Demystifying incentives in the consensus computer Loi Luu



![Related work Ø Incentive incompatible in Bitcoin Mining – [LSPSB 15] On Power Splitting Related work Ø Incentive incompatible in Bitcoin Mining – [LSPSB 15] On Power Splitting](https://slidetodoc.com/presentation_image_h2/8ec182bbd44b80b2dc48a8f9b5048925/image-29.jpg)
- Slides: 36
Demystifying incentives in the consensus computer Loi Luu, Jason Teutsch, Raghav Kulkarni, Prateek Saxena National University of Singapore
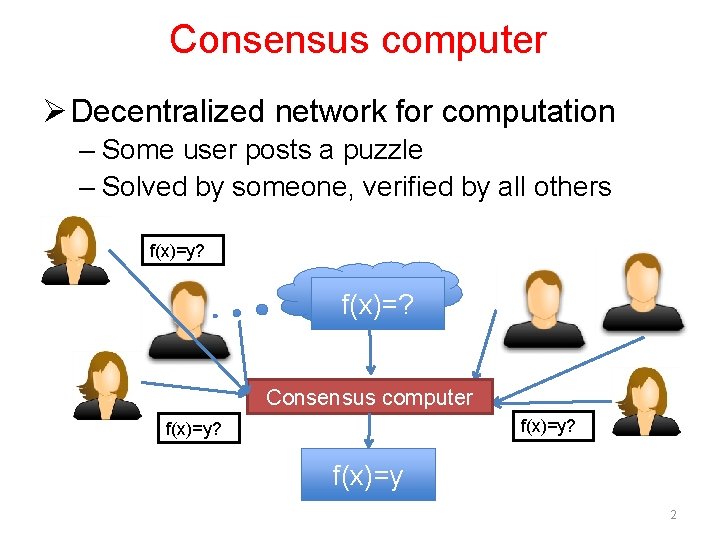
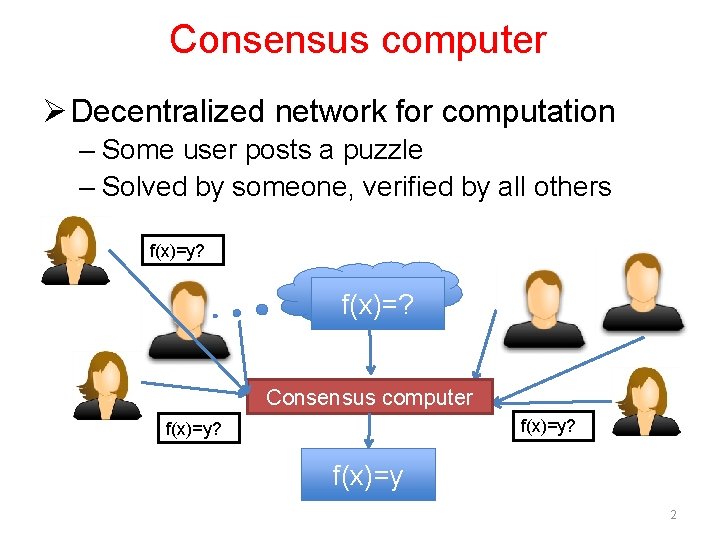
Consensus computer Ø Decentralized network for computation – Some user posts a puzzle – Solved by someone, verified by all others f(x)=y? f(x)=y f(x)=? Consensus computer f(x)=y? f(x)=y 2
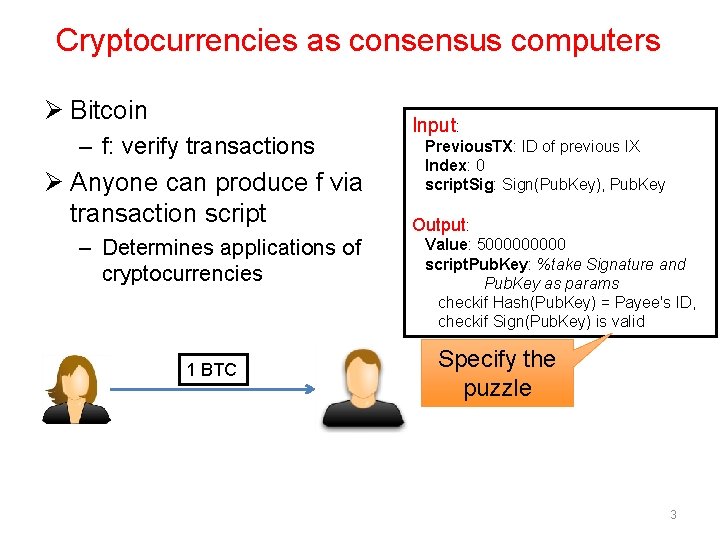
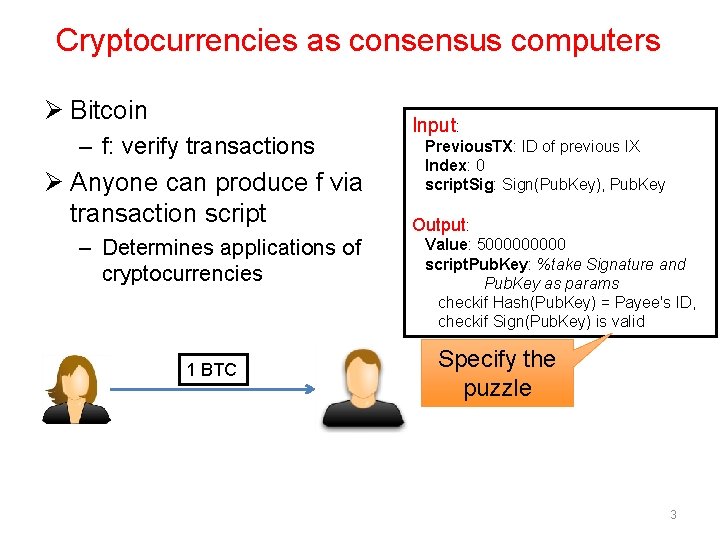
Cryptocurrencies as consensus computers Ø Bitcoin – f: verify transactions Ø Anyone can produce f via transaction script – Determines applications of cryptocurrencies 1 BTC Input: Previous. TX: ID of previous IX Index: 0 script. Sig: Sign(Pub. Key), Pub. Key Output: Value: 500000 script. Pub. Key: %take Signature and Pub. Key as params checkif Hash(Pub. Key) = Payee's ID, checkif Sign(Pub. Key) is valid Specify the puzzle 3
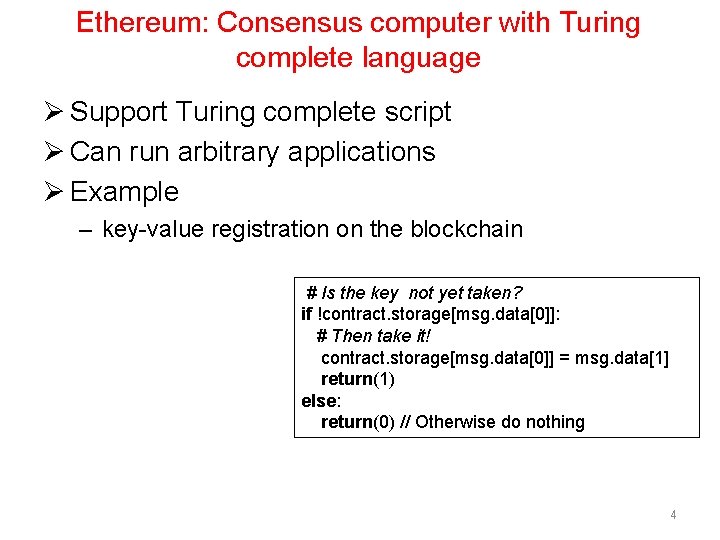
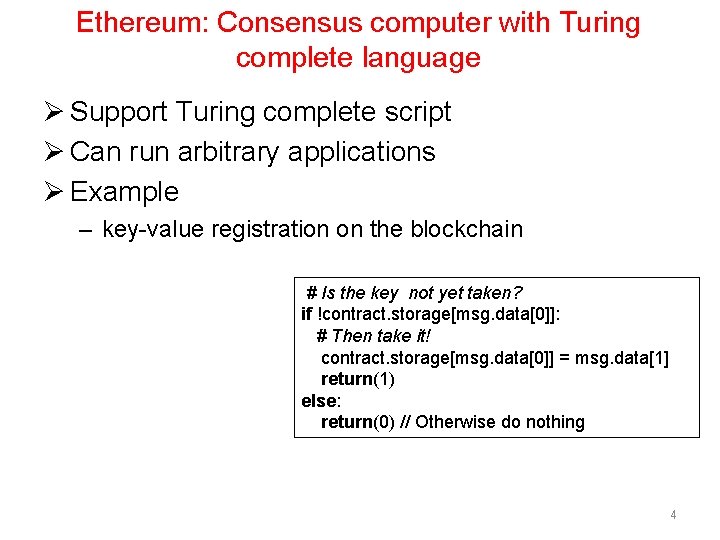
