Bot Torrent Misusing Bit Torrent to Launch DDo

Bot. Torrent: Misusing Bit. Torrent to Launch DDo. S Attacks Karim El Defrawy, Minas Gjoka, Athina Markopoulou UC Irvine
Outline Introduction o How Bit. Torrent works o Using Bit. Torrent to launch DDo. S attacks o Experiment details and results o Can we fix Bit. Torrent to prevent such attacks? o Summary o
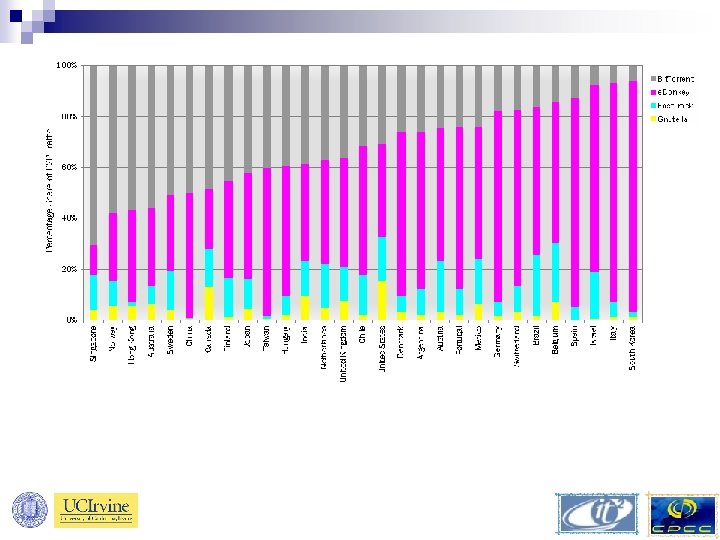
Introduction o In 2006, 60% of Internet traffic was due to peer-to-peer (P 2 P) protocols (Cache Logic) o Bit. Torrent is more than 35% by end of 2006 (Cache Logic) o Mininova torrent search engine hit 2 billion downloads (Mininova - June 13 th 2007)
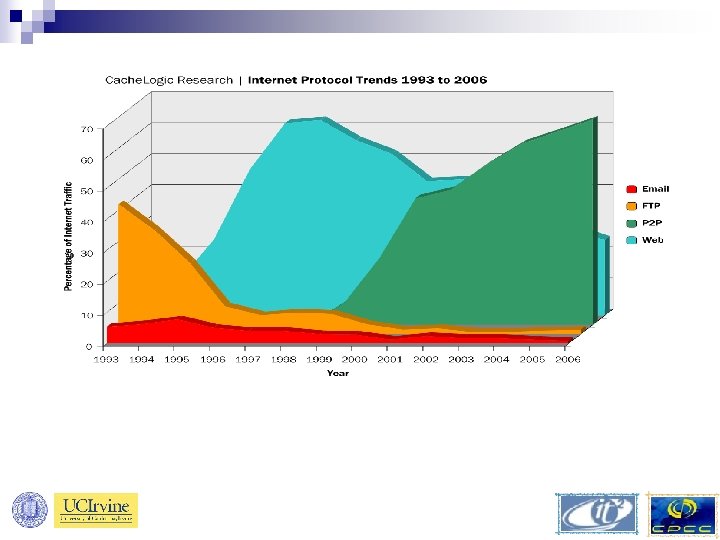
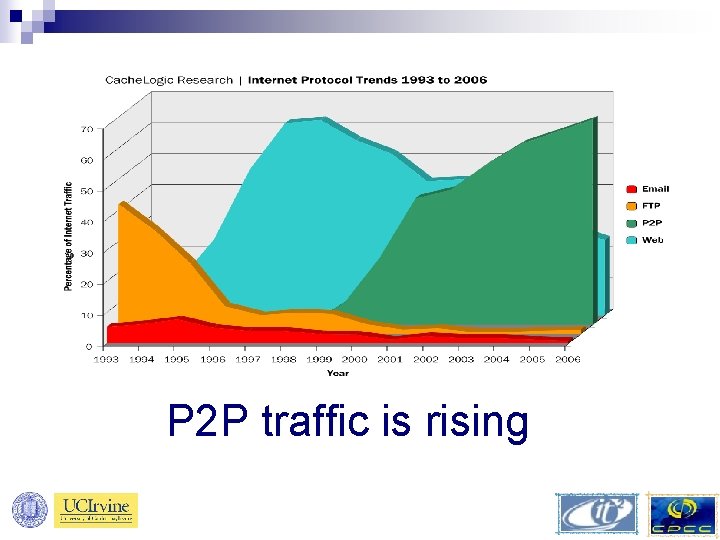
P 2 P traffic is rising
Bit. Torrent is responsible for a significant amount of P 2 P traffic
P 2 P based DDo. S attacks recently observed o announced on May 14 th 2007 observing an increase in P 2 P based DDo. S attacks o Attack based on the direct connect (DC) P 2 P system o Attack involved over 300 000 IPs o http: //www. prolexic. com/news/20070514 -alert. php
P 2 P based DDo. S attacks recently observed o announced on May 14 th 2007 observing an increase in P 2 P based DDo. S attacks o Attack based on the direct connect (DC) P 2 P system o Attack involved over 300 000 IPs o http: //www. prolexic. com/news/20070514 -alert. php P 2 P DDo. S is already happening !
