CRYPTOGRAPHY MANESH JACOB MAR THOMA COLLEGE TIRUVALLA Cryptography
CRYPTOGRAPHY MANESH JACOB MAR THOMA COLLEGE TIRUVALLA




Cryptography is the science of making communications unintelligible to all except authorized parties (sending messages in disguised form so that the intended recipients can remove the disguise and read the message) The fundamental objective of cryptography is to enable two people, usually referred as Alice and Bob, to communicate over an insecure channel in such a way that an opponent, Oscar, cannot understand what is being said.
BASIC NOTIONS PLAINTEXT: - The message we want to send (concealed) is called the plaintext. CIPHERTEXT: - after a transformation in to disguised (secret) form message is called the cipher text. ENCIPHERING or ENCRYPTION: - The process of converting a plaintext to a cipher text is called enciphering or encryption. DECIPHERING or DECRYPTION: - The process of converting a cipher text to a plaintext is called Deciphering or decryption.
BASIC NOTIONS ALPHABET: - The plaintext and cipher text are written in some alphabet consisting of certain number N of letters. LETTER or CHARACTER: - It can refer not only to the familiar A-Z, but also to numerals, blanks, punctuation marks or any other symbols that we allow ourselves to use when writing the messages. MESSAGE UNITS: - A message unit might be a single letter, a pair of letters (digraph), a triple of letters (tri-graph), or a block of 50 letters. The plaintext and cipher text are broken up into message units.
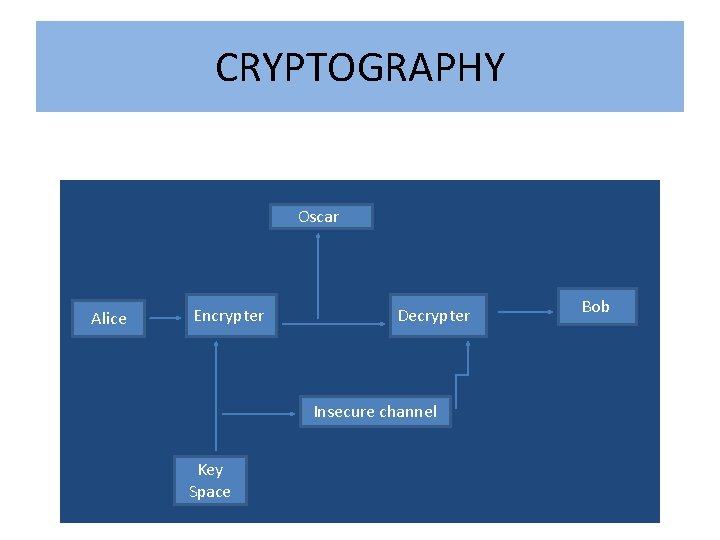
CRYPTOGRAPHY • * Oscar Alice Encrypter Decrypter Insecure channel Key Space Bob
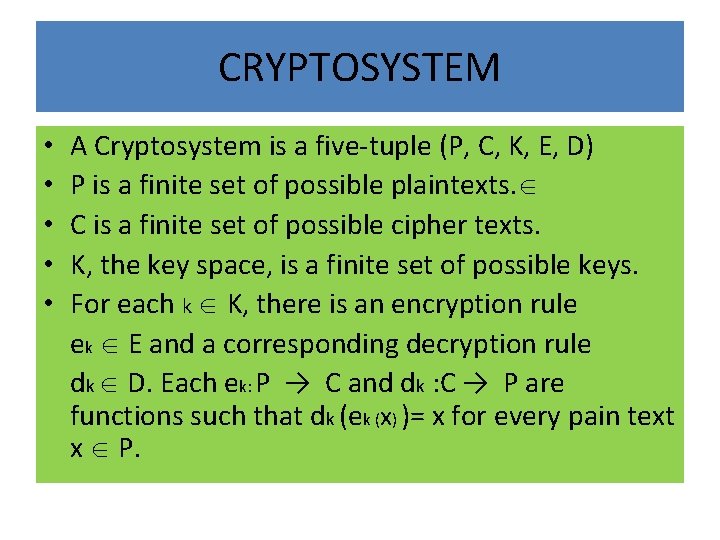
CRYPTOSYSTEM • • • A Cryptosystem is a five-tuple (P, C, K, E, D) P is a finite set of possible plaintexts. C is a finite set of possible cipher texts. K, the key space, is a finite set of possible keys. For each k K, there is an encryption rule ek E and a corresponding decryption rule dk D. Each ek: P → C and dk : C → P are functions such that dk (ek (x) )= x for every pain text x P.
