EE 122 Lecture 89 Ion Stoica September 2025
EE 122: Lecture 8/9 Ion Stoica September 20/25, 2001 istoica@cs. berkeley. edu
Overview Ø § TCP/IP architecture TCP • • IP and TCP headers Connection establishment Flow control RTT estimation istoica@cs. berkeley. edu 2
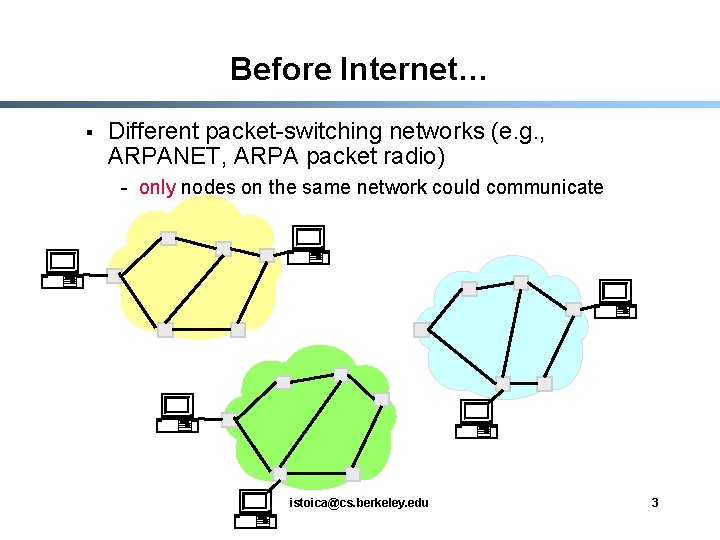
Before Internet… § Different packet-switching networks (e. g. , ARPANET, ARPA packet radio) - only nodes on the same network could communicate istoica@cs. berkeley. edu 3
Goal and Challenges § § Share resources of different packet switching networks interconnect existing networks … but, packet switching networks differ widely - Different services • E. g. , degree of reliability - Different interfaces • E. g. , length of the packet that can be transmitted, address format - Different protocols • E. g. , routing protocols istoica@cs. berkeley. edu 4
Possible solutions § Reengineer and develop one global packet switching network standard - Not economically feasible § Have every host implement the protocols of any network it wants to communicate with - Too complex, very high engineering cost istoica@cs. berkeley. edu 5
Solution § Add an extra layer: internetworking layer, also called Internet Protocol (IP) - Hosts implement one higher-level protocol - Networks interconnected by nodes that run the same protocol - Provide the interface between the new protocol and every network istoica@cs. berkeley. edu 6
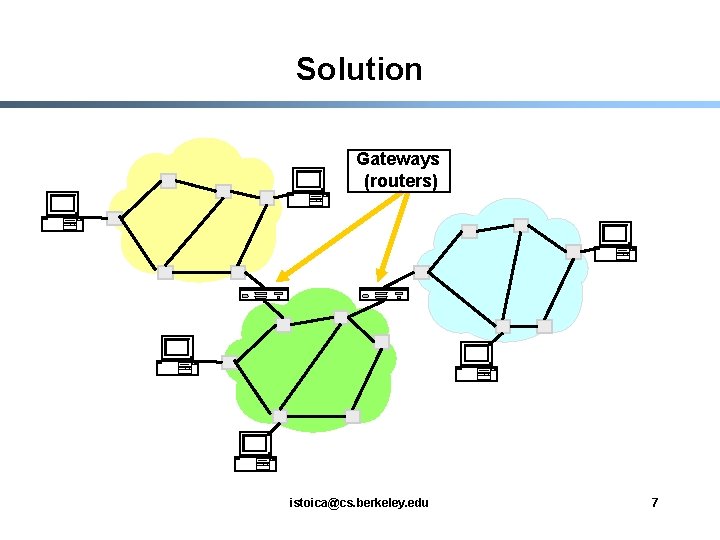
