RASPBERRY PI WHAT IS A RASPBERRY PI Raspberry
RASPBERRY PI
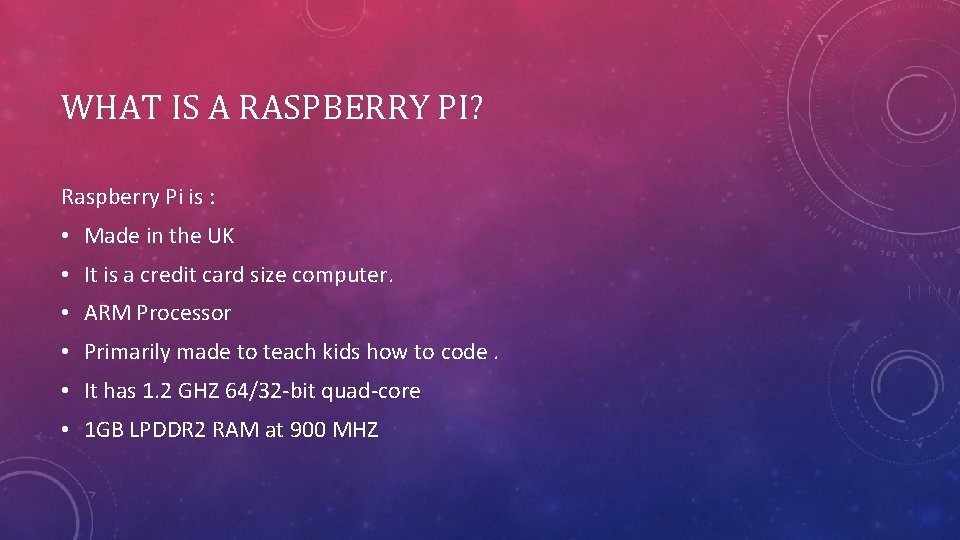
WHAT IS A RASPBERRY PI? Raspberry Pi is : • Made in the UK • It is a credit card size computer. • ARM Processor • Primarily made to teach kids how to code. • It has 1. 2 GHZ 64/32 -bit quad-core • 1 GB LPDDR 2 RAM at 900 MHZ
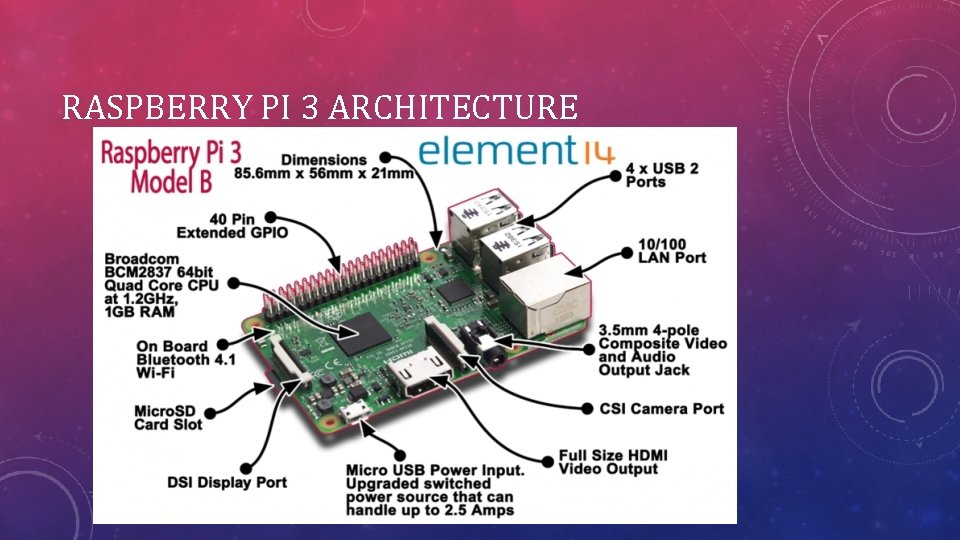
RASPBERRY PI 3 ARCHITECTURE
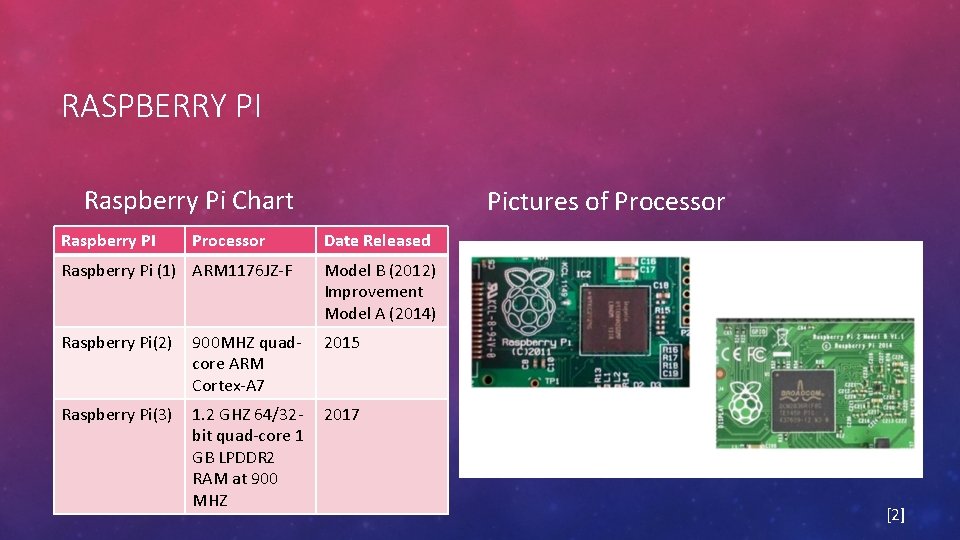
RASPBERRY PI Raspberry Pi Chart Raspberry PI Processor Pictures of Processor Date Released Raspberry Pi (1) ARM 1176 JZ-F Model B (2012) Improvement Model A (2014) Raspberry Pi(2) 900 MHZ quadcore ARM Cortex-A 7 2015 Raspberry Pi(3) 1. 2 GHZ 64/32 bit quad-core 1 GB LPDDR 2 RAM at 900 MHZ 2017 [2]
