Risk Assessment Key to a successful risk management
- Slides: 31
Risk Assessment: Key to a successful risk management program Sixteenth National HIPAA Summit Timothy H Rearick, MBA, PMP August 22, 2008
Learning Objectives n Define risk assessment n Why complete a risk assessment n How risk assessments work n Expected deliverables 2
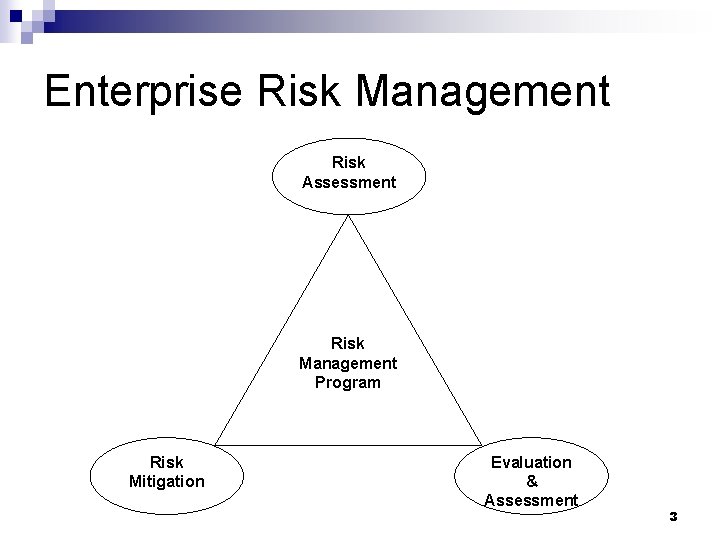
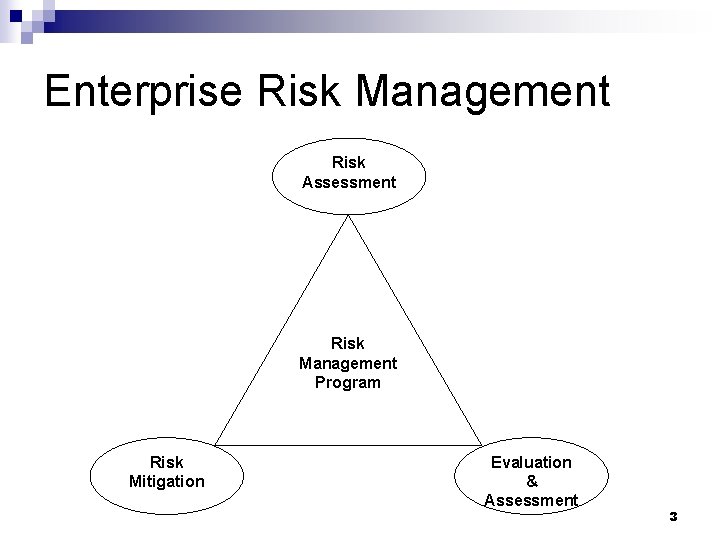
Enterprise Risk Management Risk Assessment Risk Management Program Risk Mitigation Evaluation & Assessment 3
Risk Assessment Defined n Evaluates the enterprise information security program against specific criteria (ISO/IEC 27002, NIST, etc) n Documents threats, vulnerabilities and likelihood of damage n Identifies defensive measures 4
Information Security Landscape 5
Risk Assessment Drivers n Information security incidents n Federal and State laws n Legal liability n Cost of remediating breaches 6
