WEB APPLICATION 5 SQLIA v Tautologies v IllegalLogically

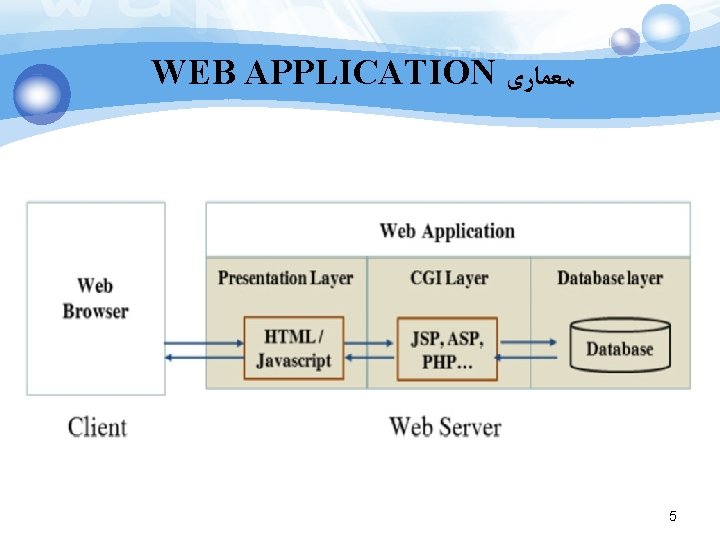
WEB APPLICATION ﻣﻌﻤﺎﺭی 5
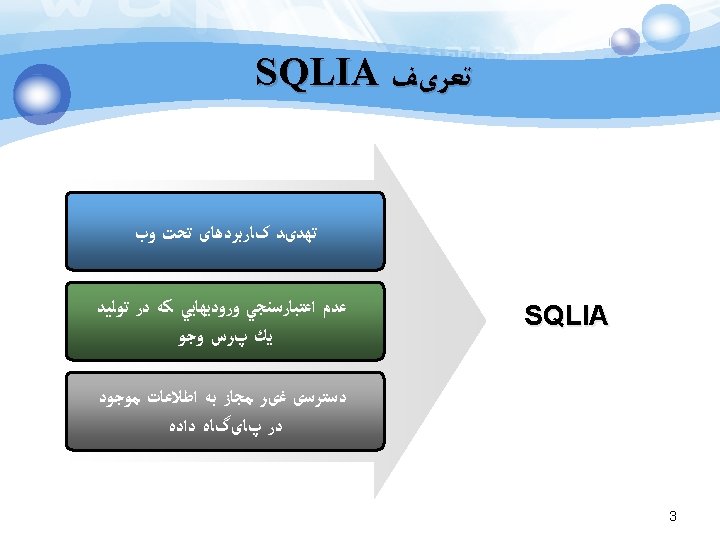
SQLIA ﺍﻧﻮﺍﻉ v Tautologies v Illegal/Logically Incorrect Queries v Union Query v Piggy- Backed Queries v Stored Procedures v Inference v Alternate Encodings 6


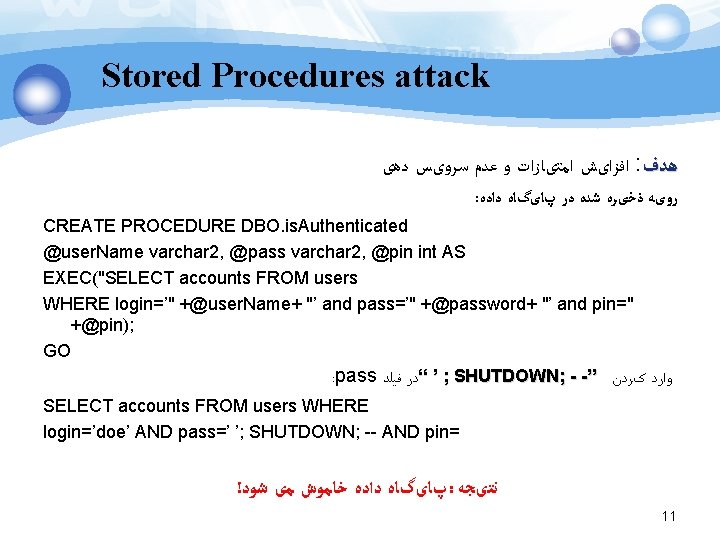
Stored Procedures attack ﺍﻓﺰﺍیﺶ ﺍﻣﺘیﺎﺯﺍﺕ ﻭ ﻋﺪﻡ ﺳﺮﻭیﺲ ﺩﻫی : ﻫﺪﻑ : ﺭﻭیﻪ ﺫﺧیﺮﻩ ﺷﺪﻩ ﺩﺭ پﺎیگﺎﻩ ﺩﺍﺩﻩ CREATE PROCEDURE DBO. is. Authenticated @user. Name varchar 2, @pass varchar 2, @pin int AS EXEC("SELECT accounts FROM users WHERE login=’" +@user. Name+ "’ and pass=’" +@password+ "’ and pin=" +@pin); GO : pass ; ’ “ﺩﺭ ﻓﻴﻠﺪ SHUTDOWN; - -” ﻭﺍﺭﺩ کﺮﺩﻥ SELECT accounts FROM users WHERE login=’doe’ AND pass=’ ’; SHUTDOWN; -- AND pin= ! پﺎیگﺎﻩ ﺩﺍﺩﻩ ﺧﺎﻣﻮﺵ ﻣی ﺷﻮﺩ : ﻧﺘیﺠﻪ 11












