Applications Computer Networks Spring 2000 John Kristoff 1
![MIME [continued] z. Allows transmission of ybinary data ymultimedia files (video/audio clips) ymultiple types MIME [continued] z. Allows transmission of ybinary data ymultimedia files (video/audio clips) ymultiple types](https://slidetodoc.com/presentation_image_h2/86e49245e58a7bb245b4e06cf7e1b2e5/image-29.jpg)
- Slides: 44
Applications Computer Networks Spring 2000 John Kristoff 1
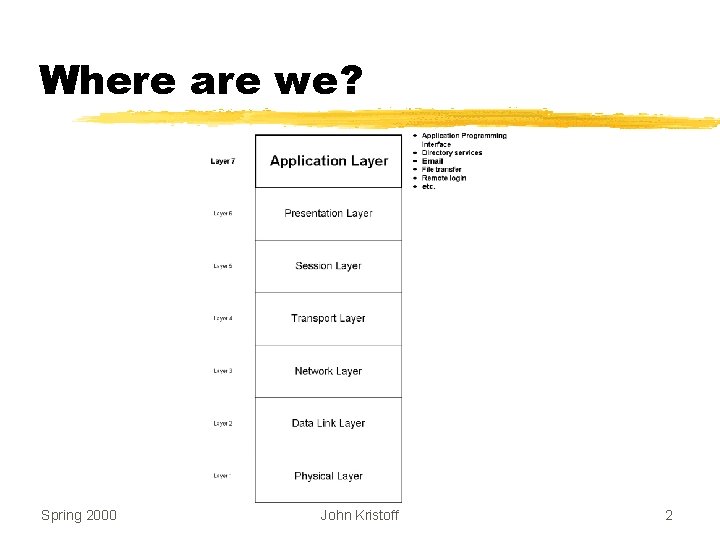
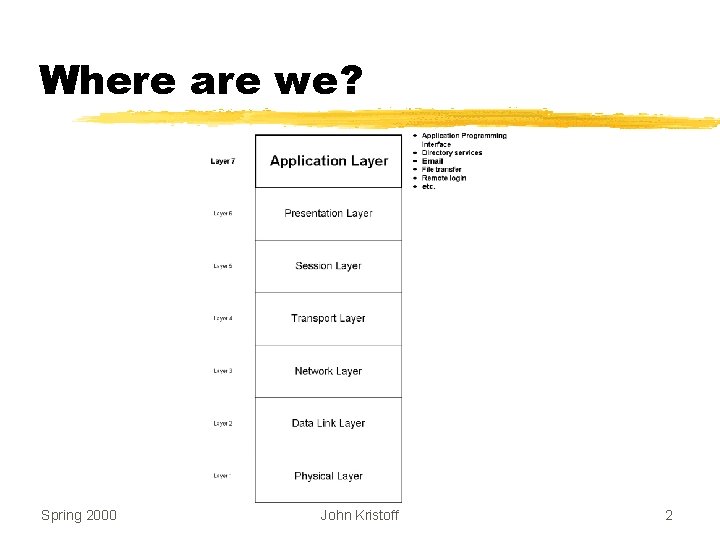
Where are we? Spring 2000 John Kristoff 2
Important Note Although the ISO OSI Reference Model defines a session and presentation layer, they are often integrated into some other layer in practice. In many cases they are simply not used. Spring 2000 John Kristoff 3
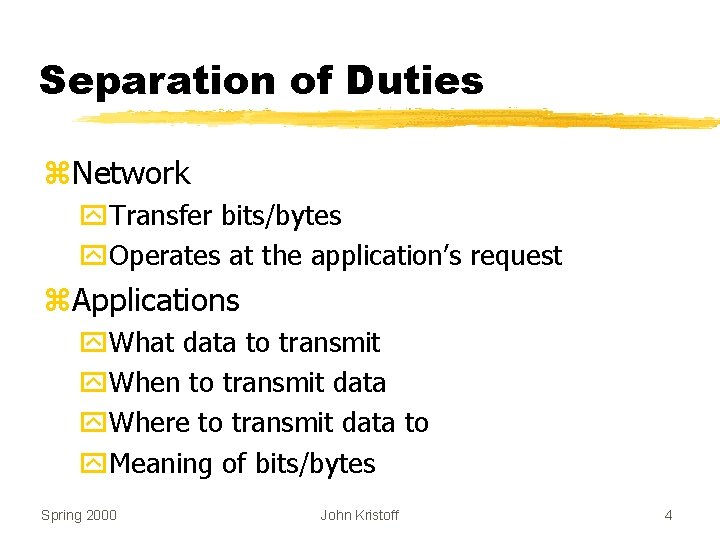
Separation of Duties z. Network y. Transfer bits/bytes y. Operates at the application’s request z. Applications y. What data to transmit y. When to transmit data y. Where to transmit data to y. Meaning of bits/bytes Spring 2000 John Kristoff 4
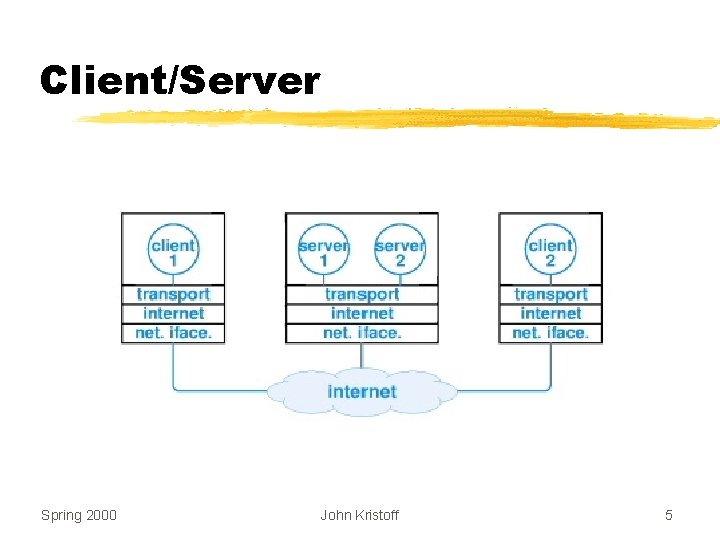
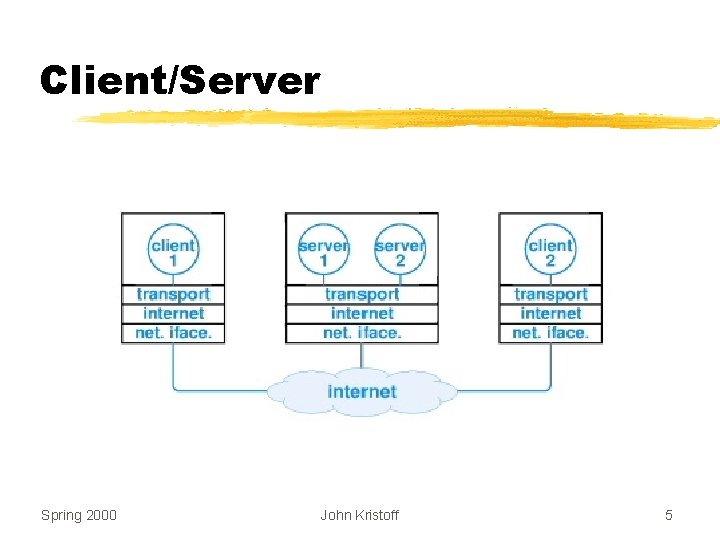
Client/Server Spring 2000 John Kristoff 5
Characteristics z. Client y. Actively initiates contacts with server y. Uses different source port for each connection z. Server y. Passively awaits connections from clients y. Uses the same source port for all clients Spring 2000 John Kristoff 6