Solution Gateways (routers) istoica@cs. berkeley. edu 7
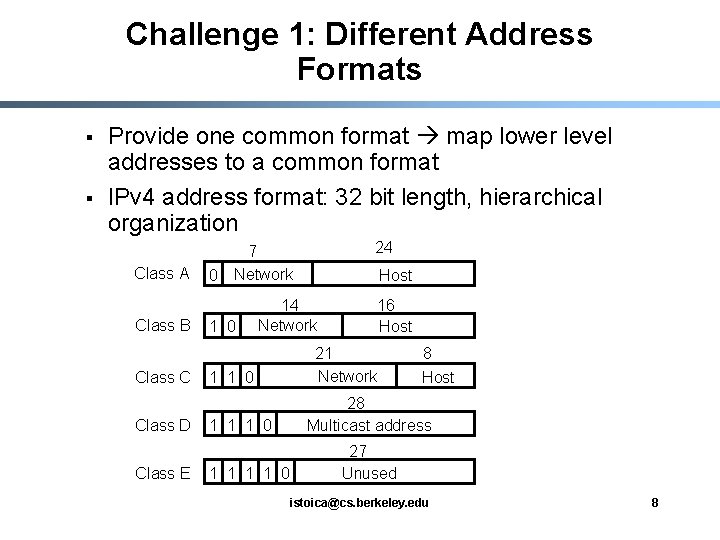
Challenge 1: Different Address Formats § § Provide one common format map lower level addresses to a common format IPv 4 address format: 32 bit length, hierarchical organization Class A Class B Class C Class D Class E 0 24 7 Network 1 0 Host 14 Network 1 1 0 1 1 1 1 0 16 Host 21 Network 8 Host 28 Multicast address 27 Unused istoica@cs. berkeley. edu 8
Challenge 2: Different Packet Sizes § § Define a maximum packet size over all networks. Why not? Implement fragmentation/re-assembly - who is doing fragmentation? - who is doing re-assembly? istoica@cs. berkeley. edu 9
Other Challenges § Errors require end-to-end reliability - Add a transport layer on top of IP § Different (routing) protocols coordinate these protocols istoica@cs. berkeley. edu 10
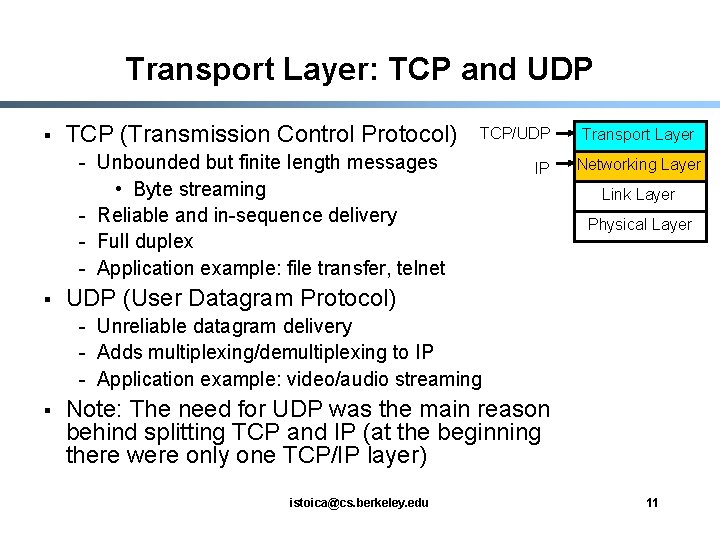
Transport Layer: TCP and UDP § TCP (Transmission Control Protocol) TCP/UDP - Unbounded but finite length messages • Byte streaming - Reliable and in-sequence delivery - Full duplex - Application example: file transfer, telnet § IP Transport Layer Networking Layer Link Layer Physical Layer UDP (User Datagram Protocol) - Unreliable datagram delivery - Adds multiplexing/demultiplexing to IP - Application example: video/audio streaming § Note: The need for UDP was the main reason behind splitting TCP and IP (at the beginning there were only one TCP/IP layer) istoica@cs. berkeley. edu 11