Ethereum: Consensus computer with Turing complete language Ø Support Turing complete script Ø Can run arbitrary applications Ø Example – key-value registration on the blockchain # Is the key not yet taken? if !contract. storage[msg. data[0]]: # Then take it! contract. storage[msg. data[0]] = msg. data[1] return(1) else: return(0) // Otherwise do nothing 4

Why study consensus computers? 5
Problem: correctness of computation? Ø Assumption: Users always verify and accept only correct solutions – Users are under attack if they verify? – Users have incentive to skip? Ø Previous work – Focus on mining – Implement more applications on top of consensus computers • Rely on the assumption 6

Oops! - 5% miners mined an invalid block - Half the network hash rate was mining without fully validating blocks - Build new blocks on top of that invalid block. 7
Findings Ø The verification assumption is shaky! – Users are vulnerable to attacks – Rational users have incentive to skip verifications – Computation may be incorrect! 8
Contributions Ø Consensus computer may produce incorrect results – Verifier’s dilemma Ø Classes of computations can be performed correctly – Formalize the protocol used by consensus computers – Understand the incentive structure Ø Techniques to support more applications 9
ANALYZING THE VERIFICATION ASSUMPTION 10
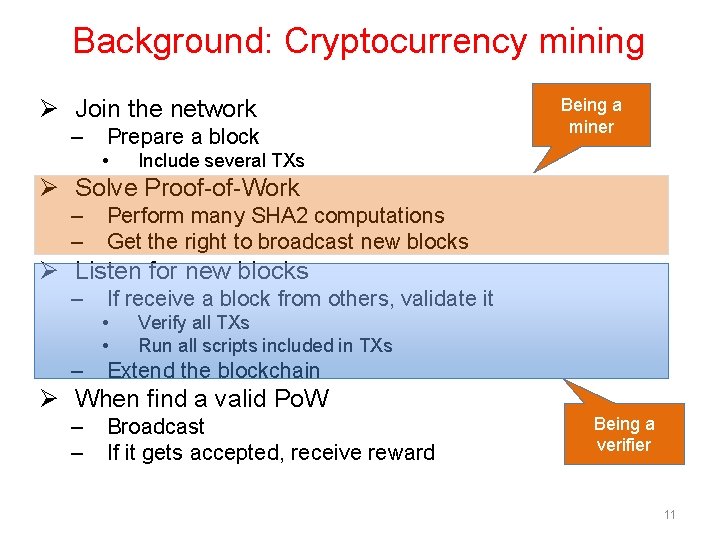
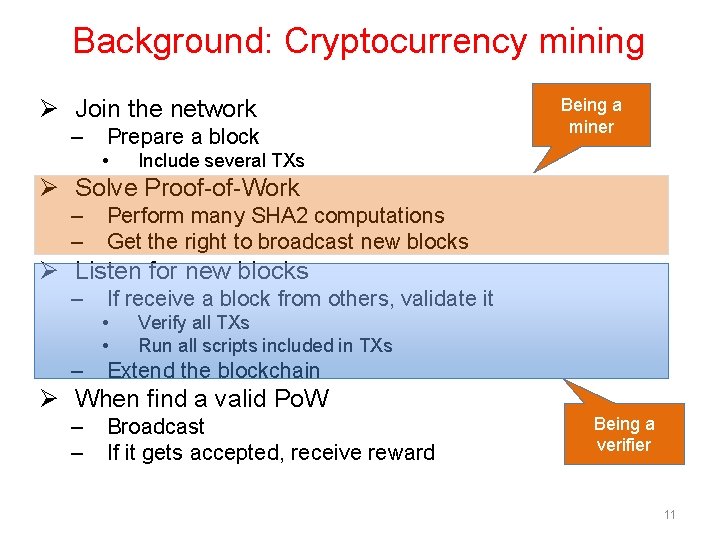
Background: Cryptocurrency mining Ø Join the network – Prepare a block • Being a miner Include several TXs Ø Solve Proof-of-Work – – Perform many SHA 2 computations Get the right to broadcast new blocks Ø Listen for new blocks – If receive a block from others, validate it • • – Verify all TXs Run all scripts included in TXs Extend the blockchain Ø When find a valid Po. W – – Broadcast If it gets accepted, receive reward Being a verifier 11