Use of Protocol Ports z. Each service given unique port number, P z. Server y. Inform Operating System it is using port P y. Waits for requests to arrive z. Client y. Forms request y. Sends request to port P on server computer Spring 2000 John Kristoff 7
Protocol Ports Key Idea Each application is assigned a unique port identifier. A server must specify the identifier when it begins execution (application startup). A client must specify the identifier when it requests the network software to contact the server. Protocol software on the server computer uses the identifier to direct incoming requests to the correct server application. Spring 2000 John Kristoff 8
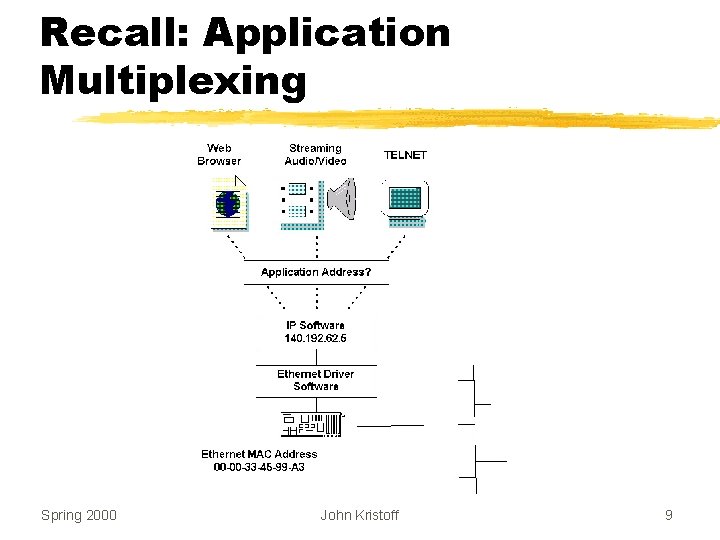
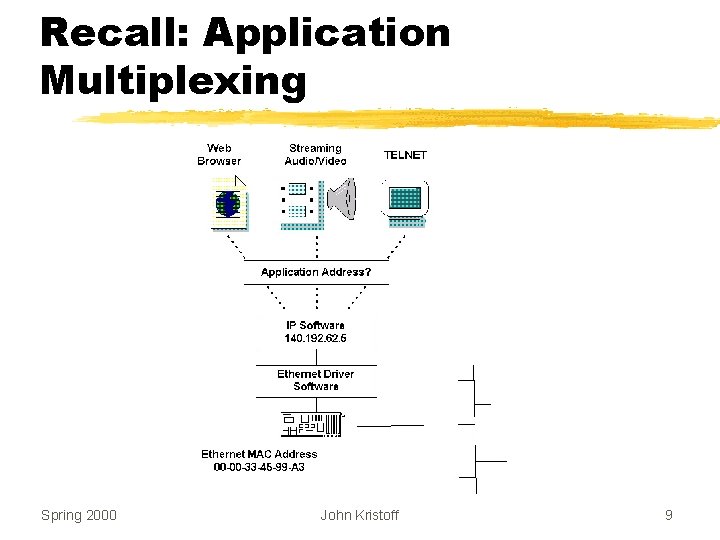
Recall: Application Multiplexing Spring 2000 John Kristoff 9
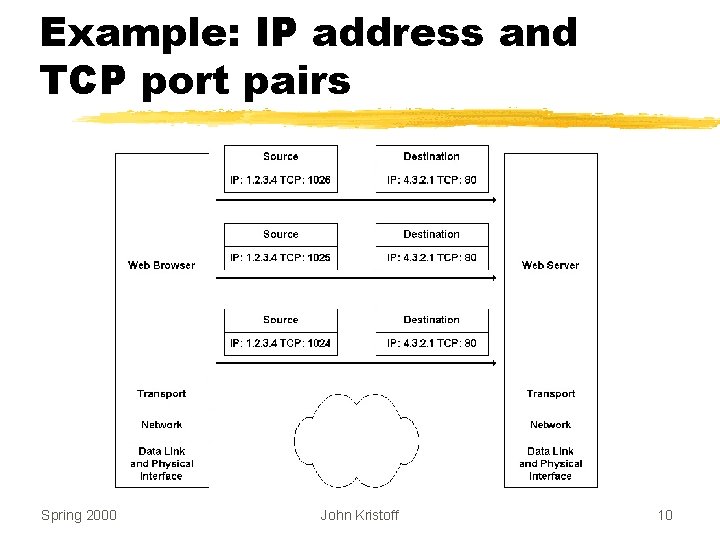
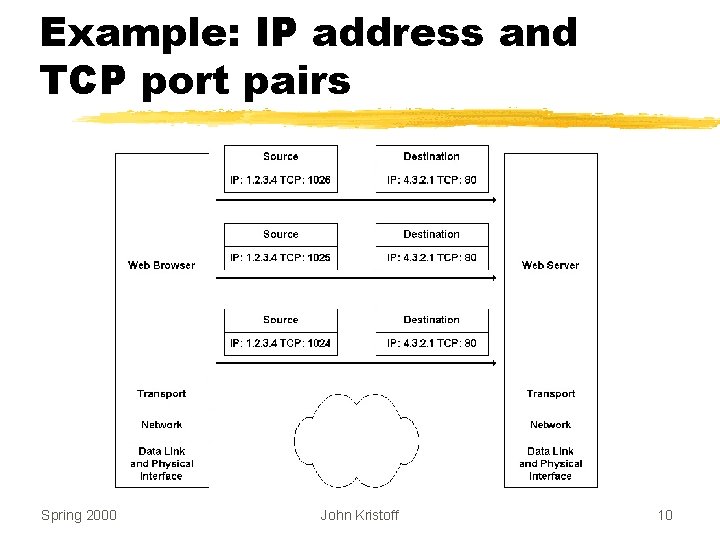
Example: IP address and TCP port pairs Spring 2000 John Kristoff 10
Interacting with Protocol Software z. Client or server uses transport protocols z. Protocol software resides in OS z. Applications outside the OS z. Mechanism to bridge the two y. Application Programming Interface (API) z The book: TCP/IP Illustrated, Volume 2 - Stevens Spring 2000 John Kristoff 11
