IBM QRadar User Behavioral Analytics 3 0 Detecting
IBM QRadar - User Behavioral Analytics 3. 0 Detecting Insider Threats and Risks
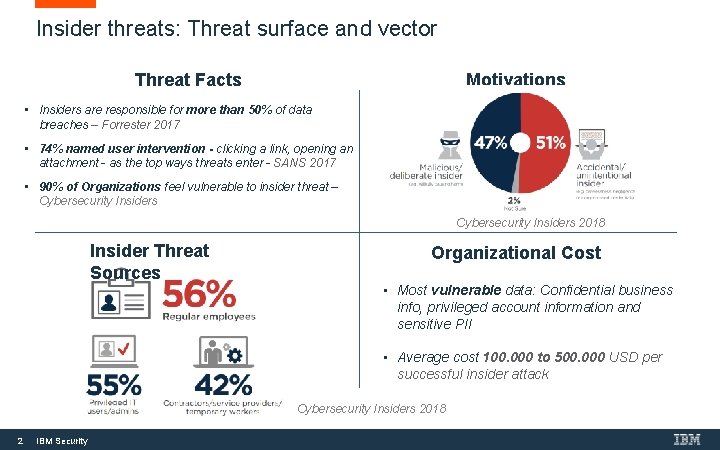
Insider threats: Threat surface and vector Motivations Threat Facts • Insiders are responsible for more than 50% of data breaches – Forrester 2017 • 74% named user intervention - clicking a link, opening an attachment - as the top ways threats enter - SANS 2017 • 90% of Organizations feel vulnerable to insider threat – Cybersecurity Insiders 2018 Insider Threat Sources Organizational Cost • Most vulnerable data: Confidential business info, privileged account information and sensitive PII • Average cost 100. 000 to 500. 000 USD per successful insider attack Cybersecurity Insiders 2018 2 IBM Security

Spectrum of Insider Threats* Lone wolves Threat actors that act on their own. Stealing or using info for malicious purpose. Vary in privileges. Collaborator Cooperate with another outsider to perpetrate a crime. Goof Acting out of ignorance, bypassing security controls, may have privilege access. Form a huge risk when becoming a pawn. “ 90% of Insider Incidents are caused by goofs” Gartner 2018 Pawn Unaware that they have been compromised. Victim of a phishing attack or malware. Common threat: Gaining illicit access followed by access abuse Based on Market Insights: Go-to-Market for Advanced Insider Threat Detection- Gartner 2018 3 IBM Security
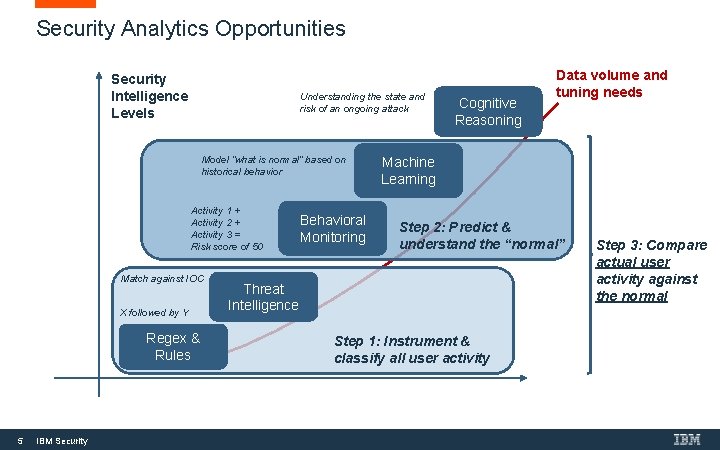
