Exploiting Bit Torrent For Fun But Not Profit
Exploiting Bit. Torrent For Fun (But Not Profit) Nikitas Liogkas, Robert Nelson, Eddie Kohler, Lixia Zhang University of California, Los Angeles
Motivation w Robustness: system always provides useful service to all connected peers n n depends on peers’ willingness to contribute but uploading not in peers’ direct self interest w Fairness: those who do not contribute should not be able to receive good service w Can fairness violations reduce robustness?
Selfish peers w Bit. Torrent fairness model n n rules for data exchange between peers “tit-for-tat” for upload decisions w Selfishness: peers violate fairness while evading detection n abuse existing protocol mechanisms is it effective (fairness violation)? impact on honest peers (robustness reduction)?
Contributions w Designed and evaluated three selfish exploits n tools for measuring robustness w Despite selfishness, Bit. Torrent quite robust n n at most 29% higher rates for the selfish peer but no considerable degradation of service w How is this robustness achieved? n n identify responsible protocol mechanisms propose five guiding design principles
Presentation outline w Bit. Torrent operation w Implementation and methodology w Design and evaluation of exploits w Discussion w Conclusions w Future work
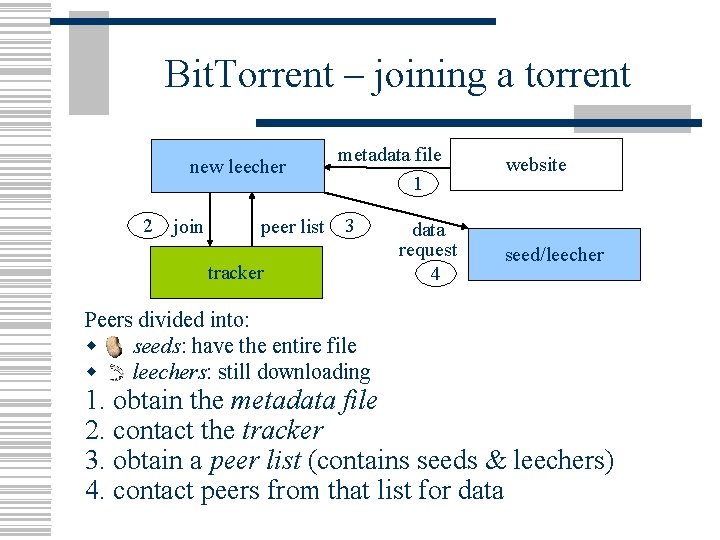
Bit. Torrent – joining a torrent new leecher 2 join peer list metadata file 1 3 tracker data request 4 website seed/leecher Peers divided into: w seeds: have the entire file w leechers: still downloading 1. obtain the metadata file 2. contact the tracker 3. obtain a peer list (contains seeds & leechers) 4. contact peers from that list for data
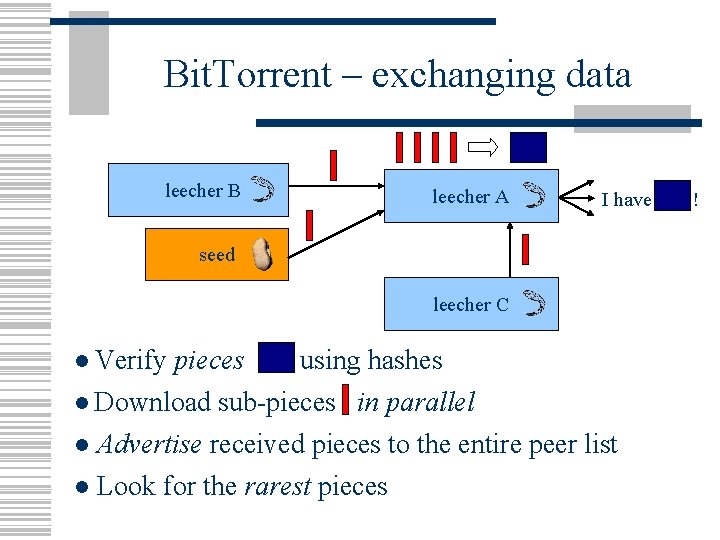
Bit. Torrent – exchanging data leecher B leecher A I have seed leecher C ● Verify pieces using hashes ● Download sub-pieces in parallel ● Advertise received pieces to the entire peer list ● Look for the rarest pieces !
