Trustworthy User Interface Design Dynamic Security Skins Rachna


- Slides: 16
Trustworthy User Interface Design: Dynamic Security Skins Rachna Dhamija and J. D. Tygar University of California, Berkeley TIPPI Workshop June 13, 2005
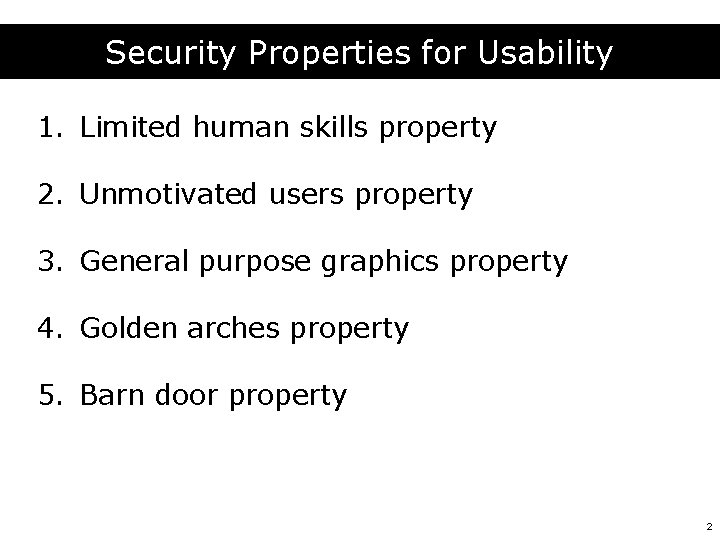
Security Properties for Usability 1. Limited human skills property 2. Unmotivated users property 3. General purpose graphics property 4. Golden arches property 5. Barn door property 2
