Security in eb XML Messaging CPPCPA Elements Elements
Security in eb. XML Messaging CPP/CPA Elements
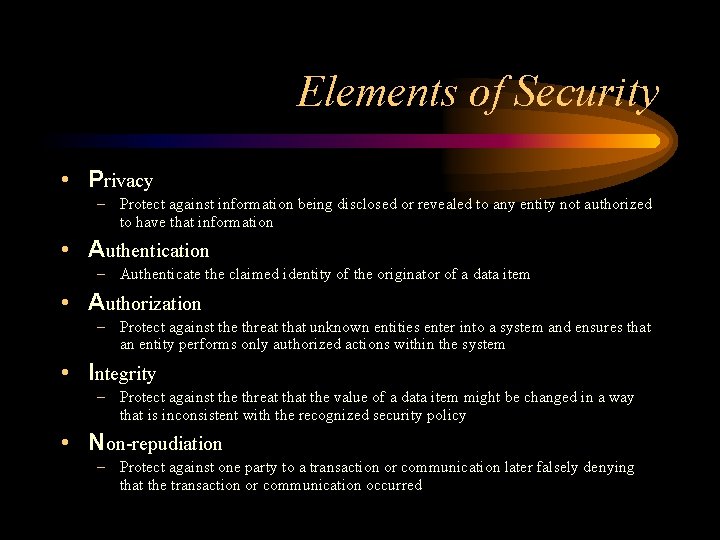
Elements of Security • Privacy – Protect against information being disclosed or revealed to any entity not authorized to have that information • Authentication – Authenticate the claimed identity of the originator of a data item • Authorization – Protect against the threat that unknown entities enter into a system and ensures that an entity performs only authorized actions within the system • Integrity – Protect against the threat the value of a data item might be changed in a way that is inconsistent with the recognized security policy • Non-repudiation – Protect against one party to a transaction or communication later falsely denying that the transaction or communication occurred
Security and Computing Infrastructure • Security can be applied to… – Transports (SSL, IPSEC) – Messages (S/MIME, PGP) – Systems
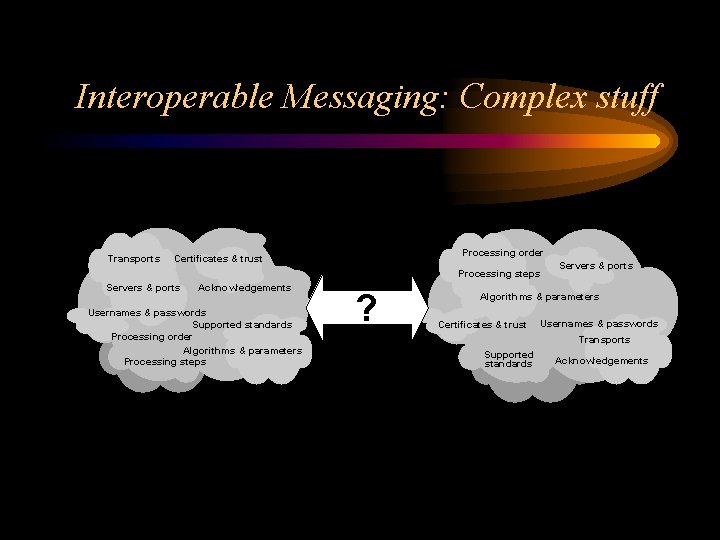
Interoperable Messaging: Complex stuff Transports Processing order Certificates & trust Processing steps Servers & ports Acknowledgements Usernames & passwords Supported standards Processing order Algorithms & parameters Processing steps ? Servers & ports Algorithms & parameters Certificates & trust Usernames & passwords Transports Supported standards Acknowledgements
Security Options • The More Obvious Stuff – Encryption – Signatures – Non-repudiation • The Less Obvious Stuff – Trust – Certificate lifecycle management – Certificate revocation