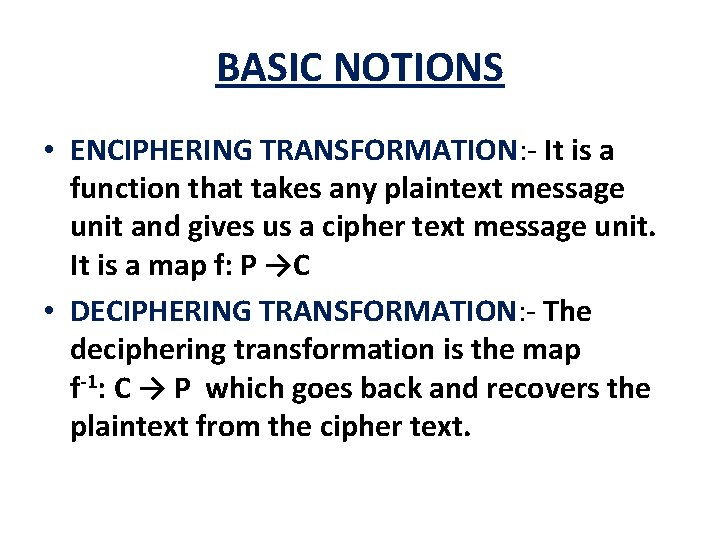
BASIC NOTIONS • ENCIPHERING TRANSFORMATION: - It is a function that takes any plaintext message unit and gives us a cipher text message unit. It is a map f: P →C • DECIPHERING TRANSFORMATION: - The deciphering transformation is the map f-1: C → P which goes back and recovers the plaintext from the cipher text.
SYMMETRIC-KEY CRYPTOSYSTEM • • THE SHIFT CIPHER. THE SUBSTITUTION CIPHER. THE AFFINE CIPHER. THE VIGENERE CIPHER. THE HILL CIPHER. THE PERMUTATION CIPHER. STREAM CIPHER.
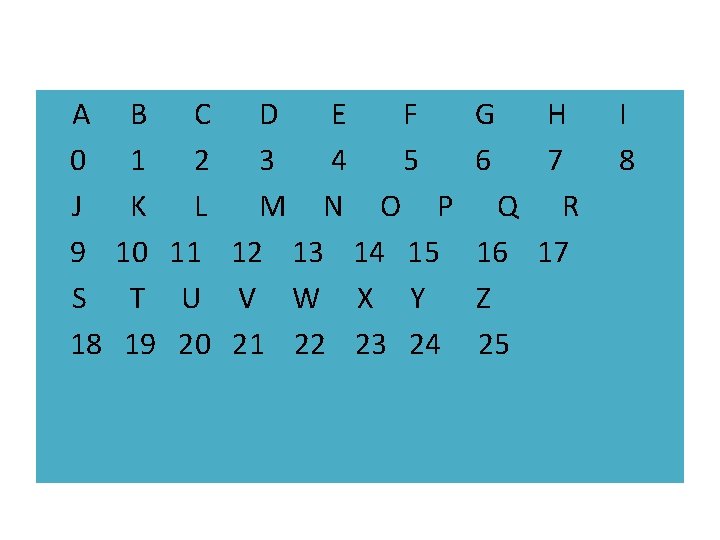
A 0 J 9 S 18 B C D E F 1 2 3 4 5 K L M N O P 10 11 12 13 14 15 T U V W X Y 19 20 21 22 23 24 G 6 H 7 Q R 16 17 Z 25 I 8
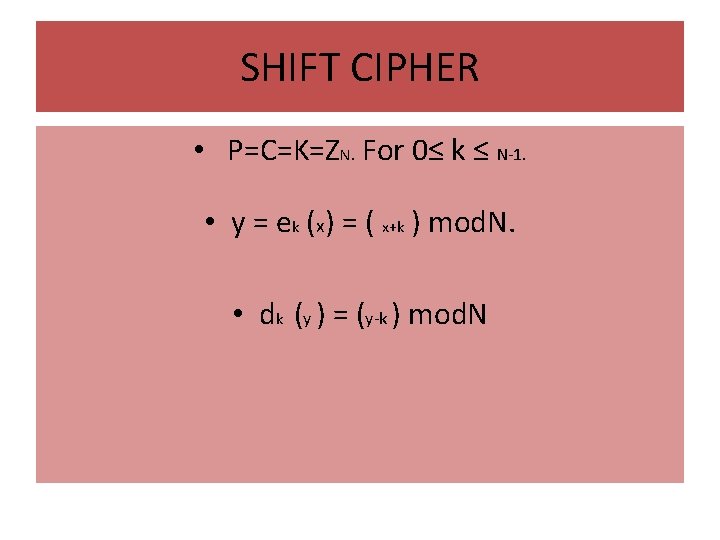
SHIFT CIPHER • P=C=K=ZN. For 0≤ k ≤ N-1. • y = ek (x) = ( x+k ) mod. N. • dk (y ) = (y-k ) mod. N
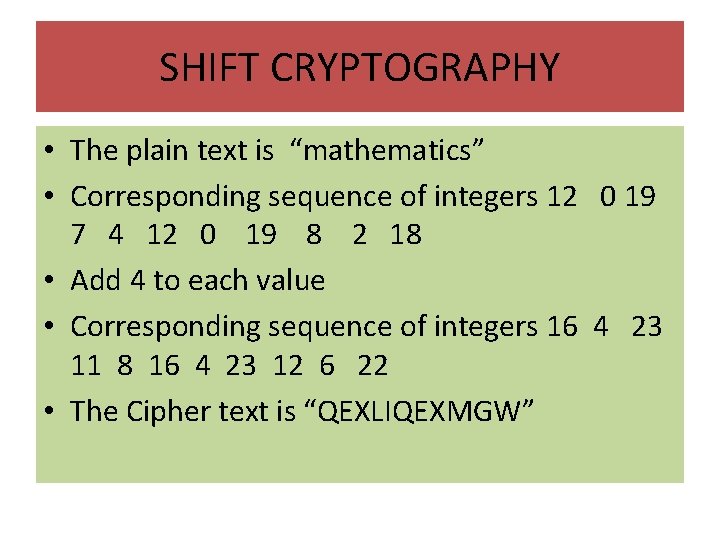
