Security Issues with PHP PHP installation PHP programming
- Slides: 15
Security Issues with PHP Ø PHP installation Ø PHP programming Willa Zhu & Eugene Burger
About PHP o It is a server-side scripting language that facilitates the creation of dynamic Web pages by embedding PHP-coded logic in HTML documents o It combines many of the finest features of Perl, C, and Java, and adds its own elements o Its popularity as a server-side scripting language is only increasing o Security issues
PHP Security The way to secure PHP scripts is through a carefully selected combination of configuration settings and safe programming practices.
PHP Configuration - php. ini The configuration file (called php 3. ini in PHP 3. 0, and simply php. ini as of PHP 4. 0) is read when PHP starts up. For the server module versions of PHP, this happens only once when the web server is started. For the CGI and CLI version, it happens on every invocation. Default location: /usr/local/lib/ Sample: http: //cvs. php. net/co. php/php-src/php. ini-dist
Install PHP in a secured manner – (1) safe_mode These options allows you to control which directories PHP scripts are allowed to access files from. By default PHP will allow a script to access a file from anywhere so it is recommended that is option be set. By predefining valid directories, data can be protected. safe_mode_exec_dir Setting this variable helps you in forceing PHP to only execute scripts from a specified directory. doc_root PHP will not serve files that are outside this directory while in safe mode.
Install PHP in a secured manner – (2) open_basedir, allow_url_fopen Thess options allows you to control which directories PHP scripts are allowed to access files from. By default PHP will allow a script to access a file from anywhere so it is recommended that is option be set. By predefining valid directories, data can be protected. max_execution_time This variable enables you to set a maximum execution time that a script can have. If a script runs longer than the allocated execution time, it will be terminated. This option will allow you to prevent attackers from tying up your web server with malicious scripts that could cause denial of service.
Install PHP in a secured manner – (3) memory_limit This allows you to control the maximum amount of memory that a script can use. Using this will help to prevent buffer overflows which may lead to more serious threats. upload_tmp_dir This designates where PHP will place files that are being uploaded. disable_functions This lists comma-separated names of functions that PHP will just ignore.
Install PHP in a secured manner – (4) safe_mode_allowed_env_vars It defines a list of prefixes that identify the names of the environment variables the user is allowed to change safe_mode_protected_env_vars The list given to this directive specifies names of environment variables that the user is not allowed to modify.
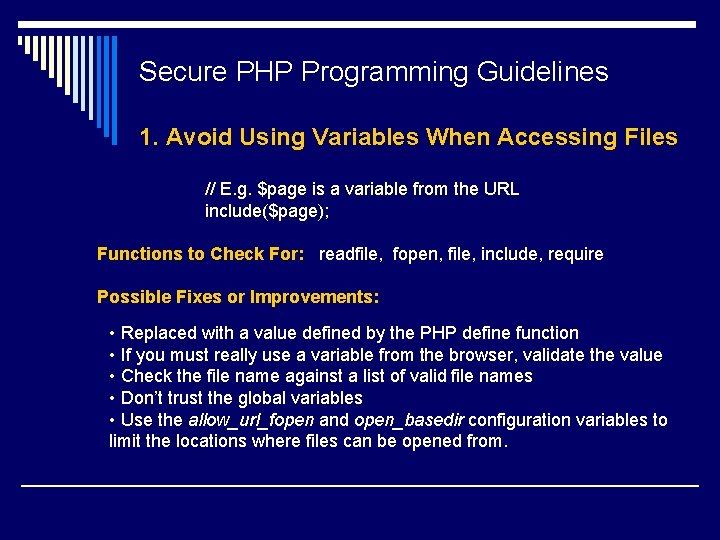
Secure PHP Programming Guidelines 1. Avoid Using Variables When Accessing Files // E. g. $page is a variable from the URL include($page); Functions to Check For: readfile, fopen, file, include, require Possible Fixes or Improvements: • Replaced with a value defined by the PHP define function • If you must really use a variable from the browser, validate the value • Check the file name against a list of valid file names • Don’t trust the global variables • Use the allow_url_fopen and open_basedir configuration variables to limit the locations where files can be opened from.
Secure PHP Programming Guidelines 2. Do Not Trust Global Variables If the register_globals option is enabled, PHP will create global variables for each GET, POST, and cookie variable included in the HTTP request. What to Check For: (Pay careful attention to the following areas) - Authentication and permission checking code - Use of variables before they are initialized. - Use of variables designed to be set by GET or POST requests. Possible Fixes or Improvements: - Disable register_globals in your php. ini file and you need to use the $HTTP_GET_VARS and $HTTP_POST_VARS associative arrays - Ensure session variables really do come from the session - initialize all global variables - check that a global variable is not in the $HTTP_POST or $HTTP_GET associative arrays.
