Agenda Welcome and Introductions Information Security Policy Update


- Slides: 23
Agenda Welcome and Introductions Information Security Policy Update IT Information Updates Workstation Lifecycle Replacement Student Printing Pilot HEAF Improvements Current & Upcoming Projects Open Discussion/New Business
Information Security Policy Update ØSecurity Policy – 4. 197 § Addresses TAC 202 C and NIST 800 -53 § 329 Controls (Moderate, High) § 115 Controls (Low) § Information Security Handbook – Summer 17 § Data Classification (Confidential, Sensitive, Public) § Information Resources Usage and Policy Agreement § Acceptable Usage
Information Security Risk Assessment Ø A systematic process of evaluating the potential risks that may be involved in a projected activity or undertaking and assessing potential organizational impacts. § Identification § Hazards § Assets at Risk § Impacts § Yearly Activity § Completed with Data Owners § Mitigation Plans Based On Findings
Information Security Awareness ØSecurity Awareness § Yearly Training for 2016 § 99 Day Campaign § Second Chance § Account Lock § Ongoing – Simulated Phishing § Mar 17 – 3. 5% § Apr 17 – 8. 2% § May 17 – 9. 2 % § Jun 17 – 6% § Jul 17 – 4. 9% § Aug 17 – 3. 4% § Ongoing – Info. Security Alerts § 2017 Security Awareness Training § Aug 26 th – Dec 15 th (111 Days) § Information Resources Use and Policy Agreement
Information Security Email ØEmail § Inbound Filtering § URL § Malicious Code § Block lists § Volume § 30 Day Inbound – 3. 7 M, 3. 3 M Blocked § 30 Day Outbound – 114. 5 K § Encryption § 30 Day Inbound – 58. 5% § 30 Day Inbound – 80. 3%
Information Security Infrastructure Ø Internet Immunization Project § Global Cyber Alliance § Sanitized DNS § Blocks Known Bad Actors Ø Dynamic Threat Blocklists § Firewall Based § Lists Updated Daily Ø Vulnerability Blocklists § Firewall Based § Lists Updated Hourly § Blocks Threats Based On Severity Ø Information Sharing § MS-ISAC § REN-ISAC § DHS Stop. Think. Connect. § SANS Institute