Password Authenticated Key Agreement § A number of protocols exist: – EKE, SPEKE, SNAPI, Auth. A, PAK, SRP, etc… § Advantages: – user doesn’t need a trusted device – secret stored in memory of the user – server doesn’t store password – no passwords sent over the network – user authentication & mutual authentication § BUT won’t stop phishing! 3
Our Solution: Usability Goals § User must be able to verify password prompt, before entering password § Rely on human skills – To login, recognize 1 image & recall 1 password – To verify server, compare 2 images § Hard to spoof security indicators 4
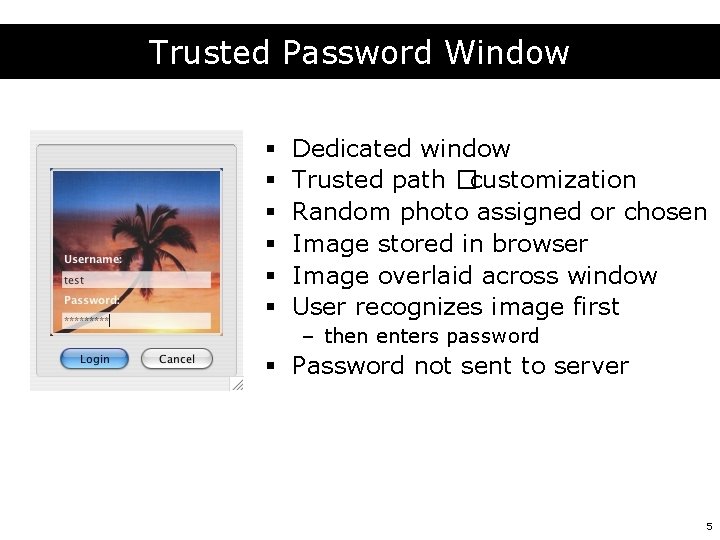