Application Programming Interface z. Part of the operating system z. Permits applications to use protocols z. Defines y. Operations allowed y. Arguments for each operation Spring 2000 John Kristoff 12
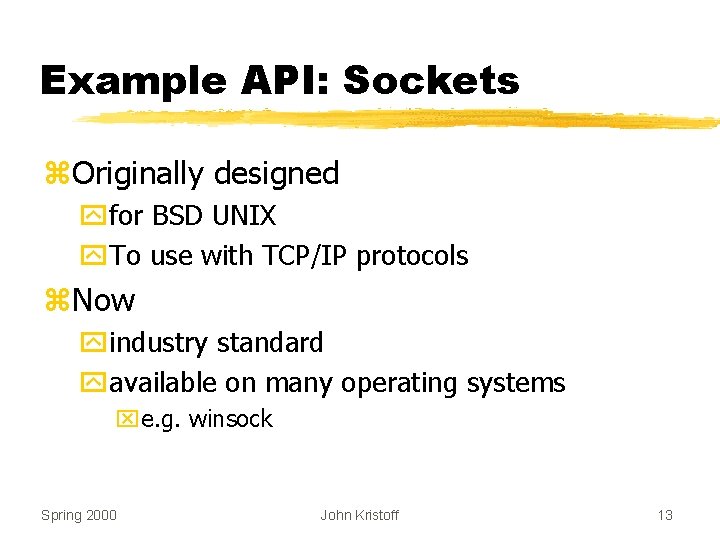
Example API: Sockets z. Originally designed yfor BSD UNIX y. To use with TCP/IP protocols z. Now yindustry standard yavailable on many operating systems xe. g. winsock Spring 2000 John Kristoff 13
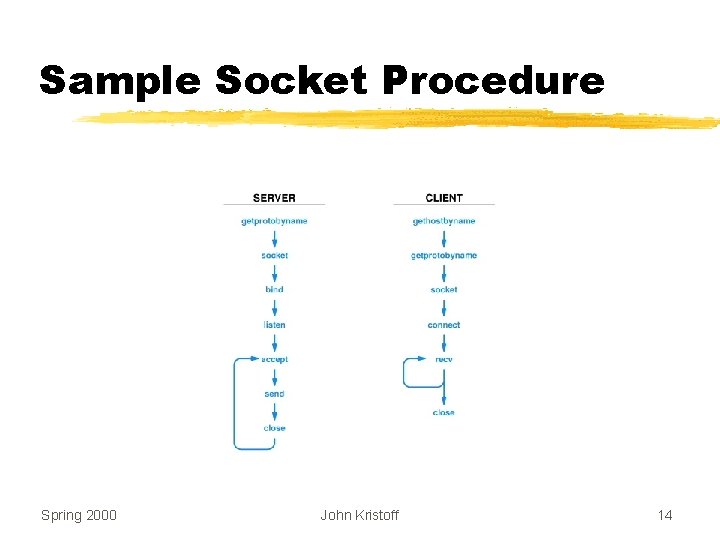
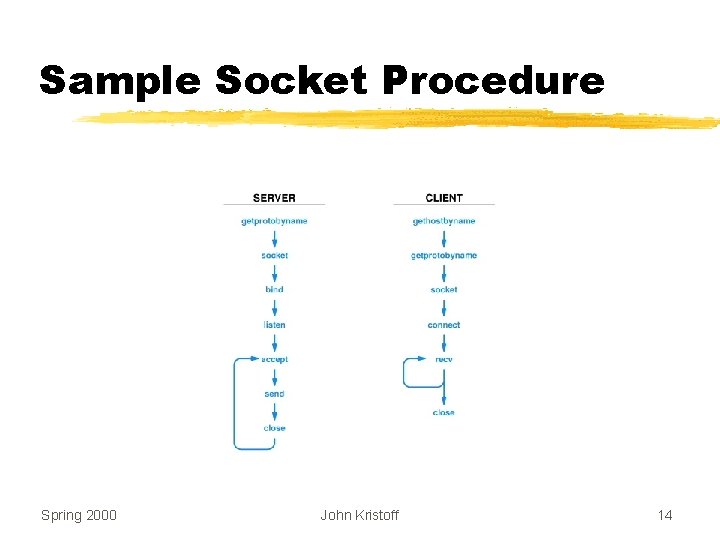
Sample Socket Procedure Spring 2000 John Kristoff 14
Example Application: DNS z Internet communication requires IP addresses z Humans prefer to use computer names z Automated system available to translate names to addresses z Known as Domain Name System (DNS) z Base specs in RFC 1034 and RFC 1035 z The book: DNS and Bind - Albitz and Liu Spring 2000 John Kristoff 15
DNS Functionality z. Given y. Name of a computer z. Return y. Computer’s internet (IP) address z. Method y. Distributed lookup y. Client contact server(s) as necessary Spring 2000 John Kristoff 16
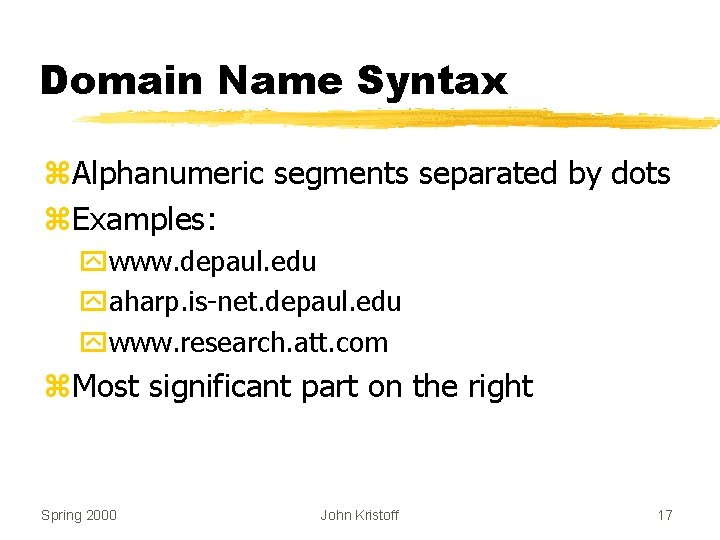
Domain Name Syntax z. Alphanumeric segments separated by dots z. Examples: ywww. depaul. edu yaharp. is-net. depaul. edu ywww. research. att. com z. Most significant part on the right Spring 2000 John Kristoff 17
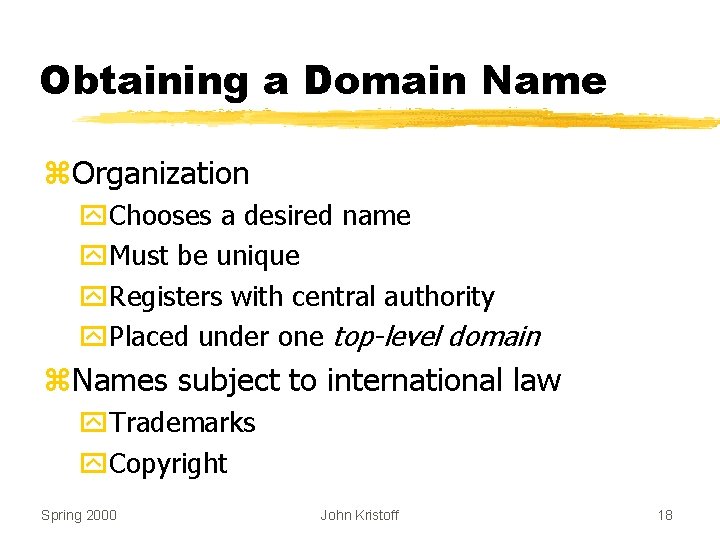
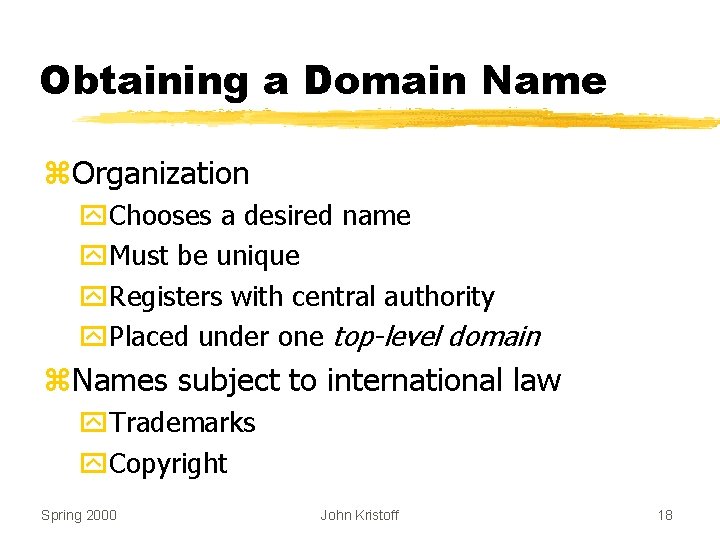