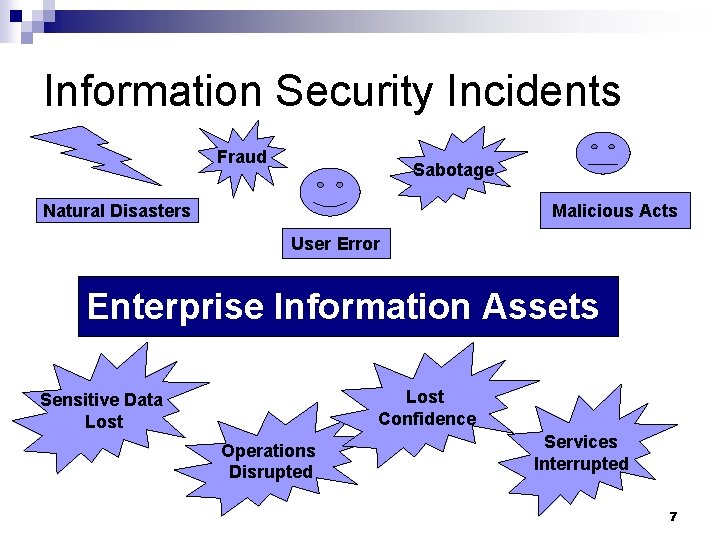
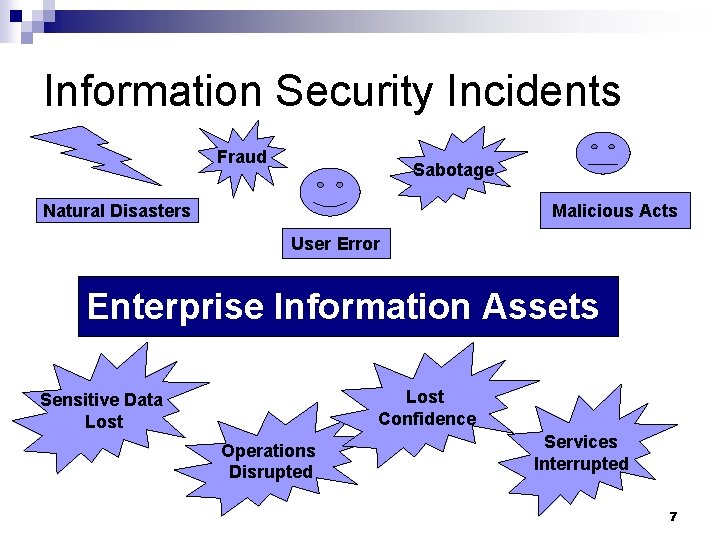
Information Security Incidents Fraud Sabotage Natural Disasters Malicious Acts User Error Enterprise Information Assets Lost Confidence Sensitive Data Lost Operations Disrupted Services Interrupted 7
Specific Infosec Incidents n Walter Reed Army Medical Center n University of Florida College of Medicine n University of Massachusetts n New York-Presbyterian Hospital n General Internal Medicine of Lancaster 8
Federal and State Laws n HIPAA n FISMA n Gramm-Leach Bliley Act n Sarbanes-Oxley n Florida Information Resource Security Policies and Standards 9
Legal Liability n Due diligence - effort made by a reasonable person to avoid harm to another party or himself n Failure to exercise due diligence may be considered negligence 10