Outline Introduction o How Bit. Torrent works o Using Bit. Torrent to launch DDo. S attacks o Experiment details and results o Can we fix Bit. Torrent to prevent such attacks? o Summary o
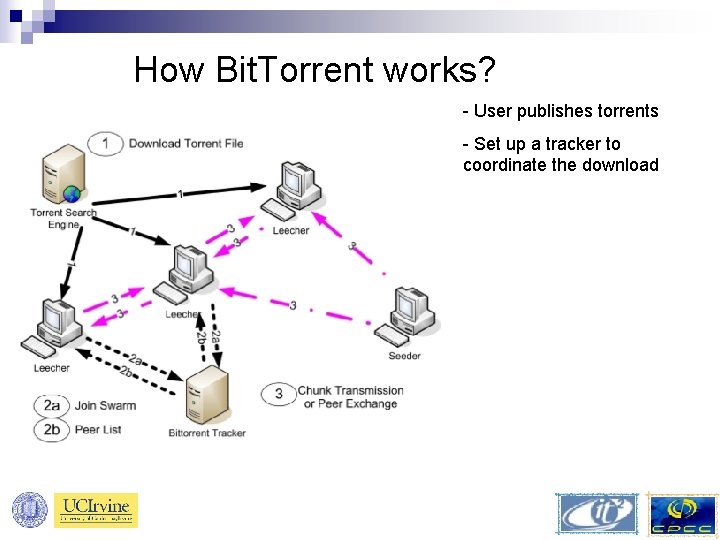
How Bit. Torrent works? - User publishes torrents - Set up a tracker to coordinate the download
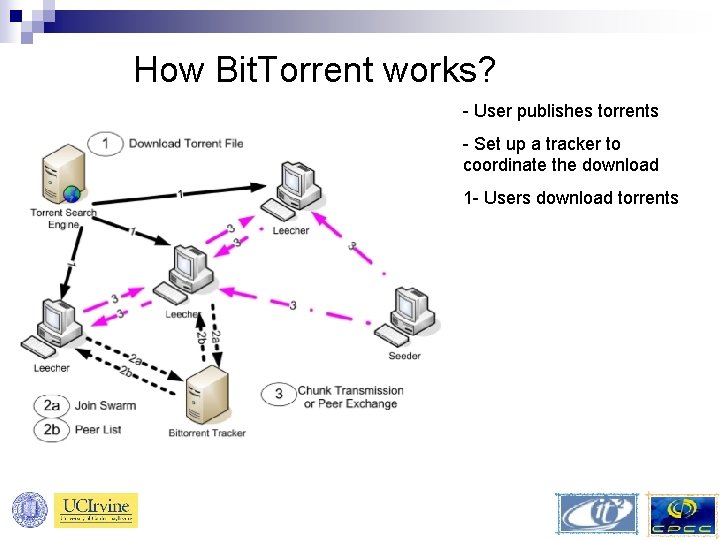
How Bit. Torrent works? - User publishes torrents - Set up a tracker to coordinate the download 1 - Users download torrents
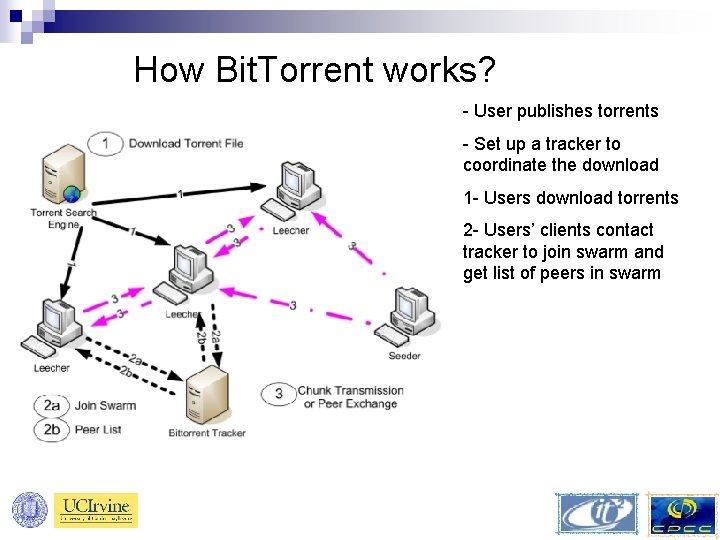
How Bit. Torrent works? - User publishes torrents - Set up a tracker to coordinate the download 1 - Users download torrents 2 - Users’ clients contact tracker to join swarm and get list of peers in swarm
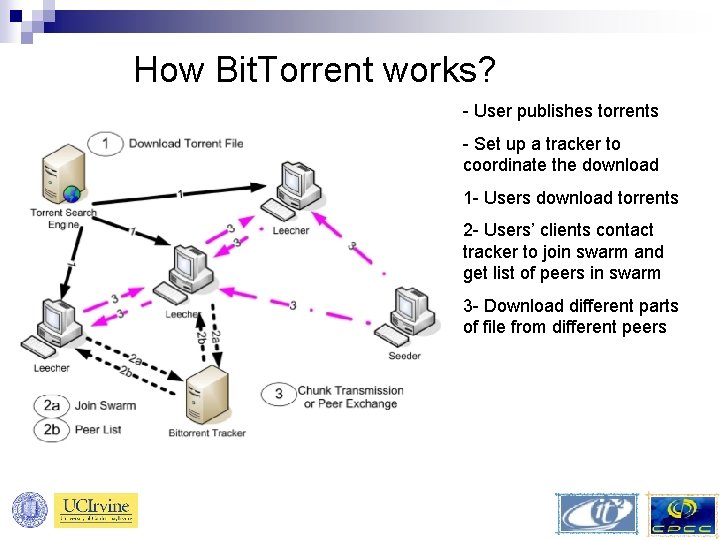
How Bit. Torrent works? - User publishes torrents - Set up a tracker to coordinate the download 1 - Users download torrents 2 - Users’ clients contact tracker to join swarm and get list of peers in swarm 3 - Download different parts of file from different peers