Security Analytics Opportunities Security Intelligence Levels Understanding the state and risk of an ongoing attack Model “what is normal” based on historical behavior Activity 1 + Activity 2 + Activity 3 = Risk score of 50 Match against IOC X followed by Y Regex & Rules 5 IBM Security Behavioral Monitoring Cognitive Reasoning Data volume and tuning needs Machine Learning Step 2: Predict & understand the “normal” Threat Intelligence Step 1: Instrument & classify all user activity Step 3: Compare actual user activity against the normal
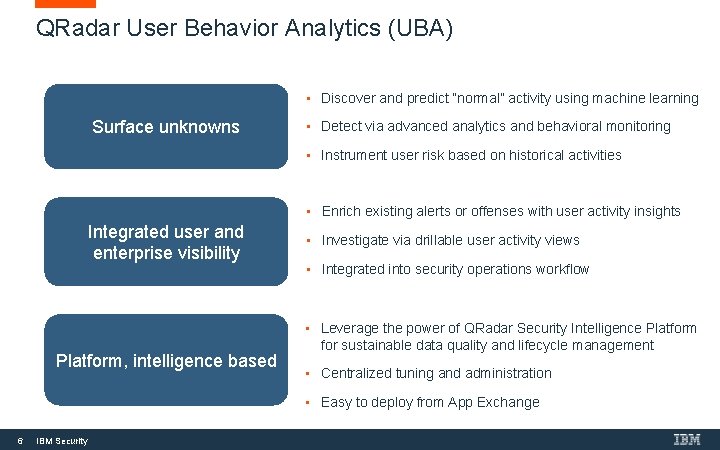
QRadar User Behavior Analytics (UBA) • Discover and predict “normal” activity using machine learning Surface unknowns • Detect via advanced analytics and behavioral monitoring • Instrument user risk based on historical activities • Enrich existing alerts or offenses with user activity insights Integrated user and enterprise visibility Platform, intelligence based • Investigate via drillable user activity views • Integrated into security operations workflow • Leverage the power of QRadar Security Intelligence Platform for sustainable data quality and lifecycle management • Centralized tuning and administration • Easy to deploy from App Exchange 6 IBM Security
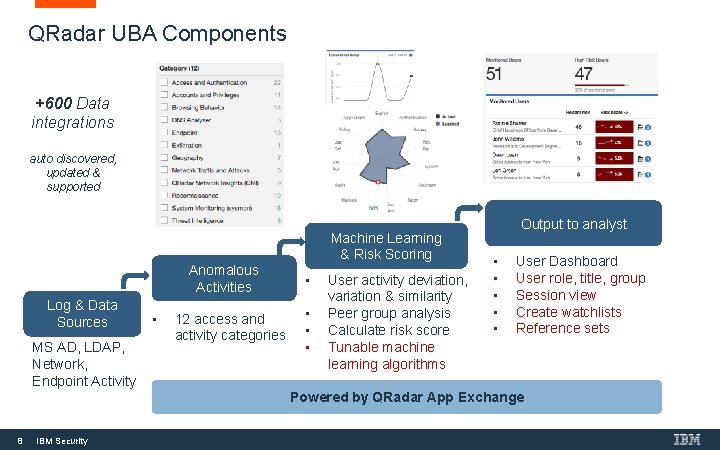
