28022008 MAESTROPLANETE INFORMEL SEMINARY Bit Hoc Bit Torrent
28/02/2008 MAESTRO/PLANETE INFORMEL SEMINARY Bit. Hoc: Bit. Torrent for wireless ad hoc networks Mohamed Karim Sbaï Jointly with: Chadi Barakat Jayeoung Choi Anwar Al Hamra Thierry Turletti EPI PLANETE 1
Wireless ad hoc networks n n No central administration No base station Nodes are both hosts and routers Need for multi-hop routing approaches The connectivity is ensured thanks to the collaboration of nodes in forwarding and routing messages of each others It is the P 2 P paradigm in the network layer. 2
P 2 P file sharing applications n n No central server Users are both clients and servers : They download content and share some of their upload capacity to serve other users. The global capacity of the system grows thanks to their collaboration. This is the P 2 P paradigm in the overlay. 3
P 2 P file sharing in wireless ad hoc networks : constraints n n n Routing overhead Transport protocols performance drops seriously in wireless multi-hop paths P 2 P file sharing solutions are topology unaware : Overlay neighbors are selected independently of their locations. How will such applications perform in wireless ad hoc networks ? What are the modifications (namely in overlay construction) to be made to ameliorate both download time and sharing ratios ? 4
Outline n n n n Overview of Bit. Torrent Framework, scenario and assumptions Performance metrics Impact of the size of pieces Impact of the scope of the neighborhood Bit. Hoc: Our solution ¡ Choking algorithm ¡ Piece selection strategy ¡ Some first results ¡ Choice of parameters and new results. Conclusions and future work 5
Outline n n n n Overview of Bit. Torrent Framework, scenario and assumptions Performance metrics Impact of the size of pieces Impact of the scope of the neighborhood Bit. Hoc: Our solution ¡ Choking algorithm ¡ Piece selection strategy ¡ Some first results ¡ Choice of parameters and new results. Conclusions and future work 6
Bit. Torrent (1/2) n n n a P 2 P efficient content distribution protocol Peer lookup: ¡ A Client contacts a central rendezvous node named Tracker to get addresses of other clients Sharing content: ¡ A file is cut into pieces (multi-sourcing) ¡ Each client shares some of its upload bandwidth with other clients ¡ Torrent : peers cooperating to download the same content ¡ Seed : a peer who finished downloading the content and still serving other peers ¡ leecher : peer who is downloading the file 7
Bit. Torrent (2/2) ¡ Choking algorithm: A peer chooses periodically a set of peers with whom it opens TCP connections to upload pieces. Only 4 simultaneous connections: 3 best uploaders + 1 a random peer (discovering new upload capacities ) Enforce cooperation and reciprocity among peers ¡ Piece selection strategy: When a peer