SHIFT CRYPTOGRAPHY • The plain text is “mathematics” • Corresponding sequence of integers 12 0 19 7 4 12 0 19 8 2 18 • Add 4 to each value • Corresponding sequence of integers 16 4 23 11 8 16 4 23 12 6 22 • The Cipher text is “QEXLIQEXMGW”
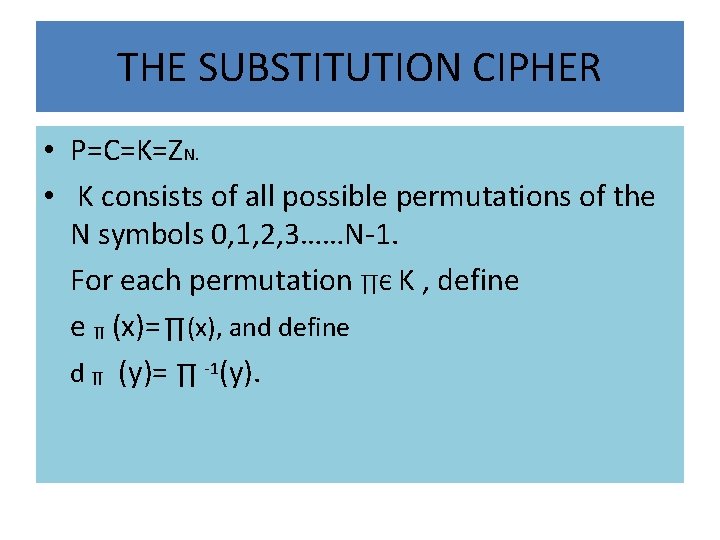
THE SUBSTITUTION CIPHER • P=C=K=ZN. • K consists of all possible permutations of the N symbols 0, 1, 2, 3……N-1. For each permutation ∏Є K , define e ∏ (x)= ∏(x), and define d ∏ (y)= ∏ -1(y).


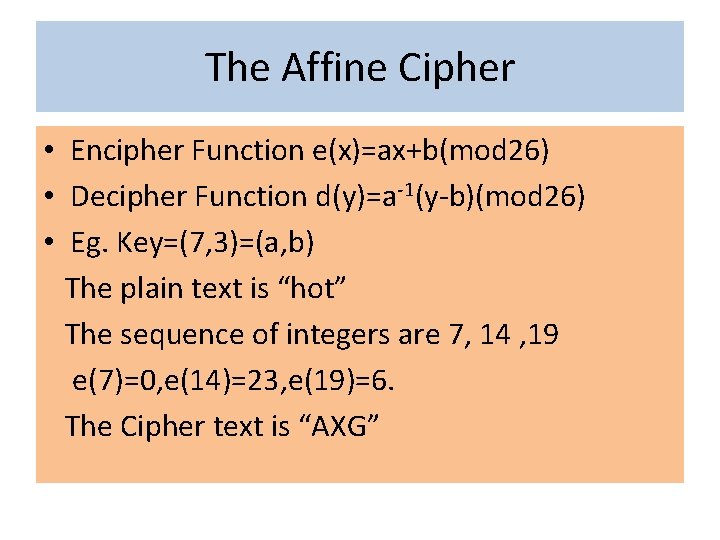
The Affine Cipher • Encipher Function e(x)=ax+b(mod 26) • Decipher Function d(y)=a-1(y-b)(mod 26) • Eg. Key=(7, 3)=(a, b) The plain text is “hot” The sequence of integers are 7, 14 , 19 e(7)=0, e(14)=23, e(19)=6. The Cipher text is “AXG”
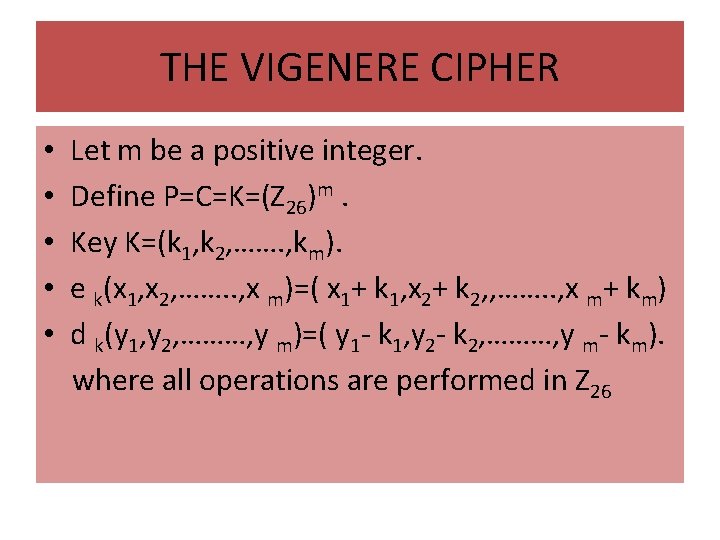
THE VIGENERE CIPHER • • • Let m be a positive integer. Define P=C=K=(Z 26)m. Key K=(k 1, k 2, ……. , km). e k(x 1, x 2, ……. . , x m)=( x 1+ k 1, x 2+ k 2, , ……. . , x m+ km) d k(y 1, y 2, ………, y m)=( y 1 - k 1, y 2 - k 2, ………, y m- km). where all operations are performed in Z 26