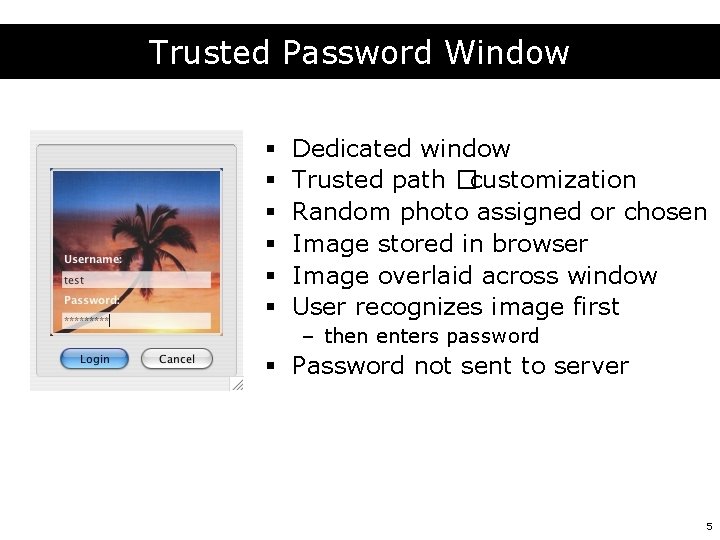
Trusted Password Window § § § Dedicated window Trusted path �customization Random photo assigned or chosen Image stored in browser Image overlaid across window User recognizes image first – then enters password § Password not sent to server 5
Security Indicators § How can the user distinguish secure windows? – static indicators – user customization – automated customization 6

Firefox Browser - 4 SSL indicators 7
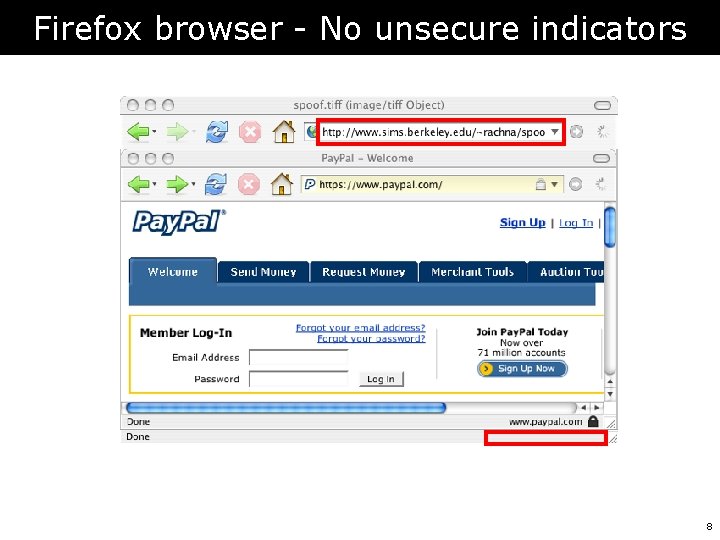