QRadar UBA Components +600 Data integrations auto discovered, updated & supported Machine Learning & Risk Scoring Anomalous Activities Log & Data Sources MS AD, LDAP, Network, Endpoint Activity • 12 access and activity categories • • User activity deviation, variation & similarity Peer group analysis Calculate risk score Tunable machine learning algorithms Output to analyst • • • User Dashboard User role, title, group Session view Create watchlists Reference sets Powered by QRadar App Exchange 8 IBM Security
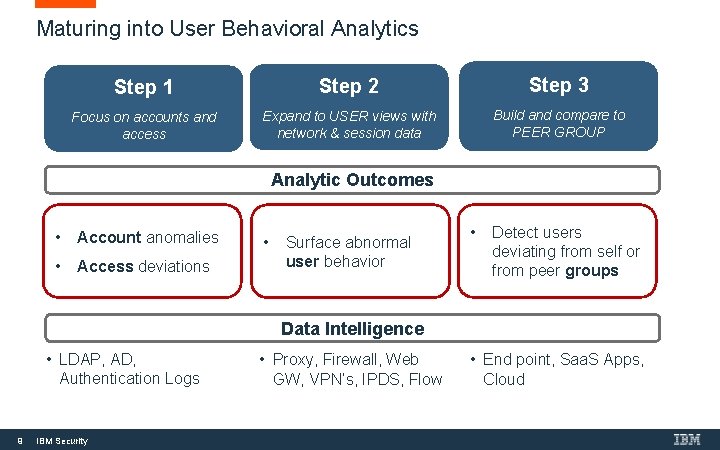
Maturing into User Behavioral Analytics Step 1 Step 2 Step 3 Focus on accounts and access Expand to USER views with network & session data Build and compare to PEER GROUP Analytic Outcomes • Account anomalies • Access deviations • Surface abnormal user behavior • Detect users deviating from self or from peer groups Data Intelligence • LDAP, AD, Authentication Logs 9 IBM Security • Proxy, Firewall, Web GW, VPN’s, IPDS, Flow • End point, Saa. S Apps, Cloud
Demo / Screenshots 10 IBM Security
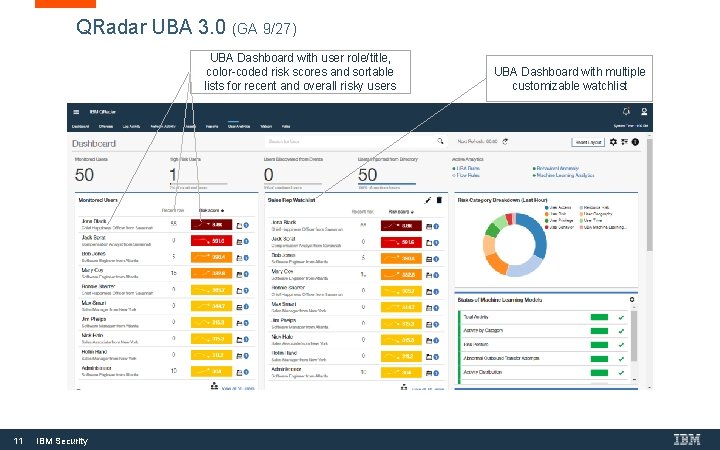
QRadar UBA 3. 0 (GA 9/27) UBA Dashboard with user role/title, color-coded risk scores and sortable lists for recent and overall risky users 11 IBM Security UBA Dashboard with multiple customizable watchlist
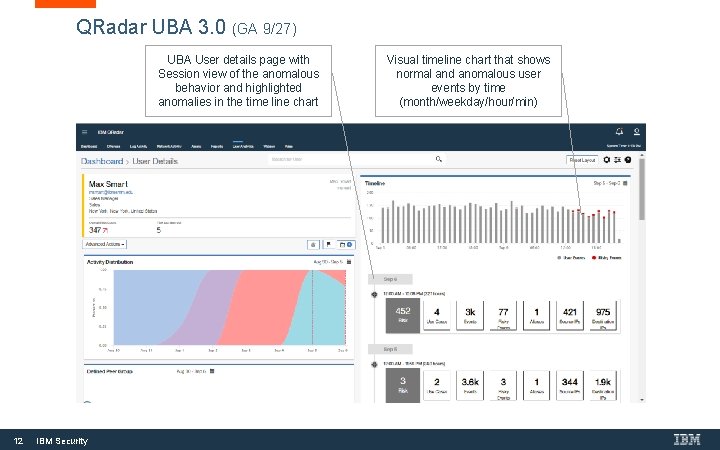
QRadar UBA 3. 0 (GA 9/27) UBA User details page with Session view of the anomalous behavior and highlighted anomalies in the time line chart 12 IBM Security Visual timeline chart that shows normal and anomalous user events by time (month/weekday/hour/min)