Overview § Ø TCP/IP architecture TCP • • IP and TCP headers Connection establishment Flow control RTT estimation istoica@cs. berkeley. edu 12
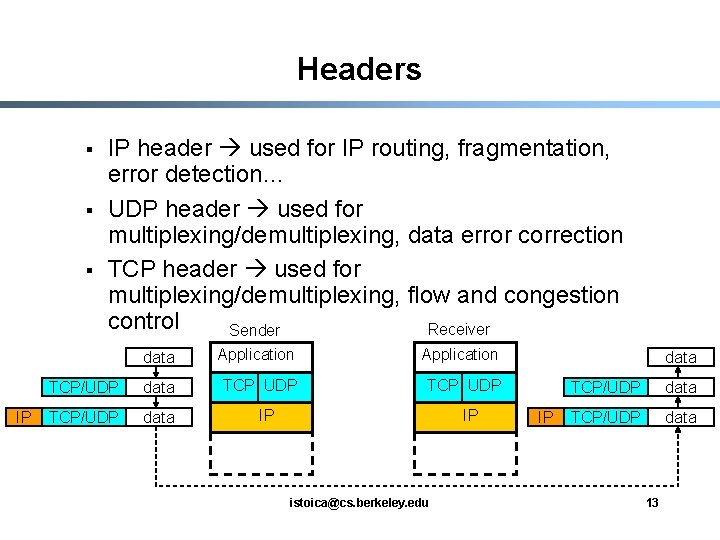
Headers § § § IP IP header used for IP routing, fragmentation, error detection… UDP header used for multiplexing/demultiplexing, data error correction TCP header used for multiplexing/demultiplexing, flow and congestion control Receiver Sender data Application TCP/UDP data TCP UDP TCP/UDP data IP IP istoica@cs. berkeley. edu data IP TCP/UDP data 13
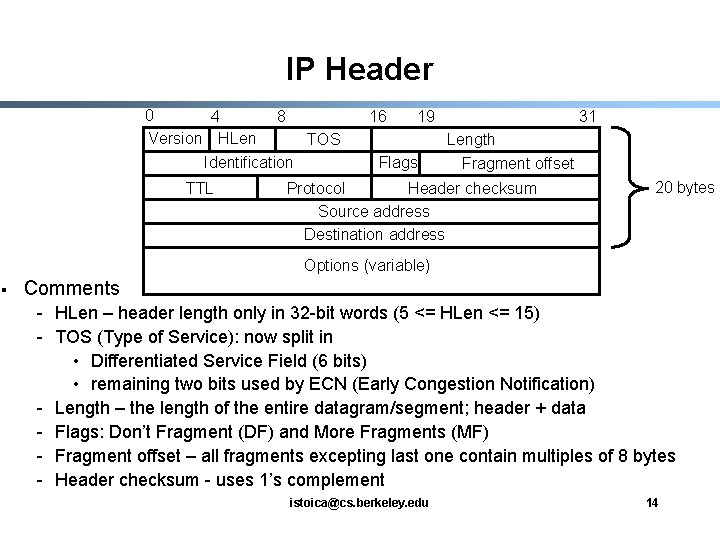
IP Header 0 4 8 Version HLen TOS Identification TTL 16 19 Flags 31 Length Fragment offset Protocol Header checksum Source address Destination address 20 bytes Options (variable) § Comments - HLen – header length only in 32 -bit words (5 <= HLen <= 15) - TOS (Type of Service): now split in • Differentiated Service Field (6 bits) • remaining two bits used by ECN (Early Congestion Notification) - Length – the length of the entire datagram/segment; header + data - Flags: Don’t Fragment (DF) and More Fragments (MF) - Fragment offset – all fragments excepting last one contain multiples of 8 bytes - Header checksum - uses 1’s complement istoica@cs. berkeley. edu 14
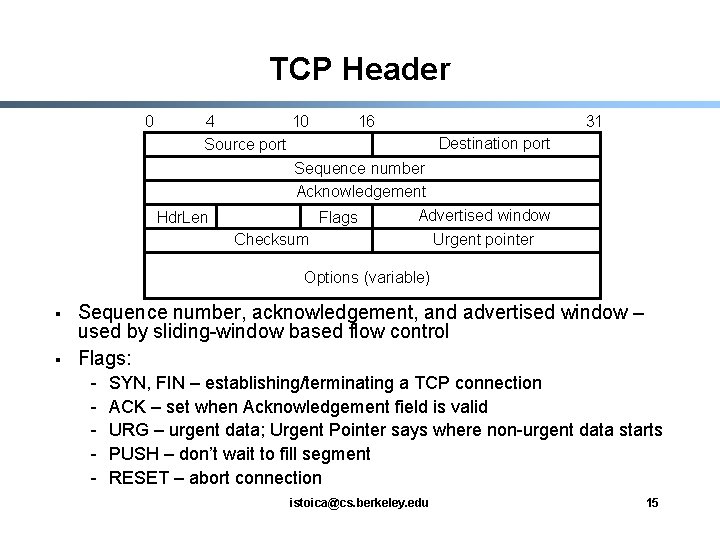