Obtaining a Domain Name z. Organization y. Chooses a desired name y. Must be unique y. Registers with central authority y. Placed under one top-level domain z. Names subject to international law y. Trademarks y. Copyright Spring 2000 John Kristoff 18
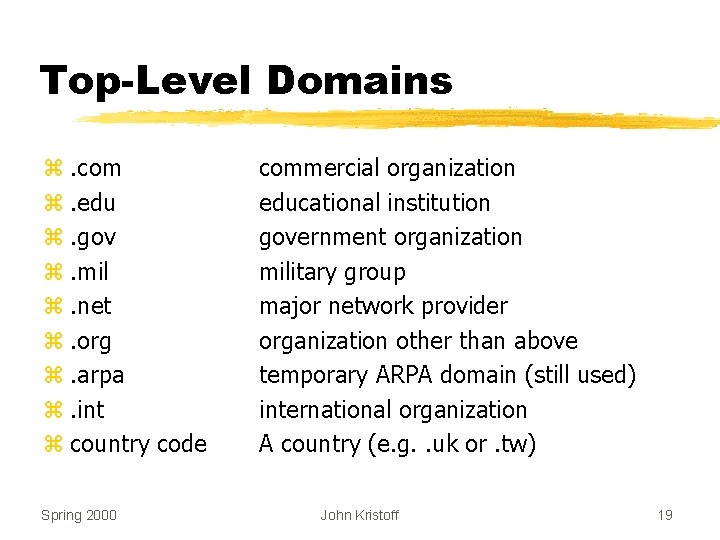
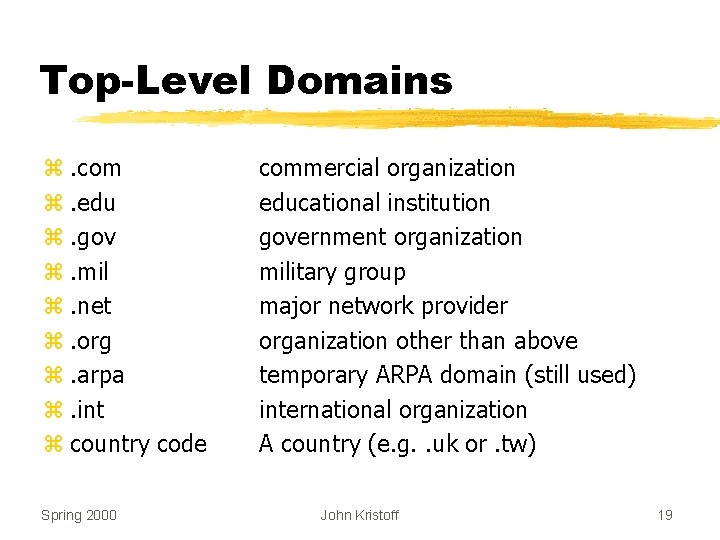
Top-Level Domains z. com z. edu z. gov z. mil z. net z. org z. arpa z. int z country code Spring 2000 commercial organization educational institution government organization military group major network provider organization other than above temporary ARPA domain (still used) international organization A country (e. g. . uk or. tw) John Kristoff 19
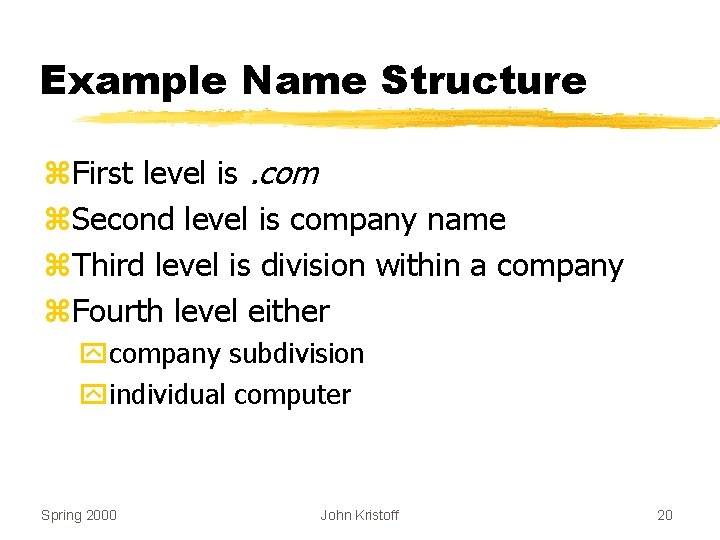
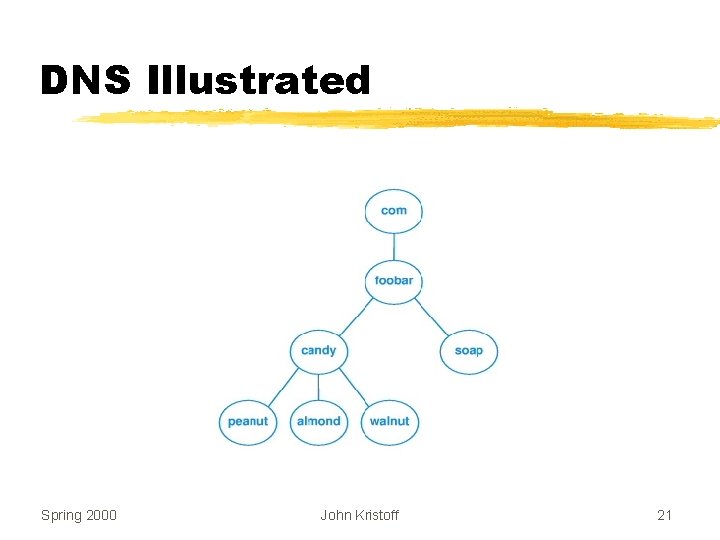
Example Name Structure z. First level is. com z. Second level is company name z. Third level is division within a company z. Fourth level either ycompany subdivision yindividual computer Spring 2000 John Kristoff 20
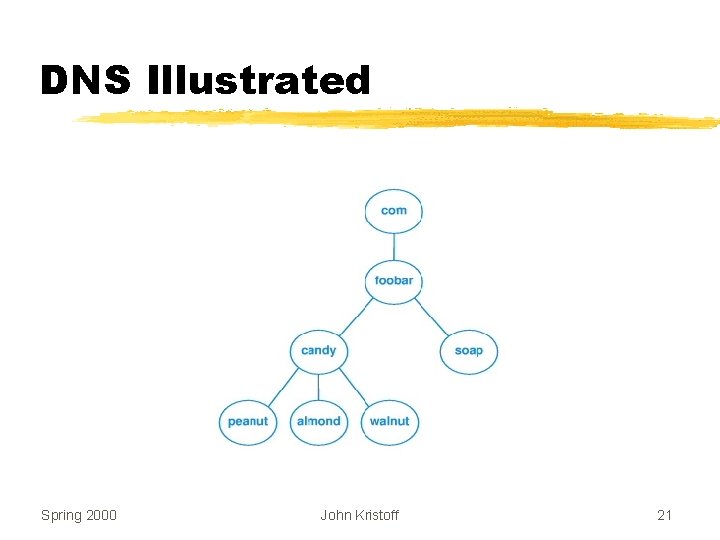
DNS Illustrated Spring 2000 John Kristoff 21
Key Concept The number of segments in a domain name corresponds to the naming hierarchy. There is no universal standard for this hierarchy; each organization can choose its own naming convention. Furthermore, names within an organization do not need to follow a uniform pattern; individual groups within the organization can choose a hierarchical structure that is appropriate for that group. Spring 2000 John Kristoff 22