receives a piece offer message from a neighbor, it selects the rarest piece in the peer list. This increases the entropy of pieces in the network and then the chance to replicate pieces after downloading them. 8
Outline n n n n Overview of Bit. Torrent Framework, scenario and assumptions Performance metrics Impact of the size of pieces Impact of the scope of the neighborhood Bit. Hoc: Our solution ¡ Choking algorithm ¡ Piece selection strategy ¡ Some first results ¡ Choice of parameters and new results. Conclusions and future work 9
Framework, scenario and assumptions Assumptions n n n All nodes are peers No mobility in the network Trackerless Bit. Torrent : a flooding of HELLO messages to discover all peers in the network. Framework n We added a module to NS-2 implementing Bit. Torrent functionalities. 10
Framework, scenario and assumptions Ad hoc scenario n n n A grid topology of N nodes (10 per row) (distance = 40 m between nodes) No mobility of nodes DSDV proactive routing protocol 802. 11 MAC Layer with RTS/CTSDATA/ACK Data rate = 1 MB/s, range = 50 m Bit. Torrent Scenario n n n 1 file = 10 Mbit 1 original seed Choking period = 40 s Flooding TTL = variable Number of pieces = variable, number of blocks = variable Block size = 1 KB 11
Outline n n n n Overview of Bit. Torrent Framework, scenario and assumptions Performance metrics Impact of the size of pieces Impact of the scope of the neighborhood Bit. Hoc: Our solution ¡ Choking algorithm ¡ Piece selection strategy ¡ Some first results ¡ Choice of parameters and new results. Conclusions and future work 12
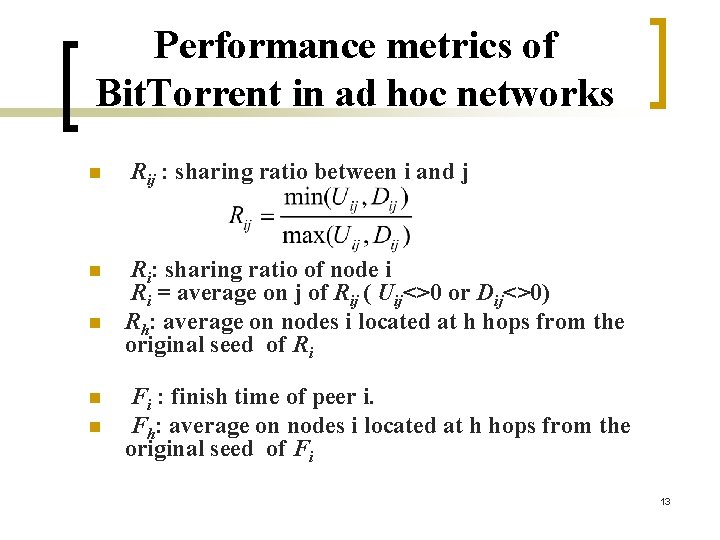
Performance metrics of Bit. Torrent in ad hoc networks n n n Rij : sharing ratio between i and j Ri: sharing ratio of node i Ri = average on j of Rij ( Uij<>0 or Dij<>0) Rh: average on nodes i located at h hops from the original seed of Ri Fi : finish time of peer i. Fh: average on nodes i located at h hops from the original seed of Fi 13
Outline n n n n Overview of Bit. Torrent Performance metrics Framework, scenario and assumptions Impact of the size of pieces Impact of the scope of the neighborhood Bit. Hoc: Our solution ¡ Choking algorithm ¡ Piece selection strategy ¡ Some first results ¡ Choice of parameters and new results. Conclusions and future work 14
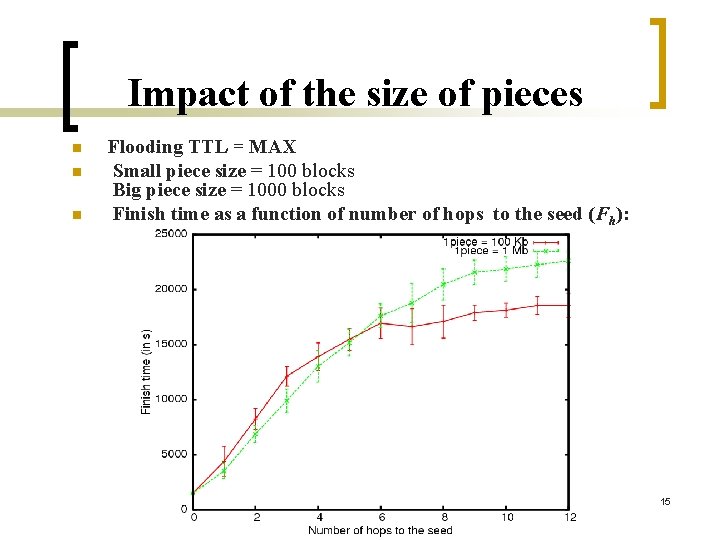
Impact of the size of pieces n n n Flooding TTL = MAX Small piece size = 100 blocks Big piece size = 1000 blocks Finish time as a function of number of hops to the seed (Fh): 15
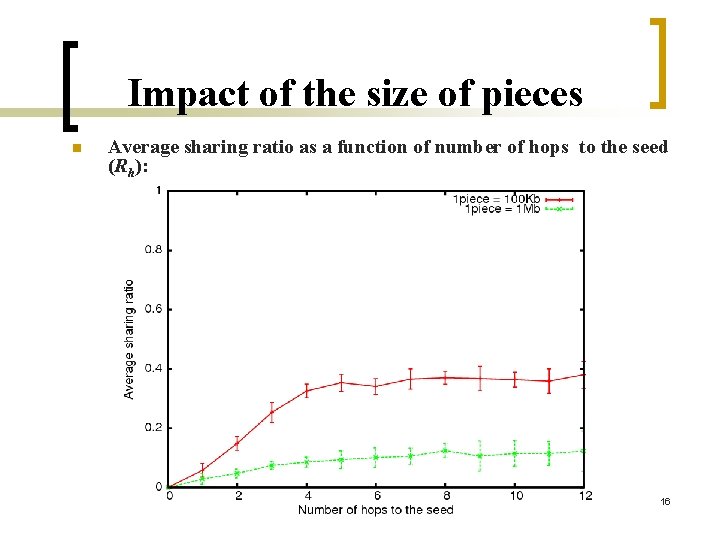
Impact of the size of pieces n Average sharing ratio as a function of number of hops to the seed (Rh): 16
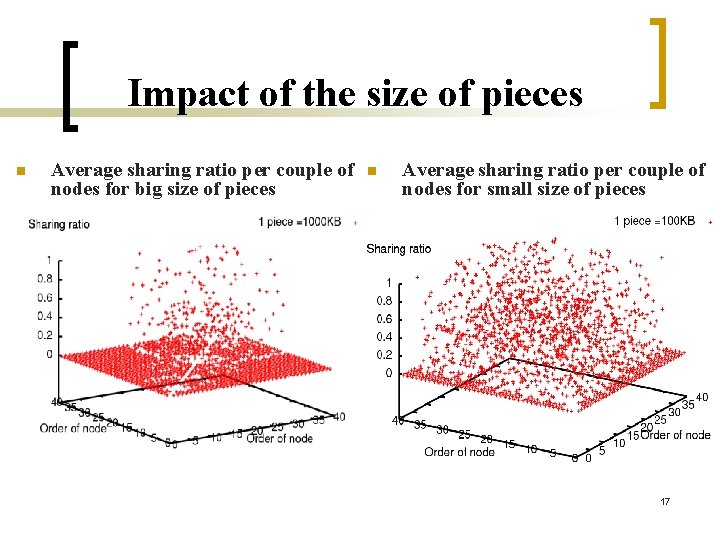
Impact of the size of pieces n Average sharing ratio per couple of nodes for big size of pieces n Average sharing ratio per couple of nodes for small size of pieces 17