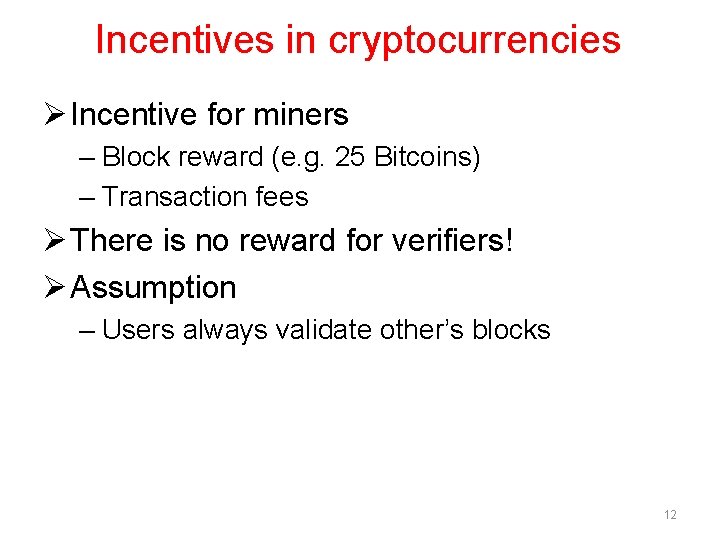
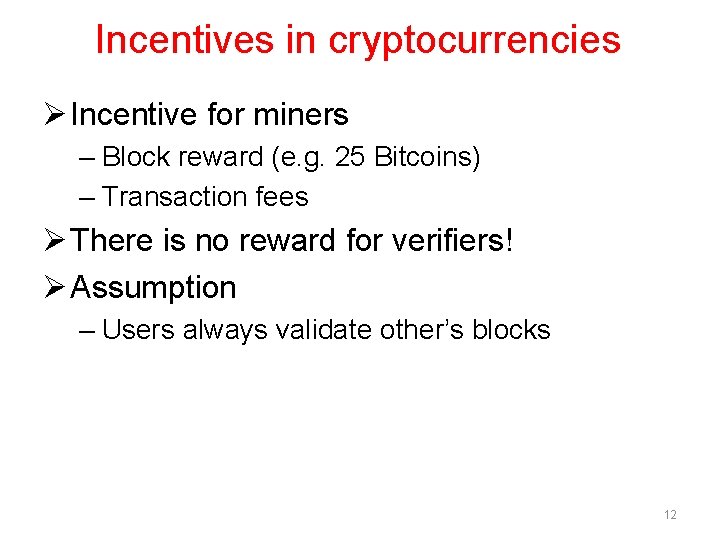
Incentives in cryptocurrencies Ø Incentive for miners – Block reward (e. g. 25 Bitcoins) – Transaction fees Ø There is no reward for verifiers! Ø Assumption – Users always validate other’s blocks 12

ATTACKS ON VERIFIERS 13
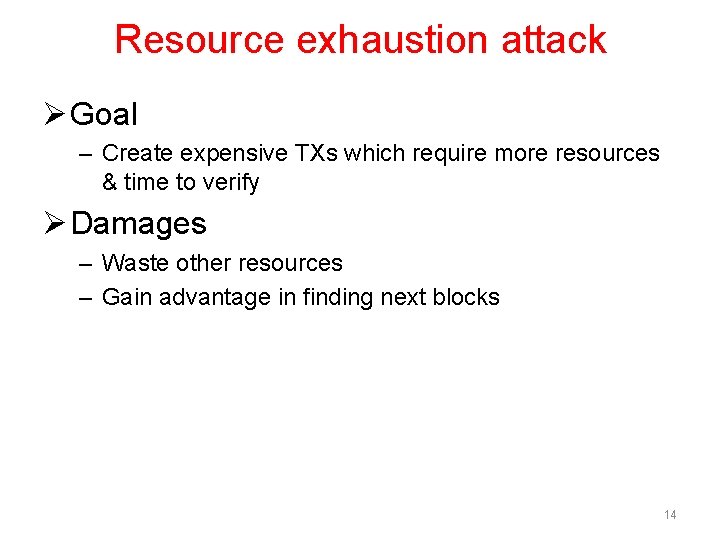
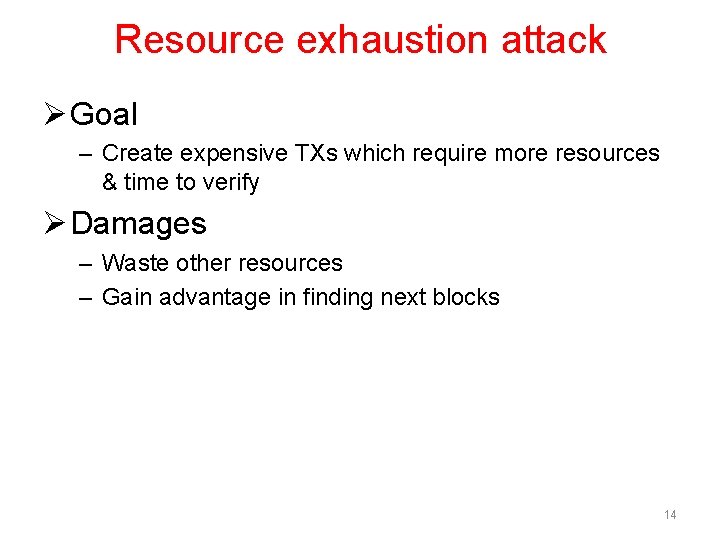
Resource exhaustion attack Ø Goal – Create expensive TXs which require more resources & time to verify Ø Damages – Waste other resources – Gain advantage in finding next blocks 14
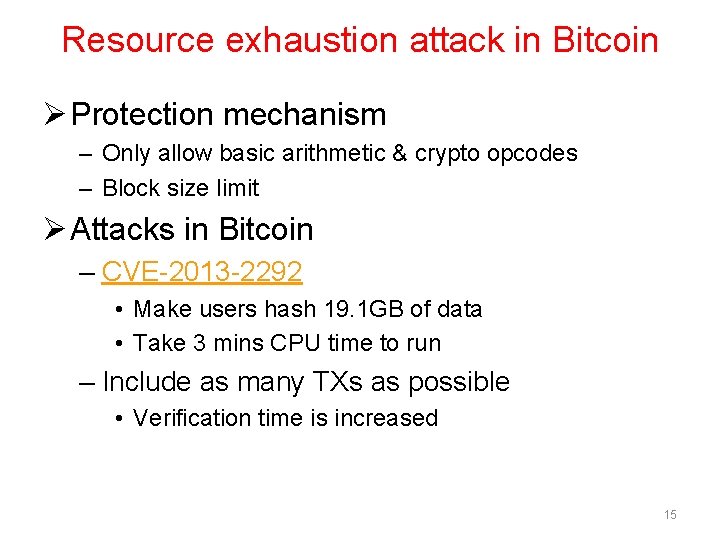
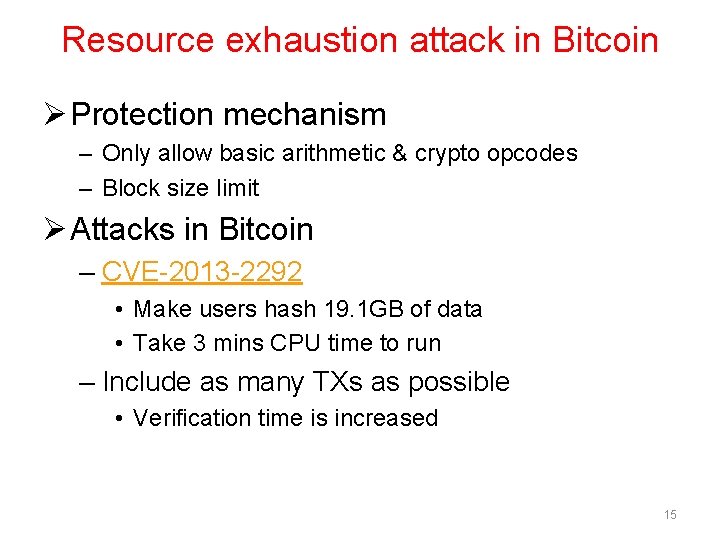
Resource exhaustion attack in Bitcoin Ø Protection mechanism – Only allow basic arithmetic & crypto opcodes – Block size limit Ø Attacks in Bitcoin – CVE-2013 -2292 • Make users hash 19. 1 GB of data • Take 3 mins CPU time to run – Include as many TXs as possible • Verification time is increased 15
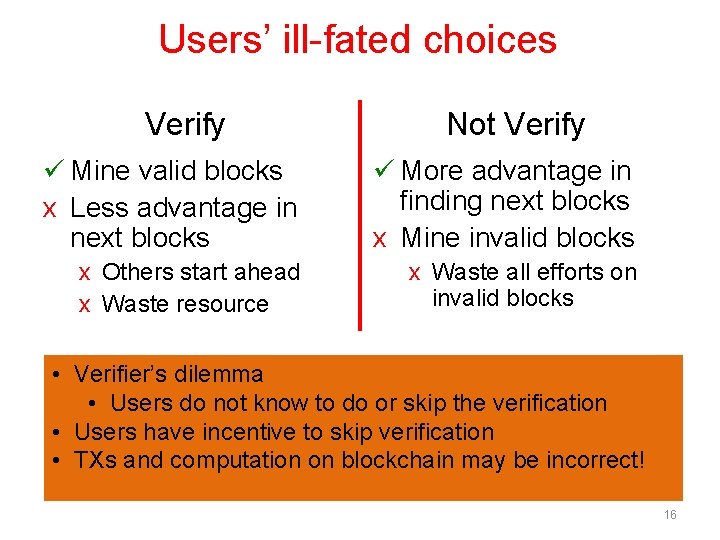
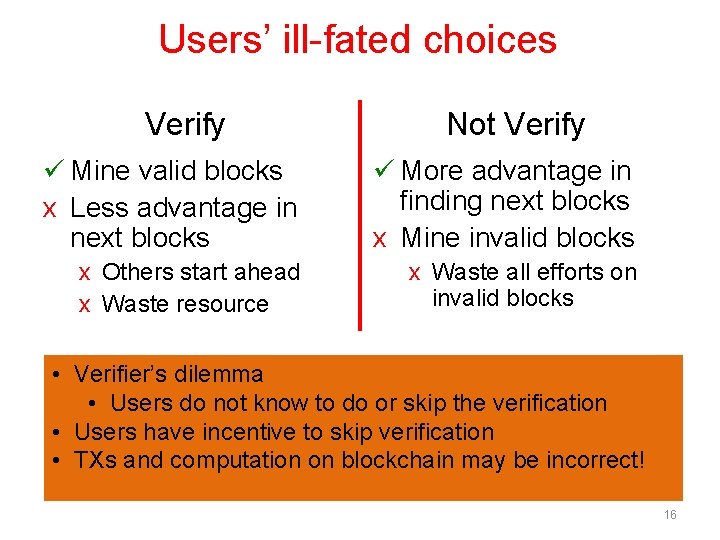
Users’ ill-fated choices Verify Not Verify ü Mine valid blocks x Less advantage in next blocks ü More advantage in finding next blocks x Mine invalid blocks x Others start ahead x Waste resource x Waste all efforts on invalid blocks • Verifier’s dilemma • Users do not know to do or skip the verification • Users have incentive to skip verification • TXs and computation on blockchain may be incorrect! 16