Outline Introduction o How Bit. Torrent works o Using Bit. Torrent to launch DDo. S attacks o Experiment details and results o Can we fix Bit. Torrent to prevent such attacks? o Summary o
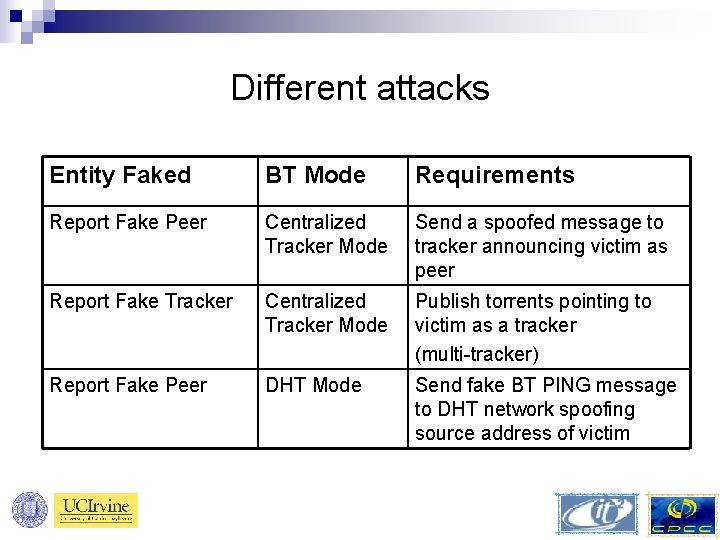
Different attacks Entity Faked BT Mode Requirements Report Fake Peer Centralized Tracker Mode Send a spoofed message to tracker announcing victim as peer Report Fake Tracker Centralized Tracker Mode Publish torrents pointing to victim as a tracker (multi-tracker) Report Fake Peer DHT Mode Send fake BT PING message to DHT network spoofing source address of victim
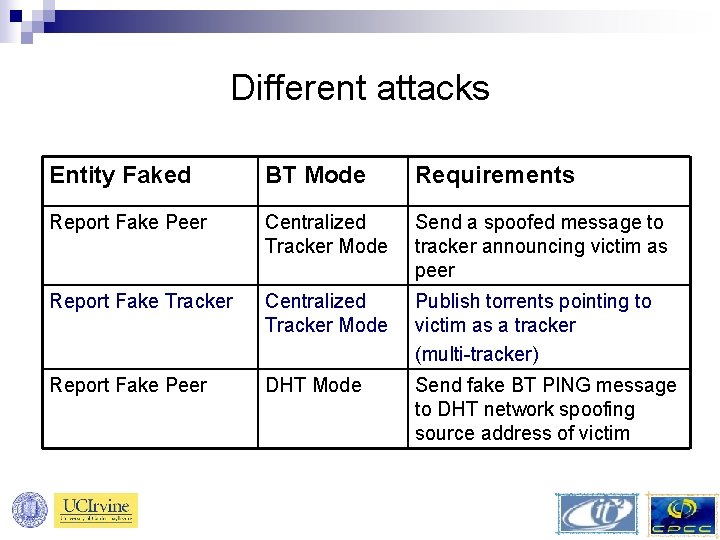
Different attacks Entity Faked BT Mode Requirements Report Fake Peer Centralized Tracker Mode Send a spoofed message to tracker announcing victim as peer Report Fake Tracker Centralized Tracker Mode Publish torrents pointing to victim as a tracker (multi-tracker) Report Fake Peer DHT Mode Send fake BT PING message to DHT network spoofing source address of victim
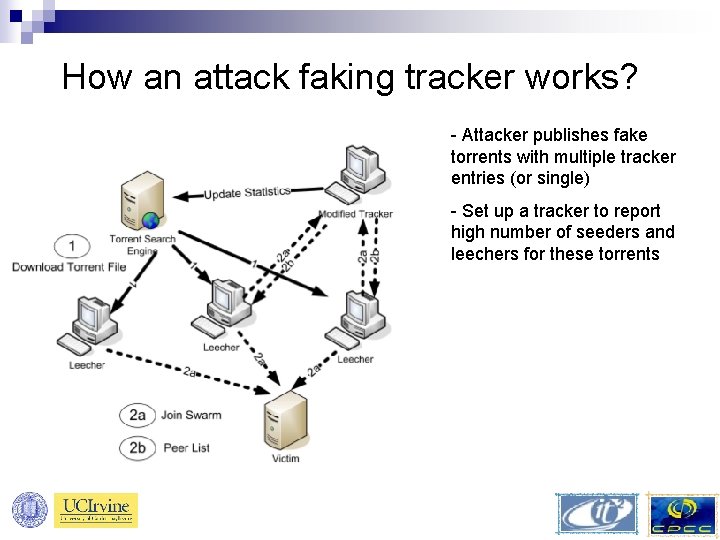
How an attack faking tracker works? - Attacker publishes fake torrents with multiple tracker entries (or single) - Set up a tracker to report high number of seeders and leechers for these torrents
