Serverside Security Parallels International Gmb H All rights
Server-side Security © Parallels International Gmb. H. All rights reserved.
WEB security • HTTP • HTML, Java. Script • Same Origin Policy • XSS • CSRF © Parallels International Gmb. H. All rights reserved. 1
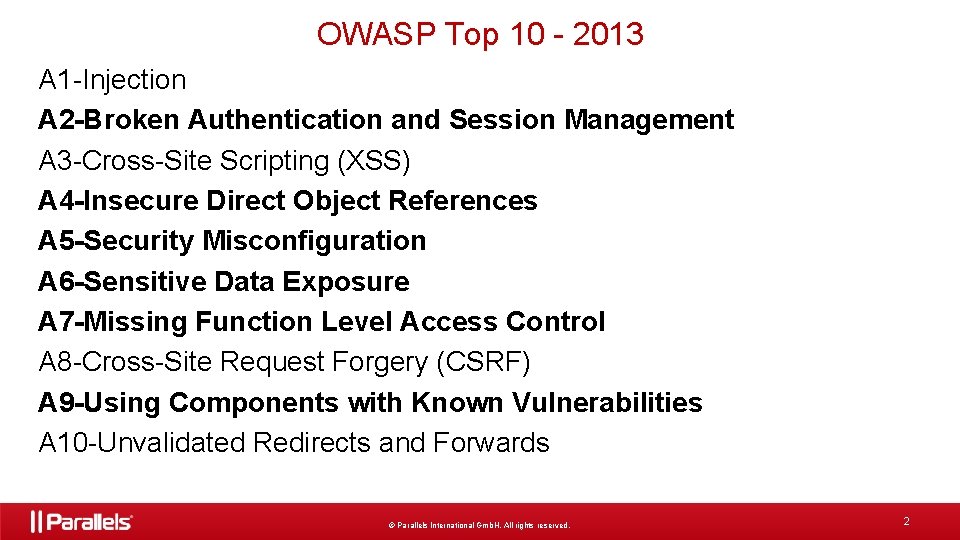
OWASP Top 10 - 2013 A 1 -Injection A 2 -Broken Authentication and Session Management A 3 -Cross-Site Scripting (XSS) A 4 -Insecure Direct Object References A 5 -Security Misconfiguration A 6 -Sensitive Data Exposure A 7 -Missing Function Level Access Control A 8 -Cross-Site Request Forgery (CSRF) A 9 -Using Components with Known Vulnerabilities A 10 -Unvalidated Redirects and Forwards © Parallels International Gmb. H. All rights reserved. 2
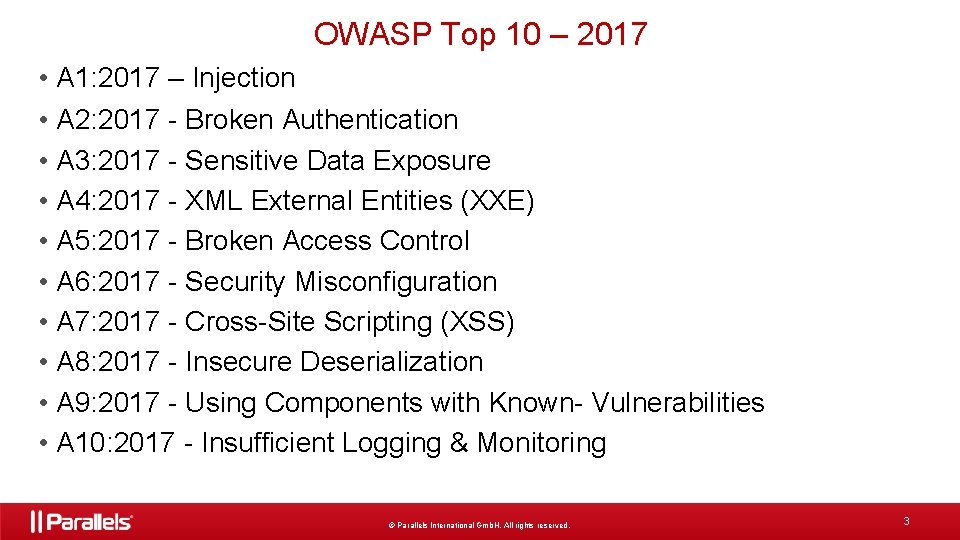
OWASP Top 10 – 2017 • A 1: 2017 – Injection • A 2: 2017 - Broken Authentication • A 3: 2017 - Sensitive Data Exposure • A 4: 2017 - XML External Entities (XXE) • A 5: 2017 - Broken Access Control • A 