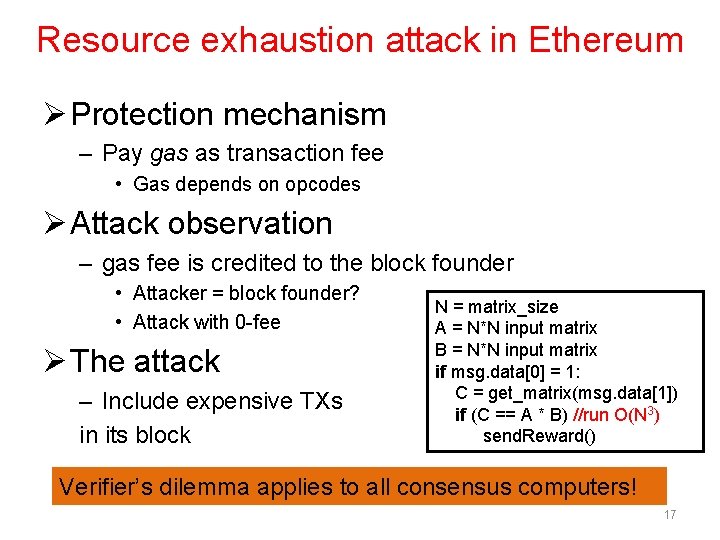
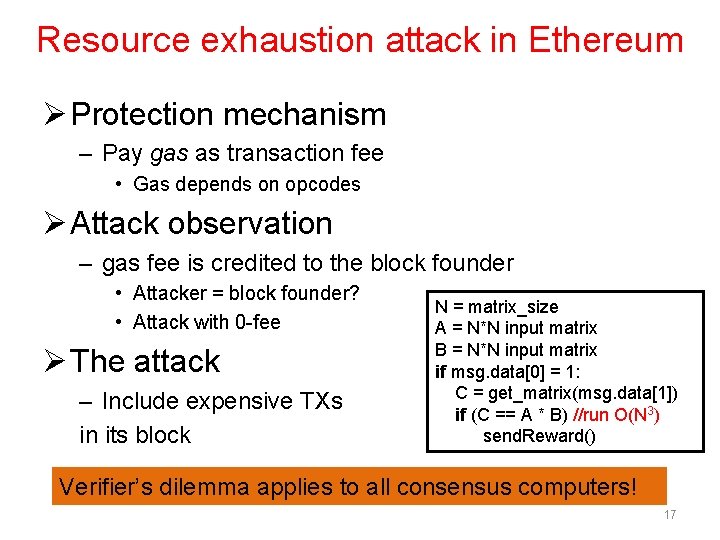
Resource exhaustion attack in Ethereum Ø Protection mechanism – Pay gas as transaction fee • Gas depends on opcodes Ø Attack observation – gas fee is credited to the block founder • Attacker = block founder? • Attack with 0 -fee Ø The attack – Include expensive TXs in its block N = matrix_size A = N*N input matrix B = N*N input matrix if msg. data[0] = 1: C = get_matrix(msg. data[1]) if (C == A * B) //run O(N 3) send. Reward() Verifier’s dilemma applies to all consensus computers! 17
INCENTIVIZING VERIFICATION 18
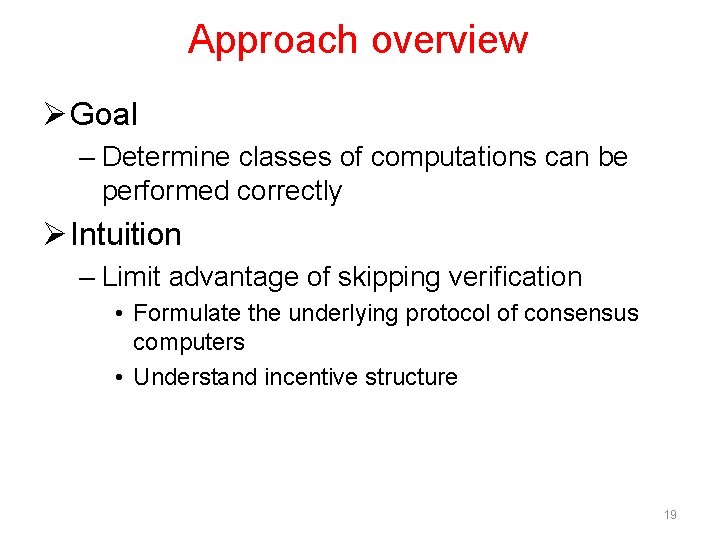
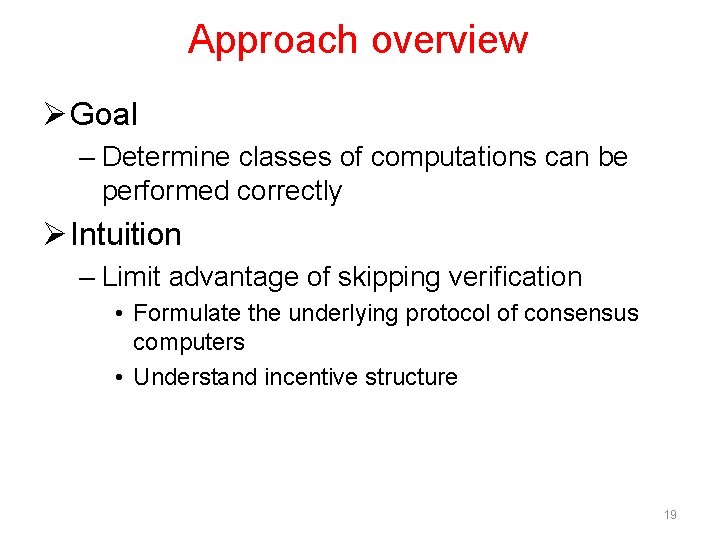
Approach overview Ø Goal – Determine classes of computations can be performed correctly Ø Intuition – Limit advantage of skipping verification • Formulate the underlying protocol of consensus computers • Understand incentive structure 19
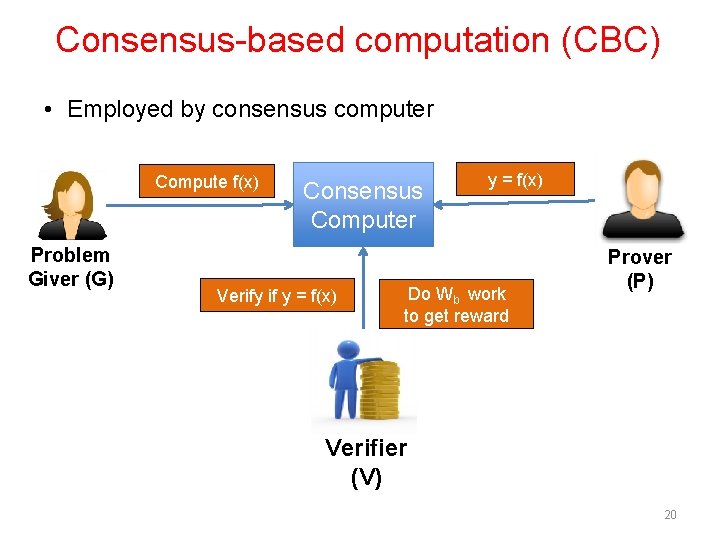
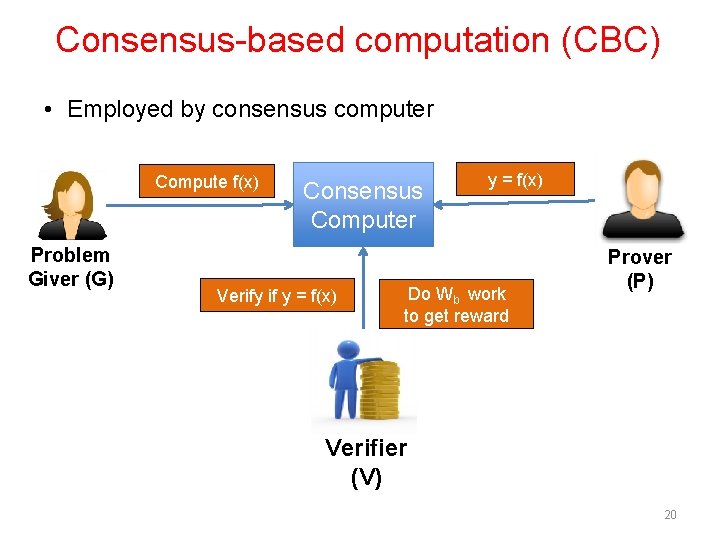
Consensus-based computation (CBC) • Employed by consensus computer Compute f(x) Problem Giver (G) Consensus Computer Verify if y = f(x) Do Wb work to get reward Prover (P) Verifier (V) 20
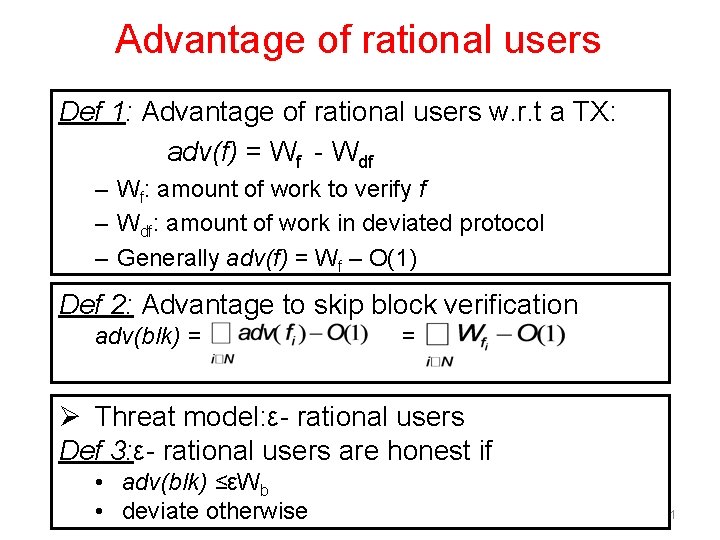
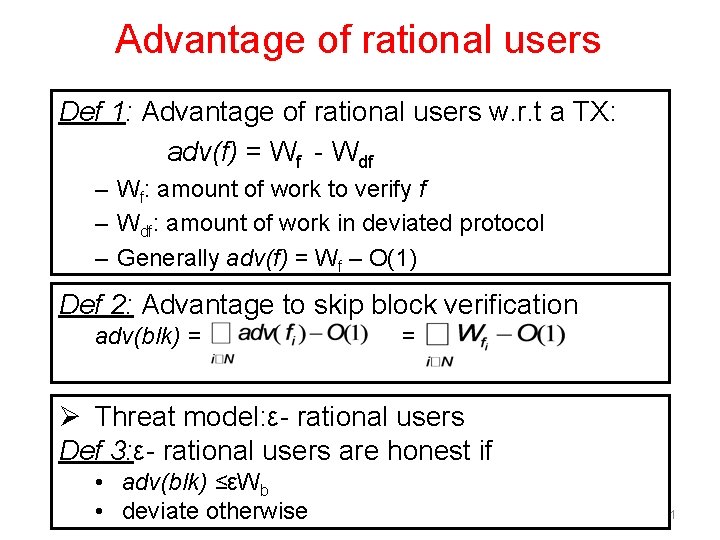