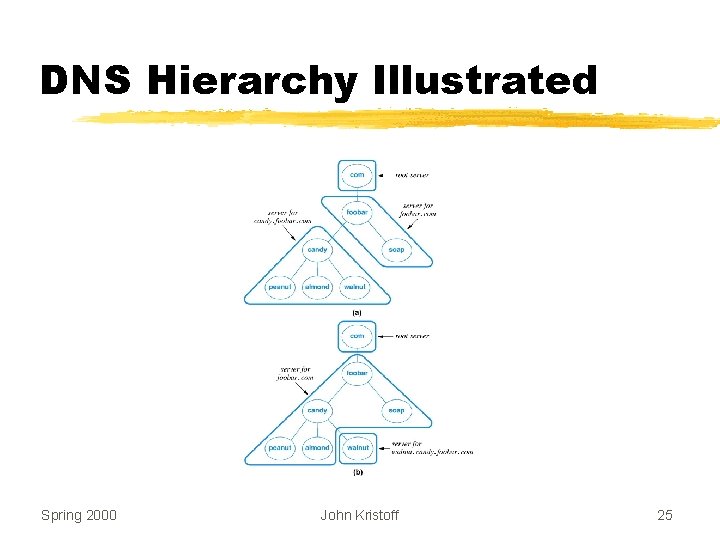
DNS Client/Server Interaction z. Client known as resolver z. Multiple DNS servers used z. Arranged in a hierarchy z. Each server corresponds to contiguous part of naming hierarchy Spring 2000 John Kristoff 23
Inter-Server Links All domain name servers are linked together to form a unified system. Each server knows how to reach a root server and how to reach servers that are authorities for names further down the hierarchy. Spring 2000 John Kristoff 24
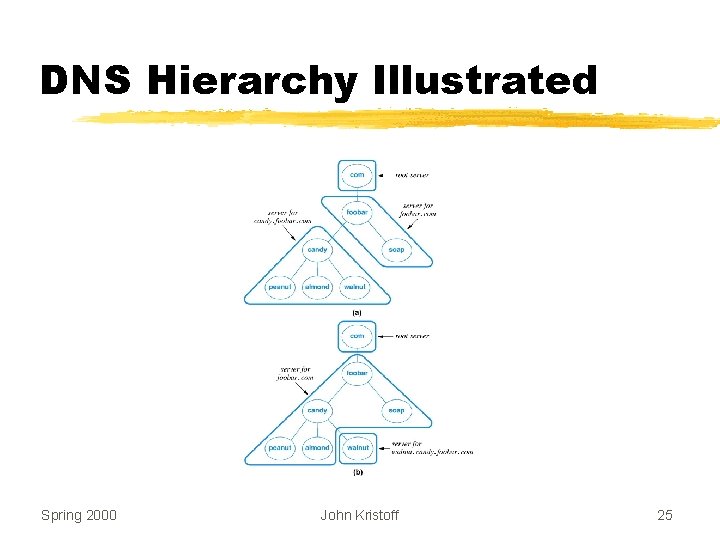
DNS Hierarchy Illustrated Spring 2000 John Kristoff 25
DNS Record Types z. Stored with each name z. Resolver must specify the type in lookup request y Type A (address): IP address for name y Type MX (mail exchanger): IP address of mail server for the name y Type CNAME (Computer Name): alias to another name Spring 2000 John Kristoff 26
Example Application: Internet Email z. Email address ytext string which specifies destination mailbox ye. g. jtk@depaul. edu, jtk@aharp. is-net. depaul. edu z. Mail message format yheader xidentifies sender, receiver, contents xformat is keyword: information yblank line ybody Spring 2000 John Kristoff 27
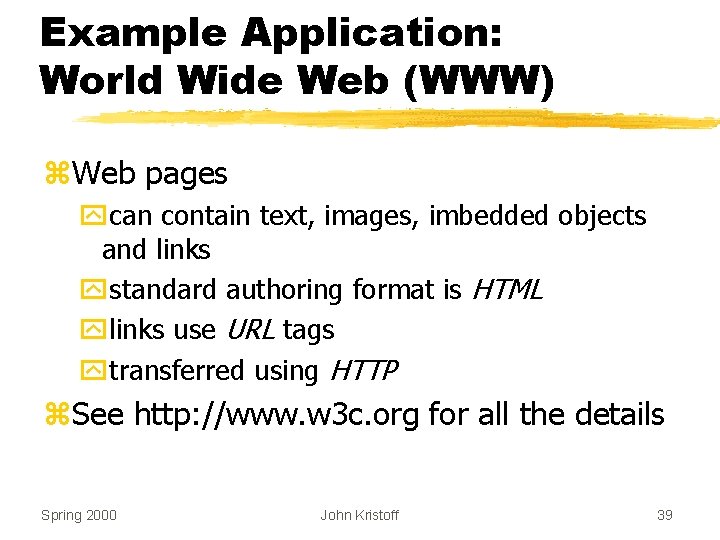
MIME z. Original email restricted to ASCII text z. Users desire to send yimage files yaudio clips ycompiled (binary) programs z. Solution y. Multi-purpose Internet Mail Exchange (MIME) y. Defined in RFC 1521 and RFC 1522 Spring 2000 John Kristoff 28