6: 2017 - Security Misconfiguration • A 7: 2017 - Cross-Site Scripting (XSS) • A 8: 2017 - Insecure Deserialization • A 9: 2017 - Using Components with Known- Vulnerabilities • A 10: 2017 - Insufficient Logging & Monitoring © Parallels International Gmb. H. All rights reserved. 3
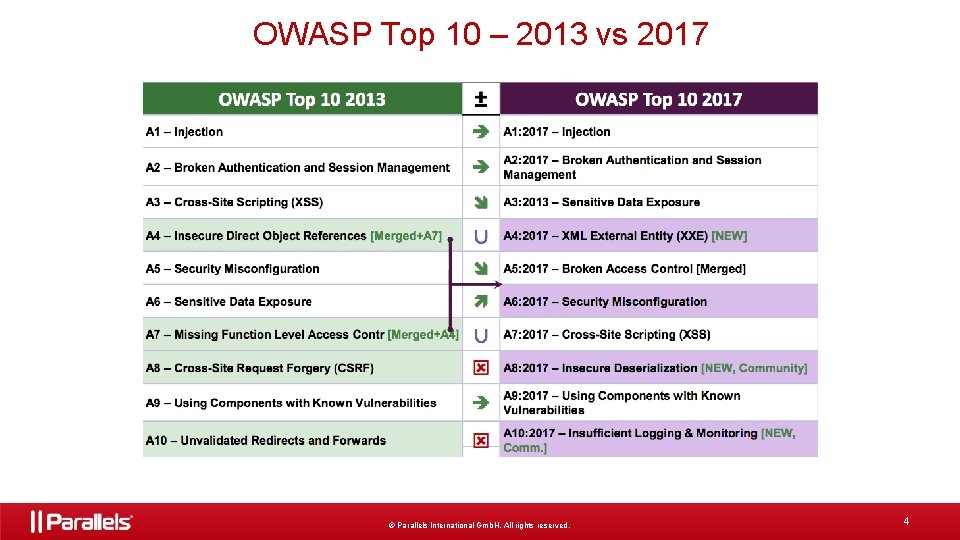
OWASP Top 10 – 2013 vs 2017 © Parallels International Gmb. H. All rights reserved. 4
Authentication © Parallels International Gmb. H. All rights reserved. 5
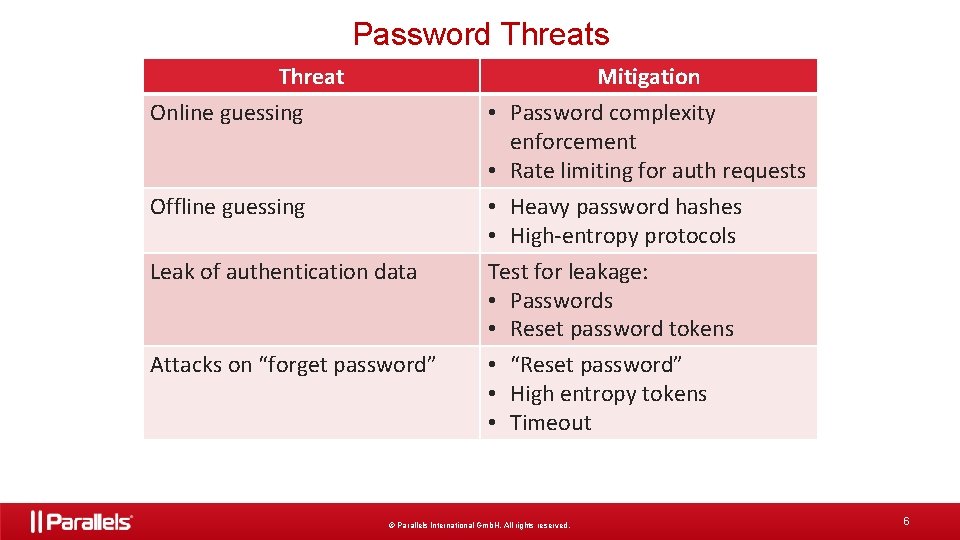
Password Threats Threat Mitigation Online guessing Offline guessing Leak of authentication data Attacks on “forget password” • Password complexity enforcement • Rate limiting for auth requests • Heavy password hashes • High-entropy protocols Test for leakage: • Passwords • Reset password tokens • “Reset password” • High entropy tokens • Timeout © Parallels International Gmb. H. All rights reserved. 6
Session Management © Parallels International Gmb. H. All rights reserved. 7