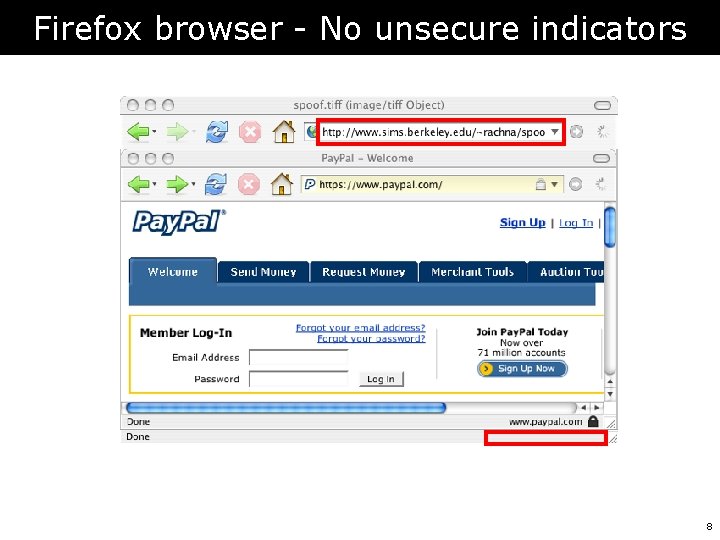
Firefox browser - No unsecure indicators 8
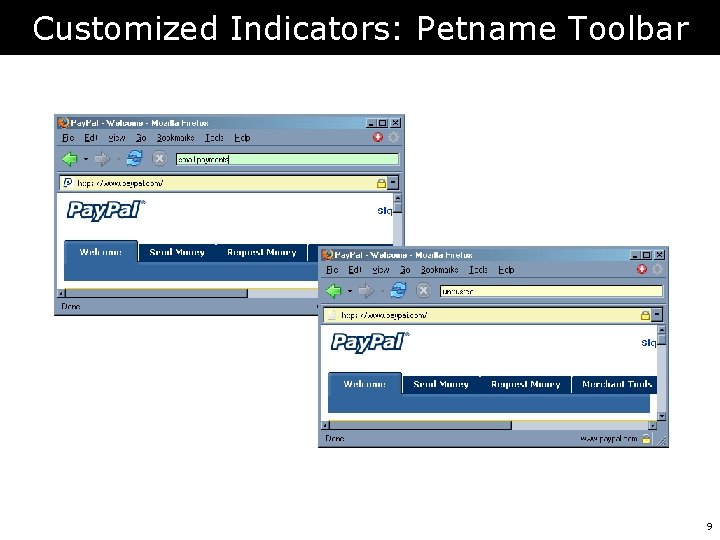
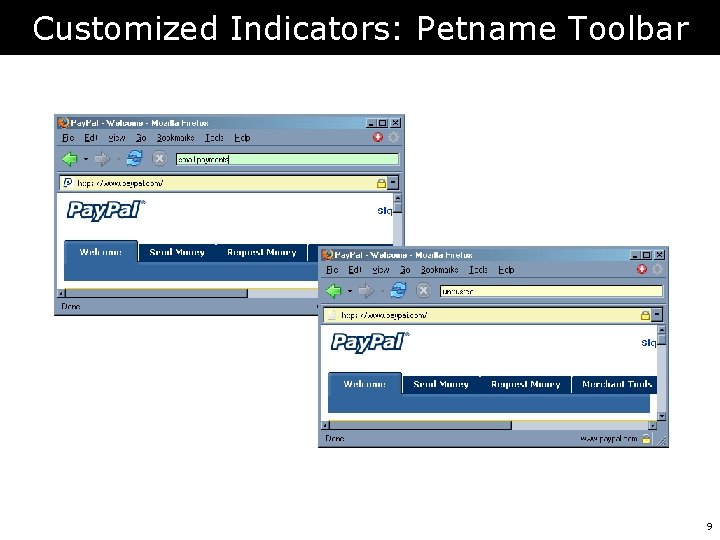
Customized Indicators: Petname Toolbar 9
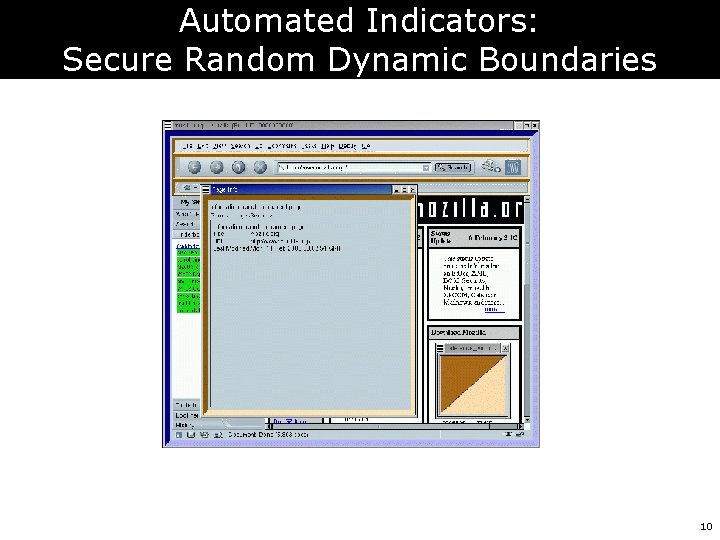
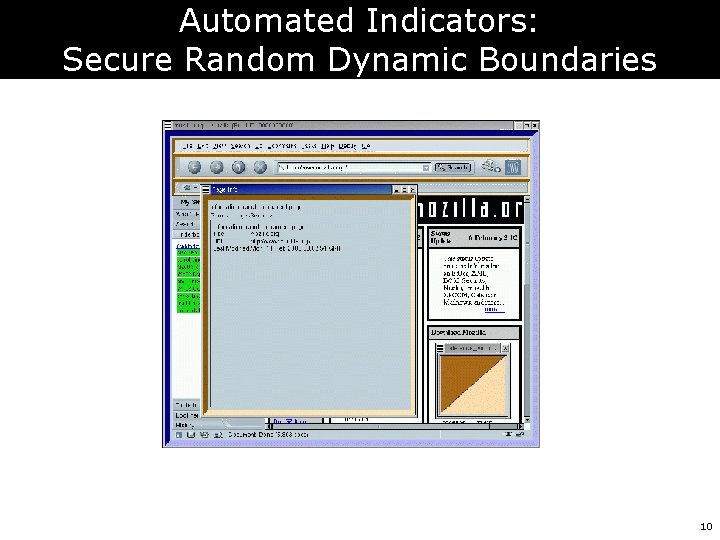
Automated Indicators: Secure Random Dynamic Boundaries 10
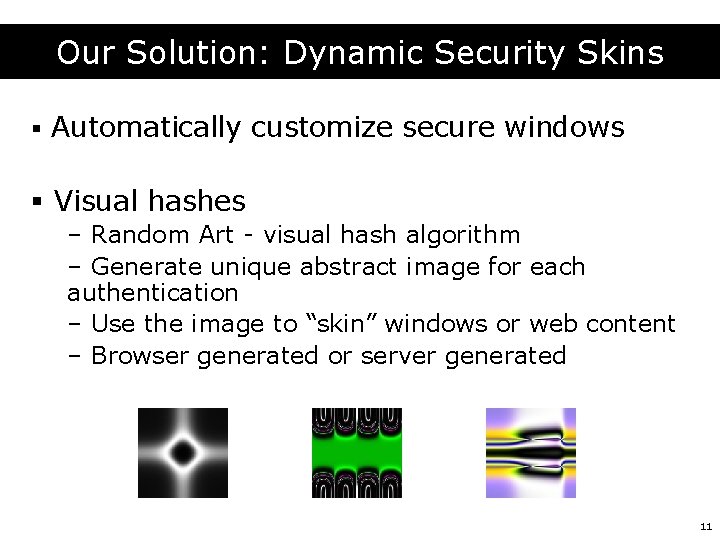
Our Solution: Dynamic Security Skins § Automatically customize secure windows § Visual hashes – Random Art - visual hash algorithm – Generate unique abstract image for