![MIME continued z Allows transmission of ybinary data ymultimedia files videoaudio clips ymultiple types MIME [continued] z. Allows transmission of ybinary data ymultimedia files (video/audio clips) ymultiple types](https://slidetodoc.com/presentation_image_h2/86e49245e58a7bb245b4e06cf7e1b2e5/image-29.jpg)
MIME [continued] z. Allows transmission of ybinary data ymultimedia files (video/audio clips) ymultiple types in a single message ymixed formats z. Backward compatible Spring 2000 John Kristoff 29
MIME Encoding z Sender yinserts additional header lines yencodes binary data in (printable) ASCII z Sent like standard message z Receiver yinterprets header lines y. Extracts and decodes parts z Separate standards for content and encoding Spring 2000 John Kristoff 30
MIME Example z. Header lines added MIME-Version: 1. 0 Content-Type: Multipart/Mixed; Boundary=xxxsep z. Specifies y. Using MIME version 1. 0 y. Line xxxsep appears before each message part Spring 2000 John Kristoff 31
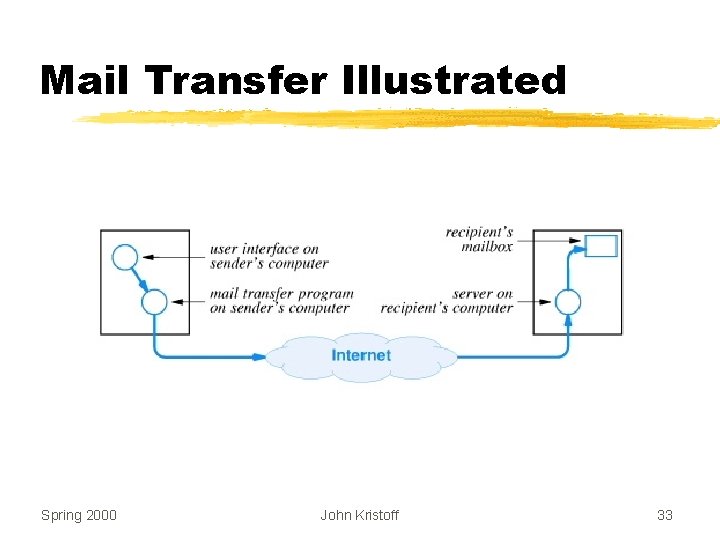
Simple Mail Transfer Protocol (SMTP) z Runs on top of TCP z Used between y. Mail transfer program on sender’s computer y. Mail server on recipient’s computer z Specifies how y. Client interacts with server y. Recipients specified y. Message is transferred z Defined in RFC 821 Spring 2000 John Kristoff 32