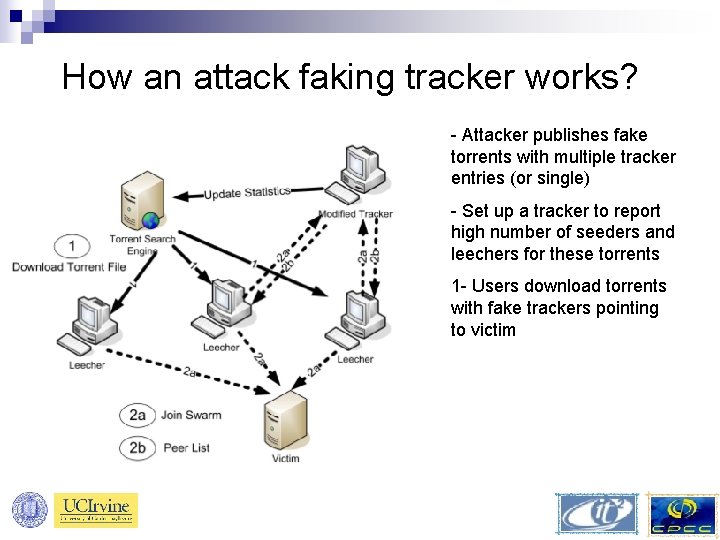
How an attack faking tracker works? - Attacker publishes fake torrents with multiple tracker entries (or single) - Set up a tracker to report high number of seeders and leechers for these torrents 1 - Users download torrents with fake trackers pointing to victim
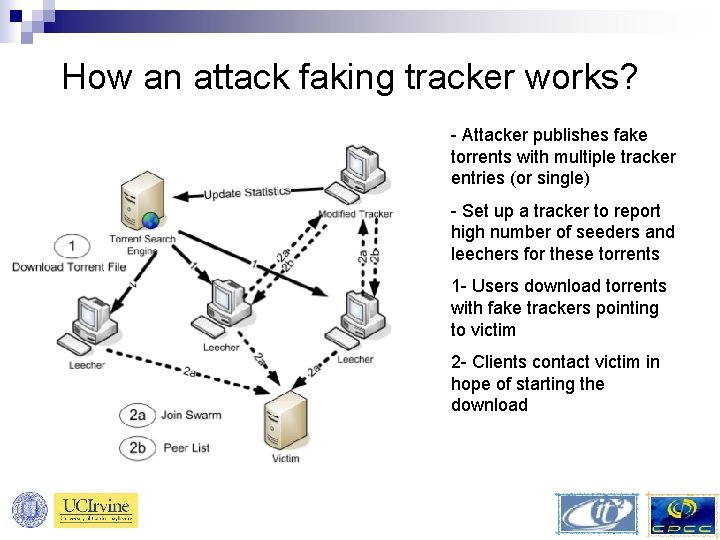
How an attack faking tracker works? - Attacker publishes fake torrents with multiple tracker entries (or single) - Set up a tracker to report high number of seeders and leechers for these torrents 1 - Users download torrents with fake trackers pointing to victim 2 - Clients contact victim in hope of starting the download
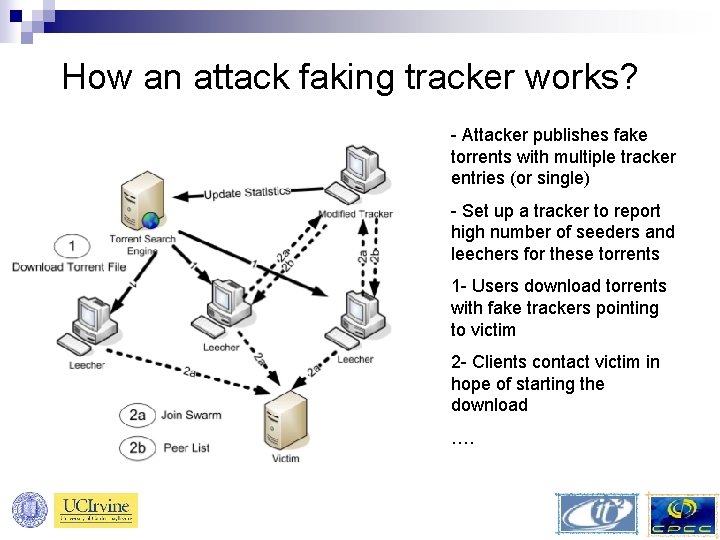
How an attack faking tracker works? - Attacker publishes fake torrents with multiple tracker entries (or single) - Set up a tracker to report high number of seeders and leechers for these torrents 1 - Users download torrents with fake trackers pointing to victim 2 - Clients contact victim in hope of starting the download ….