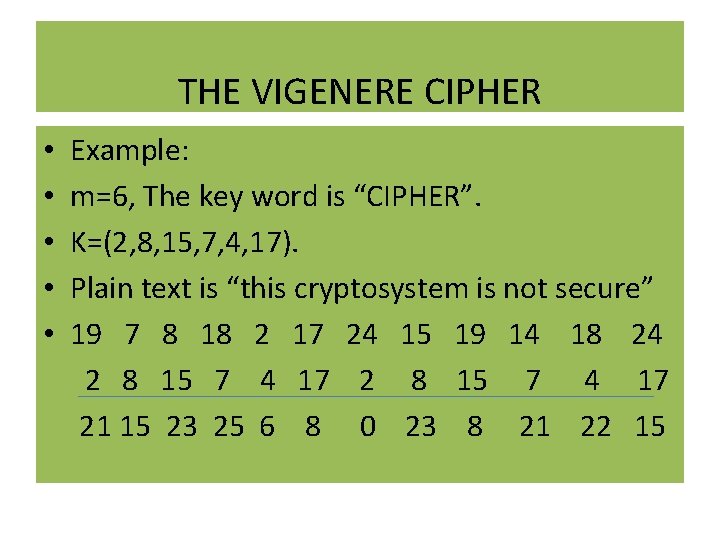
THE VIGENERE CIPHER • • • Example: m=6, The key word is “CIPHER”. K=(2, 8, 15, 7, 4, 17). Plain text is “this cryptosystem is not secure” 19 7 8 18 2 17 24 15 19 14 18 24 2 8 15 7 4 17 21 15 23 25 6 8 0 23 8 21 22 15
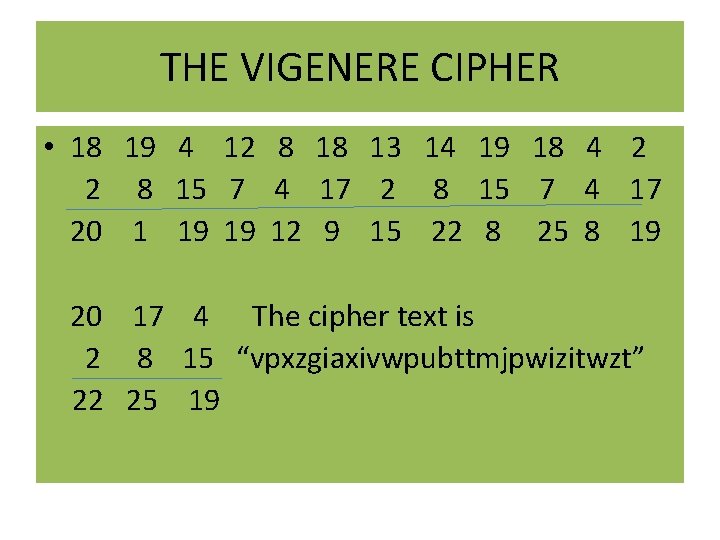
THE VIGENERE CIPHER • 18 19 4 12 8 18 13 14 19 18 4 2 2 8 15 7 4 17 20 1 19 19 12 9 15 22 8 25 8 19 20 17 4 The cipher text is 2 8 15 “vpxzgiaxivwpubttmjpwizitwzt” 22 25 19
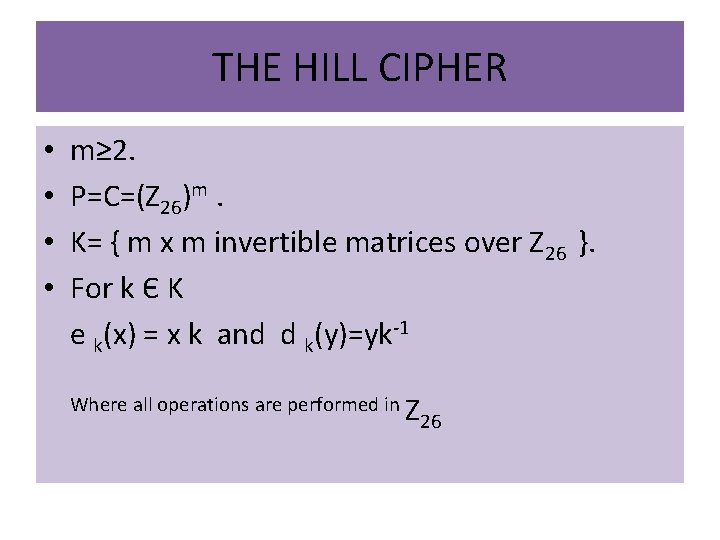
THE HILL CIPHER • • m≥ 2. P=C=(Z 26)m. K= { m x m invertible matrices over Z 26 }. For k Є K e k(x) = x k and d k(y)=yk-1 Where all operations are performed in Z 26
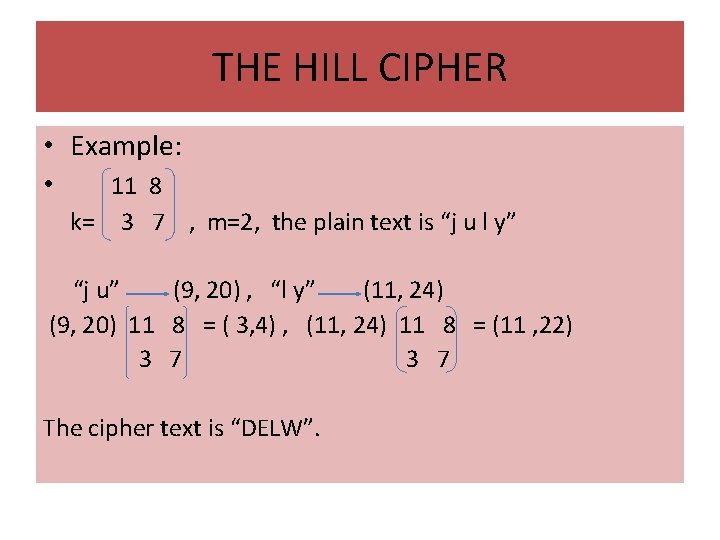
THE HILL CIPHER • Example: • 11 8 k= 3 7 , m=2, the plain text is “j u l y” “j u” (9, 20) , “l y” (11, 24) (9, 20) 11 8 = ( 3, 4) , (11, 24) 11 8 = (11 , 22) 3 7 The cipher text is “DELW”.