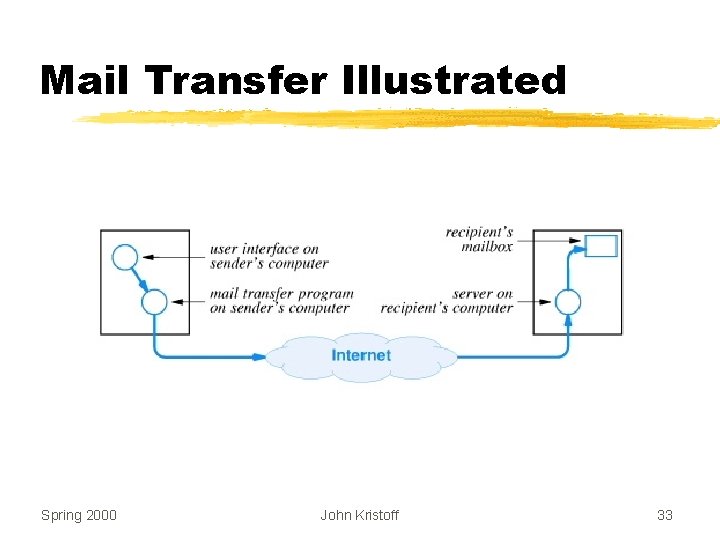
Mail Transfer Illustrated Spring 2000 John Kristoff 33
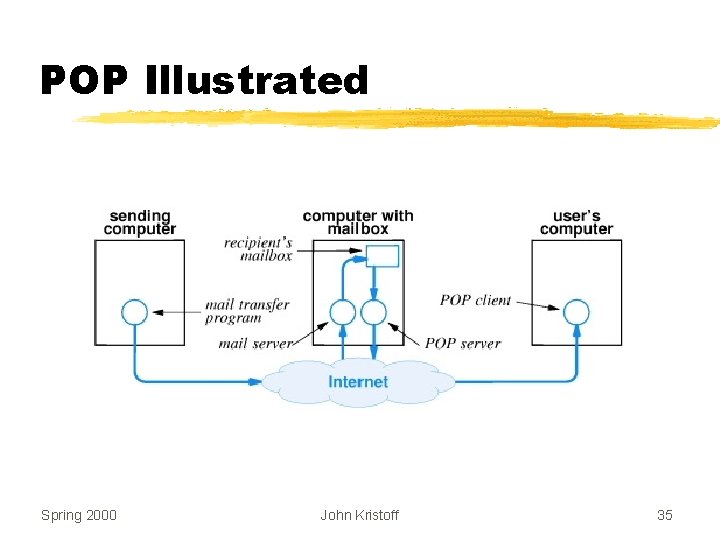
Computers Without Mail Servers (SMTP) z. Typically ysmall, personal computer ynot continuously connected to the network z. To receive email, user must yestablish mailbox on large computer (server) yaccess mailbox as necessary z. Post Office Protocol (POP) often used ydefined in RFC 1939 Spring 2000 John Kristoff 34
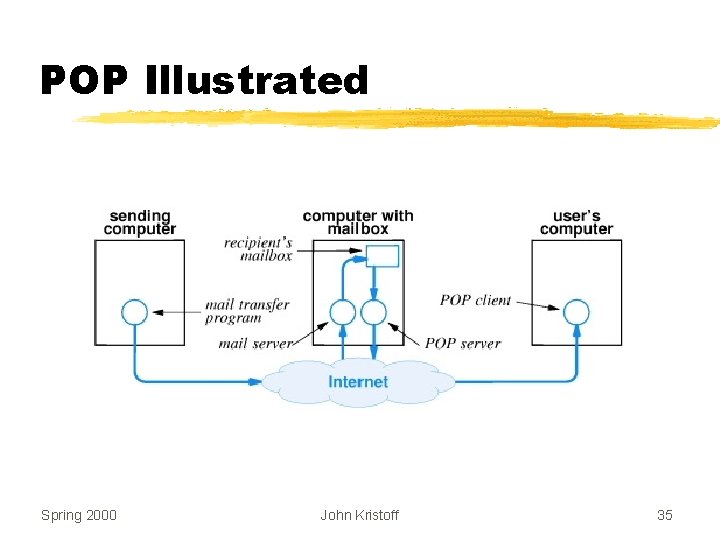
POP Illustrated Spring 2000 John Kristoff 35
Example Application: Remote Login w/ TELNET z Provides interactive access to computer from a remote site z Text-oriented interface z User y invokes client y specifies remote computer z Client y forms TCP connection to server y passes keystrokes over connection y displays output on screen z Defined in RFC 854 Spring 2000 John Kristoff 36
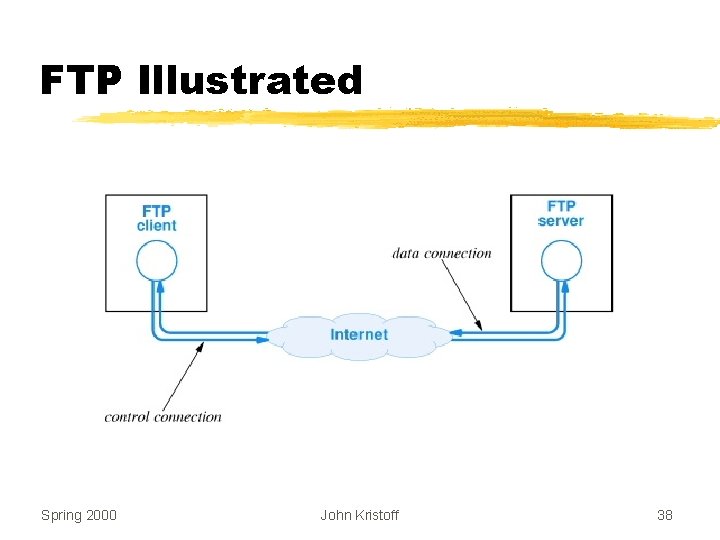
Example Application: File Transfer Protocol (FTP) z. Complete file copy z. Uses TCP z. Supports binary or text file transfers z. Large set of commands z. Until 1995, it was the major source of packets on the Internet z. Defined in RFC 959 Spring 2000 John Kristoff 37
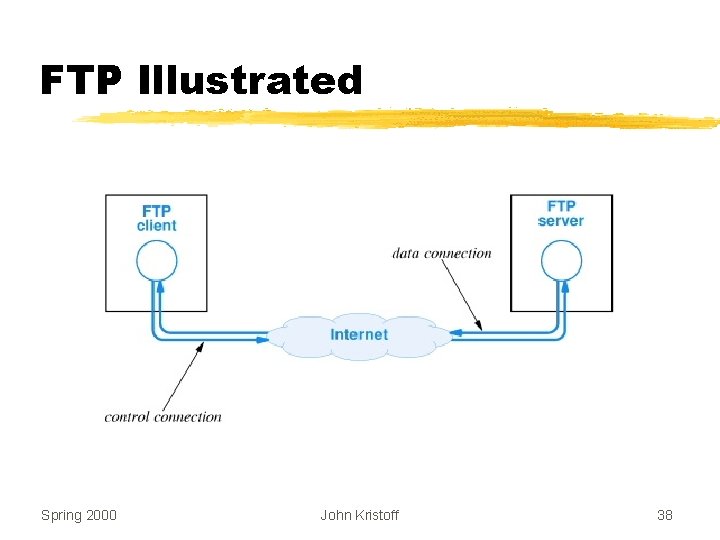
FTP Illustrated Spring 2000 John Kristoff 38