Outline Introduction o How Bit. Torrent works o Using Bit. Torrent to launch DDo. S attacks o Experiment details and results o Can we fix Bit. Torrent to prevent such attacks? o Summary o
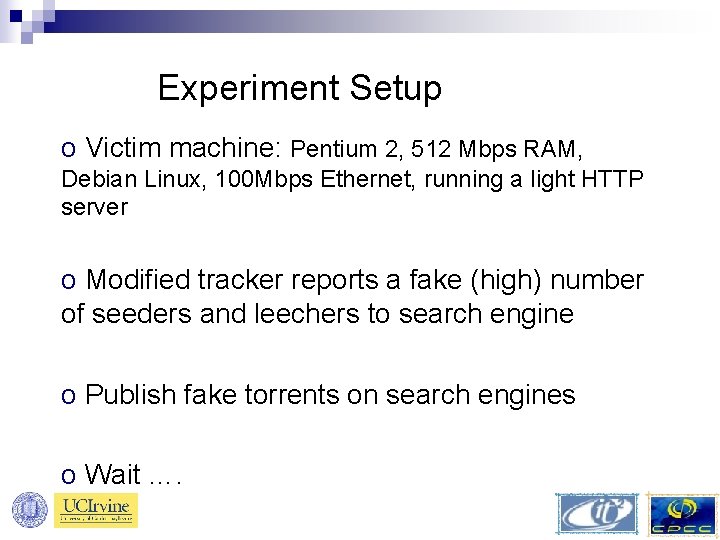
Experiment Setup o Victim machine: Pentium 2, 512 Mbps RAM, Debian Linux, 100 Mbps Ethernet, running a light HTTP server o Modified tracker reports a fake (high) number of seeders and leechers to search engine o Publish fake torrents on search engines o Wait ….
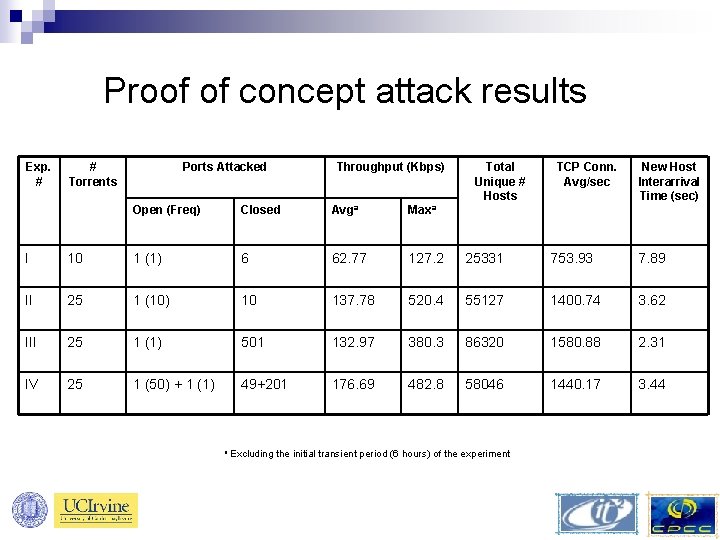
Proof of concept attack results Exp. # # Torrents Ports Attacked Throughput (Kbps) Open (Freq) Closed Avga Maxa Total Unique # Hosts TCP Conn. Avg/sec New Host Interarrival Time (sec) I 10 1 (1) 6 62. 77 127. 2 25331 753. 93 7. 89 II 25 1 (10) 10 137. 78 520. 4 55127 1400. 74 3. 62 III 25 1 (1) 501 132. 97 380. 