Secure PHP Programming Guidelines 3. Use the. php extension for all script files If use other extensions (such as. lib or. inc) are used, the contents of these files will be seen from browser, including any PHP code. This may reveal intellectual property, passwords or weaknesses in your code. What to Check For: Examine the file names of all script files. Possible Fixes or Improvements: - Use the. php extension for all script files - Place library and configuration files outside the web server's document root directory (use include_path in php. ini) - prevent all. inc files from being displayed (in Apache’s configuration file)
Secure PHP Programming Guidelines 4. Place sensitive content outside the document root directory Many PHP systems are designed to restrict access to documents or images through user authentication and access control lists. However, these documents are frequently stored as files in a subdirectory of the directory containing the PHP scripts. This makes these files available directly by using the appropriate URL in your browser. What to Check For: Examine the placement of directories used to store files containing privileged content. Possible Fixes or Improvements: - Store content as files in a directory outside the web server's document root directory. - Store content in a database - Use web server features such as Apache's. htaccess files to prevent direct access to content directories.
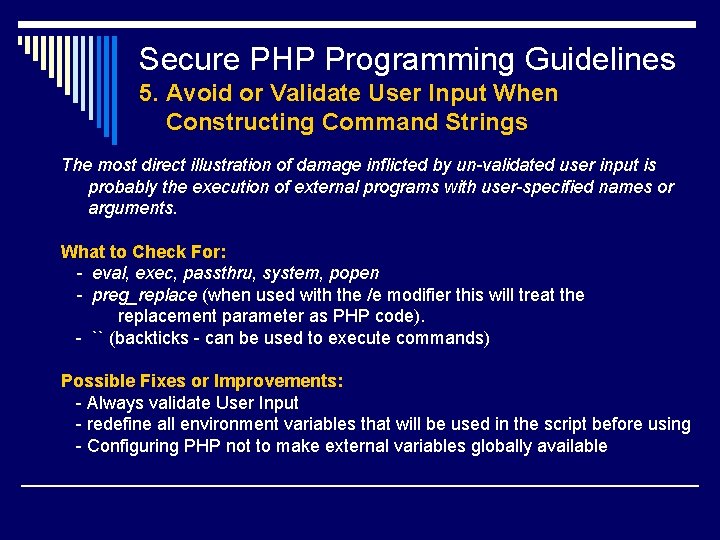
Secure PHP Programming Guidelines 5. Avoid or Validate User Input When Constructing Command Strings The most direct illustration of damage inflicted by un-validated user input is probably the execution of external programs with user-specified names or arguments. What to Check For: - eval, exec, passthru, system, popen - preg_replace (when used with the /e modifier this will treat the replacement parameter as PHP code). - `` (backticks - can be used to execute commands) Possible Fixes or Improvements: - Always validate User Input - redefine all environment variables that will be used in the script before using - Configuring PHP not to make external variables globally available
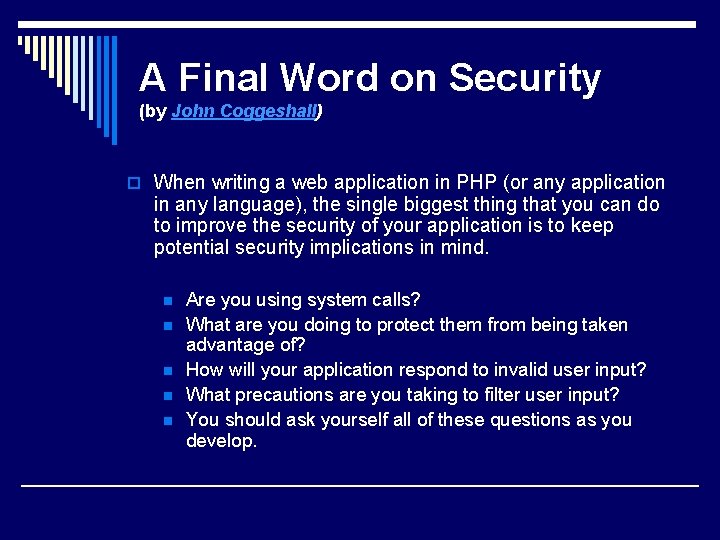
A Final Word on Security (by John Coggeshall) o When writing a web application in PHP (or any application in any language), the single biggest thing that you can do to improve the security of your application is to keep potential security implications in mind. n n n Are you using system calls? What are you doing to protect them from being taken advantage of? How will your application respond to invalid user input? What precautions are you taking to filter user input? You should ask yourself all of these questions as you develop.
Some PHP Security Resources URLs o http: //www. linuxsecurity. com/feature_stories/feature_story-117. html o http: //www. developer. com/lang/article. php/918141 o http: //www. developer. com/lang/article. php/922871 o http: //www. onlamp. com/pub/a/php/2003/03/20/php_security. html o http: //www. onlamp. com/pub/a/php/2003/07/31/php_foundations. html o http: //www. onlamp. com/pub/a/php/2003/08/28/php_foundations. html o http: //www. onlamp. com/pub/a/php/2003/10/09/php_foundations. html o http: //www. sklar. com/page/article/owasp-top-ten