TCP Header 0 4 10 16 Destination port Source port Sequence number Acknowledgement Advertised window Hdr. Len Flags Checksum Urgent pointer 31 Options (variable) § § Sequence number, acknowledgement, and advertised window – used by sliding-window based flow control Flags: - SYN, FIN – establishing/terminating a TCP connection ACK – set when Acknowledgement field is valid URG – urgent data; Urgent Pointer says where non-urgent data starts PUSH – don’t wait to fill segment RESET – abort connection istoica@cs. berkeley. edu 15
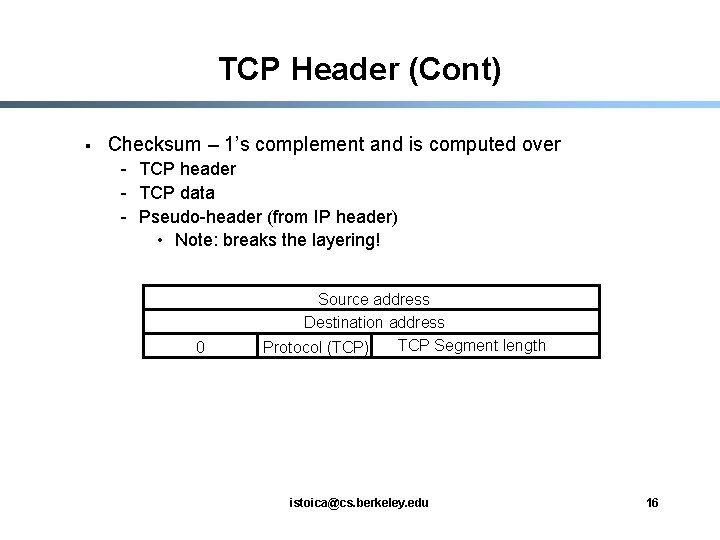
TCP Header (Cont) § Checksum – 1’s complement and is computed over - TCP header - TCP data - Pseudo-header (from IP header) • Note: breaks the layering! 0 Source address Destination address TCP Segment length Protocol (TCP) istoica@cs. berkeley. edu 16
Overview § Ø TCP/IP architecture TCP • • IP and TCP headers Connection establishment Flow control RTT estimation istoica@cs. berkeley. edu 17
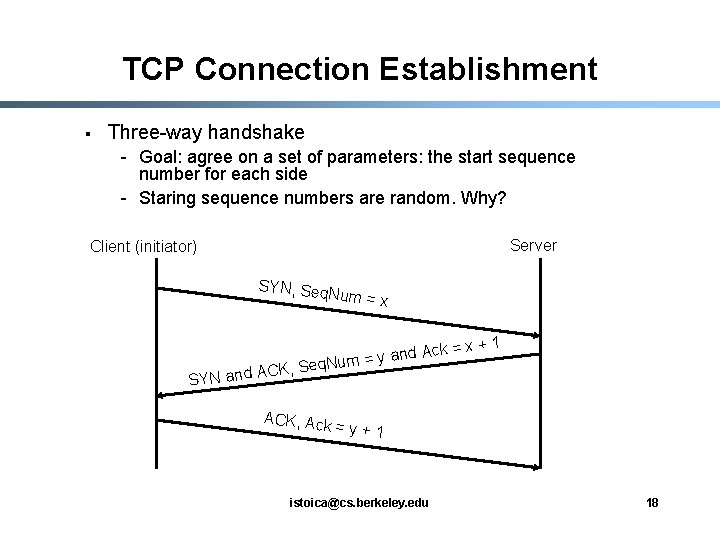
TCP Connection Establishment § Three-way handshake - Goal: agree on a set of parameters: the start sequence number for each side - Staring sequence numbers are random. Why? Server Client (initiator) SYN, Seq Num = x nd Ack a y = m u q. N CK, Se A d n a N SY ACK, Ack =x+1 =y+1 istoica@cs. berkeley. edu 18
Overview § Ø TCP/IP architecture TCP • • IP and TCP headers Connection establishment Flow control RTT estimation istoica@cs. berkeley. edu 19
Basic Problem § § How much traffic do you send? Two components - Flow control • Make sure that the receiver can receive as fast as you send - Congestion control (see Lecture 10) • Make sure that the network delivers the packets to the receiver istoica@cs. berkeley. edu 20