each authentication – Use the image to “skin” windows or web content – Browser generated or server generated 11
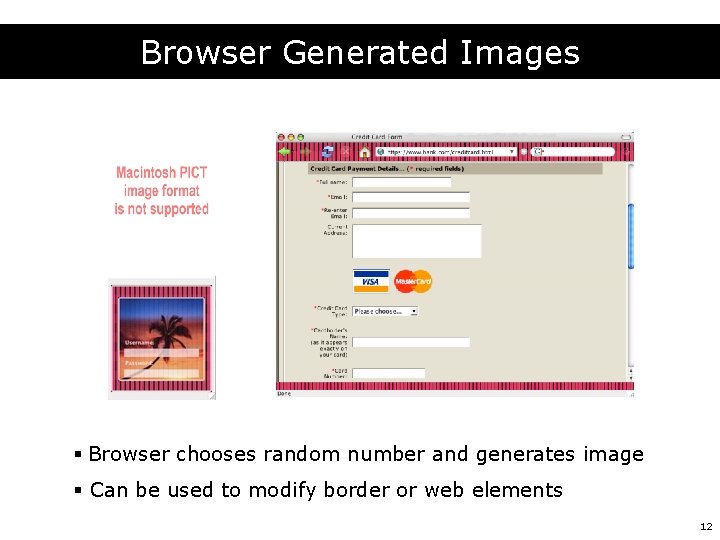
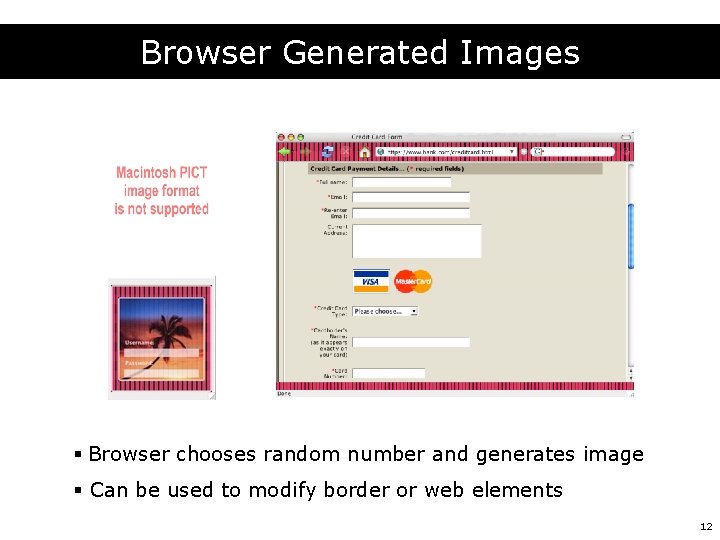
Browser Generated Images § Browser chooses random number and generates image § Can be used to modify border or web elements 12
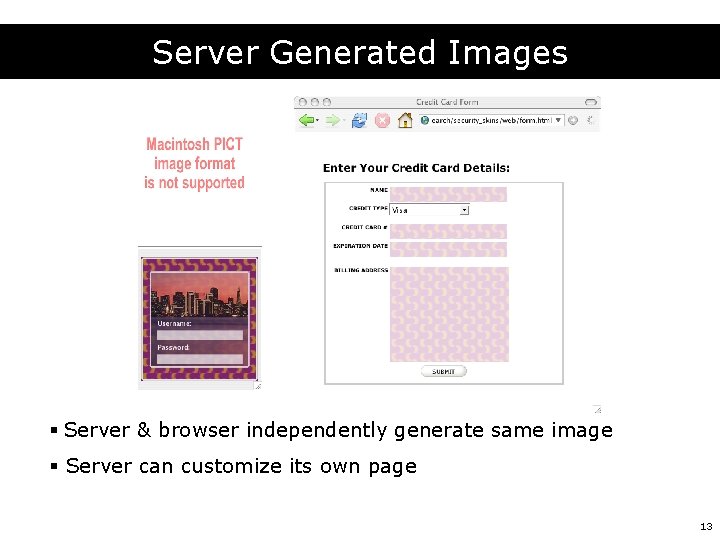
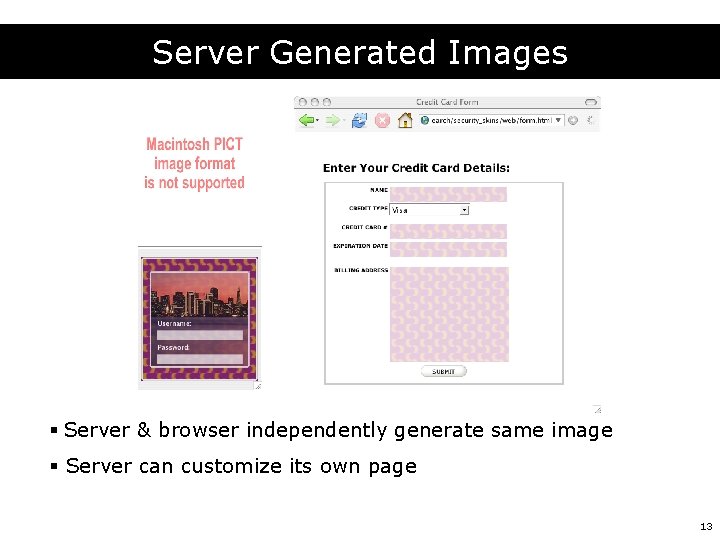
Server Generated Images § Server & browser independently generate same image § Server can customize its own page 13