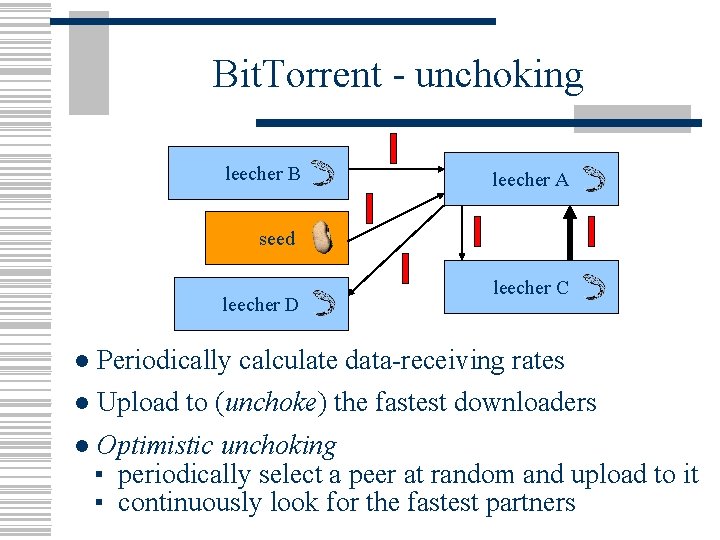
Bit. Torrent - unchoking leecher B leecher A seed leecher D leecher C ● Periodically calculate data-receiving rates ● Upload to (unchoke) the fastest downloaders ● Optimistic unchoking ▪ periodically select a peer at random and upload to it ▪ continuously look for the fastest partners
Presentation outline w Bit. Torrent operation w Implementation and methodology w Design and evaluation of exploits w Discussion w Conclusions w Future work
Implementation w implemented all three exploits in the Ctorrent client w ensured that our changes did not interfere with regular protocol operation w exploits do not exhaust all possible selfish behavior… w but prove to be valuable tools for evaluating robustness
Experimental methodology w Private torrents n eight leechers & one seed on Planetlab l n n n most torrents are small [Guo et al. , IMC’ 05] impose download and upload limits leechers join according to Poisson purpose: measure benefit to selfish (fairness), impact on honest (robustness) w Public torrents n n two clients join the same torrent together purpose: reveal impact in real settings
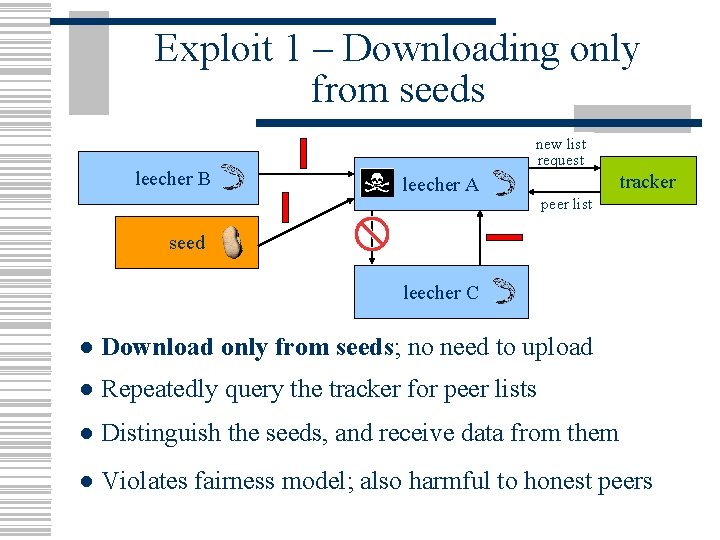
Exploit 1 – Downloading only from seeds leecher B new list request leecher A tracker peer list seed leecher C ● Download only from seeds; no need to upload ● Repeatedly query the tracker for peer lists ● Distinguish the seeds, and receive data from them ● Violates fairness model; also harmful to honest peers