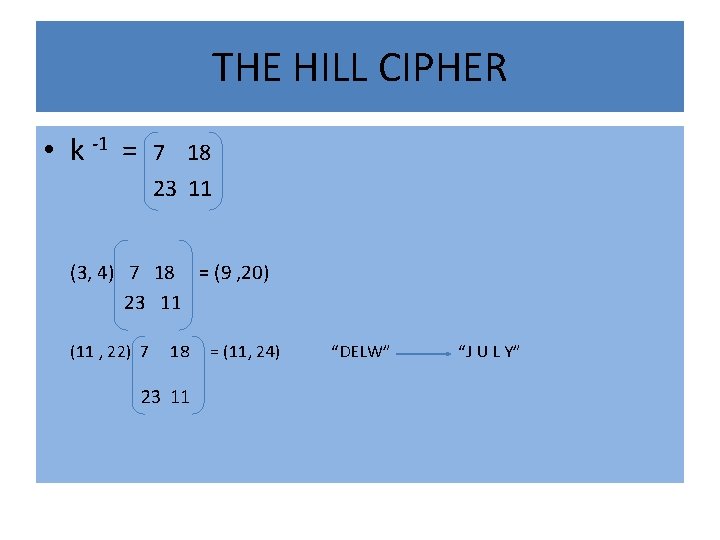
THE HILL CIPHER • k -1 = 7 18 23 11 (3, 4) 7 18 = (9 , 20) 23 11 (11 , 22) 7 18 23 11 = (11, 24) “DELW” “J U L Y”
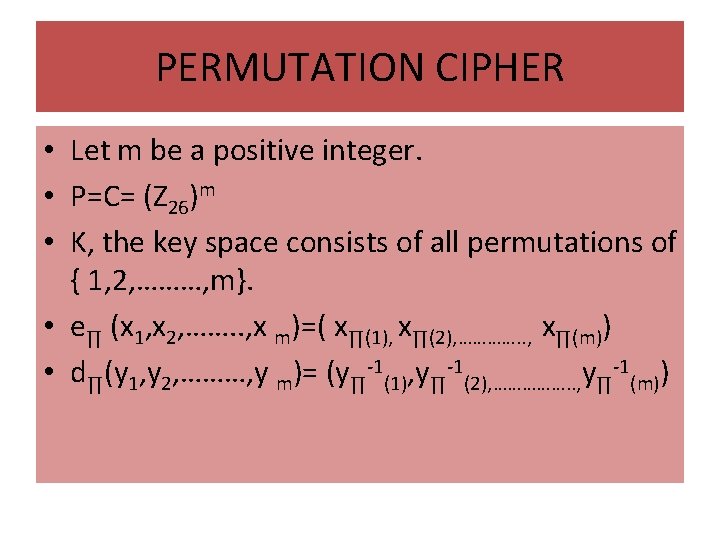
PERMUTATION CIPHER • Let m be a positive integer. • P=C= (Z 26)m • K, the key space consists of all permutations of { 1, 2, ………, m}. • e∏ (x 1, x 2, ……. . , x m)=( x∏(1), x∏(2), …………. . , x∏(m)) • d∏(y 1, y 2, ………, y m)= (y∏-1(1), y∏-1(2), ……………. . , y∏-1(m))
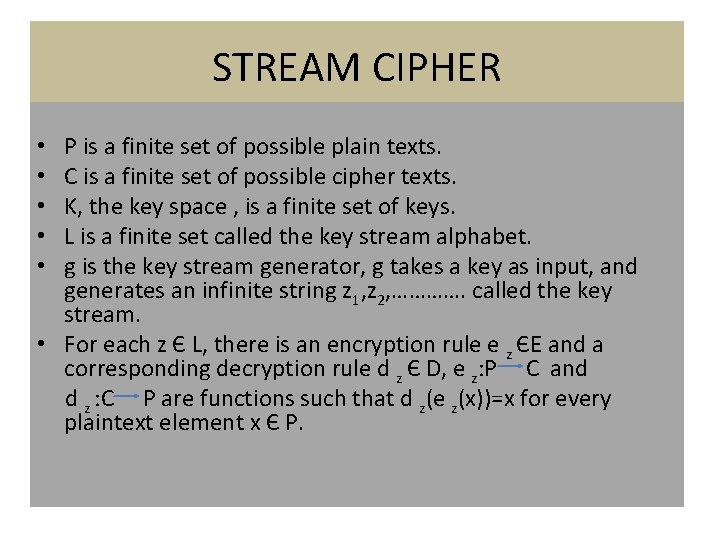
STREAM CIPHER P is a finite set of possible plain texts. C is a finite set of possible cipher texts. K, the key space , is a finite set of keys. L is a finite set called the key stream alphabet. g is the key stream generator, g takes a key as input, and generates an infinite string z 1, z 2, …………. called the key stream. • For each z Є L, there is an encryption rule e z ЄE and a corresponding decryption rule d z Є D, e z: P C and d z : C P are functions such that d z(e z(x))=x for every plaintext element x Є P. • • •
CRYPTANALYSIS • The science of breaking codes is called cryptanalysis. This is the most important part of cryptography. Here, we can decrypt the cipher text to the plain text without knowing the secret key. In this part we use theory of probability, theory of frequency analysis etc.