Data Protection Costs Less n Gartner Research 9 -16 -2005 ¨ Protecting customer data costs less n n $6 -$16/account to protect $90/account to mitigate a breach n Ponemon 11 -07 ¨ Institute© & PGP Co Study Estimate mitigation cost at $197/record 11
Types of Assessments n ISO/IEC 27002: 2005 n NIST n HIPAA n Co. Bit n NSA IAM 12
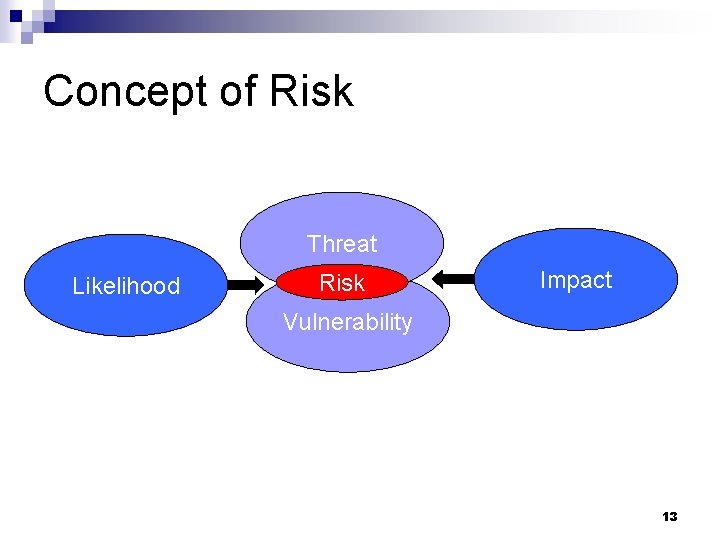
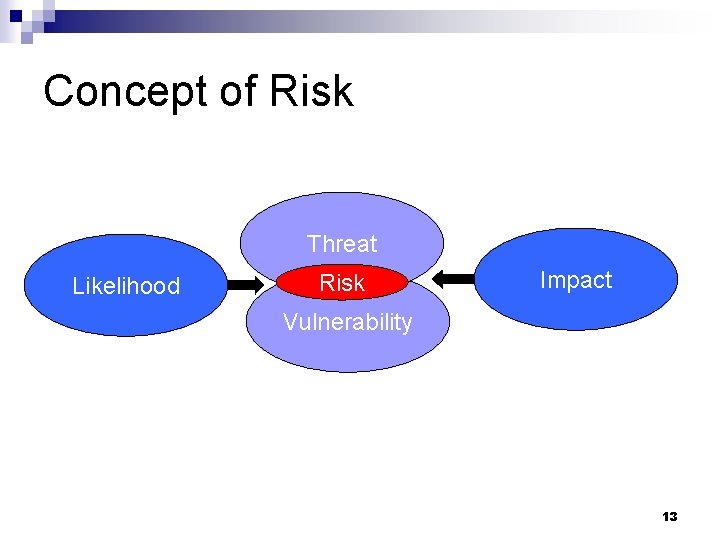
Concept of Risk Threat Likelihood Risk Impact Vulnerability 13
Risk Assessment Process 1. 2. 3. 4. 5. System characterization Threat identification Vulnerability identification Control analysis Likelihood determination 14
Risk Assessment Process 6. 7. 8. 9. Impact analysis Risk determination Control recommendations Results documentation 15
Risk Assessment Process n System characterization ¨ Hardware, software, system interfaces ¨ Data and information ¨ People (users and IT staff responsible for system) 16