Outline n n n n Overview of Bit. Torrent Framework, scenario and assumptions Performance metrics Impact of the size of pieces Impact of the scope of the neighborhood Bit. Hoc: Our solution ¡ Choking algorithm ¡ Piece selection strategy ¡ Some first results ¡ Choice of parameters and new results. Conclusions and future work 18
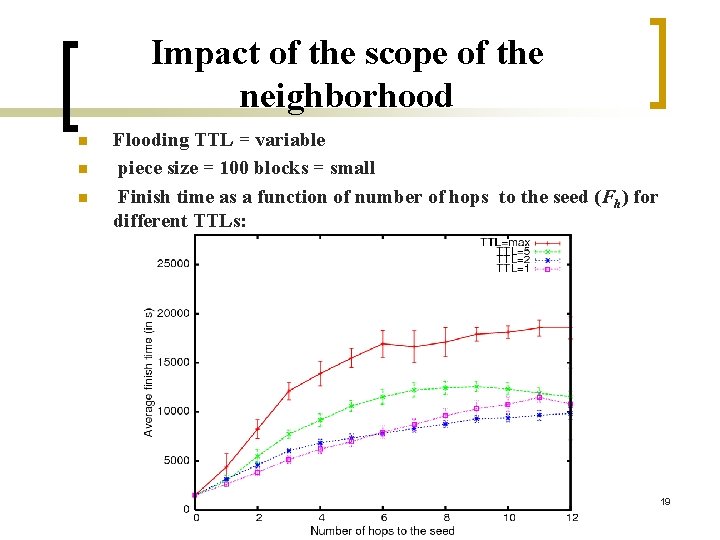
Impact of the scope of the neighborhood n n n Flooding TTL = variable piece size = 100 blocks = small Finish time as a function of number of hops to the seed (Fh) for different TTLs: 19
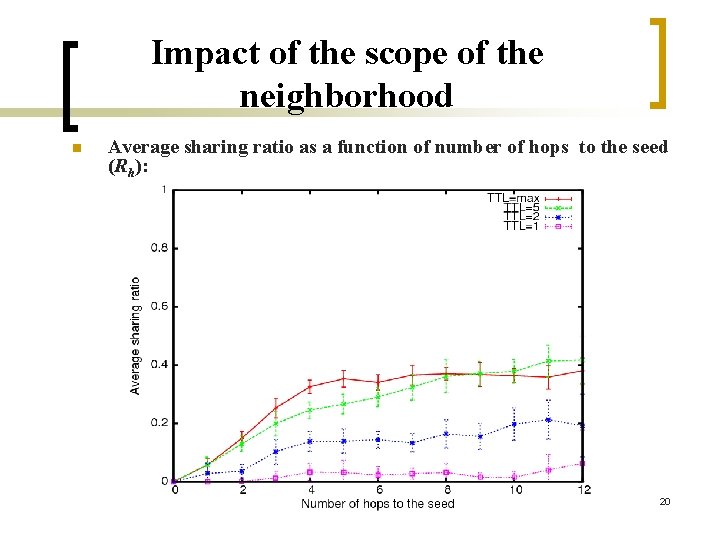
Impact of the scope of the neighborhood n Average sharing ratio as a function of number of hops to the seed (Rh): 20
Outline n n n n Overview of Bit. Torrent Framework, scenario and assumptions Performance metrics Impact of the size of pieces Impact of the scope of the neighborhood Bit. Hoc: Our solution ¡ Choking algorithm ¡ Piece selection strategy ¡ Some first results ¡ Choice of parameters and new results. Conclusions and future work 21
Bit. Hoc: Our solution n Reduced neighborhood + a few connections to far peers good TCP performance in near neighborhood and more entropy of pieces for better sharing. Peers are classified into 2 tables : NNT : Nearby Neighbors Table (hops <=2) FNT : Far Neighbors Table (hops > 2) We redefine the choking algorithm and the piece selection strategy 22