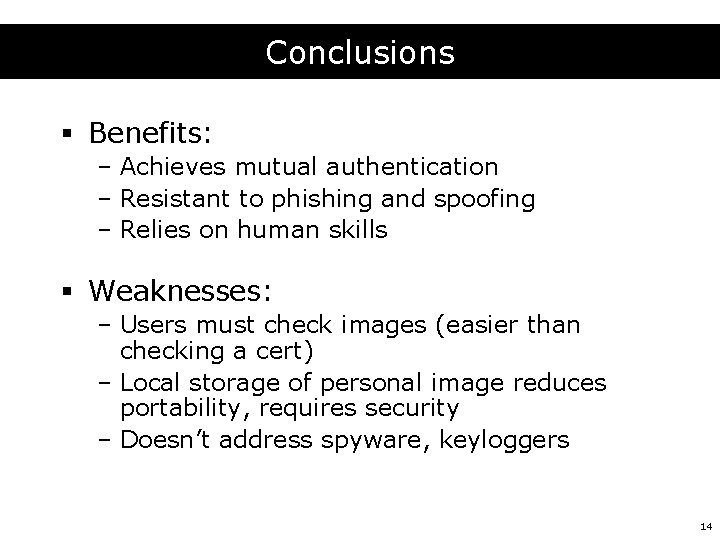
Conclusions § Benefits: – Achieves mutual authentication – Resistant to phishing and spoofing – Relies on human skills § Weaknesses: – Users must check images (easier than checking a cert) – Local storage of personal image reduces portability, requires security – Doesn’t address spyware, keyloggers 14
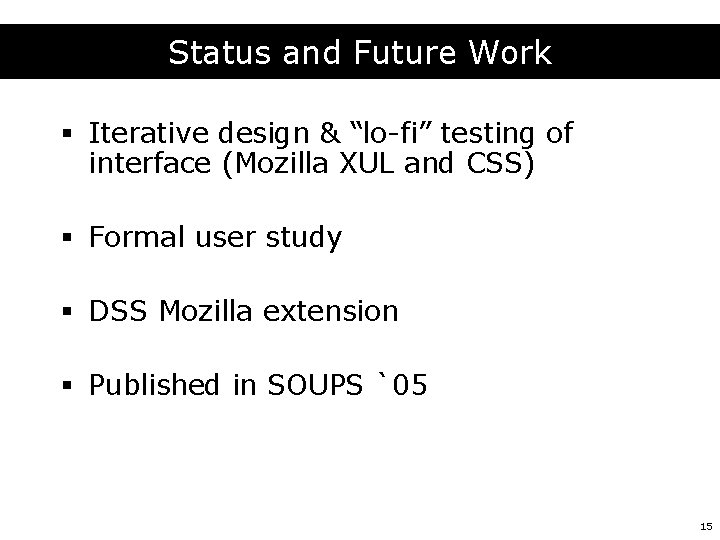
Status and Future Work § Iterative design & “lo-fi” testing of interface (Mozilla XUL and CSS) § Formal user study § DSS Mozilla extension § Published in SOUPS `05 15

16