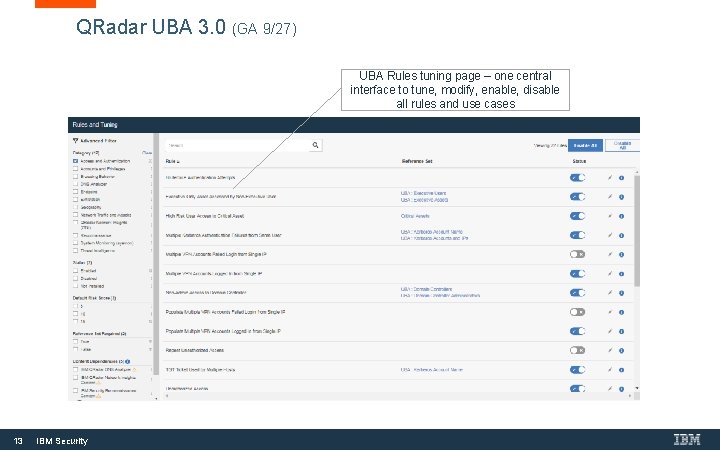
QRadar UBA 3. 0 (GA 9/27) UBA Rules tuning page – one central interface to tune, modify, enable, disable all rules and use cases 13 IBM Security
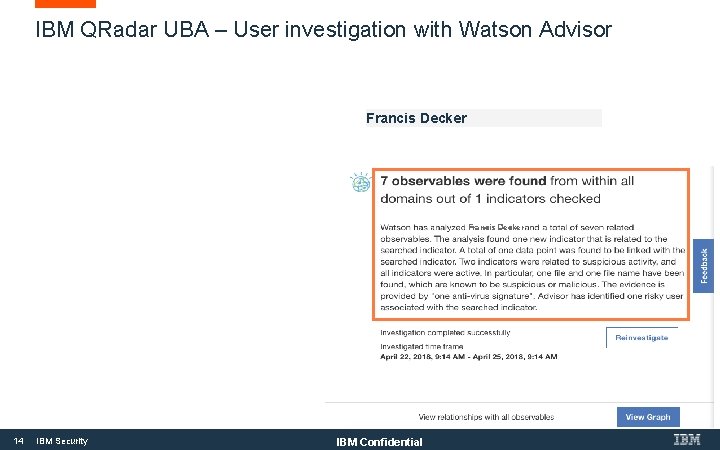
IBM QRadar UBA – User investigation with Watson Advisor Francis Decker 14 IBM Security IBM Confidential
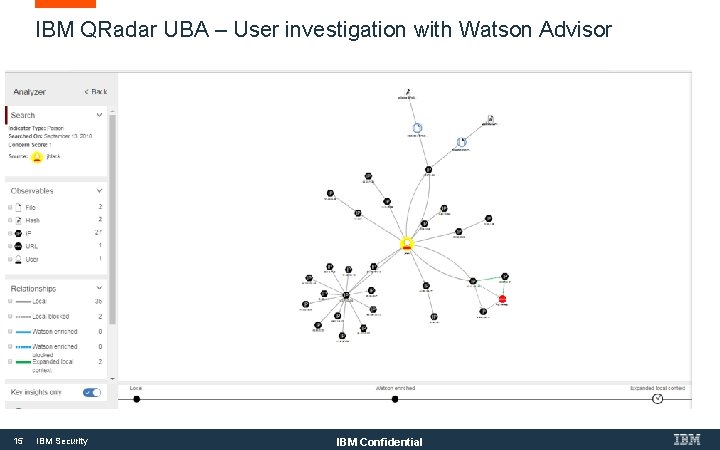
IBM QRadar UBA – User investigation with Watson Advisor 15 IBM Security IBM Confidential
Automate Your SOC with AI QRADAR ADVISOR WITH WATSON Product Marketing, WW Sales, Offering Management October 2018

Challenge #1: Unaddressed threats Endpoints Network activity Data activity Users and identities Threat intelligence Configuration information Vulnerabilities and threats Application activity Cloud platforms 17 IBM Security Insider Threats Information is often overlooked simply because analysts do not know how it is connected External threats Cloud risks Vulnerabilities Critical data
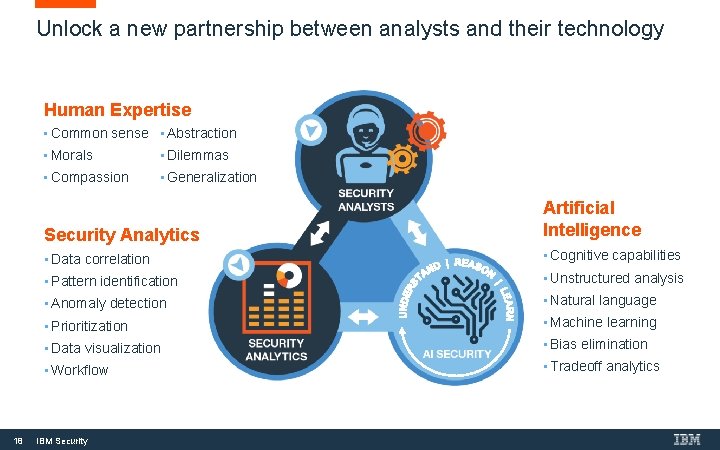
Unlock a new partnership between analysts and their technology Human Expertise • Common sense • Abstraction 18 • Morals • Dilemmas • Compassion • Generalization Security Analytics Artificial Intelligence • Data correlation • Cognitive capabilities • Pattern identification • Unstructured analysis • Anomaly detection • Natural language • Prioritization • Machine learning • Data visualization • Bias elimination • Workflow • Tradeoff analytics IBM Security