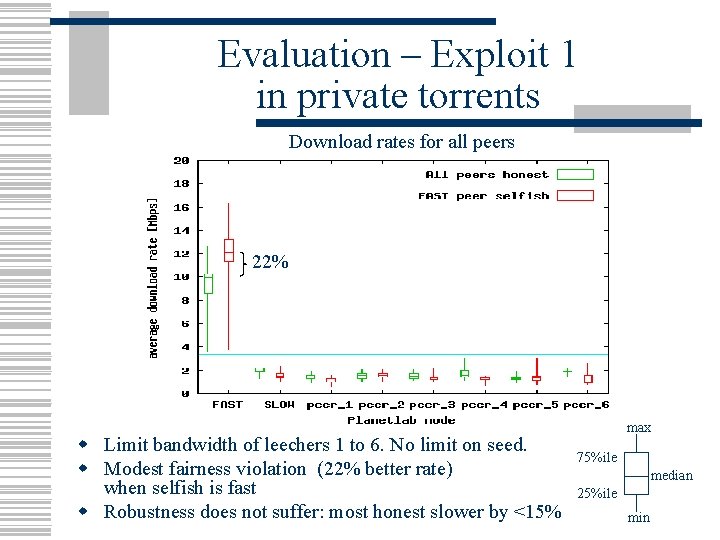
Evaluation – Exploit 1 in private torrents Download rates for all peers 22% w Limit bandwidth of leechers 1 to 6. No limit on seed. w Modest fairness violation (22% better rate) when selfish is fast w Robustness does not suffer: most honest slower by <15% max 75%ile median 25%ile min
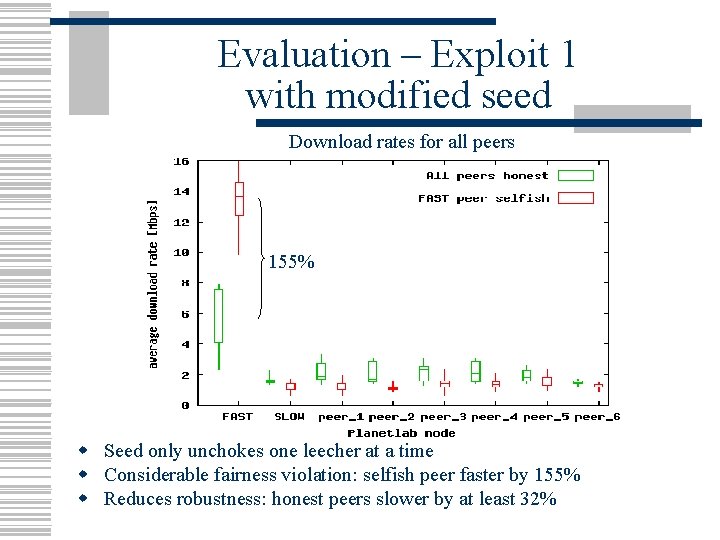
Evaluation – Exploit 1 with modified seed Download rates for all peers 155% w Seed only unchokes one leecher at a time w Considerable fairness violation: selfish peer faster by 155% w Reduces robustness: honest peers slower by at least 32%
Evaluation – Exploit 1 in public torrents w Tested with small (< 20 peers) and large (> 150 peers) torrents w Selfish leecher gets consistently higher download rates (7 -20%) w Does particularly well in torrents with many seeds w Greater incentive to cheat in popular torrents
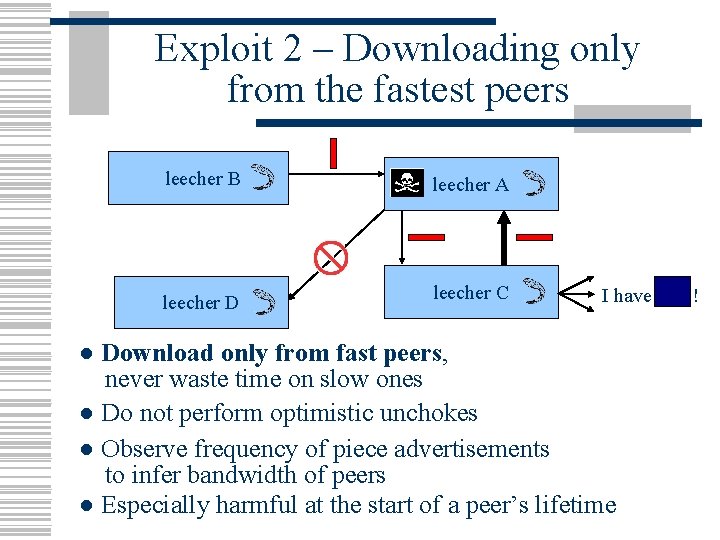
Exploit 2 – Downloading only from the fastest peers leecher B leecher D leecher A leecher C I have ● Download only from fast peers, never waste time on slow ones ● Do not perform optimistic unchokes ● Observe frequency of piece advertisements to infer bandwidth of peers ● Especially harmful at the start of a peer’s lifetime !