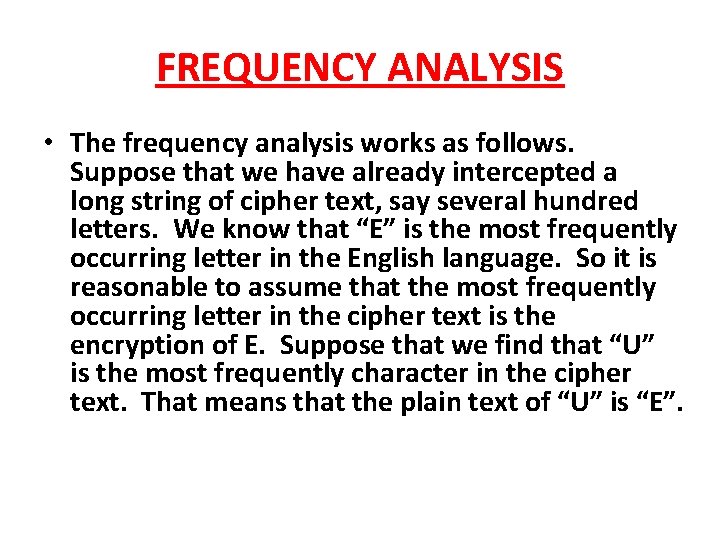
FREQUENCY ANALYSIS • The frequency analysis works as follows. Suppose that we have already intercepted a long string of cipher text, say several hundred letters. We know that “E” is the most frequently occurring letter in the English language. So it is reasonable to assume that the most frequently occurring letter in the cipher text is the encryption of E. Suppose that we find that “U” is the most frequently character in the cipher text. That means that the plain text of “U” is “E”.
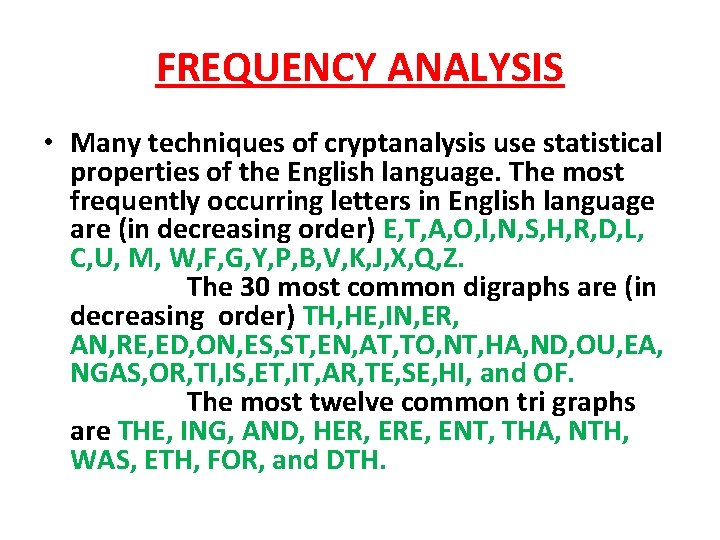
FREQUENCY ANALYSIS • Many techniques of cryptanalysis use statistical properties of the English language. The most frequently occurring letters in English language are (in decreasing order) E, T, A, O, I, N, S, H, R, D, L, C, U, M, W, F, G, Y, P, B, V, K, J, X, Q, Z. The 30 most common digraphs are (in decreasing order) TH, HE, IN, ER, AN, RE, ED, ON, ES, ST, EN, AT, TO, NT, HA, ND, OU, EA, NGAS, OR, TI, IS, ET, IT, AR, TE, SE, HI, and OF. The most twelve common tri graphs are THE, ING, AND, HER, ERE, ENT, THA, NTH, WAS, ETH, FOR, and DTH.
FERMAT’S LITTLE THEOREM • Let p be a prime. Any integer a satisfies ap Ξ a mod p, and any integer a not divisible by p satisfies ap-1 Ξ 1 mod p.