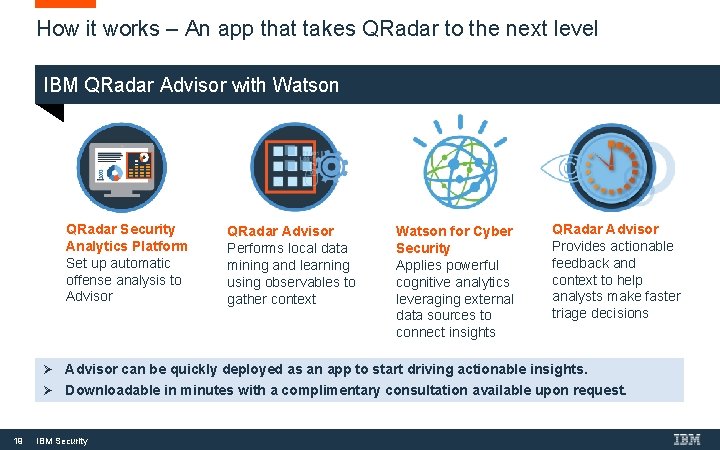
How it works – An app that takes QRadar to the next level IBM QRadar Advisor with Watson QRadar Security Analytics Platform Set up automatic offense analysis to Advisor 19 QRadar Advisor Performs local data mining and learning using observables to gather context Watson for Cyber Security Applies powerful cognitive analytics leveraging external data sources to connect insights QRadar Advisor Provides actionable feedback and context to help analysts make faster triage decisions Ø Advisor can be quickly deployed as an app to start driving actionable insights. Ø Downloadable in minutes with a complimentary consultation available upon request. IBM Security
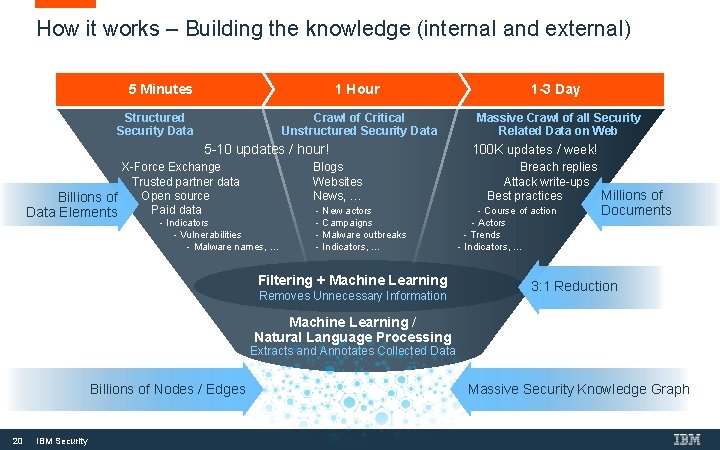
How it works – Building the knowledge (internal and external) 5 Minutes Structured Security Data 1 Hour 1 -3 Day Crawl of Critical Unstructured Security Data Massive Crawl of all Security Related Data on Web 5 -10 updates / hour! X-Force Exchange Trusted partner data Open source Billions of Paid data Data Elements Blogs Websites News, … - Indicators - Vulnerabilities - Malware names, … - New actors - Campaigns - Malware outbreaks - Indicators, … Filtering + Machine Learning Removes Unnecessary Information 100 K updates / week! Breach replies Attack write-ups Best practices Millions of - Course of action - Actors - Trends - Indicators, … Documents 3: 1 Reduction Machine Learning / Natural Language Processing Extracts and Annotates Collected Data Billions of Nodes / Edges 20 IBM Security Massive Security Knowledge Graph