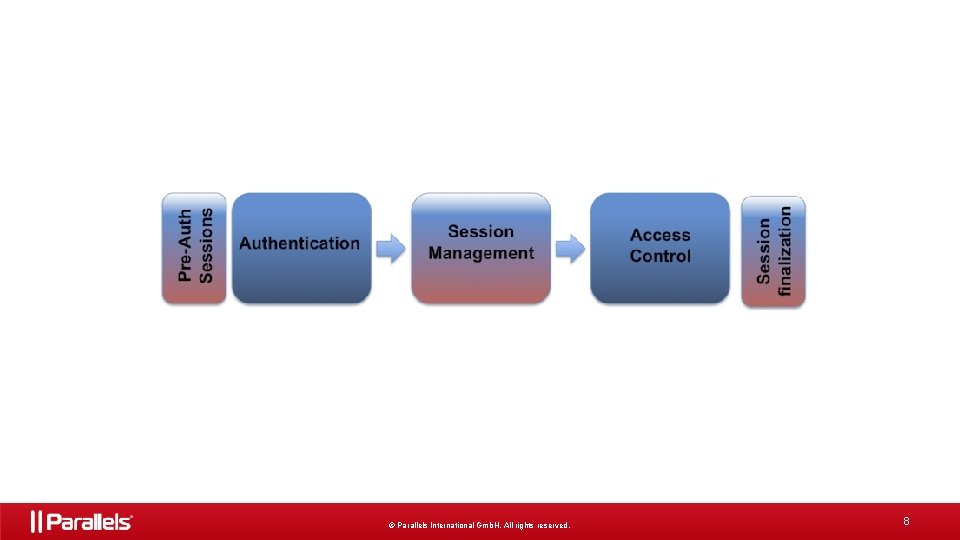
© Parallels International Gmb. H. All rights reserved. 8
Session ID • Example: employee ID, badge • Session ID (SID) – string of chars or numbers © Parallels International Gmb. H. All rights reserved. 9
Session mechanisms • GET • http: //site. com/Admin. php? Session. ID=12345678 • POST • hidden form fields • Cookies • with or without expiration • Custom Headers © Parallels International Gmb. H. All rights reserved. 10
Attacks • Hijacking • prediction • brute force • interception • Fixation © Parallels International Gmb. H. All rights reserved. 11
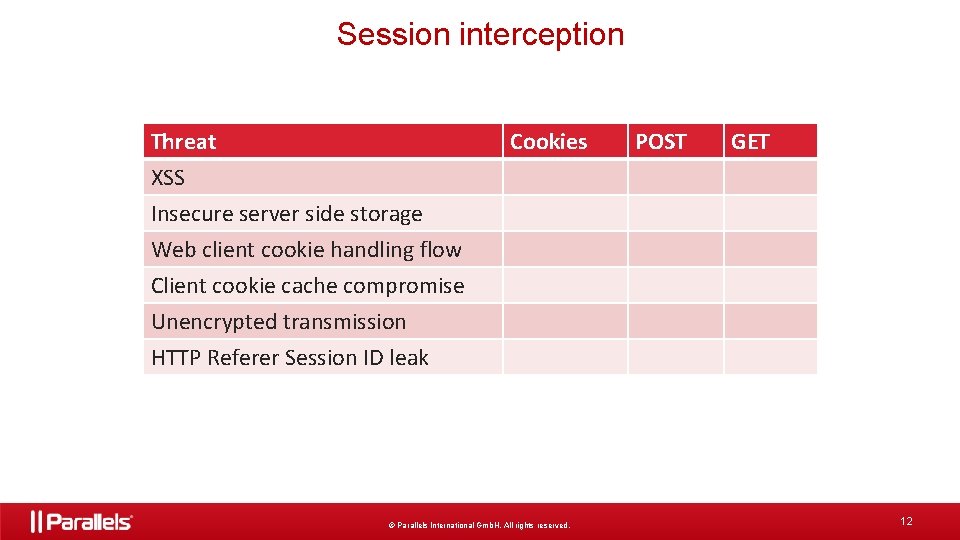
Session interception Threat Cookies POST GET XSS Insecure server side storage Web client cookie handling flow Client cookie cache compromise Unencrypted transmission HTTP Referer Session ID leak © Parallels International Gmb. H. All rights reserved. 12
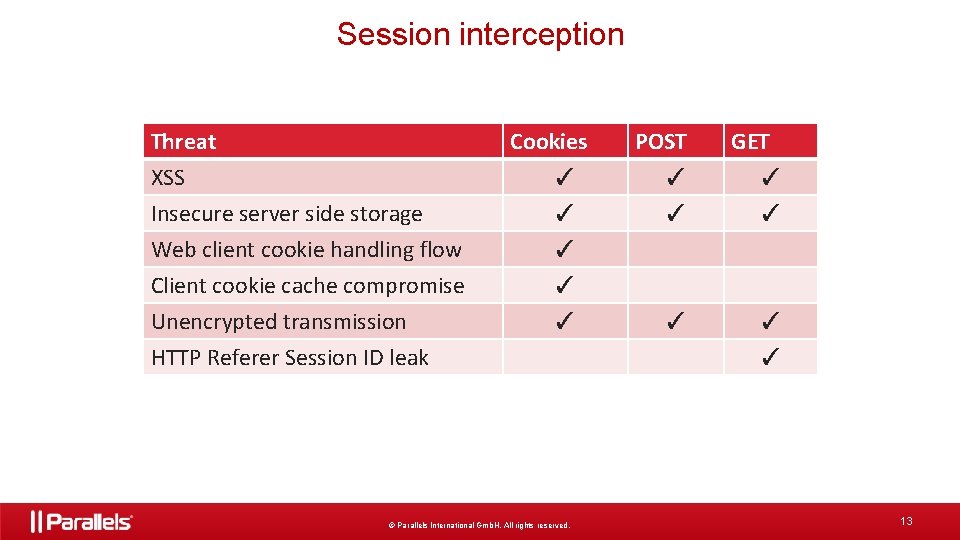