Advantage of rational users Def 1: Advantage of rational users w. r. t a TX: adv(f) = Wf - Wdf – Wf: amount of work to verify f – Wdf: amount of work in deviated protocol – Generally adv(f) = Wf – O(1) Def 2: Advantage to skip block verification adv(blk) = = Ø Threat model: ε- rational users Def 3: ε- rational users are honest if • adv(blk) ≤εWb • deviate otherwise 21
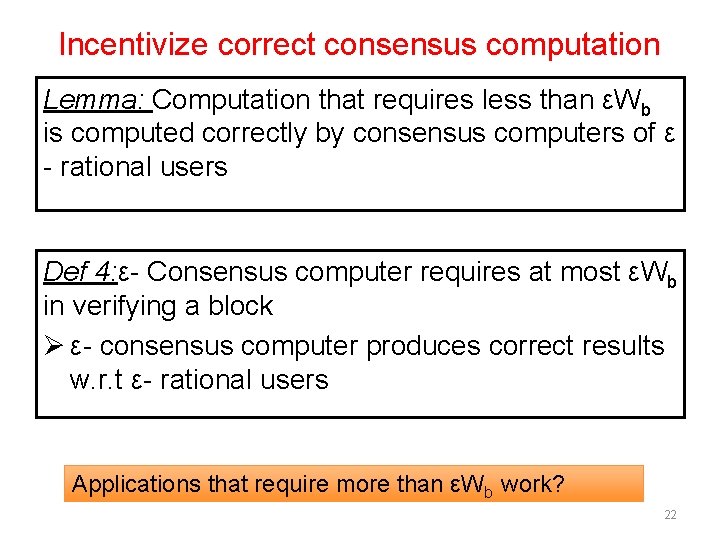
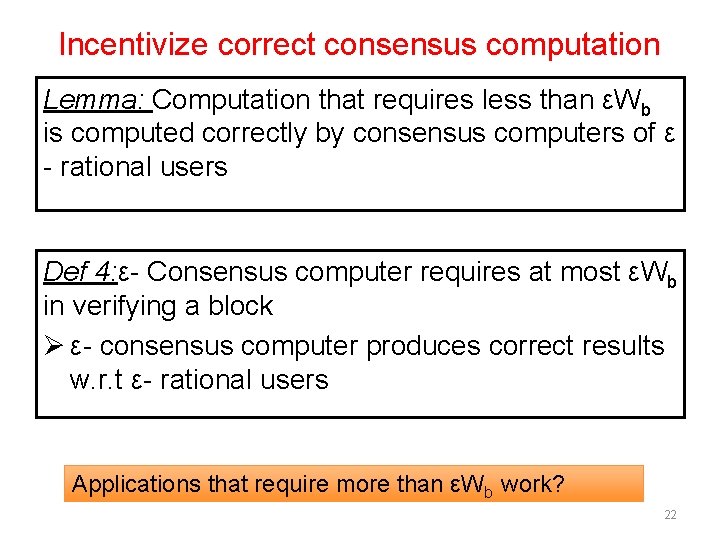
Incentivize correct consensus computation Lemma: Computation that requires less than εWb is computed correctly by consensus computers of ε - rational users Def 4: ε- Consensus computer requires at most εWb in verifying a block Ø ε- consensus computer produces correct results w. r. t ε- rational users Applications that require more than εWb work? 22
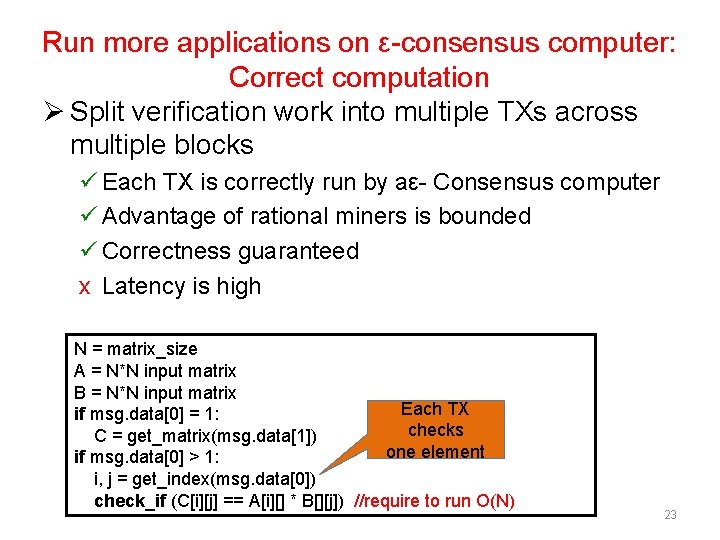
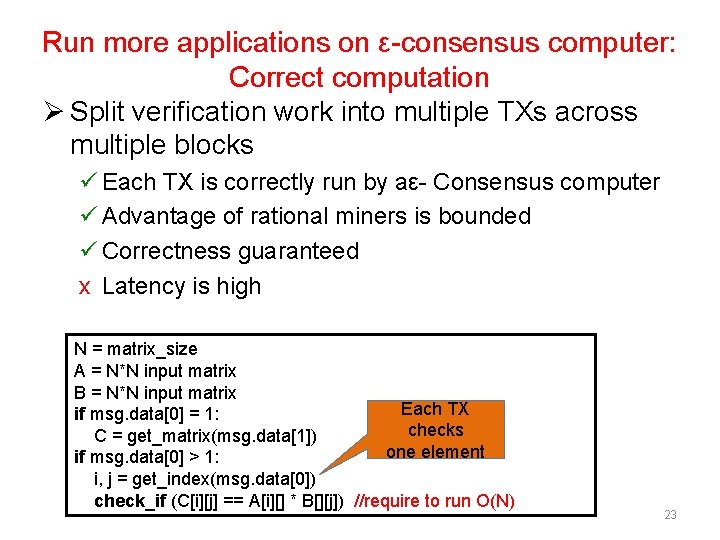
Run more applications on ε-consensus computer: Correct computation Ø Split verification work into multiple TXs across multiple blocks ü Each TX is correctly run by aε- Consensus computer ü Advantage of rational miners is bounded ü Correctness guaranteed x Latency is high N = matrix_size A = N*N input matrix B = N*N input matrix Each TX if msg. data[0] = 1: checks C = get_matrix(msg. data[1]) one element if msg. data[0] > 1: i, j = get_index(msg. data[0]) check_if (C[i][j] == A[i][] * B[][j]) //require to run O(N) 23
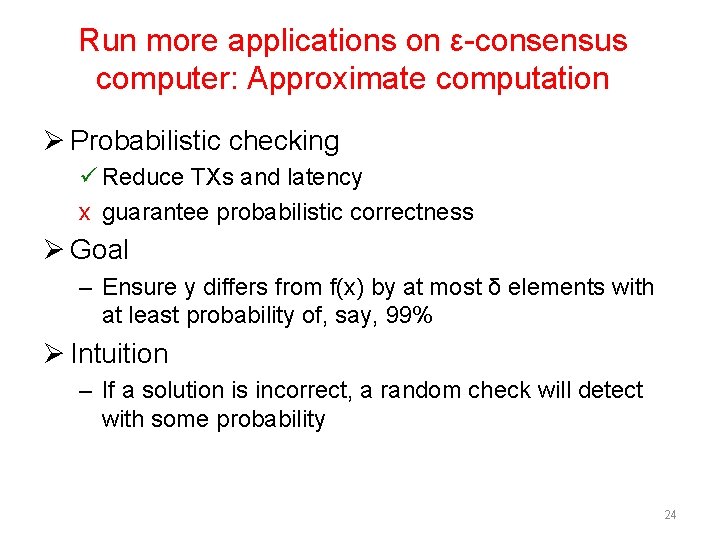
Run more applications on ε-consensus computer: Approximate computation Ø Probabilistic checking ü Reduce TXs and latency x guarantee probabilistic correctness Ø Goal – Ensure y differs from f(x) by at most δ elements with at least probability of, say, 99% Ø Intuition – If a solution is incorrect, a random check will detect with some probability 24