3 86320 1580. 88 2. 31 IV 25 1 (50) + 1 (1) 49+201 176. 69 482. 8 58046 1440. 17 3. 44 a Excluding the initial transient period (6 hours) of the experiment
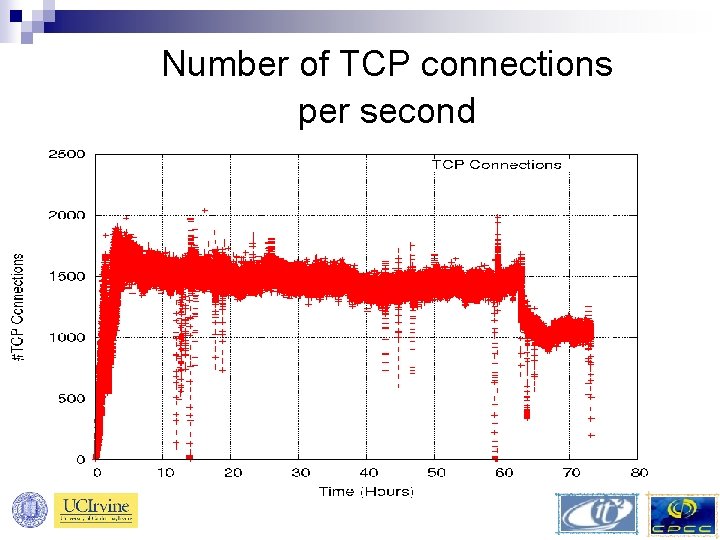
Number of TCP connections per second
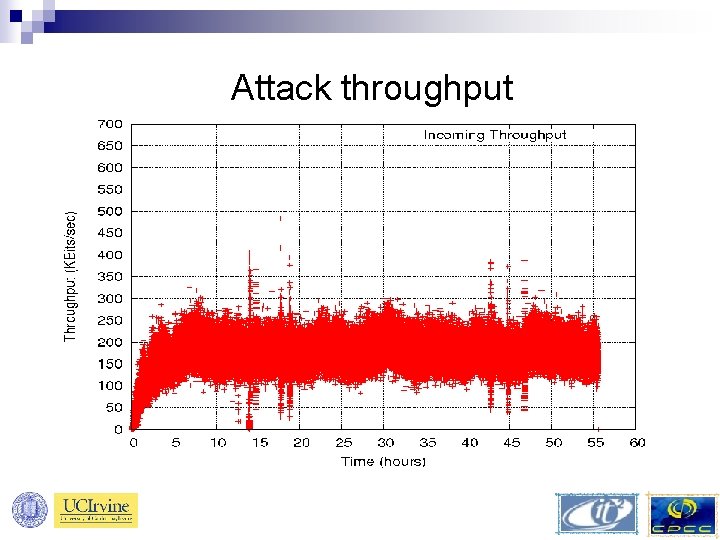
Attack throughput
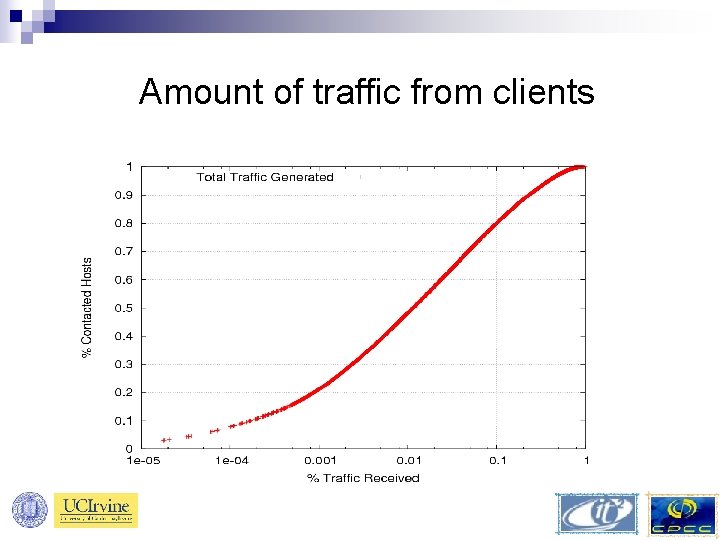
Amount of traffic from clients
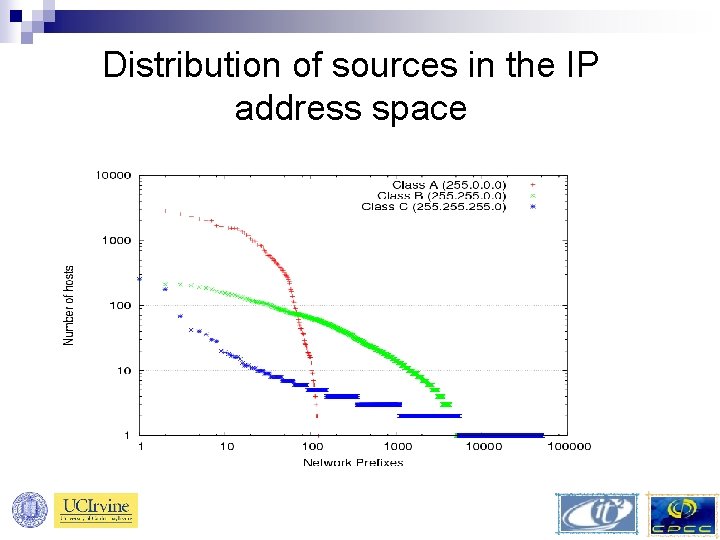
Distribution of sources in the IP address space
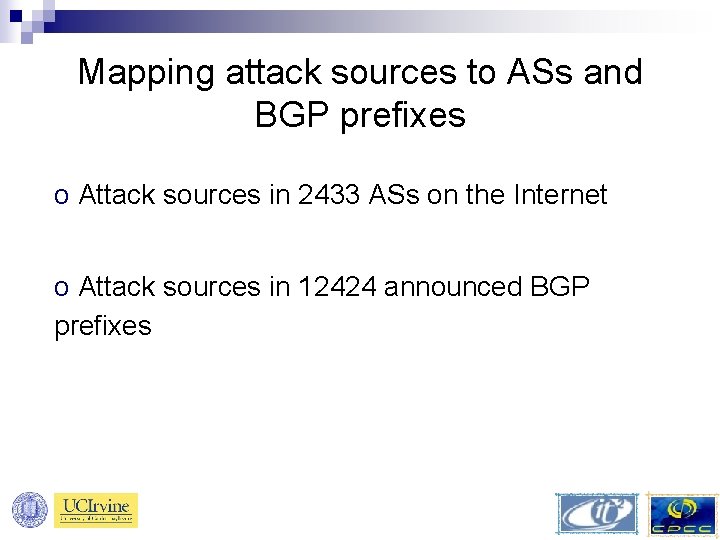
Mapping attack sources to ASs and BGP prefixes o Attack sources in 2433 ASs on the Internet o Attack sources in 12424 announced BGP prefixes
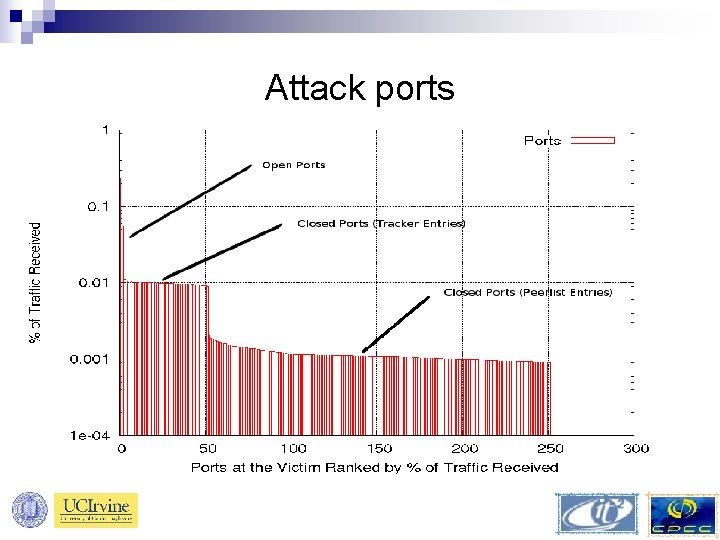
Attack ports
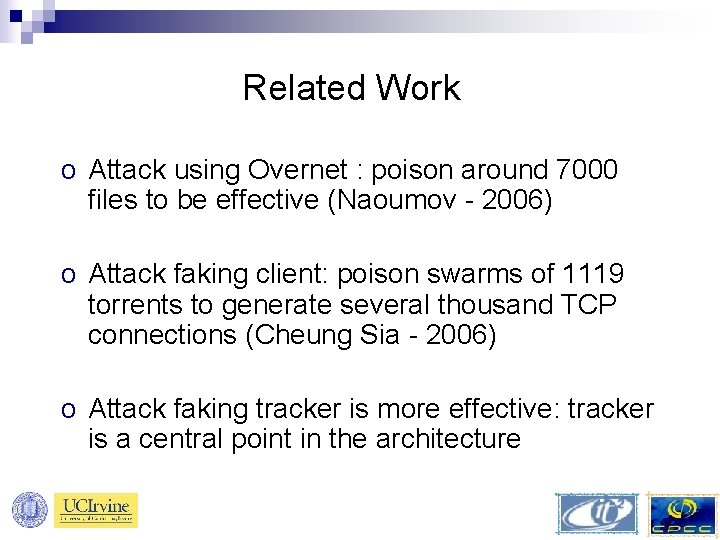
Related Work o Attack using Overnet : poison around 7000 files to be effective (Naoumov - 2006) o Attack faking client: poison swarms of 1119 torrents to generate several thousand TCP connections (Cheung Sia - 2006) o Attack faking tracker is more effective: tracker is a central point in the architecture
Outline Introduction o How Bit. Torrent works o Using Bit. Torrent to launch DDo. S attacks o Experiment details and results o Can we fix Bit. Torrent to prevent such attacks? o Summary o
Reporting the problem We contacted: o Bit. Torrent and Bram Cohen o Search Engines: Mininova, Pirate Bay, Bit. Torrent Monster o Clients developers: Azureus, Bitcomet o Prolexic o Response from Azureus developers only
Solutions o Handshake between clients and trackers similar to the one between clients. o Clients exchange view of trackers similar to exchanging view of peers. o Mechanism to identify and trace the seeders of the fake torrents (based on hashes).