Session interception Threat Cookies XSS Insecure server side storage Web client cookie handling flow Client cookie cache compromise Unencrypted transmission HTTP Referer Session ID leak ✓ ✓ ✓ © Parallels International Gmb. H. All rights reserved. POST GET ✓ ✓ ✓ ✓ 13
Session fixation 1. 2. 3. 4. Attacker creates link with pre-defined session id Victim uses link to login Web app uses existing session id Attacker uses known session id © Parallels International Gmb. H. All rights reserved. 14
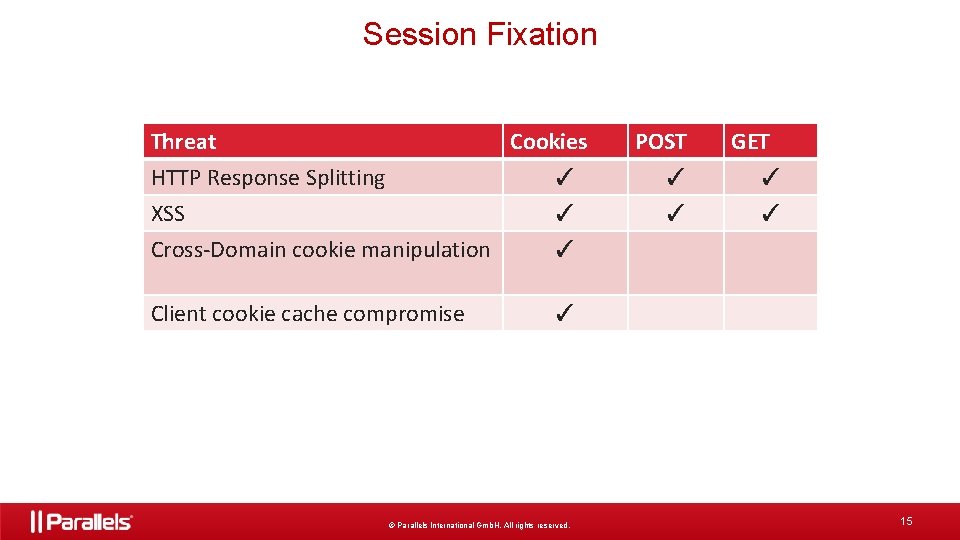
Session Fixation Threat Cookies HTTP Response Splitting XSS Cross-Domain cookie manipulation ✓ ✓ ✓ Client cookie cache compromise ✓ © Parallels International Gmb. H. All rights reserved. POST ✓ ✓ GET ✓ ✓ 15
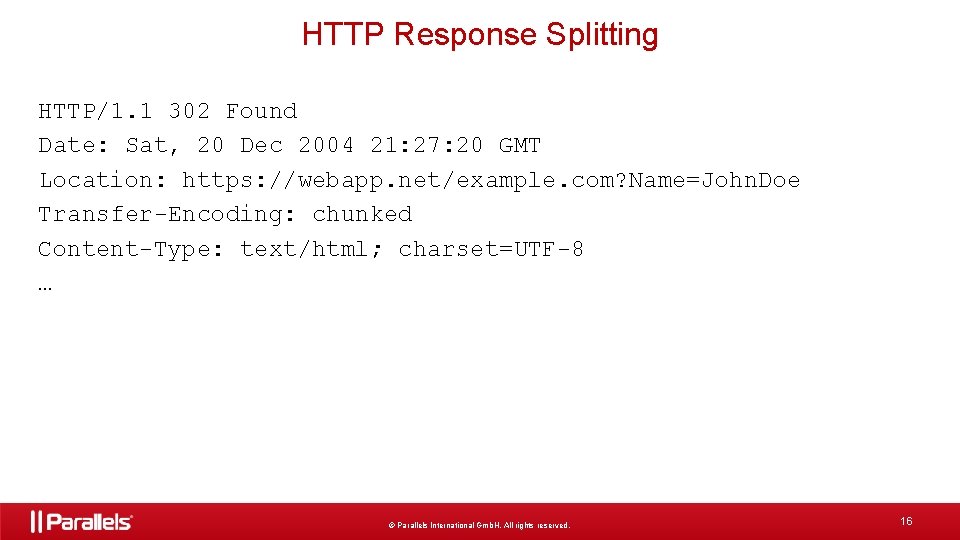
HTTP Response Splitting HTTP/1. 1 302 Found Date: Sat, 20 Dec 2004 21: 27: 20 GMT Location: https: //webapp. net/example. com? Name=John. Doe Transfer-Encoding: chunked Content-Type: text/html; charset=UTF-8 … © Parallels International Gmb. H. All rights reserved. 16