Outline n n n n Overview of Bit. Torrent Framework, scenario and assumptions Performance metrics Impact of the size of pieces Impact of the scope of the neighborhood Bit. Hoc: Our solution ¡ Choking algorithm ¡ Piece selection strategy ¡ Some first results ¡ Choice of parameters and new results. Conclusions and future work 23
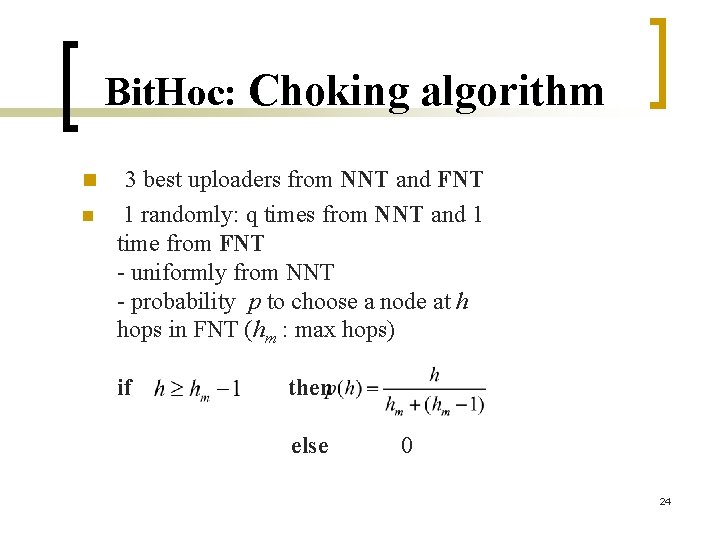
Bit. Hoc: Choking algorithm n n 3 best uploaders from NNT and FNT 1 randomly: q times from NNT and 1 time from FNT - uniformly from NNT - probability p to choose a node at h hops in FNT (hm : max hops) if then else 0 24
Outline n n n n Overview of Bit. Torrent Framework, scenario and assumptions Performance metrics Impact of the size of pieces Impact of the scope of the neighborhood Bit. Hoc: Our solution ¡ Choking algorithm ¡ Piece selection strategy ¡ Some first results ¡ Choice of parameters and new results. Conclusions and future work 25
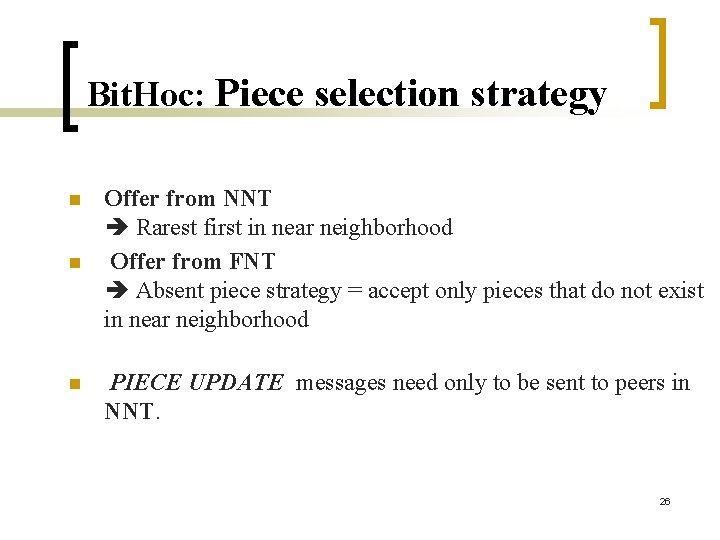
Bit. Hoc: Piece selection strategy n n n Offer from NNT Rarest first in near neighborhood Offer from FNT Absent piece strategy = accept only pieces that do not exist in near neighborhood PIECE UPDATE messages need only to be sent to peers in NNT. 26