Information Security 2017 Trends Ø 2016 Perspective – Low Lights § 3000 Data Breaches § 2. 2 Billion Records Exposed § Yahoo Breach Made Public - 1. 5 Billion User Accounts Exposed Ø 2017 Trends § Nation State Hacking – Russia, China, Iran, North Korea § Disruptive and Attention Seeking Groups § For Profit Cybercrime – Made To Order Malware § Cheap, Devastating § Designed To Be Monetized § Hacktivism – Anonymous, ANT, Political Groups
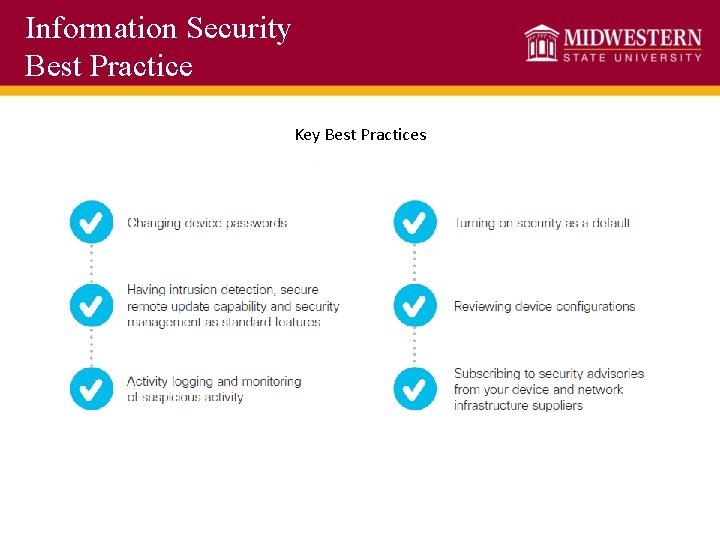
Information Security Best Practice Key Best Practices
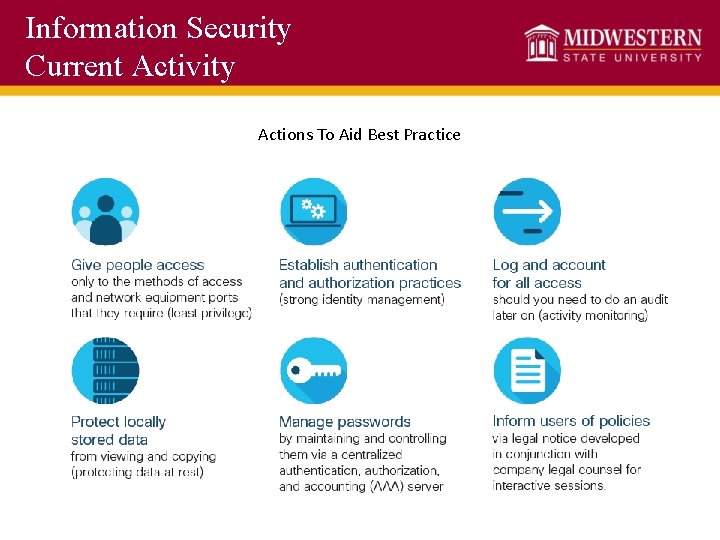
Information Security Current Activity Actions To Aid Best Practice
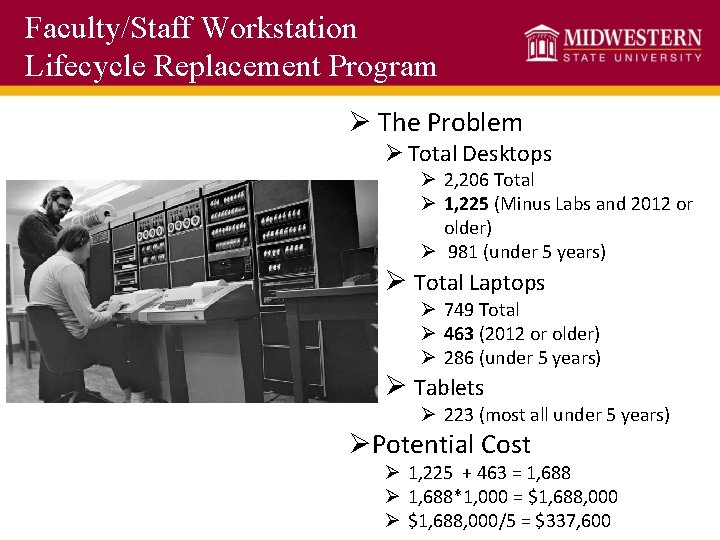
Faculty/Staff Workstation Lifecycle Replacement Program Ø The Problem Ø Total Desktops Ø 2, 206 Total Ø 1, 225 (Minus Labs and 2012 or older) Ø 981 (under 5 years) Ø Total Laptops Ø 749 Total Ø 463 (2012 or older) Ø 286 (under 5 years) Ø Tablets Ø 223 (most all under 5 years) ØPotential Cost Ø 1, 225 + 463 = 1, 688 Ø 1, 688*1, 000 = $1, 688, 000 Ø $1, 688, 000/5 = $337, 600
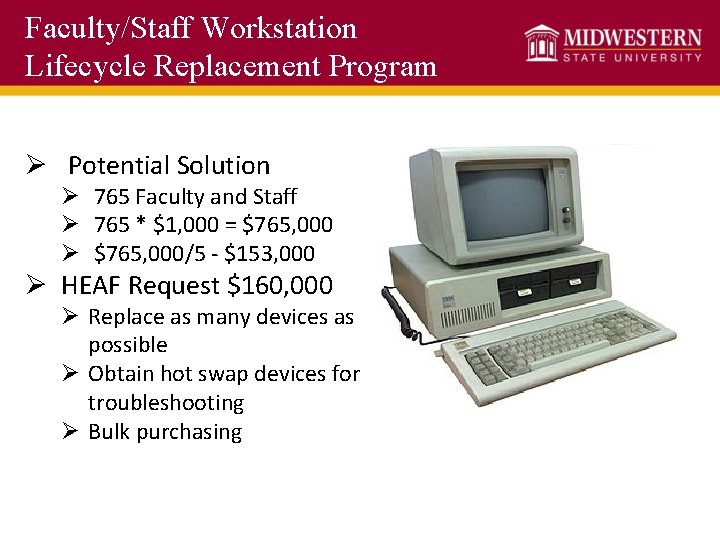
Faculty/Staff Workstation Lifecycle Replacement Program Ø Potential Solution Ø 765 Faculty and Staff Ø 765 * $1, 000 = $765, 000 Ø $765, 000/5 - $153, 000 Ø HEAF Request $160, 000 Ø Replace as many devices as possible Ø Obtain hot swap devices for troubleshooting Ø Bulk purchasing
Faculty/Staff Workstation Lifecycle Replacement Program Ø Draft Guidelines First Year Ø Ø Ø 5 Year Replacement Goal Primary Device Only Oldest Computers first Base Computing Standards Above base or secondary devices not included Ø Not included Ø Lab Computers Ø Student Computers Ø Secondary Devices
Faculty/Staff Workstation Lifecycle Replacement Program Ø Reclamation Ø This first year many likely headed to surplus Ø If device is still supportable, IT will work with department/college on replacement first. Ø IT will then look at greatest campus need for replacement (GA, TA, student computers)