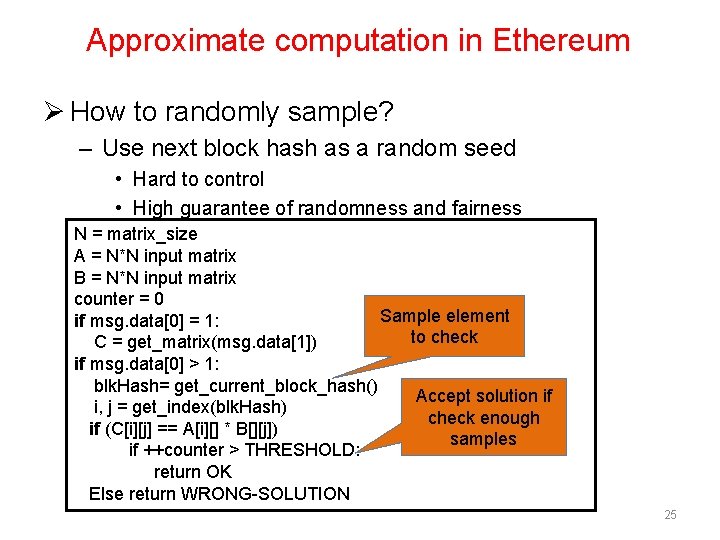
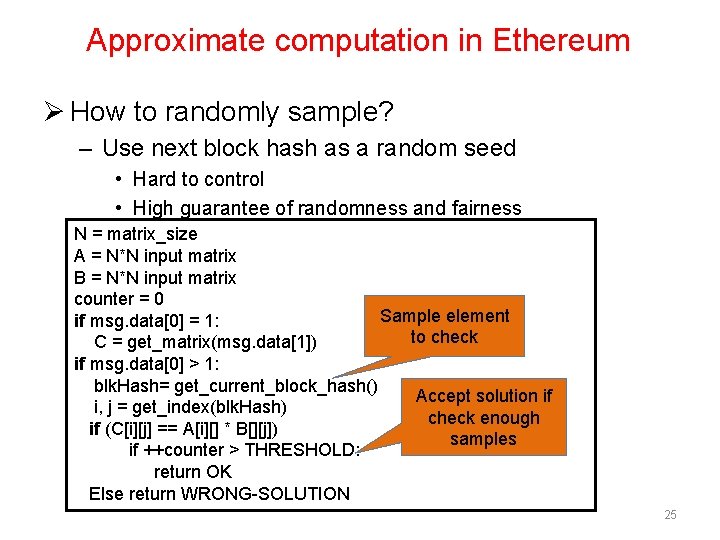
Approximate computation in Ethereum Ø How to randomly sample? – Use next block hash as a random seed • Hard to control • High guarantee of randomness and fairness N = matrix_size A = N*N input matrix B = N*N input matrix counter = 0 Sample element if msg. data[0] = 1: to check C = get_matrix(msg. data[1]) if msg. data[0] > 1: blk. Hash= get_current_block_hash() Accept solution if i, j = get_index(blk. Hash) check enough if (C[i][j] == A[i][] * B[][j]) samples if ++counter > THRESHOLD: return OK Else return WRONG-SOLUTION 25
Other case studies Ø Correct consensus computation – GCD computation of large numbers – Dot product Ø Approximate consensus computation – Matrix multiplication – Sorting – k-coloring 26
Conclusion Ø Computation done by consensus computer is not guaranteed! – Verifier’s dilemma Ø Determine classes of computations can be executed correctly – Formalize the consensus computer protocol – Understand the incentive structure Ø Techniques to deploy large applications – Tradeoff between correctness & performance 27
Thank you Q&A Email: loiluu@comp. nus. edu. sg 28
![Related work Ø Incentive incompatible in Bitcoin Mining LSPSB 15 On Power Splitting Related work Ø Incentive incompatible in Bitcoin Mining – [LSPSB 15] On Power Splitting](https://slidetodoc.com/presentation_image_h2/8ec182bbd44b80b2dc48a8f9b5048925/image-29.jpg)