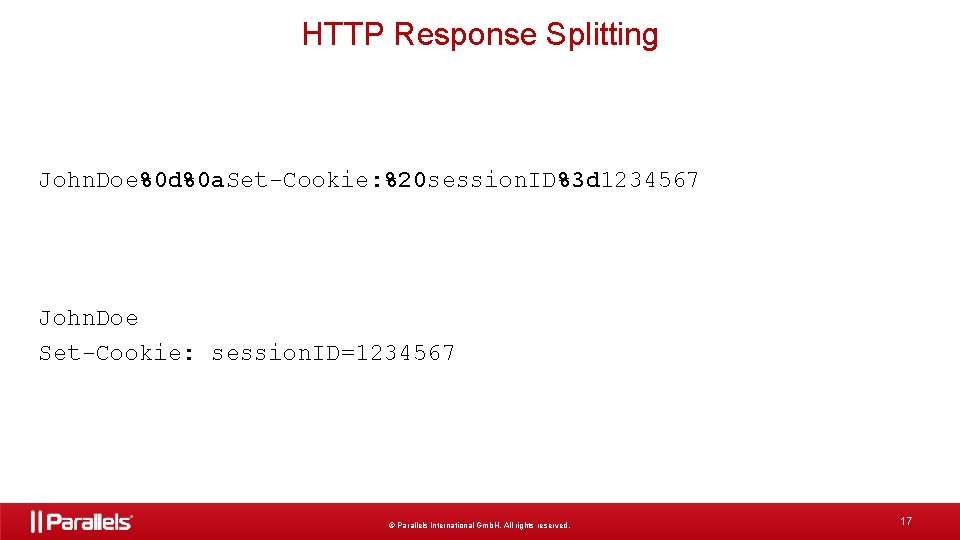
HTTP Response Splitting John. Doe%0 d%0 a. Set-Cookie: %20 session. ID%3 d 1234567 John. Doe Set-Cookie: session. ID=1234567 © Parallels International Gmb. H. All rights reserved. 17
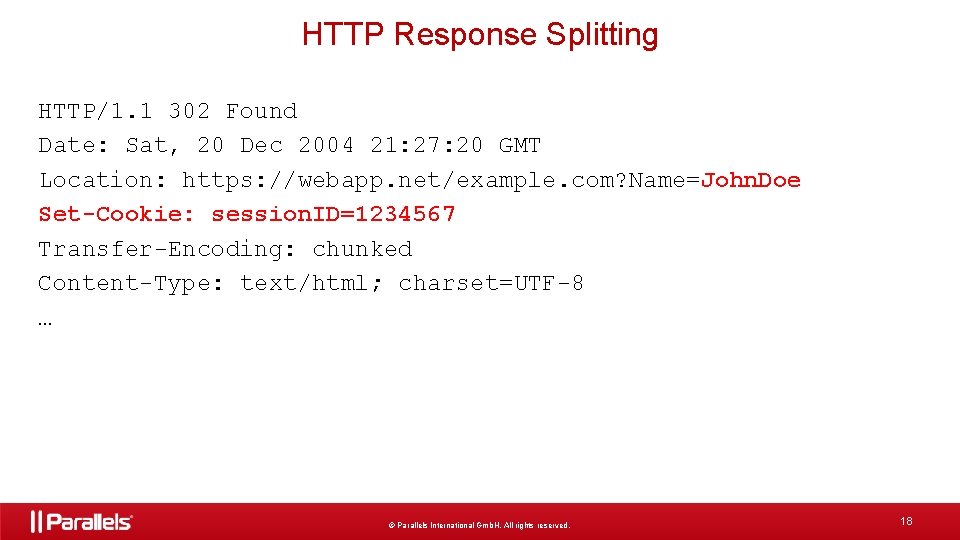
HTTP Response Splitting HTTP/1. 1 302 Found Date: Sat, 20 Dec 2004 21: 27: 20 GMT Location: https: //webapp. net/example. com? Name=John. Doe Set-Cookie: session. ID=1234567 Transfer-Encoding: chunked Content-Type: text/html; charset=UTF-8 … © Parallels International Gmb. H. All rights reserved. 18
Automatic Session Expiration • Idle Timeout • Absolute Timeout • Renewal Timeout © Parallels International Gmb. H. All rights reserved. 19
Session: checks and countermeasures • Strong encryption on all transmissions • Store only ID on client • GET variable Referer filtering • Perform sanity checks to detect hijacking © Parallels International Gmb. H. All rights reserved. 20

Access Control © Parallels International Gmb. H. All rights reserved. 21