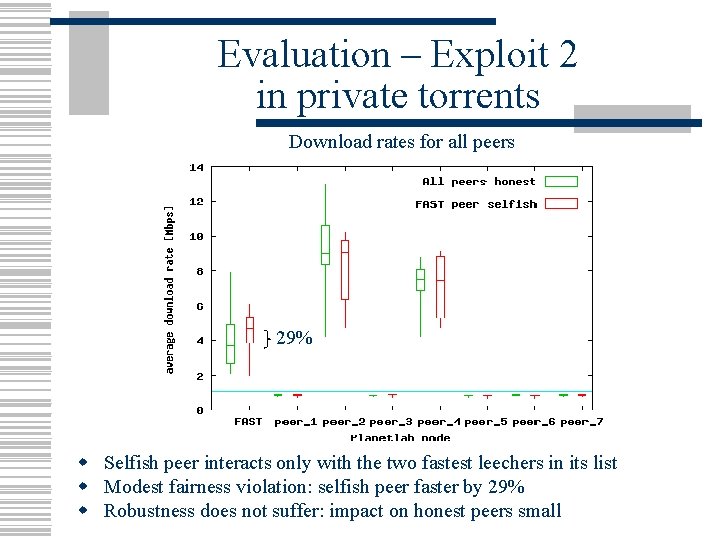
Evaluation – Exploit 2 in private torrents Download rates for all peers 29% w Selfish peer interacts only with the two fastest leechers in its list w Modest fairness violation: selfish peer faster by 29% w Robustness does not suffer: impact on honest peers small
Evaluation – Exploit 2 in public torrents w Exploit fails in public torrents n consistently lower download rates (1 -30%) w Reasons n n optimistic unchoking aids in discovering the best partners short-term calculations beat our advertisement-based estimations w Mechanism for continuous adaptation is valuable
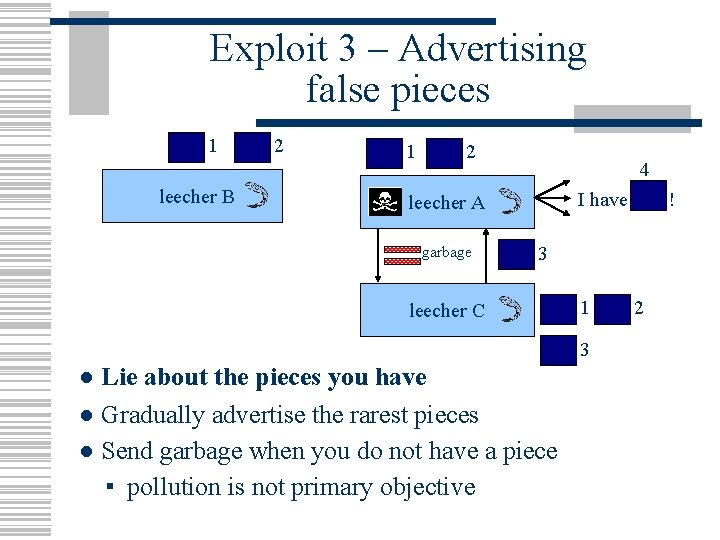
Exploit 3 – Advertising false pieces 1 leecher B 2 1 2 4 I have leecher A garbage ! 3 leecher C 1 3 ● Lie about the pieces you have ● Gradually advertise the rarest pieces ● Send garbage when you do not have a piece ▪ pollution is not primary objective 2
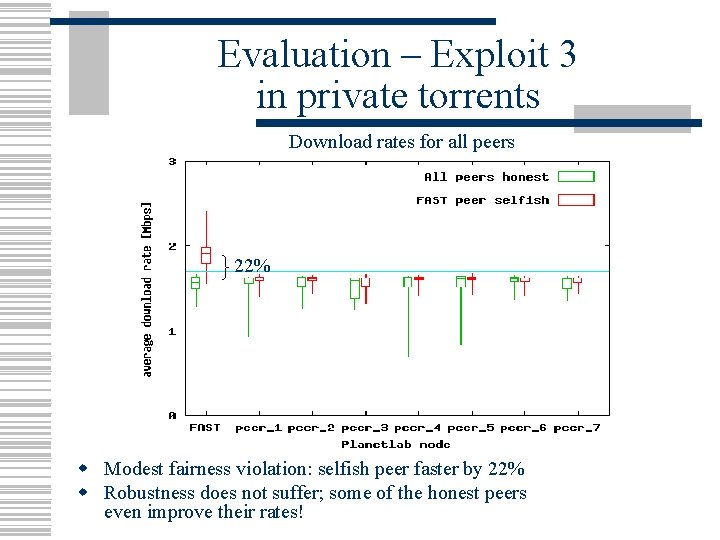
Evaluation – Exploit 3 in private torrents Download rates for all peers 22% w Modest fairness violation: selfish peer faster by 22% w Robustness does not suffer; some of the honest peers even improve their rates!