eb. XML Delivery Channel Covers the Obvious • Delivery Channel = Document Exchange Layer + Transport Layer • Delivery Channel characteristics – – – nonrepudiation. Of. Origin nonredupiation. Of. Receipt secure. Transport confidentiality authenticated authorized
How to Deal with the Less Obvious • These are PKI issues that need to be addressed to facilitate interoperability • The key to understanding these issues is an understanding of X. 509 certificates – Creation – Issuance – Management
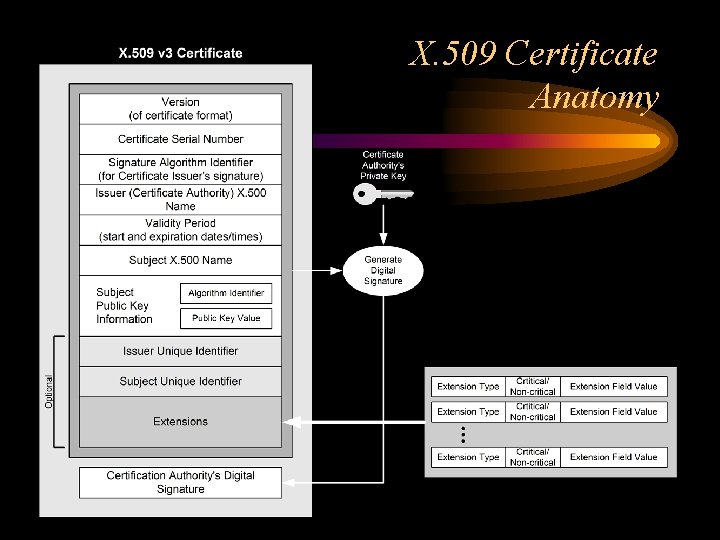
X. 509 Certificate Anatomy
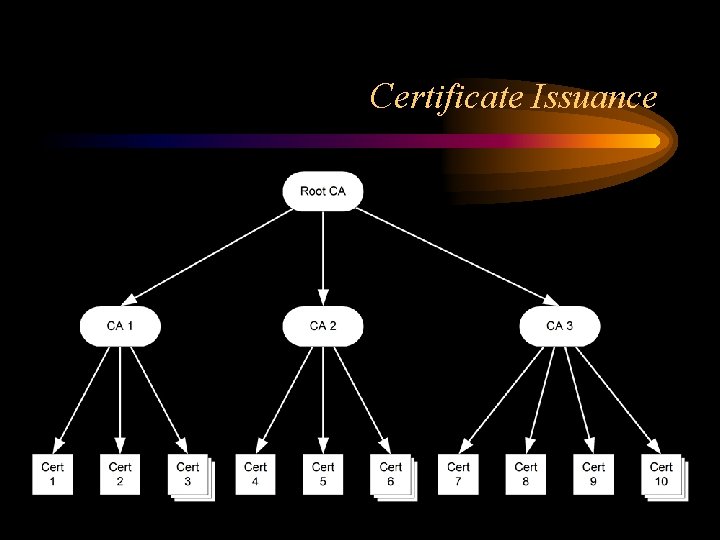
Certificate Issuance
Certificate Management Includes • Key registration • Key archive and recovery • Centralized revocation information – CRLs – OCSP • Certificate publication to a repository
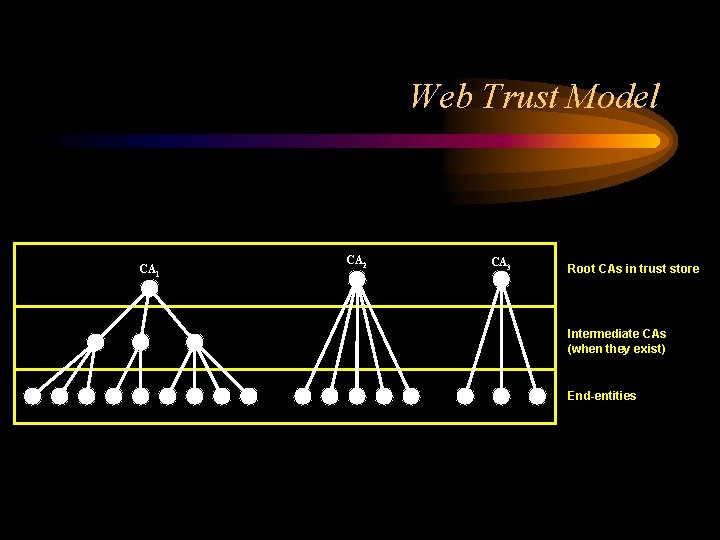
Web Trust Model CA 1 CA 2 CA 3 Root CAs in trust store Intermediate CAs (when they exist) End-entities
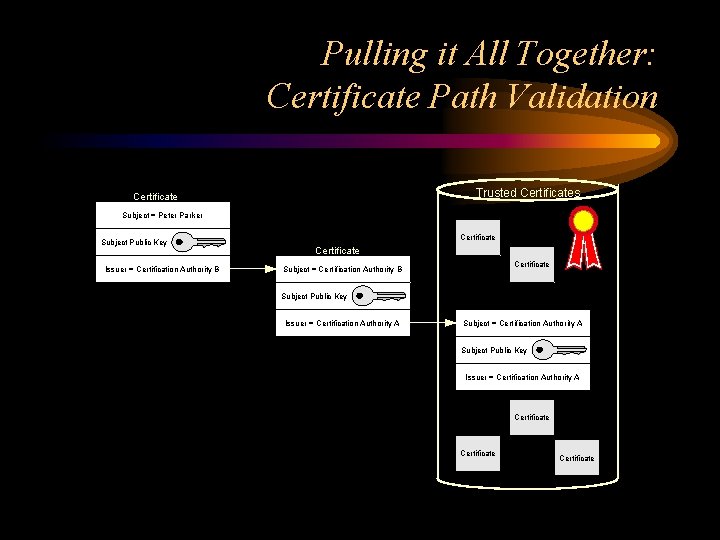
Pulling it All Together: Certificate Path Validation Trusted Certificates Certificate 1 Subject = Peter Parker Subject Public Key Issuer = Certification Authority B Certificate 2 Certificate Subject = Certification Authority B Subject Public Key Issuer = Certification Authority A Certificate 3 Subject = Certification Authority A Subject Public Key Issuer = Certification Authority A Certificate
- Slides: 12