Attacks on Access Control • Vertical Access Control Attacks A standard user accessing admin functionality • Horizontal Access Control Attacks User accessing data of another user • Business Logic Access Control Attacks Abuse of workflow © Parallels International Gmb. H. All rights reserved. 22
Insecure Direct Object References http: //example. com/app/account. Info? acct=notmyacct © Parallels International Gmb. H. All rights reserved. 23
Insecure Direct Object References • Use per user or session indirect object references • Check access © Parallels International Gmb. H. All rights reserved. 24
Function Level Access Control 1. Navigation to unauthorized functions… 2. Server side authorization missing… 3. Server side checks rely on user input… © Parallels International Gmb. H. All rights reserved. 25
Authorization HOWTO • Check authorization for every operation • Check authorization for object to operate on • Never rely on client-side authorization • Double-check transaction state on server © Parallels International Gmb. H. All rights reserved. 26
Components with Know Vulnerabilities © Parallels International Gmb. H. All rights reserved. 27
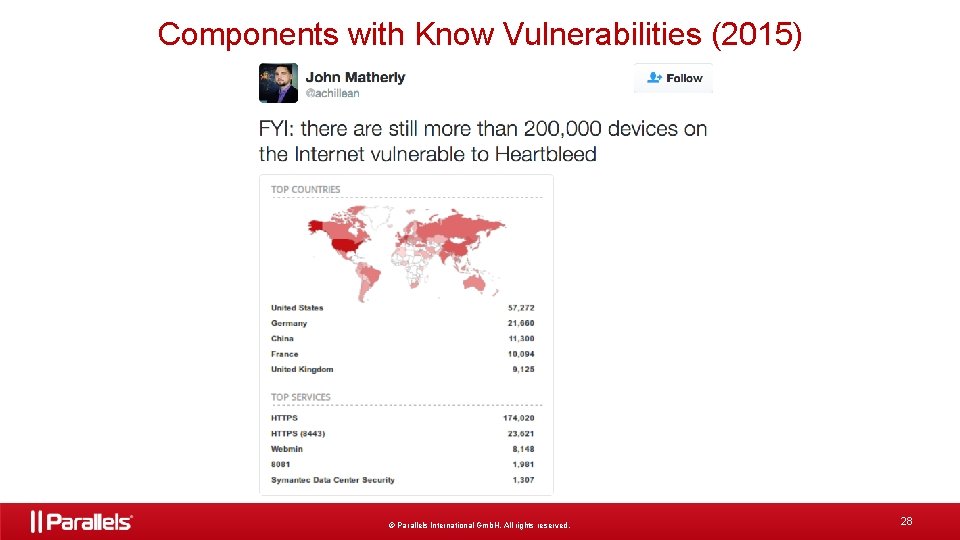
Components with Know Vulnerabilities (2015) © Parallels International Gmb. H. All rights reserved. 28
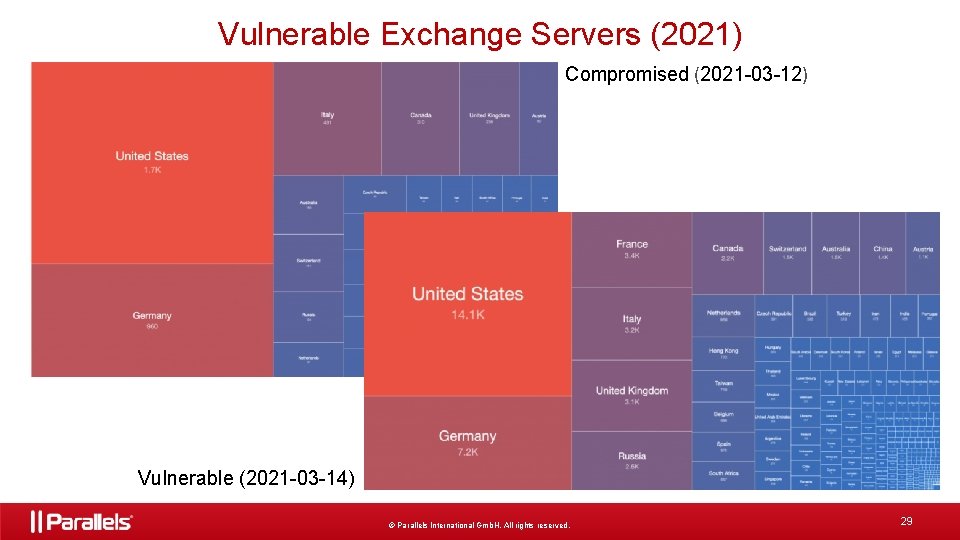
Vulnerable Exchange Servers (2021) Compromised (2021 -03 -12) Vulnerable (2021 -03 -14) © Parallels International Gmb. H. All rights reserved. 29
3 rd Party Components HOTWO • Evaluate security of new component • Keep registry of 3 rd party components • Check for security alerts • Plan dependencies’ upgrades © Parallels International Gmb. H. All rights reserved. 30
Insufficient Logging & Monitoring • Auditable events, such as logins, failed logins, and high value transactions are not logged. • Logs of applications and APIs are not monitored for suspicious activity. • Alerting thresholds and response escalation as per the risk of the data held by the application is not in place or effective. © Parallels International Gmb. H. All rights reserved. 31