PUBLIC KEY CRYPTOSYSTEM • A public key cryptosystem has the property that someone who known’s only how to encipher cannot use the encipher key to find the deciphering key without a prohibitively lengthy computation.
PUBLIC KEY CRYPTOSYSTEM • In other words the enciphering function f: P→C is easy to compute once the enciphering key KE is known, but it is very hard in practice to compute the inverse f-1: C→P.
PUBLIC KEY CRYPTOSYSTEM • An element k of the key space is really a pair of keys. K = ( kpriv. , kpub) called the private key and the public key respectively, • for each public key kpub there is a corresponding encryption function and for each private key kpriv there is a corresponding decryption function
PUBLIC KEY CRYPTOSYSTEM • The public key cryptosystem is associated with two components, one way function and trapdoor information. • A one way function is an invertible function that is easy to compute, but whose inverse is difficult to compute. • Secure public key cryptosystem one built using one-way functions that have a trapdoor. The trapdoor is a piece of auxiliary information that allows the inverse to be easily computed.



RSA PUBLIC KEY CRYPTOSYSTEM • The RSA Cryptosystem is one of the oldest and most popular public key cryptosystem. • It is based on the tremendous difficulty of factoring. • The inventors of RSA are Ron Rivest, Adi Shamir and Leonard Adleman.
RSA PUBLIC KEY CRYPTOSYSTEM In this cryptosystem each user A chooses two primes p. A and q. A and a random number e. A which has no common factor with(p. A -1)( q. A -1). Next, A computes n. A=p. Aq. A , φ( n. A) = (p. A -1)( q. A -1) = n. A+1 -p. A- q. A and the multiplicative inverse of e. A mod(n. A), let it be d. A. She makes public the enciphering key KE, A = (n. A, e. A) and conceals the deciphering key KD, A = (n. A, d. A).
The enciphering transformation is the map f: Z/n. Z to itself given by f(m) = me(mod n. A). The deciphering transformation is the map f-1 : Z/n. Z to itself given by f-1(C) = Cd(modn. A). A cryptanalyst faces the problem of recovering “C” knowing only (n. A, e. A), the public key. This is called the “RSA Problem”.
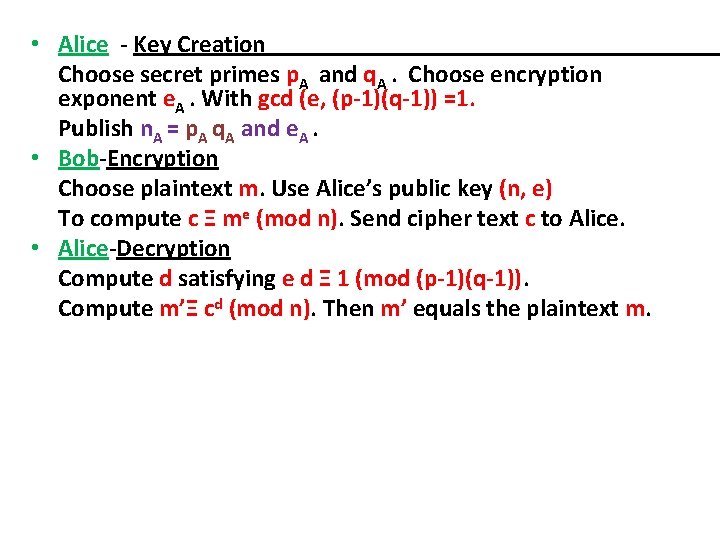
• Alice - Key Creation Choose secret primes p. A and q. A. Choose encryption exponent e. A. With gcd (e, (p-1)(q-1)) =1. Publish n. A = p. A q. A and e. A. • Bob-Encryption Choose plaintext m. Use Alice’s public key (n, e) To compute c Ξ me (mod n). Send cipher text c to Alice. • Alice-Decryption Compute d satisfying e d Ξ 1 (mod (p-1)(q-1)). Compute m’Ξ cd (mod n). Then m’ equals the plaintext m.
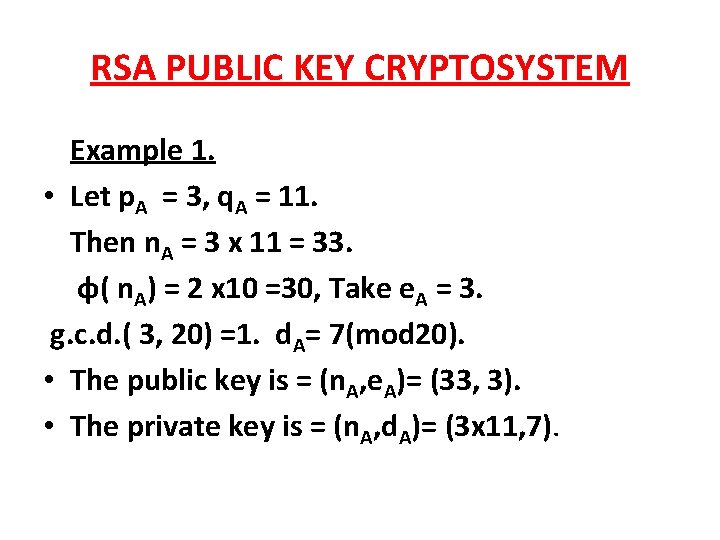
RSA PUBLIC KEY CRYPTOSYSTEM Example 1. • Let p. A = 3, q. A = 11. Then n. A = 3 x 11 = 33. φ( n. A) = 2 x 10 =30, Take e. A = 3. g. c. d. ( 3, 20) =1. d. A= 7(mod 20). • The public key is = (n. A, e. A)= (33, 3). • The private key is = (n. A, d. A)= (3 x 11, 7).