Related work Ø Incentive incompatible in Bitcoin Mining – [LSPSB 15] On Power Splitting Games in Distributed Computation: The Case of Bitcoin Pooled Mining – [Eyal 15] The miner’s dilemma Ø Other Bitcoin attacks – [Rosen 11] Analysis of Bitcoin Pooled Mining Reward Systems • Pool hopping, Lie in wait attack – [Eyal. Si 13] Majority is not enough: Bitcoin mining is vulnerable • Selfish mining attack – [HKZG 15] Eclipse Attacks on Bitcoin’s Peer-to-Peer Network 29
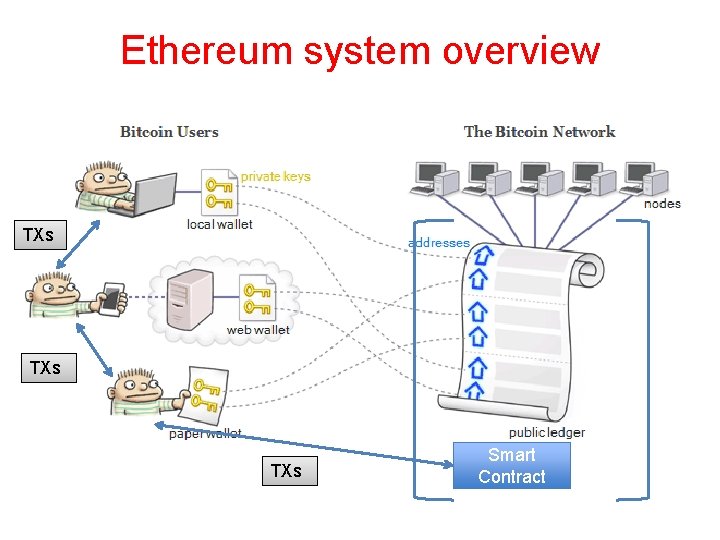
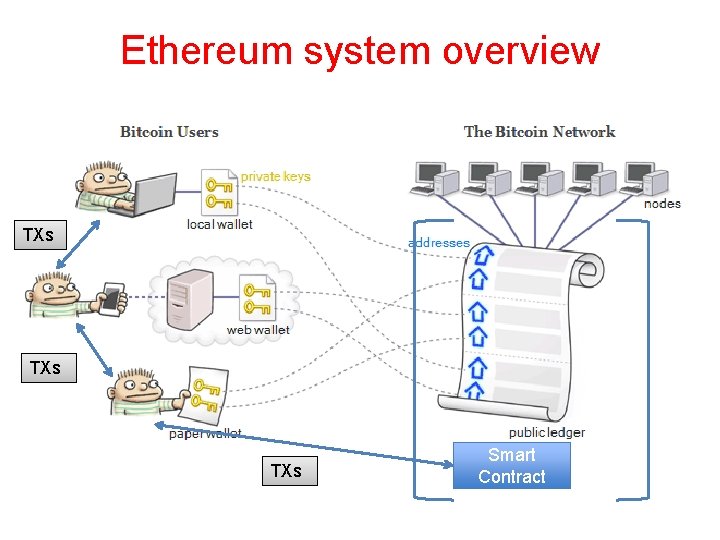
Ethereum system overview TXs TXs Smart Contract
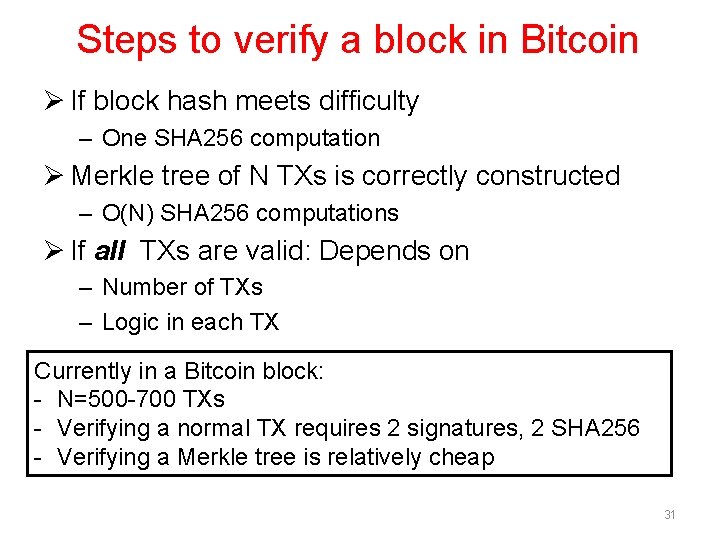
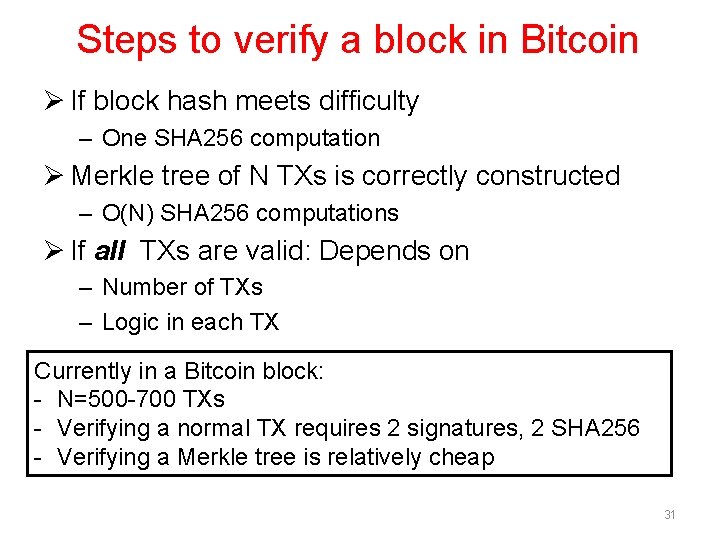
Steps to verify a block in Bitcoin Ø If block hash meets difficulty – One SHA 256 computation Ø Merkle tree of N TXs is correctly constructed – O(N) SHA 256 computations Ø If all TXs are valid: Depends on – Number of TXs – Logic in each TX Currently in a Bitcoin block: - N=500 -700 TXs - Verifying a normal TX requires 2 signatures, 2 SHA 256 - Verifying a Merkle tree is relatively cheap 31
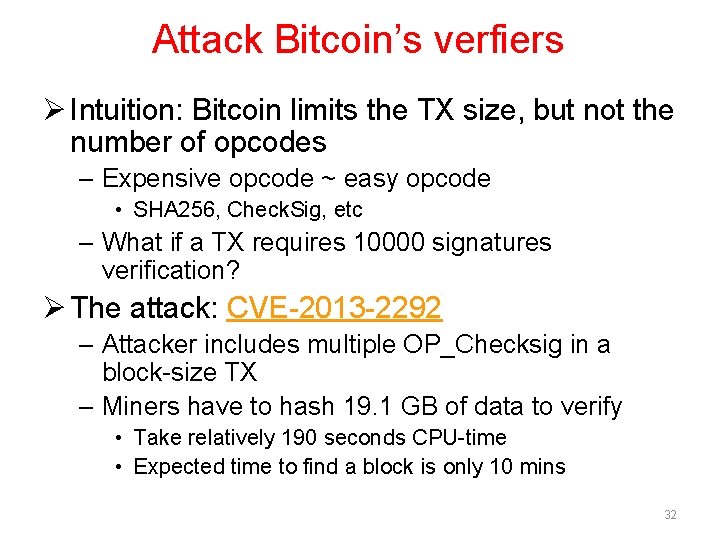
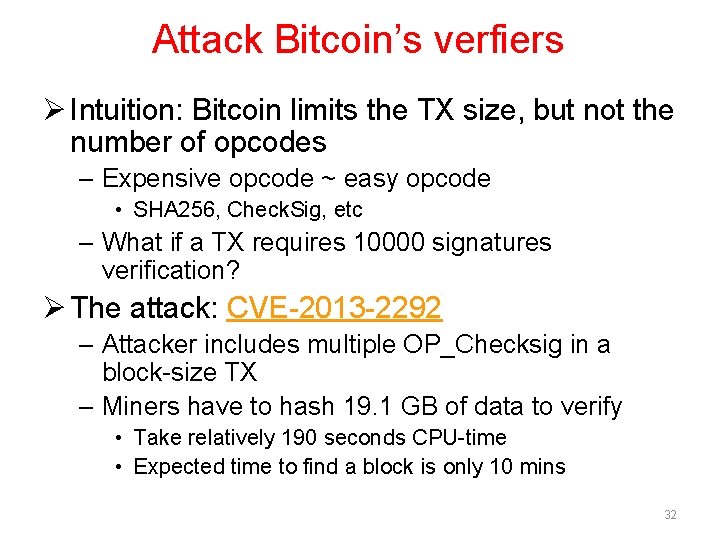
Attack Bitcoin’s verfiers Ø Intuition: Bitcoin limits the TX size, but not the number of opcodes – Expensive opcode ~ easy opcode • SHA 256, Check. Sig, etc – What if a TX requires 10000 signatures verification? Ø The attack: CVE-2013 -2292 – Attacker includes multiple OP_Checksig in a block-size TX – Miners have to hash 19. 1 GB of data to verify • Take relatively 190 seconds CPU-time • Expected time to find a block is only 10 mins 32