Student Printing Ø The Issue Ø Student Printing in Four Computer Labs Ø Fall 2016 = 1, 000, 463 pages Ø Spring 2017 = 958, 302 pages Ø Summer 2017 = 70, 707 pages Ø Total = 2, 029, 472 pages ØWhat this Looks Like Ø Ø Ø Equivalent to 4, 059 reams of paper annually 11 reams per day average 5, 560 pages per day average One tree is between 8, 000 and 20, 000 pages 4 printers are using up from 101 to 253 trees annually
Student Printing Ø Potential Solutions Ø Wepa Pilot Ø 4 Kiosks Ø CSC, Moffett, Legacy, Prothro-Yeager Ø $5 print credit, equivalent to 100 pages Ø Additional functionality Ø Card swipe, print from cloud storage, USB, D 2 L, web
Student Printing ØImpacts: Ø Total of 3, 860 students printed last fall in labs Ø Of those 660 printed 500 or more pages Ø 180 students printed 1, 000 pages or more ØPotential Next Steps Ø Reduce $100 print credit which is equivalent to 2, 000 pages to $25 for Spring semester (500 pages).
Information Technology HEAF Improvements ØWireless Improvements ØDisaster Recovery ØClassroom Upgrades § Dillard Hall Upgrades § Will be reaching out to colleges for next summer upgrades § Computer Lab Upgrades § Server Upgrades § Network infrastructure Upgrades § Hardin South
Information Technology Current Project Highlights Ø Banner 9 Ø Current Banner INB will be called Admin Pages in Banner 9 (Summer 2018) ØFlower Mound Campus Ø Scheduled to open next semester for classes Ø HSHS – New Data Center Ø Construction to start this semester, completed by Spring 2019 Ø Radius CRM Ø Implementing this fall
Information Technology Current Project Highlights Ø Degree Works Ø January/February Go Live ØTime. Clocks Plus ØDomain Name Change ØOthers in the Queue: Ø Ace. Ware Ø Track. IT Ø Team. Mate Ø Handshake Ø CS Gold Upgrade Ø TLETS Upgrade Ø Alertus Ø Digital Signage Ø E-Signatures
Information Technology Upcoming Project Highlights Ø Domain Change Ø Moving from mwsu. edu to msutexas. edu Ø 6 months plus 6 month extension. Ø 2018 Calendar Year Ø What to Expect Ø Email change Ø url changes (websites, research, publications) Ø Personal accounts linked to mwsu. edu

Information Technology Upcoming Project Highlights ØTwo Current Open Positions ØProgrammer Analyst 2 ØAudio Visual Tech

Ø Questions Ø Comments Ø Concerns