TCP Flow Control vs. Link Layer Flow Control § § § Flow control runs end-to-end, instead of on the same link RTT can vary widely Receiver’s maximum window size can vary - Because resources allocated to a connection varies § Sender’s maximum window size varies - Because it is used to throttle back the sender where there is congestion (see Lecture 10) § Others: - Sequence numbers counts bytes not packets - Packets usually called segments istoica@cs. berkeley. edu 21
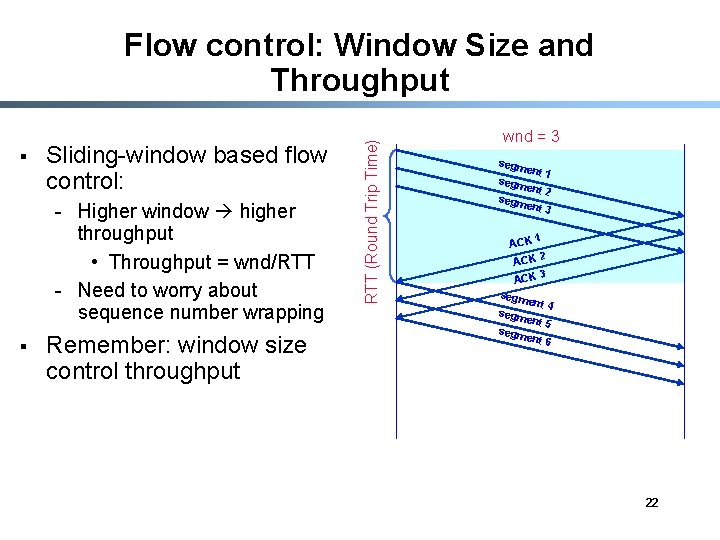
§ Sliding-window based flow control: - Higher window higher throughput • Throughput = wnd/RTT - Need to worry about sequence number wrapping § Remember: window size control throughput RTT (Round Trip Time) Flow control: Window Size and Throughput wnd = 3 segm e nt 1 segm ent 2 segm ent 3 1 ACK 2 ACK 3 ACK segm e nt 4 nt 5 segm e nt 6 22
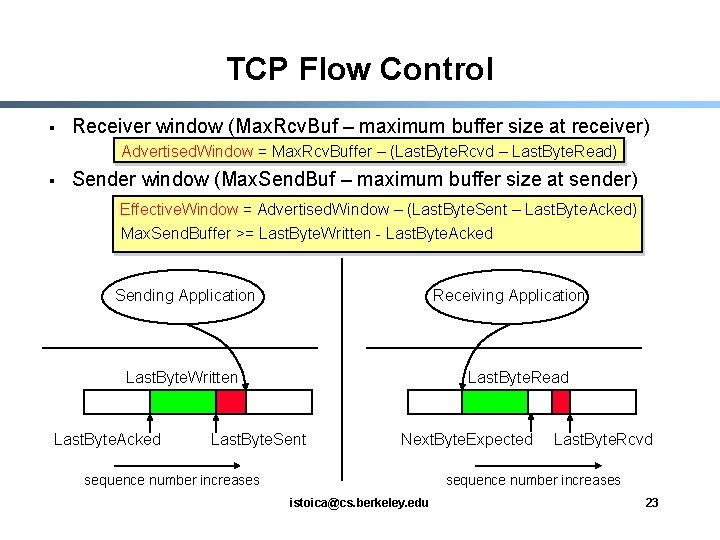
TCP Flow Control § Receiver window (Max. Rcv. Buf – maximum buffer size at receiver) Advertised. Window = Max. Rcv. Buffer – (Last. Byte. Rcvd – Last. Byte. Read) § Sender window (Max. Send. Buf – maximum buffer size at sender) Effective. Window = Advertised. Window – (Last. Byte. Sent – Last. Byte. Acked) Max. Send. Buffer >= Last. Byte. Written - Last. Byte. Acked Sending Application Receiving Application Last. Byte. Written Last. Byte. Acked Last. Byte. Read Last. Byte. Sent Next. Byte. Expected sequence number increases Last. Byte. Rcvd sequence number increases istoica@cs. berkeley. edu 23