Evaluation – Exploit 3 in public torrents w Exploit fails in public torrents n n modern implementations keep state about the origin of pieces lying leechers easily detected w Remembering past interactions enables defending against false piece advertisements
Presentation outline w Bit. Torrent operation w Implementation and methodology w Design and evaluation of exploits w Discussion w Conclusions w Future work
Design principles w Parallel downloading w Memory of past interactions w Problem partitioning w Export minimal information w Keep the network connected
Principles #1 and #2 w Maintain parallel interactions with multiple peers n example: limited impact of the downloadonly-from-seeds exploit w Maintain memory of past interactions n n example: failure of the false-advertisements exploit in public torrents trade-off between robustness and performance
![Principle #3 w Enforce problem partitioning [Shneidman et al. , PODC’ 04] n n Principle #3 w Enforce problem partitioning [Shneidman et al. , PODC’ 04] n n](http://slidetodoc.com/presentation_image_h/cde39f2ea26e7b60b98c5fe65fa69ed3/image-25.jpg)
Principle #3 w Enforce problem partitioning [Shneidman et al. , PODC’ 04] n n “No peer should be able to influence another peer’s decision-making by declaring false information” Not enforced by Bit. Torrent Should decouple data needs (pieces) from the provided service (unchoking) Could harm performance
Principles #4 and #5 w Export minimal information necessary n n example: hide that you are a seed super-seeding policy does just that w Keep the network connected n n optimistic unchoking: random choice that aids robustness value evident in the failure of the downloadfrom-the fastest exploit in public torrents
![Related work w Describes the basic Bit. Torrent mechanisms [Cohen, P 2 PECON’ 03] Related work w Describes the basic Bit. Torrent mechanisms [Cohen, P 2 PECON’ 03]](http://slidetodoc.com/presentation_image_h/cde39f2ea26e7b60b98c5fe65fa69ed3/image-27.jpg)
Related work w Describes the basic Bit. Torrent mechanisms [Cohen, P 2 PECON’ 03] w Feasibility of selfish behavior in Bit. Torrent [Shneidman et al. , PINS’ 04] w Theoretical analysis [Qiu et al. , SIGCOMM’ 04] w Simulations [Bharambe et al. , MSR-TR-2005] w Measurement studies [Izal et al. , PAM’ 04, Pouwelse et al. , Delft TR 2004 and IPTPS’ 05, Guo et al. , IMC’ 05]
Conclusions w Presented three selfish exploits w Bit. Torrent quite robust, despite fairness violations w Identified protocol characteristics that enable robustness w Proposed five guiding design principles
Future work w Investigate combinations of exploits w Our exploits do not exhaust the complete space of selfish behavior n how to methodically design other (possibly more successful) exploits? w Selfish behavior in multi-torrent systems
Exploiting Bit. Torrent For Fun (But Not Profit) Nikitas Liogkas, Robert Nelson, Eddie Kohler, Lixia Zhang Questions?
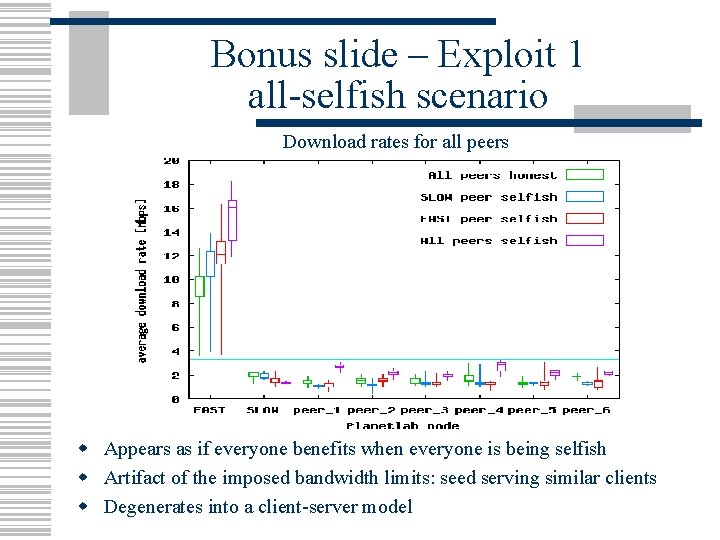
Bonus slide – Exploit 1 all-selfish scenario Download rates for all peers w Appears as if everyone benefits when everyone is being selfish w Artifact of the imposed bandwidth limits: seed serving similar clients w Degenerates into a client-server model
- Slides: 31