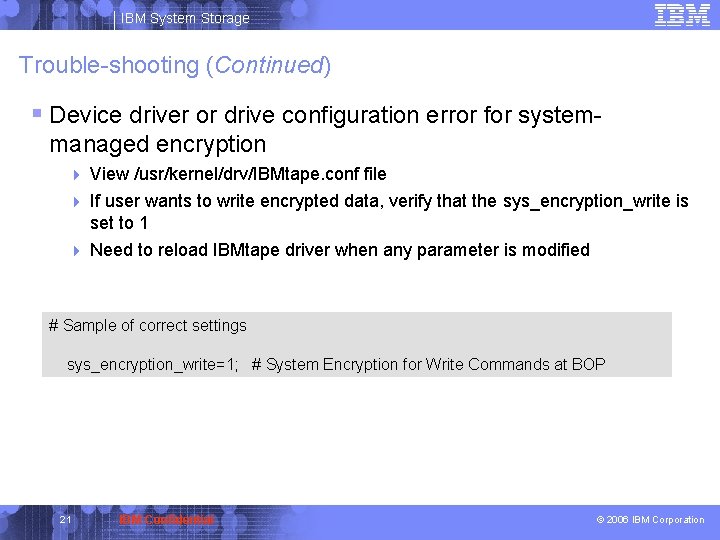
IBM System Storage Trouble-shooting (Continued) § Device driver or drive configuration error for systemmanaged encryption 4 View /usr/kernel/drv/IBMtape. conf file If user wants to write encrypted data, verify that the sys_encryption_write is set to 1 4 Need to reload IBMtape driver when any parameter is modified 4 # Sample of correct settings sys_encryption_write=1; # System Encryption for Write Commands at BOP 21 IBM Confidential © 2006 IBM Corporation
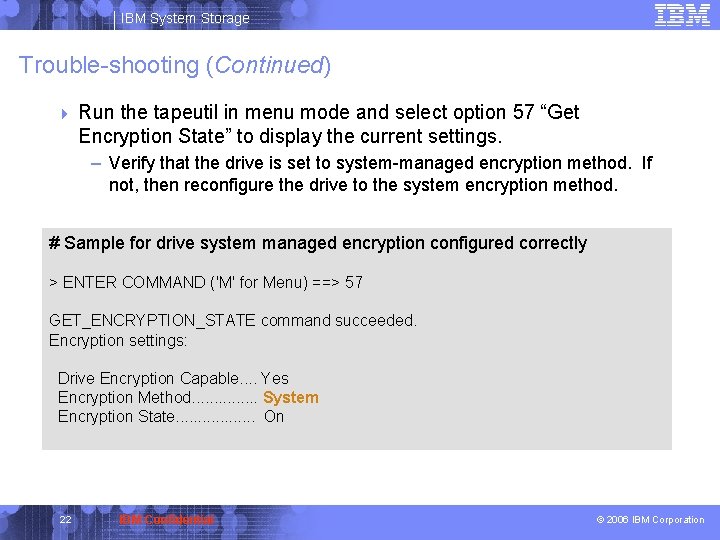
IBM System Storage Trouble-shooting (Continued) 4 Run the tapeutil in menu mode and select option 57 “Get Encryption State” to display the current settings. – Verify that the drive is set to system-managed encryption method. If not, then reconfigure the drive to the system encryption method. # Sample for drive system managed encryption configured correctly > ENTER COMMAND ('M' for Menu) ==> 57 GET_ENCRYPTION_STATE command succeeded. Encryption settings: Drive Encryption Capable. . Yes Encryption Method. . . . System Encryption State. . . . On 22 IBM Confidential © 2006 IBM Corporation
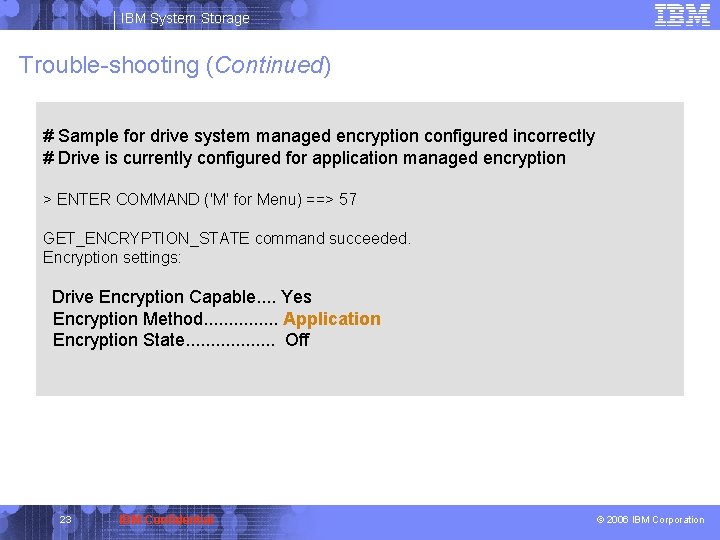
IBM System Storage Trouble-shooting (Continued) # Sample for drive system managed encryption configured incorrectly # Drive is currently configured for application managed encryption > ENTER COMMAND ('M' for Menu) ==> 57 GET_ENCRYPTION_STATE command succeeded. Encryption settings: Drive Encryption Capable. . Yes Encryption Method. . . . Application Encryption State. . . . Off 23 IBM Confidential © 2006 IBM Corporation
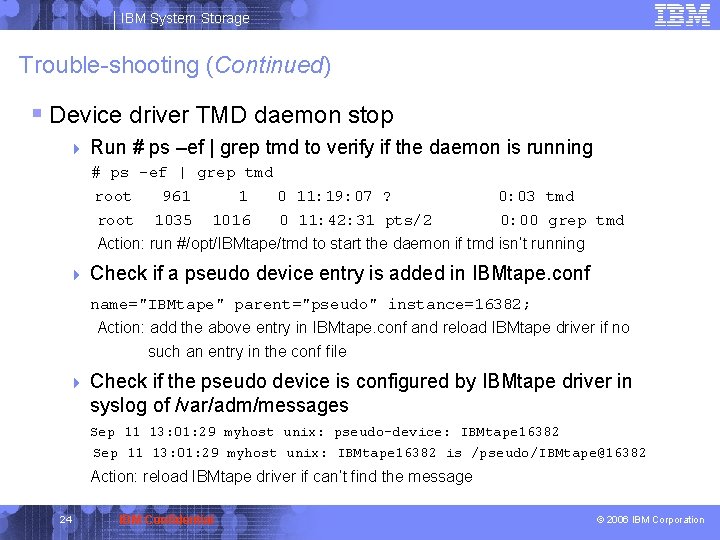
IBM System Storage Trouble-shooting (Continued) § Device driver TMD daemon stop 4 Run # ps –ef | grep tmd to verify if the daemon is running # ps -ef | grep tmd root 961 1 0 11: 19: 07 ? root 1035 1016 0 11: 42: 31 pts/2 0: 03 tmd 0: 00 grep tmd Action: run #/opt/IBMtape/tmd to start the daemon if tmd isn’t running 4 Check if a pseudo device entry is added in IBMtape. conf name="IBMtape" parent="pseudo" instance=16382; Action: add the above entry in IBMtape. conf and reload IBMtape driver if no such an entry in the conf file 4 Check if the pseudo device is configured by IBMtape driver in syslog of /var/adm/messages Sep 11 13: 01: 29 myhost unix: pseudo-device: IBMtape 16382 Sep 11 13: 01: 29 myhost unix: IBMtape 16382 is /pseudo/IBMtape@16382 Action: reload IBMtape driver if can’t find the message 24 IBM Confidential © 2006 IBM Corporation