Outline n n n n Overview of Bit. Torrent Framework, scenario and assumptions Performance metrics Impact of the size of pieces Impact of the scope of the neighborhood Bit. Hoc: Our solution ¡ Choking algorithm ¡ Piece selection strategy ¡ Some first results ¡ Choice of parameters and new results. Conclusions and future work 27
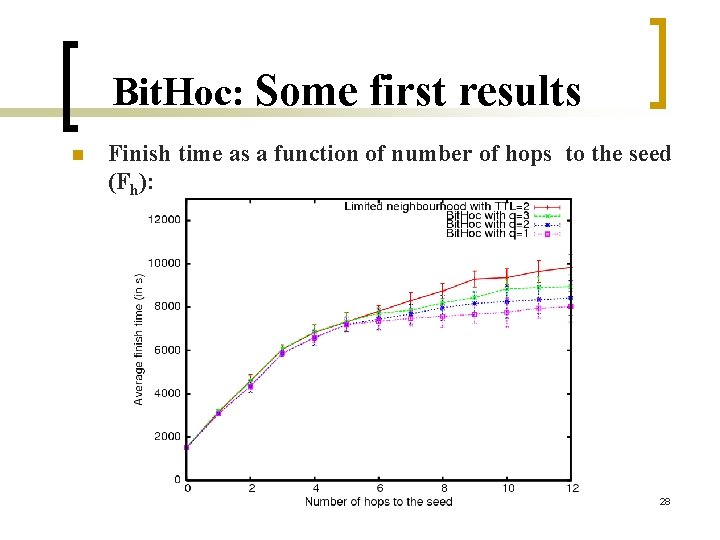
Bit. Hoc: Some first results n Finish time as a function of number of hops to the seed (Fh): 28
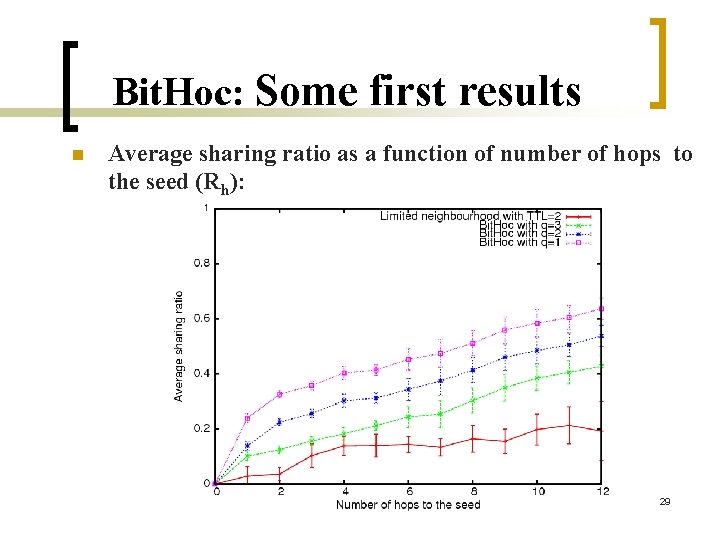
Bit. Hoc: Some first results n Average sharing ratio as a function of number of hops to the seed (Rh): 29
Outline n n n n Overview of Bit. Torrent Framework, scenario and assumptions Performance metrics Impact of the size of pieces Impact of the scope of the neighborhood Bit. Hoc: Our solution ¡ Choking algorithm ¡ Piece selection strategy ¡ Some first results ¡ Choice of parameters and new results. Conclusions and future work 30
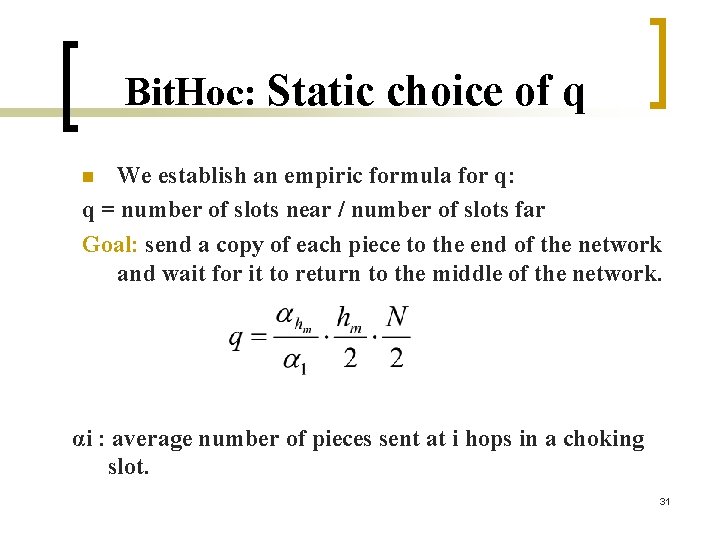
Bit. Hoc: Static choice of q We establish an empiric formula for q: q = number of slots near / number of slots far Goal: send a copy of each piece to the end of the network and wait for it to return to the middle of the network. n αi : average number of pieces sent at i hops in a choking slot. 31
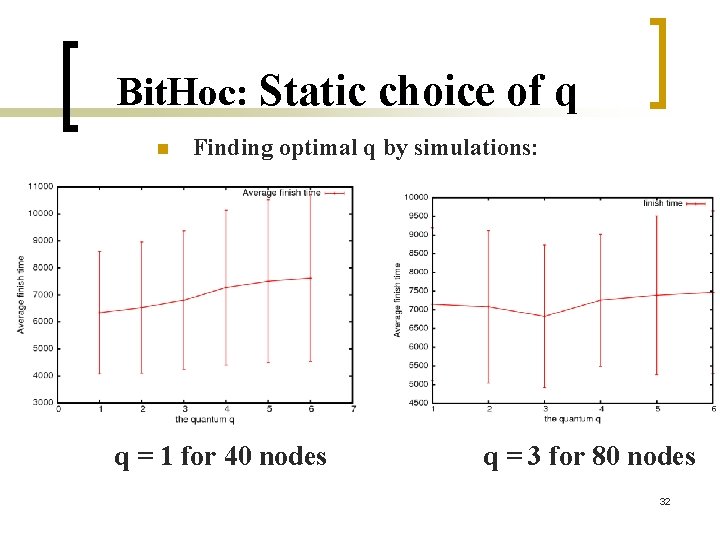
Bit. Hoc: Static choice of q n Finding optimal q by simulations: q = 1 for 40 nodes q = 3 for 80 nodes 32
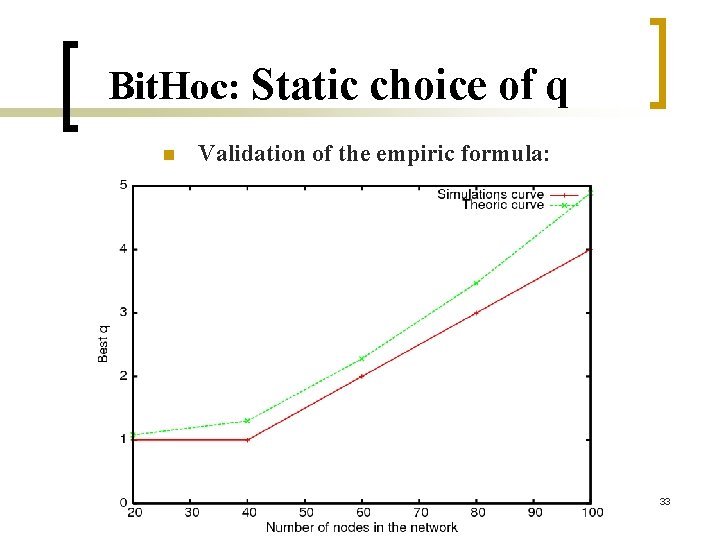
Bit. Hoc: Static choice of q n Validation of the empiric formula: 33
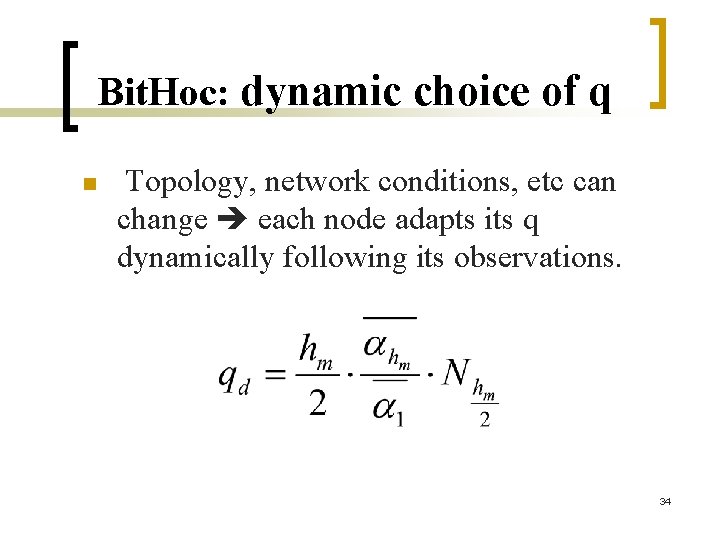