Overview § Ø TCP/IP architecture TCP • • IP and TCP headers Connection establishment Flow control RTT estimation istoica@cs. berkeley. edu 24
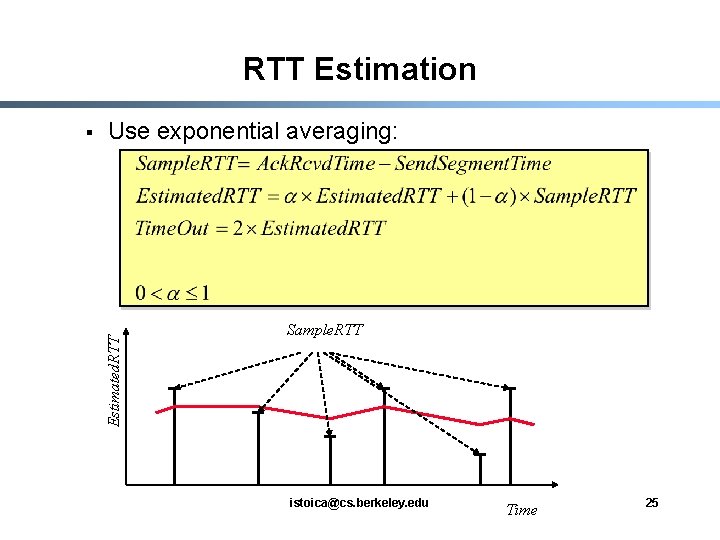
RTT Estimation Use exponential averaging: Estimated. RTT § Sample. RTT istoica@cs. berkeley. edu Time 25
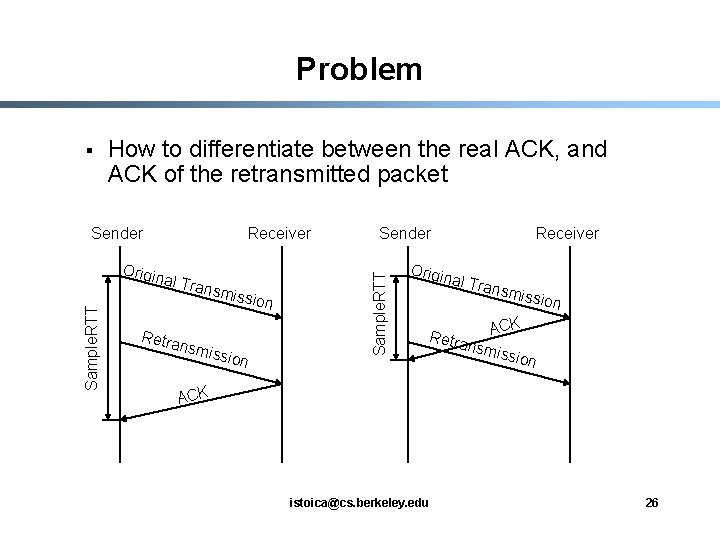
Problem How to differentiate between the real ACK, and ACK of the retransmitted packet Sender Sample. RTT Origin Receiver al Tra nsmis Retra nsmi sion ssion Sender Sample. RTT § Origin Receiver al Tra n smiss ion CK Retra A nsmi ssion ACK istoica@cs. berkeley. edu 26
Karn/Partridge Algorithm § § Measure Sample. RTT only for original transmissions Exponential backoff for each retransmission, double Estimated. RTT istoica@cs. berkeley. edu 27
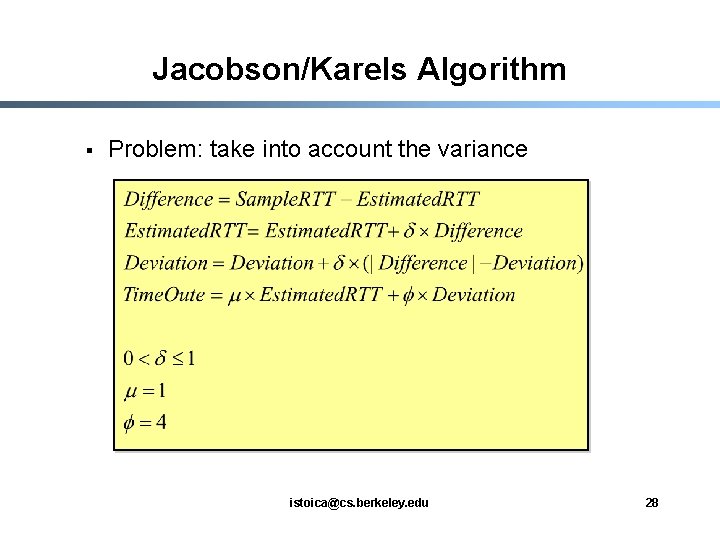
Jacobson/Karels Algorithm § Problem: take into account the variance istoica@cs. berkeley. edu 28
Summary § TCP/IP architecture - Add a layer (i. e. , the IP layer) to interconnect existing networks - Add a layer (i. e. , transport layer) to provide multiplexing/demultiplexing, reliability, and in-order delivery § TCP - Connection establishment three way handshake - Flow control based on sliding window protocol - Congestion control next lecture istoica@cs. berkeley. edu 29
- Slides: 29