Example Application: World Wide Web (WWW) z. Web pages ycan contain text, images, imbedded objects and links ystandard authoring format is HTML ylinks use URL tags ytransferred using HTTP z. See http: //www. w 3 c. org for all the details Spring 2000 John Kristoff 39
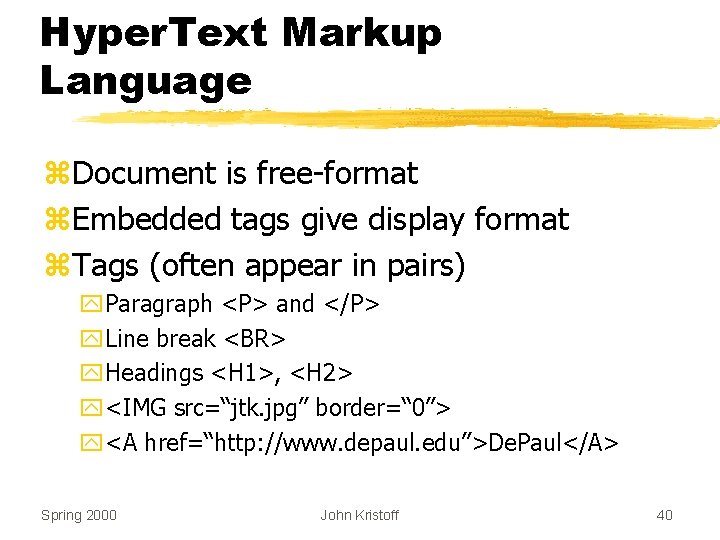
Hyper. Text Markup Language z. Document is free-format z. Embedded tags give display format z. Tags (often appear in pairs) y. Paragraph <P> and </P> y. Line break <BR> y. Headings <H 1>, <H 2> y<IMG src=“jtk. jpg” border=“ 0”> y<A href=“http: //www. depaul. edu”>De. Paul</A> Spring 2000 John Kristoff 40
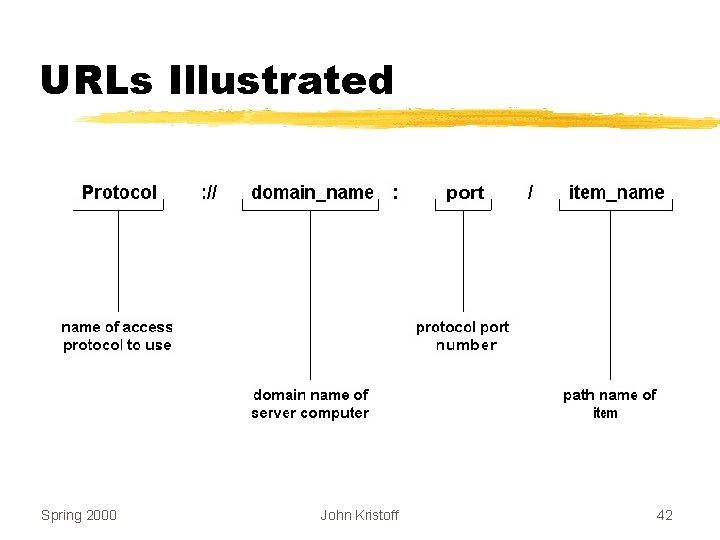
Uniform Resource Locator (URL) z. Symbolic representation z. Embedded in HTML document z. Browser yhides text of link from user yassociates link with item on page ymakes items selectable Spring 2000 John Kristoff 41
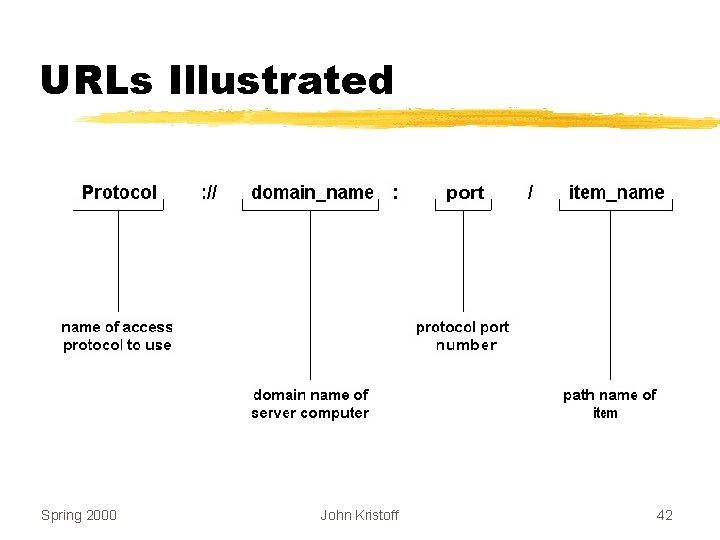
URLs Illustrated Spring 2000 John Kristoff 42
Hyper. Text Transfer Protocol (HTTP) z. Web server makes web pages available z. Server uses port 80 by default z. Web client (browser) requests pages z. Creates a TCP connection to server z. HTTP sits on top of TCP z. HTTP v 1. 1 defined in RFC 2068 y major enhancement over v 1. 0: single TCP connection for multiple HTTP requests Spring 2000 John Kristoff 43
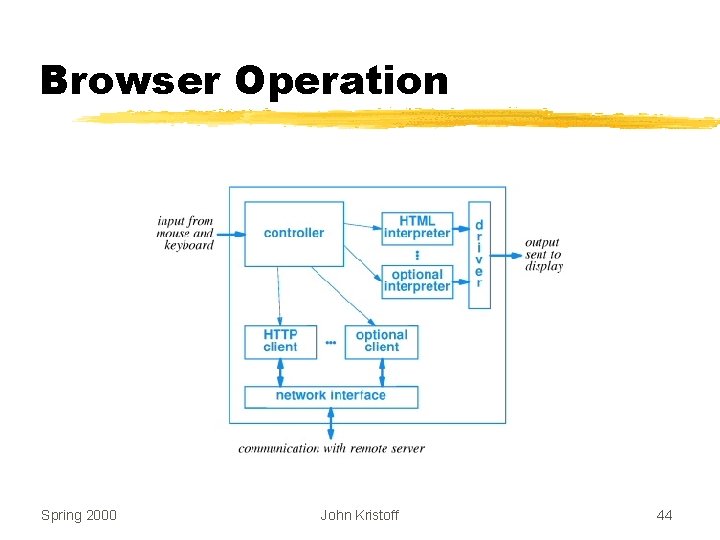
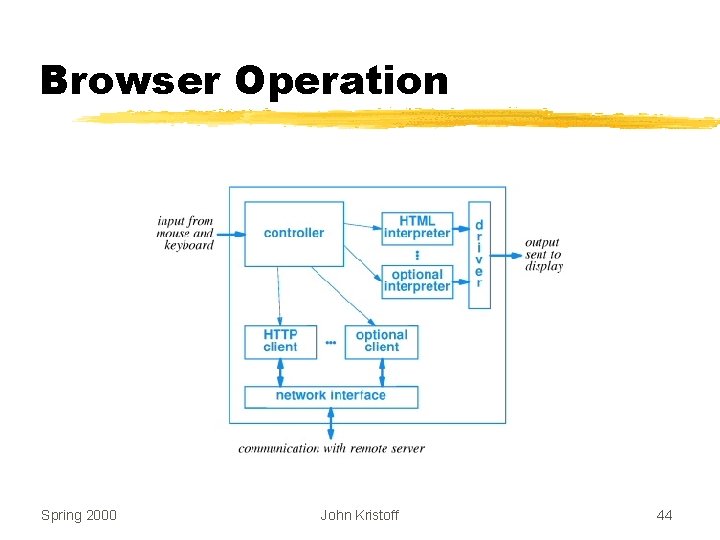
Browser Operation Spring 2000 John Kristoff 44