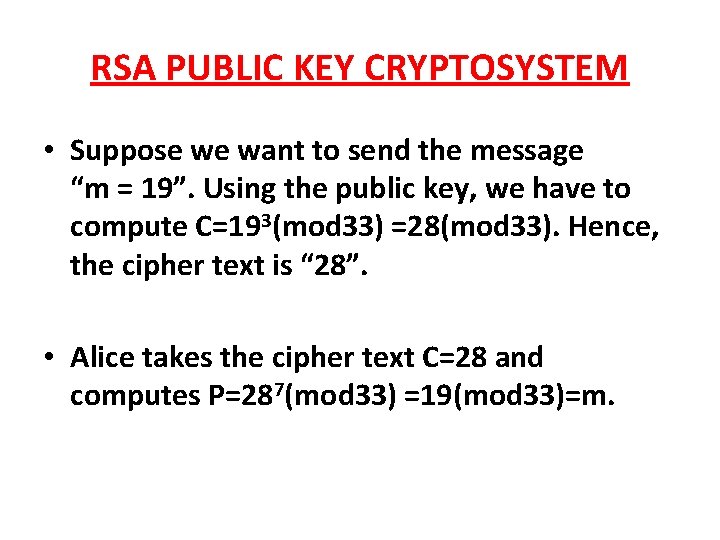
RSA PUBLIC KEY CRYPTOSYSTEM • Suppose we want to send the message “m = 19”. Using the public key, we have to compute C=193(mod 33) =28(mod 33). Hence, the cipher text is “ 28”. • Alice takes the cipher text C=28 and computes P=287(mod 33) =19(mod 33)=m.
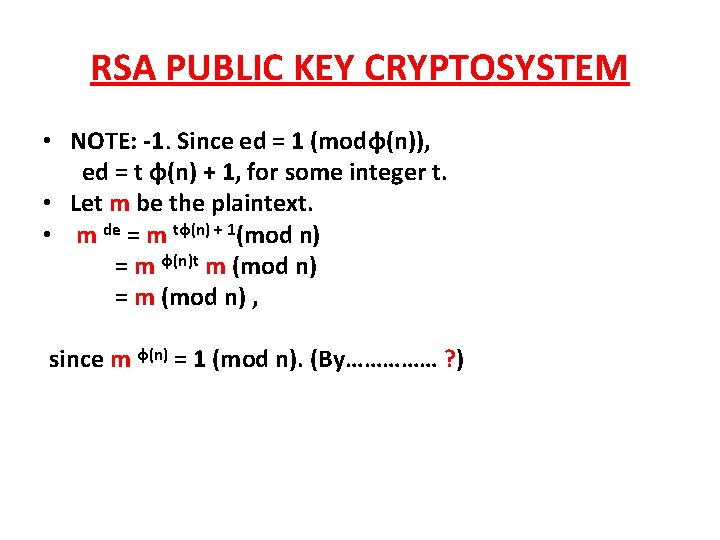
RSA PUBLIC KEY CRYPTOSYSTEM • NOTE: -1. Since ed = 1 (modφ(n)), ed = t φ(n) + 1, for some integer t. • Let m be the plaintext. • m de = m tφ(n) + 1(mod n) = m φ(n)t m (mod n) = m (mod n) , since m φ(n) = 1 (mod n). (By…………… ? )
RSA PUBLIC KEY CRYPTOSYSTEM EXAMPLE 2. • Bob chooses two secret primes p=1223 and q=1987. • Bob computes his public modulus n = p x q = 1223 x 1987 = 2430101 and φ(n)=1222 x 1986 =2426892. • Bob chooses a public encryption exponent e = 948047 with the property that gcd(948047, 2426892) =1.
RSA PUBLIC KEY CRYPTOSYSTEM • public key (n, e) = (2430101, 948047) • Private key ( p x q, d)= (1223 x 1987, 1051235) • Suppose we want to send the message “m = 1070777”. Using the public key, we have to compute C=1070777948047 (mod 2430101) =1473513(mod 2430101). • Hence, the cipher text is “ 1473513”.
RSA PUBLIC KEY CRYPTOSYSTEM • Bob takes the cipher text c=1473513 and computes cd (mod n)= 14735131051235 =1070777(mod 2430101) = m.
RSA PUBLIC KEY CRYPTOSYSTEM • If the RSA cryptosystem is to be secure, it is certainly necessary that n = pq must be large enough that factoring it will be computationally infeasible. • Current factoring algorithms are able to factor numbers having up to 512 bits in their binary representation. • It is generally recommended that, to be on the safe side, one should choose each of p and q to be 512 -bit primes; then n will be a 1024 -bit modulus. • Factoring a number of this size is well beyond the capacity of the best current factoring algorithms.

TRUTH WILL MAKE YOU FREe kochumon 13@gmail. com
- Slides: 51