Risk Assessment Process n n Threat identification Vulnerability identification Control analysis Likelihood determination 17
Risk Assessment Process n n Impact analysis Risk determination Control recommendations Results documentation 18
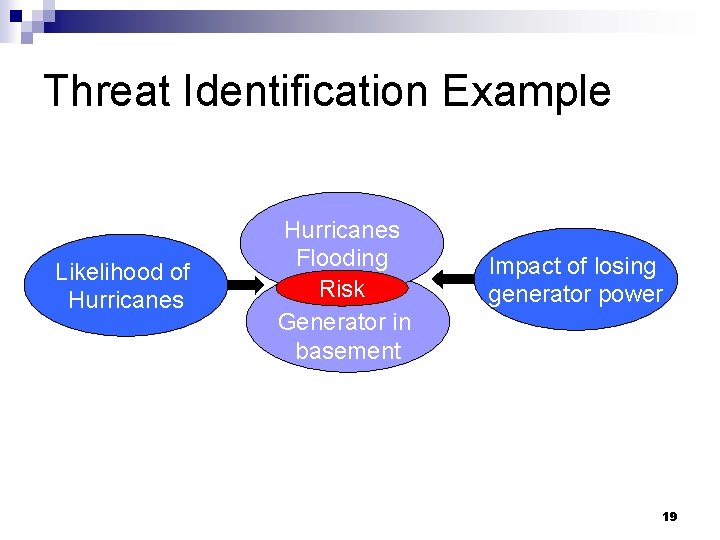
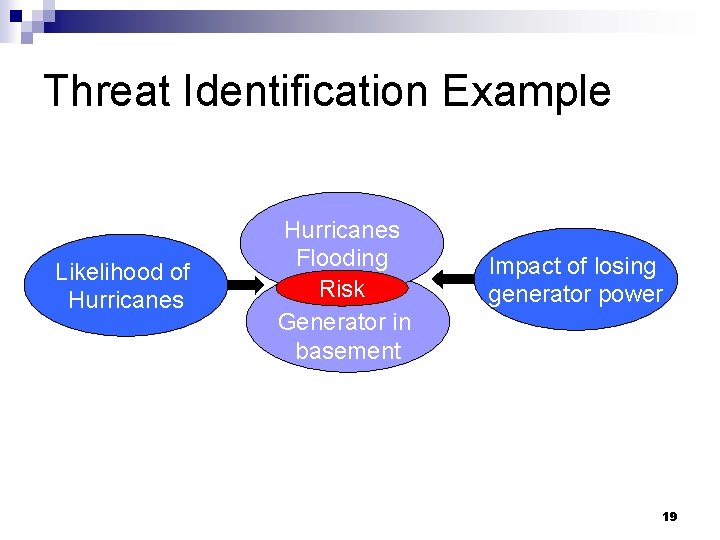
Threat Identification Example Likelihood of Hurricanes Flooding Risk Generator in basement Impact of losing generator power 19
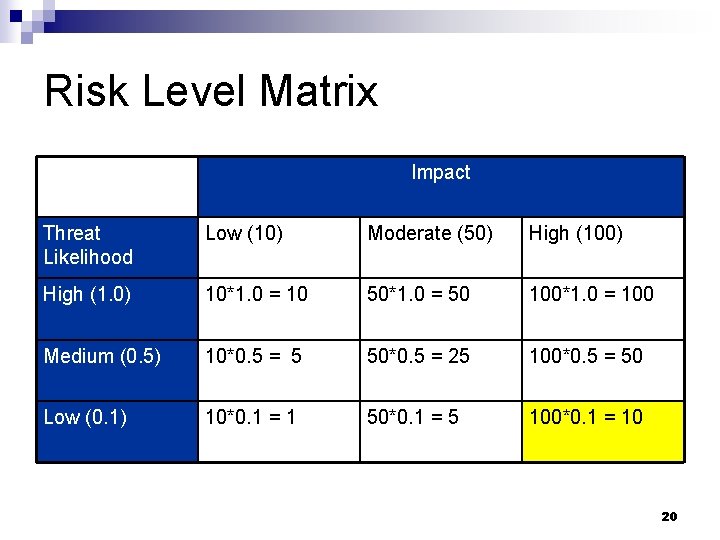
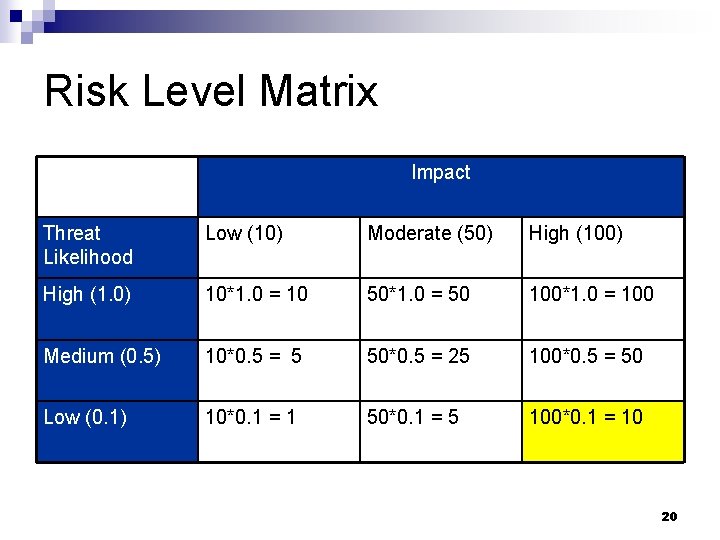
Risk Level Matrix Impact Threat Likelihood Low (10) Moderate (50) High (100) High (1. 0) 10*1. 0 = 10 50*1. 0 = 50 100*1. 0 = 100 Medium (0. 5) 10*0. 5 = 5 50*0. 5 = 25 100*0. 5 = 50 Low (0. 1) 10*0. 1 = 1 50*0. 1 = 5 100*0. 1 = 10 20
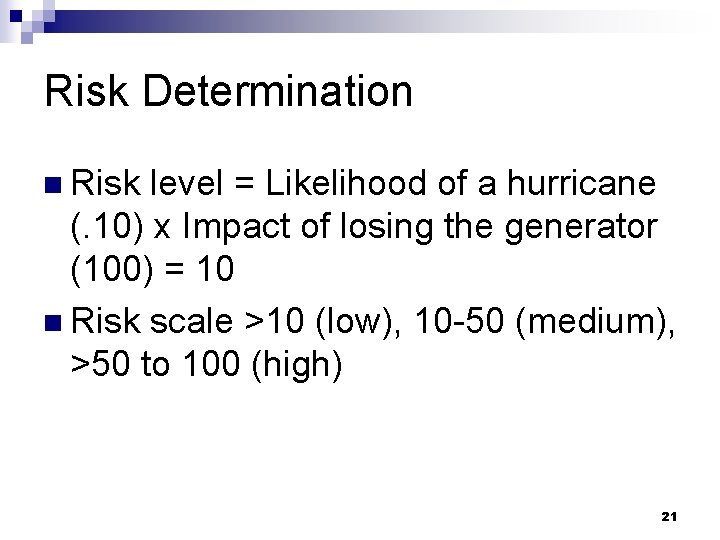
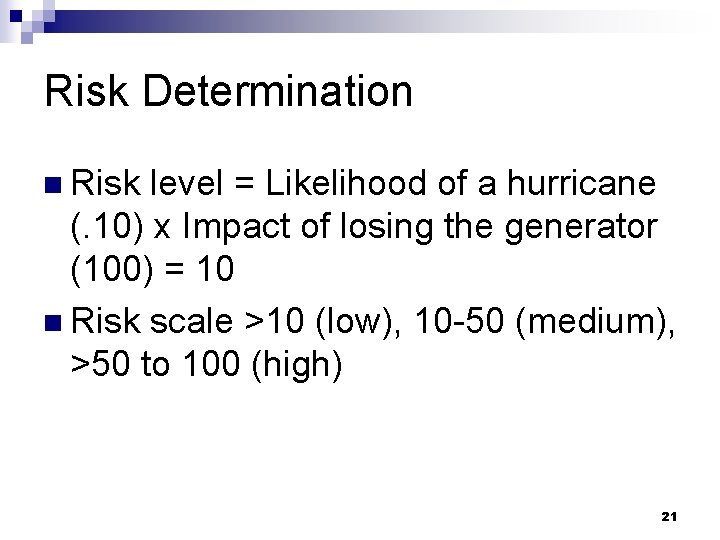
Risk Determination n Risk level = Likelihood of a hurricane (. 10) x Impact of losing the generator (100) = 10 n Risk scale >10 (low), 10 -50 (medium), >50 to 100 (high) 21