ﺭﺍﻩ ﻫﺎی ﺩﻓﺎﻋی CODE SECURELY MONITOR FOR ATTACKS BLOCK ATTACKS 23





ﻣﺮﺍﺟﻊ 1. Bravenboer, M. , Dolstra, E. , Visser, E. , "Preventing injection attacks with syntax embeddings", Science of Computer Programming, vol. 75, pp. 473 -495, 2010. 2. Clarke, J. , "SQL Injection Attacks and Defense", Elsevier, Syngress Publishing, Inc. , 2009. 3. Halfond, W. G. J. , Viegas, J. , Orso, A. , "A Classification of SQL Injection Attacks and Countermeasures", Computing, 2006. 4. Jeong, I. Lee, S. , Yeo, S. , Moond, J. , "A novel method for SQL injection attack detection based on removing SQL query attribute values", Mathematical and Computer Modelling, vol. 55, pp. 58– 68, 2012. 5. Mackay, C. A. , "SQL Injection Attacks and Some Tips on How to Prevent Them", Technical report, The Code Project, 2005, http: //www. codeproject. com/cs/database/Sql. Injection. Attacks. asp. 6. Moyle, S. , "The blackhat’s toolbox: SQL injections", Network Security, pp. 12 -14, 2007. 7. Muthuprasanna, M. , Kothari, W. Ke, S. , "Eliminating SQL Injection Attacks - A Transparent Defense Mechanism", Analysis ﻭ. 8. Nystrom, M. G. , "SQL Injection Detection", O'Reilly Media, Inc, 2007. 9. Ping-Chen, X. , "SQL injection attack and guard technical research", Procedia Engineering, vol. 15, pp. 4131 - 4135, 2011. 29

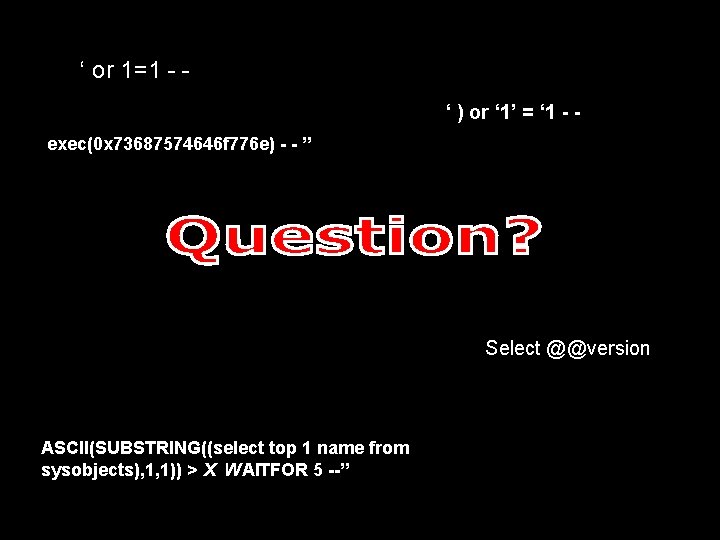
‘ or 1=1 - ‘ ) or ‘ 1’ = ‘ 1 - exec(0 x 73687574646 f 776 e) - - ” Select @@version ASCII(SUBSTRING((select top 1 name from sysobjects), 1, 1)) > X WAITFOR 5 --’’
- Slides: 31