Outline Introduction o How Bit. Torrent works o Using Bit. Torrent to launch DDo. S attacks o Experiment details and results o Can we fix Bit. Torrent to prevent such attacks? o Summary o
Summary o Presented misusing Bit. Torrent to launch DDo. S attacks o Proof of concept attack implementation o Analyzed characteristics of the attack o Proposed fixes to Bit. Torrent to detect and prevent such attacks o Currently implementing fixes
Questions ?

Thank you! keldefra@uci. edu mgjoka@uci. edu athina@uci. edu
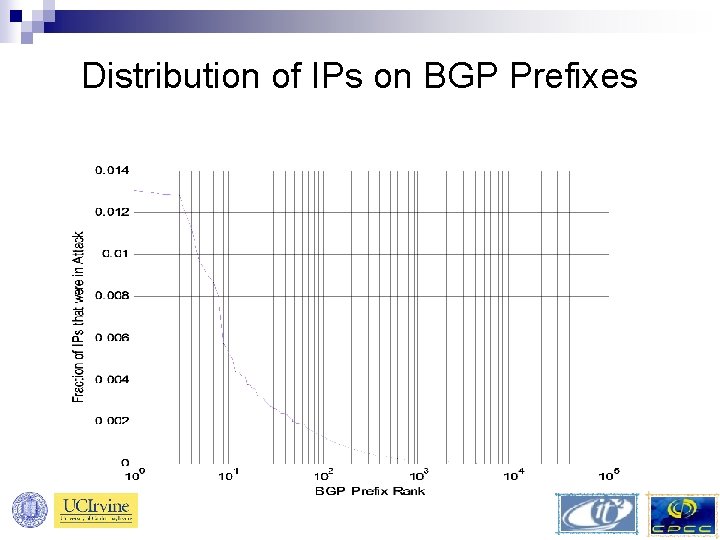
Distribution of IPs on BGP Prefixes
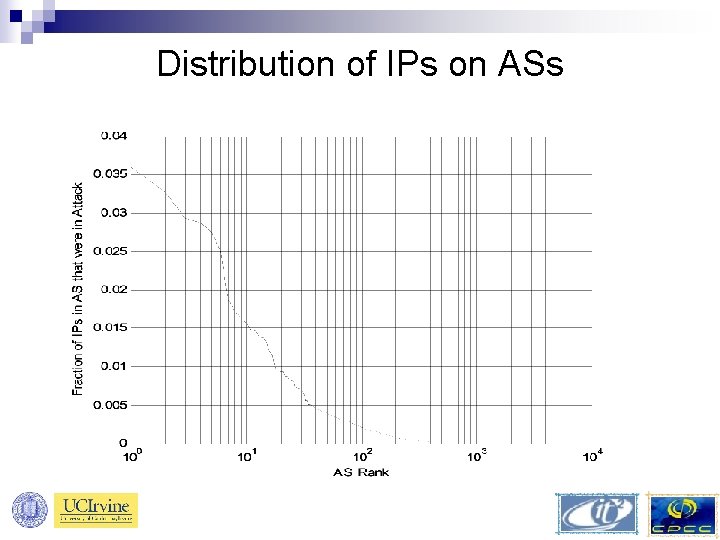
Distribution of IPs on ASs
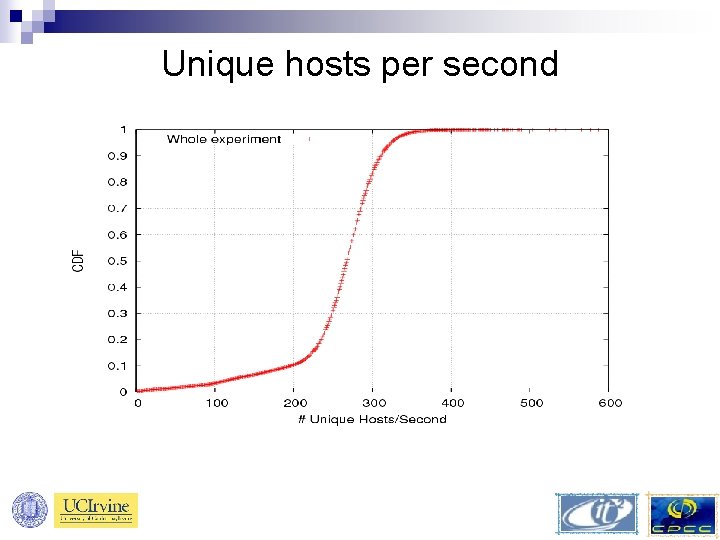
Unique hosts per second
- Slides: 41