Project Deliverables n Statement of Work n Project Plan n Information System Identification Guide n Criticality Matrix n Final Report 22
Critical Success Factors Senior executive support n Full support/participation of IT Team n Competent risk assessment team n Awareness/cooperation of the user community n On-going evaluation and assessment of the IT related mission risks n 23
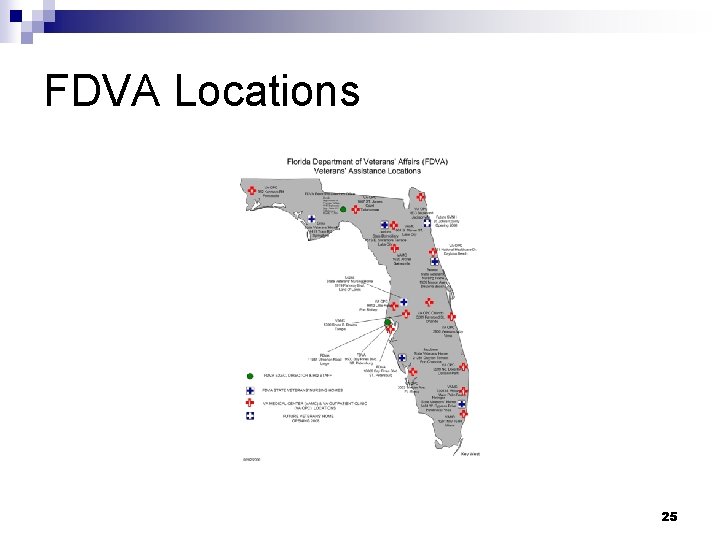
Case Study - FDVA n Florida Affairs Department of Veterans’ ¨Cabinet Agency serving 2 million veterans n Veterans Benefits and Assistance Division n State Veterans’ Homes Program ¨Operating ¨ 647 budget of $71, 000 FTE 24
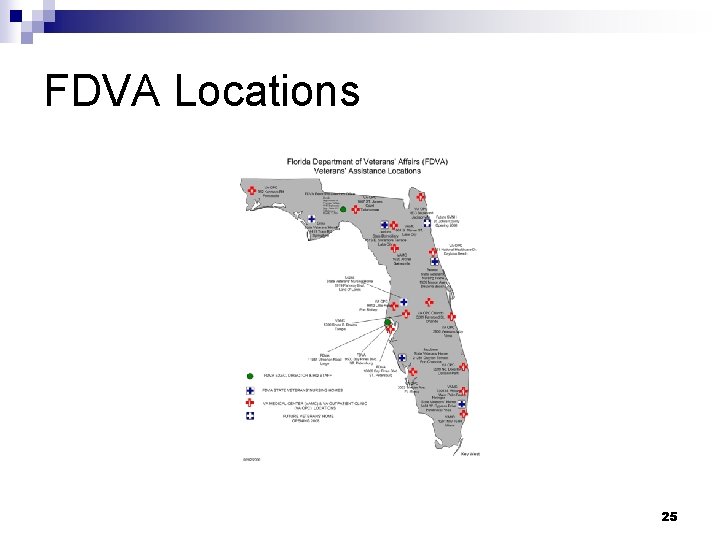
FDVA Locations 25
Case Study - Approach n Funded by Homeland Security grant n NIST 800 -30 methodology n Issued Request for Proposal n Met Federal and State requirements 26
Case Study - Value n Comprehensive n Independent n Demonstrated commitment n Validation 27
Case Study - Findings n Five key recommendations Physical security ¨ Continuity of Operations Plan (COOP) ¨ Systems testing/development ¨ Systems input/output procedures ¨ Policies and procedures ¨ 28
Case Study - Remediation Added security personnel n Revised COOP n Separated testing/development from production n Documented systems input/output procedures n Reviewed and revised policies and procedures n 29
For More Information n National Institute of Standards and Technology (Computer Security Division) http: //csrc. nist. gov/ n HIPAA Security Standard http: //www. cms. hhs. gov/securitystandard/ n ISO/IEC 27002: 2005 Information security standard http: //www. iso. org/ 30
Questions & Answers n For ¨ Further Information Contact Timothy H. Rearick 850 -339 -9094 trearick. ac@northhighland. com 31