Security Misconfiguration 1. 2. 3. 4. Insecure defaults Inappropriate/weak tools Excessive functionality Too verbose error messages © Parallels International Gmb. H. All rights reserved. 32
Default passwords • Users not aware about default password • Default password seem strong • Users will not change default password © Parallels International Gmb. H. All rights reserved. 33
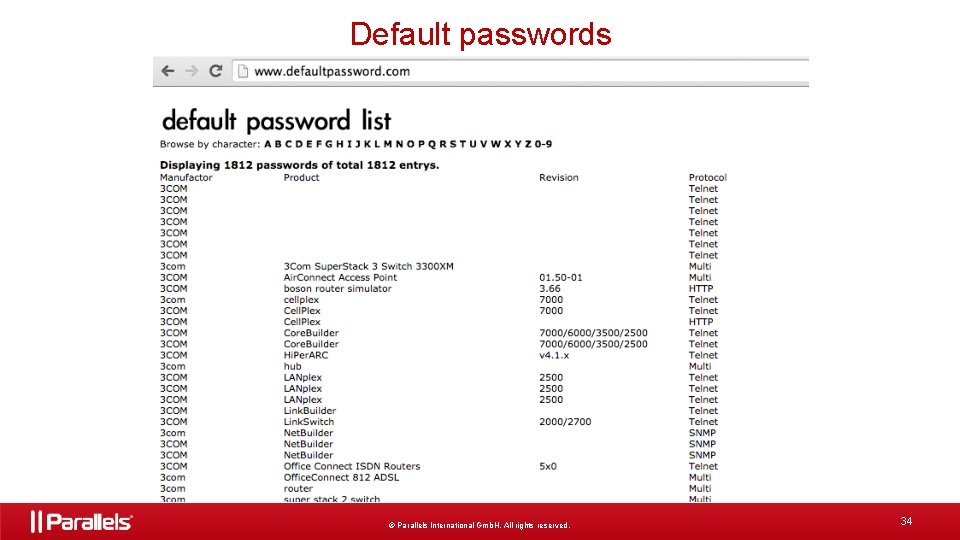
Default passwords © Parallels International Gmb. H. All rights reserved. 34
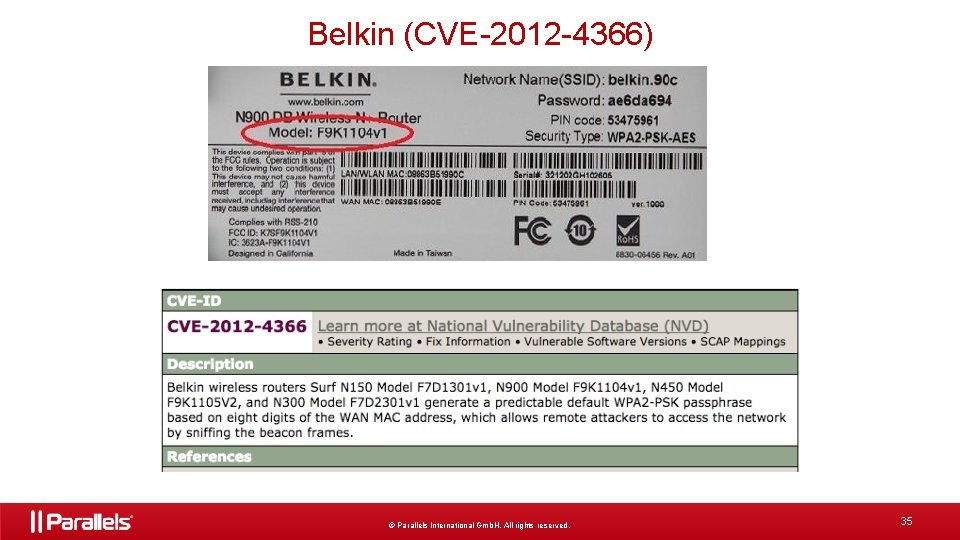
Belkin (CVE-2012 -4366) © Parallels International Gmb. H. All rights reserved. 35
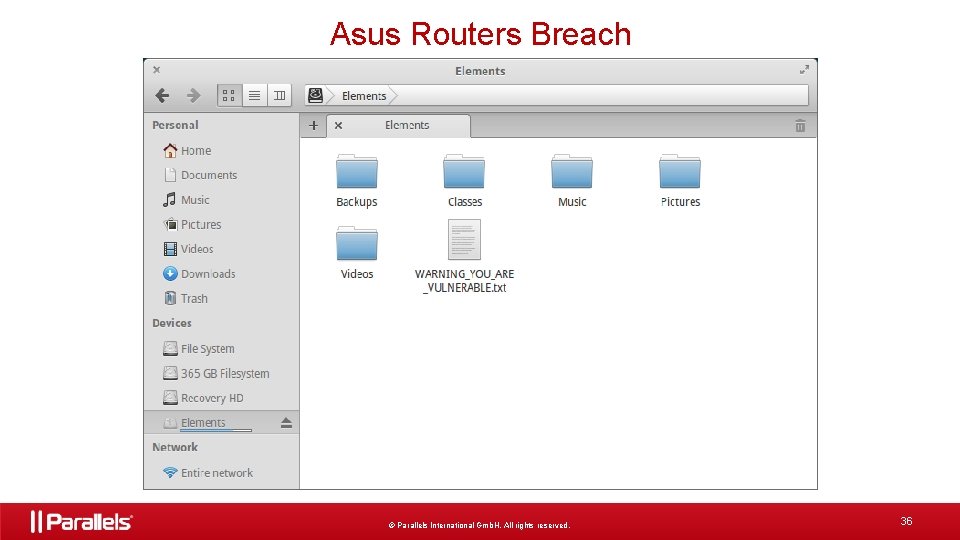
Asus Routers Breach © Parallels International Gmb. H. All rights reserved. 36
Questions? © Parallels International Gmb. H. All rights reserved. 38
Thank you! © Parallels International Gmb. H. All rights reserved. 39
- Slides: 39