Bit. Hoc: dynamic choice of q n Topology, network conditions, etc can change each node adapts its q dynamically following its observations. 34
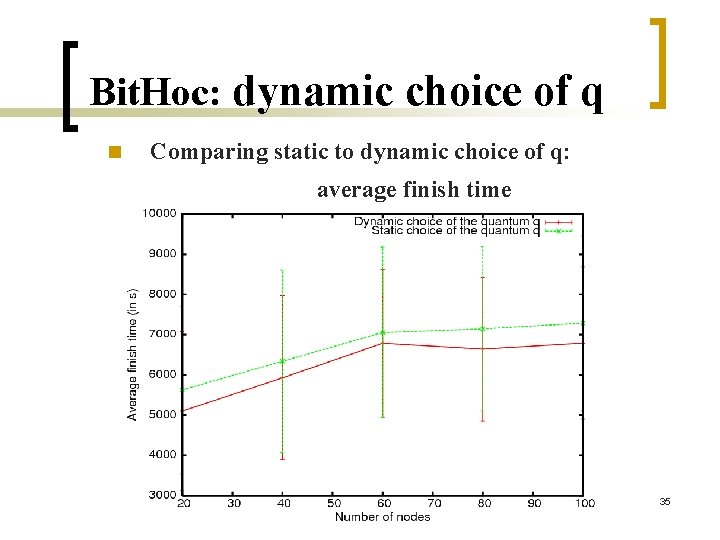
Bit. Hoc: dynamic choice of q n Comparing static to dynamic choice of q: average finish time 35
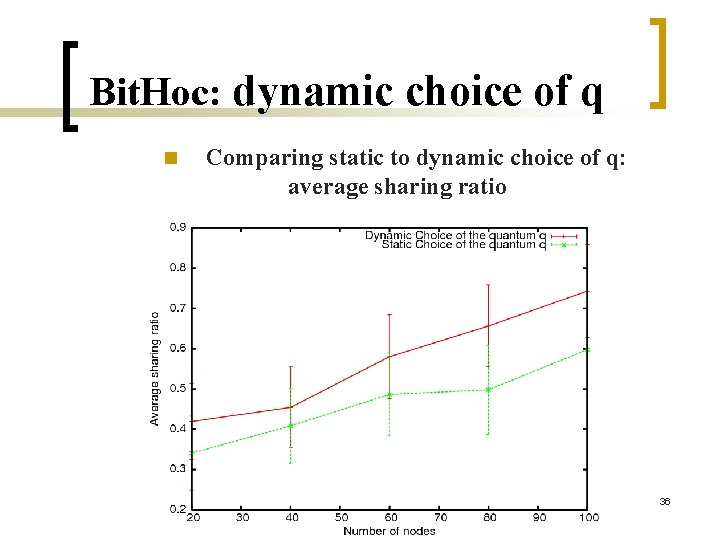
Bit. Hoc: dynamic choice of q n Comparing static to dynamic choice of q: average sharing ratio 36
Outline n n n n Overview of Bit. Torrent Framework, scenario and assumptions Performance metrics Impact of the size of pieces Impact of the scope of the neighborhood Bit. Hoc: Our solution ¡ Choking algorithm ¡ Piece selection strategy ¡ Some first results ¡ Choice of parameters and new results. Conclusions and future work 37
Conclusions and future work Bit. Hoc gives better finish times and better sharing ratios than other solutions even those limiting the scope of the neighborhood n Bit. Hoc finds a good management of neighbor and piece selection strategies ¡ Good performance in near neighborhood ¡ Better entropy by adding some few connections to far nodes ¡ Only absent pieces are sent to far nodes n Future work: ¡ Impact of mobility of nodes ¡ Studying the case of sparse overlays ¡ Optimizing lookup in wireless ad hoc networks 38 ¡ Real implementation and testing of the protocol n
THANK YOU ? E-mail: Mohamed_Karim. Sbai@sophia. inria. fr 39
- Slides: 39