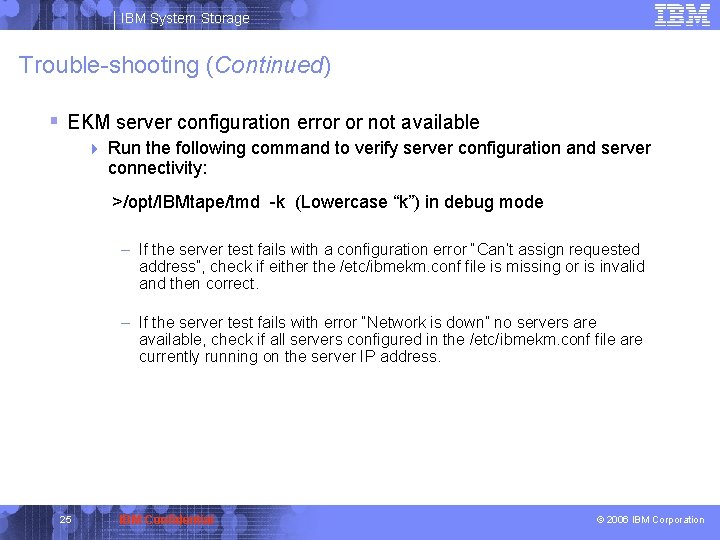
IBM System Storage Trouble-shooting (Continued) § EKM server configuration error or not available 4 Run the following command to verify server configuration and server connectivity: >/opt/IBMtape/tmd -k (Lowercase “k”) in debug mode – If the server test fails with a configuration error “Can’t assign requested address”, check if either the /etc/ibmekm. conf file is missing or is invalid and then correct. – If the server test fails with error “Network is down” no servers are available, check if all servers configured in the /etc/ibmekm. conf file are currently running on the server IP address. 25 IBM Confidential © 2006 IBM Corporation
IBM System Storage Trouble-shooting (Continued) § EKM server configuration error or not available (Continued) 4 Invoke the tapeutil menu and select option 58 or run the following command to verify server configuration and server connectivity: >tapeutil –f/dev/rmt/1 stn ekmtest – If the full drive to server encryption test fails with a permission error “Permission denied”, check if either the ekm server isn’t available recently or the drive isn’t claimed in ekm server. 26 IBM Confidential © 2006 IBM Corporation
IBM System Storage Trouble-shooting (Continued) § Other failures 4 require PFE and/or development analysis 4 the following data should be provided for a problem (2 st for example): – Collect the system, driver and device information running /opt/IBMtape/diags_info script – Turn on debug flag to log proxy manager/tcpip manager and tmd trace in /var/log/tmd. log and/or /var/adm/messages # /opt/IBMtape/tmd –s --- stop the daemon # /opt/IBMtape/tmd –t --- turn on the tracing and start the daemon – tapeutil –f /dev/rmt/2 stn ekmtest > ekmtest. out – Trun on IBMtape tracing and log the trace in /var/adm/messages 27 IBM Confidential © 2006 IBM Corporation
- Slides: 27