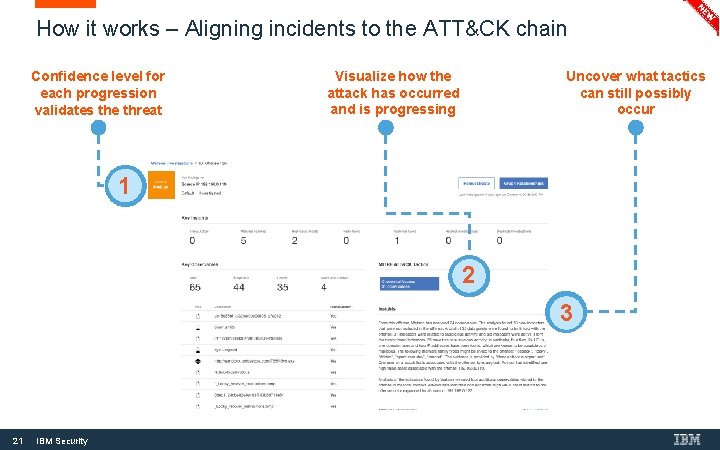
How it works – Aligning incidents to the ATT&CK chain Confidence level for each progression validates the threat Visualize how the attack has occurred and is progressing Uncover what tactics can still possibly occur 1 2 3 21 IBM Security
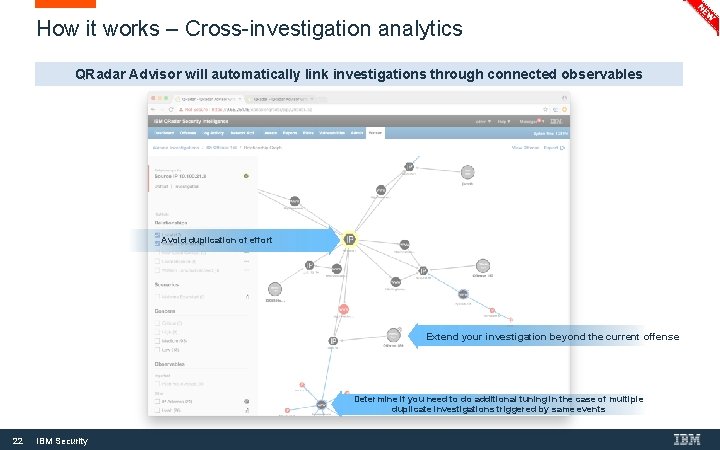
How it works – Cross-investigation analytics QRadar Advisor will automatically link investigations through connected observables Avoid duplication of effort Extend your investigation beyond the current offense Determine if you need to do additional tuning in the case of multiple duplicate investigations triggered by same events 22 IBM Security
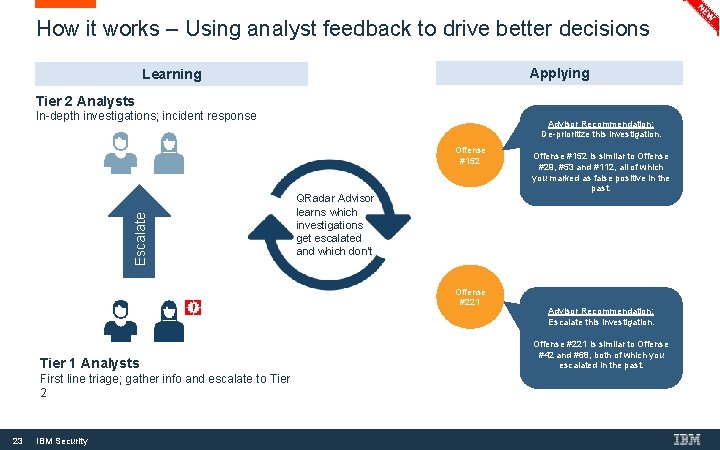
How it works – Using analyst feedback to drive better decisions Applying Learning Tier 2 Analysts In-depth investigations; incident response Advisor Recommendation: De-prioritize this investigation. Escalate Offense #152 QRadar Advisor learns which investigations get escalated and which don’t Offense #221 Tier 1 Analysts First line triage; gather info and escalate to Tier 2 23 IBM Security Offense #152 is similar to Offense #29, #53 and #112, all of which you marked as false positive in the past. Advisor Recommendation: Escalate this investigation. Offense #221 is similar to Offense #42 and #68, both of which you escalated in the past.