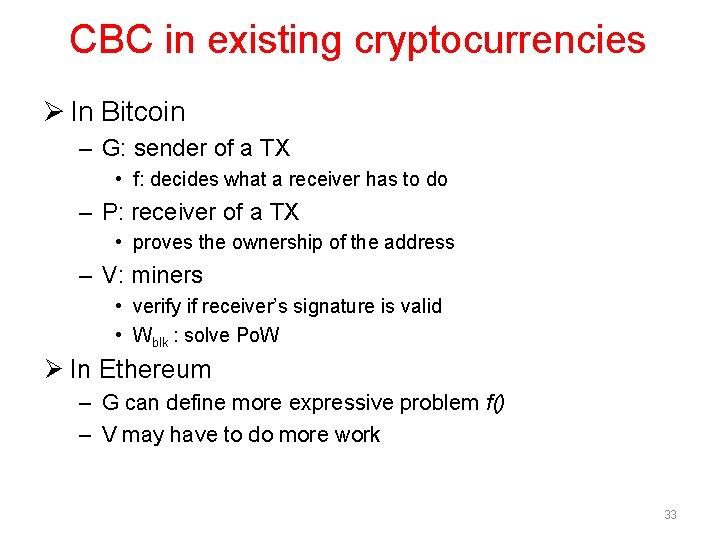
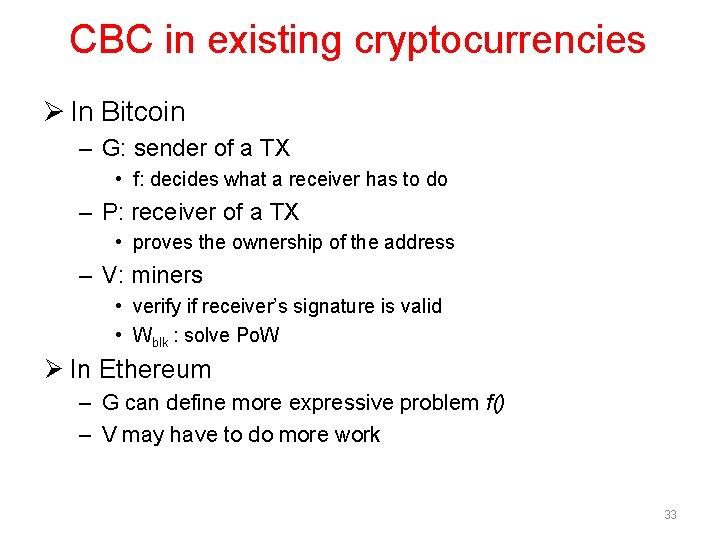
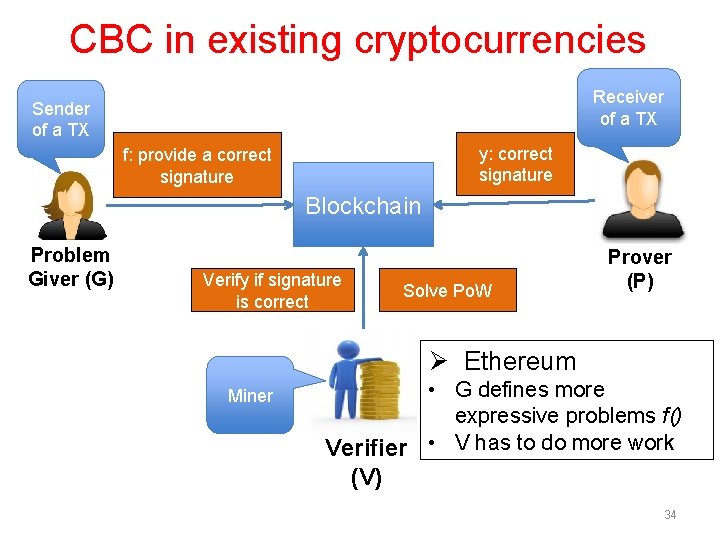
CBC in existing cryptocurrencies Ø In Bitcoin – G: sender of a TX • f: decides what a receiver has to do – P: receiver of a TX • proves the ownership of the address – V: miners • verify if receiver’s signature is valid • Wblk : solve Po. W Ø In Ethereum – G can define more expressive problem f() – V may have to do more work 33
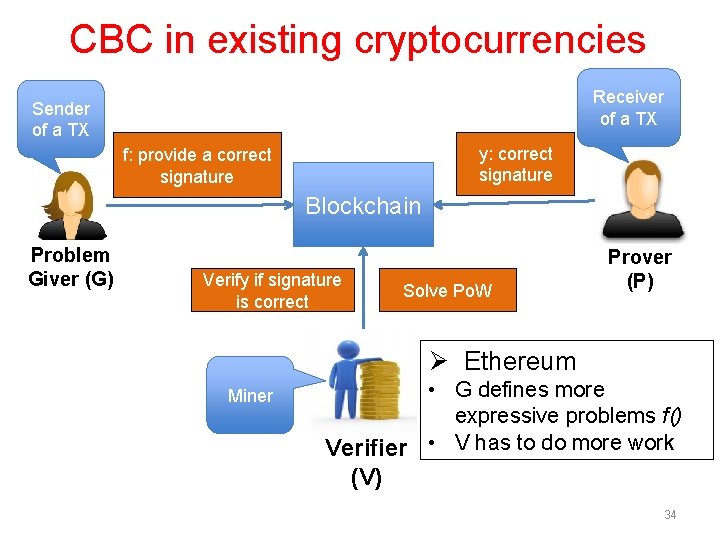
CBC in existing cryptocurrencies Receiver of a TX Sender of a TX y: correct signature f: provide a correct signature Blockchain Problem Giver (G) Verify if signature is correct Solve Po. W Prover (P) Ø Ethereum Miner • G defines more expressive problems f() Verifier • V has to do more work (V) 34
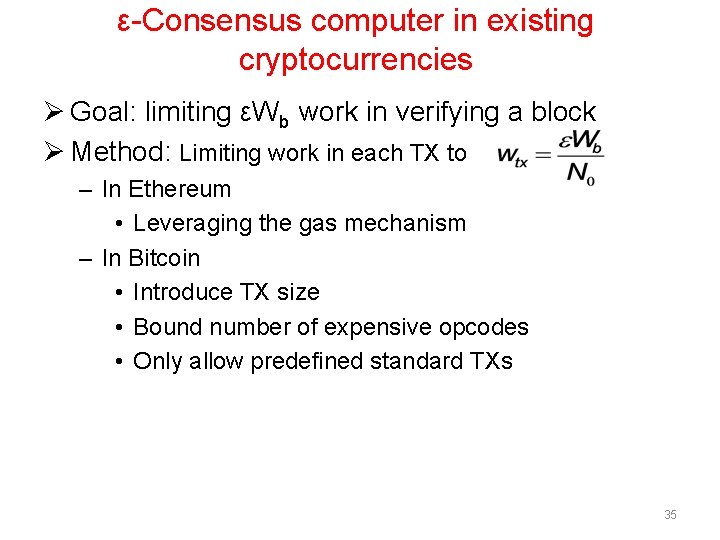
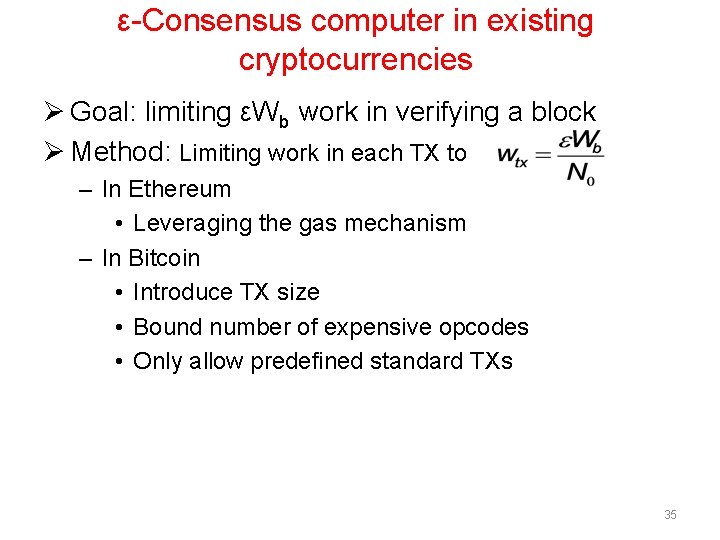
ε-Consensus computer in existing cryptocurrencies Ø Goal: limiting εWb work in verifying a block Ø Method: Limiting work in each TX to – In Ethereum • Leveraging the gas mechanism – In Bitcoin • Introduce TX size • Bound number of expensive opcodes • Only allow predefined standard TXs 35
gas_limit in Ethereum Ø Limit the gas in a block Ø Can be adjusted by miners – Let the “consensus” decide the gas_limit Ø Different miners have different thresholds for gas_limit – Raise gas_limit to above the gas required in the attack – Some miners are vulnerable 36