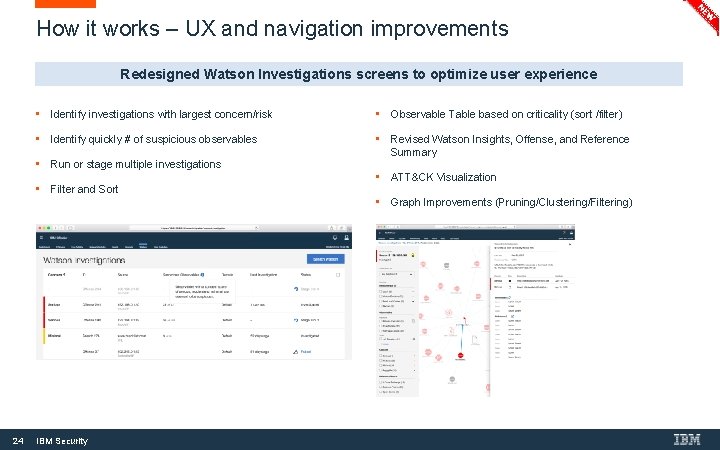
How it works – UX and navigation improvements Redesigned Watson Investigations screens to optimize user experience 24 • Identify investigations with largest concern/risk • Observable Table based on criticality (sort /filter) • Identify quickly # of suspicious observables • • Run or stage multiple investigations Revised Watson Insights, Offense, and Reference Summary • Filter and Sort • ATT&CK Visualization • Graph Improvements (Pruning/Clustering/Filtering) IBM Security
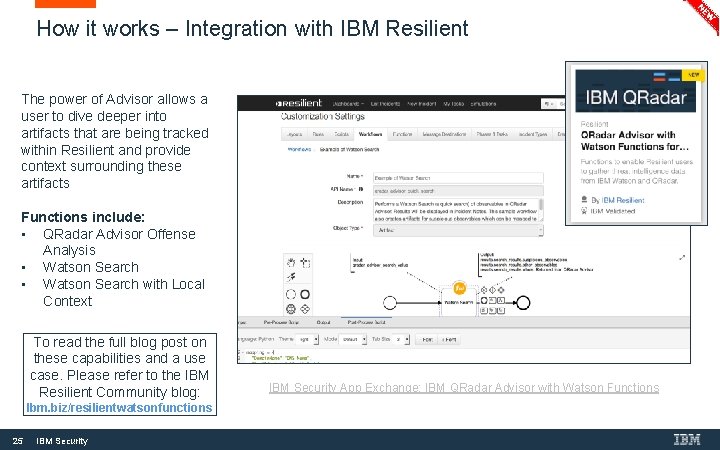
How it works – Integration with IBM Resilient The power of Advisor allows a user to dive deeper into artifacts that are being tracked within Resilient and provide context surrounding these artifacts Functions include: • QRadar Advisor Offense Analysis • Watson Search with Local Context To read the full blog post on these capabilities and a use case. Please refer to the IBM Resilient Community blog: Ibm. biz/resilientwatsonfunctions 25 IBM Security App Exchange: IBM QRadar Advisor with Watson Functions
THANK YOU FOLLOW US ON: ibm. com/securityintelligence. com xforce. ibmcloud. com @ibmsecurity youtube/user/ibmsecuritysolutions © Copyright IBM Corporation 2016. All rights reserved. The information contained in these materials is provided for informational purposes only, and is provided AS IS without warranty of any kind, express or implied. Any statement of direction represents IBM's current intent, is subject to change or withdrawal, and represent only goals and objectives. IBM, the IBM logo, and other IBM products and services are trademarks of the International Business Machines Corporation, in the United States, other countries or both. Other company, product, or service names may be trademarks or service marks of others. Statement of Good Security Practices: IT system security involves protecting systems and information through prevention, detection and response to improper access from within and outside your enterprise. Improper access can result in information being altered, destroyed, misappropriated or misused or can result in damage to or misuse of your systems, including for use in attacks on others. No IT system or product should be considered completely secure and no single product, service or security measure can be completely effective in preventing improper use or access. IBM systems, products and services are designed to be part of a lawful, comprehensive security approach, which will necessarily involve additional operational procedures, and may require other systems, products or services to be most effective. IBM does not warrant that any systems, products or services are immune from, or will make your enterprise immune from, the malicious or illegal conduct of any party.
- Slides: 24