![THE OFFICIAL OPERATING SYSTEMS [3] THE OFFICIAL OPERATING SYSTEMS [3]](http://slidetodoc.com/presentation_image_h2/3be67fba4289f005895f816cdd302ab0/image-5.jpg)
THE OFFICIAL OPERATING SYSTEMS [3]
![THIRD PARTY OPERATING SYSTEMS [3] THIRD PARTY OPERATING SYSTEMS [3]](http://slidetodoc.com/presentation_image_h2/3be67fba4289f005895f816cdd302ab0/image-6.jpg)
THIRD PARTY OPERATING SYSTEMS [3]
OTHER RASPBERRY PI SOFTWARE The Link below showcase more Raspberry Pi software option: Raspberry Pi Software
![HOW TO INSTALL NEW OUT OF THE BOX (NOOBS) SOFTWARE [3] HOW TO INSTALL NEW OUT OF THE BOX (NOOBS) SOFTWARE [3]](http://slidetodoc.com/presentation_image_h2/3be67fba4289f005895f816cdd302ab0/image-8.jpg)
HOW TO INSTALL NEW OUT OF THE BOX (NOOBS) SOFTWARE [3]

WRITING SD CARDS FROM WINDOWS WITH WIN 32 DISK IMAGER
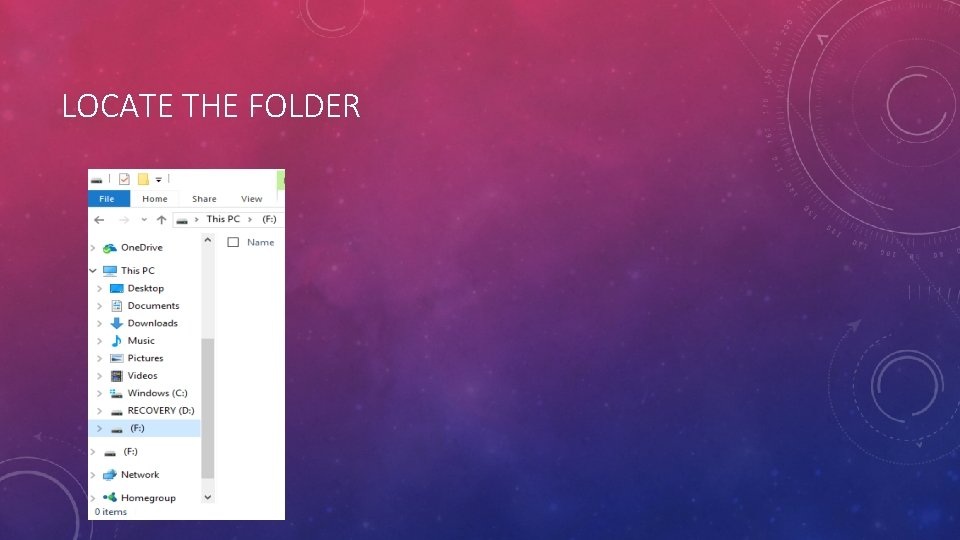
LOCATE THE FOLDER
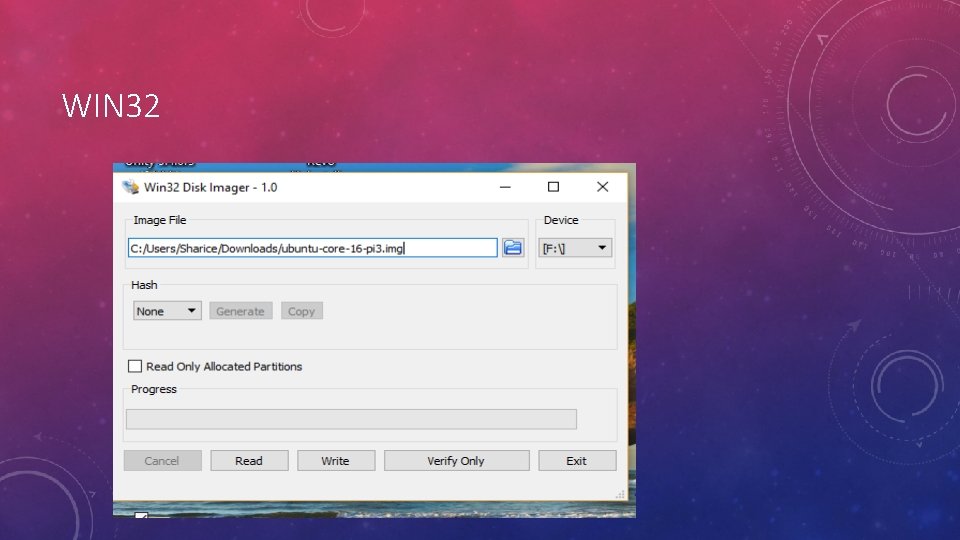
WIN 32
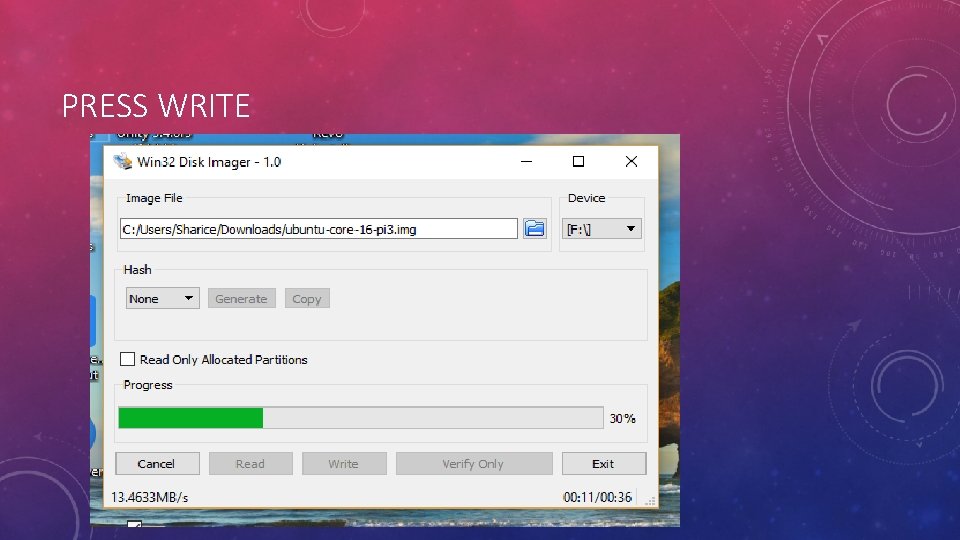
PRESS WRITE
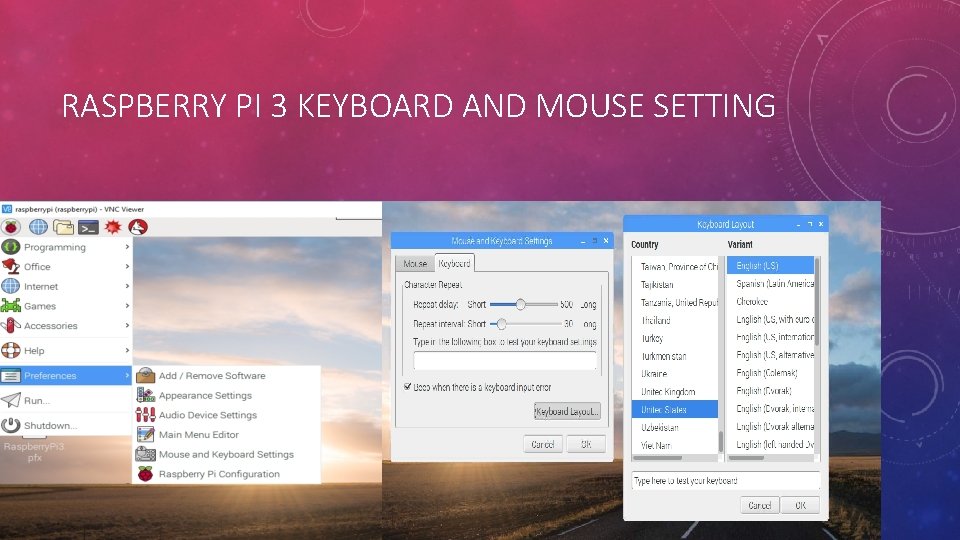
RASPBERRY PI 3 KEYBOARD AND MOUSE SETTING

DESKTOP VIEW OF NOOBS
![BLUE J JAVA IDE [1] BLUE J JAVA IDE [1]](http://slidetodoc.com/presentation_image_h2/3be67fba4289f005895f816cdd302ab0/image-15.jpg)
BLUE J JAVA IDE [1]
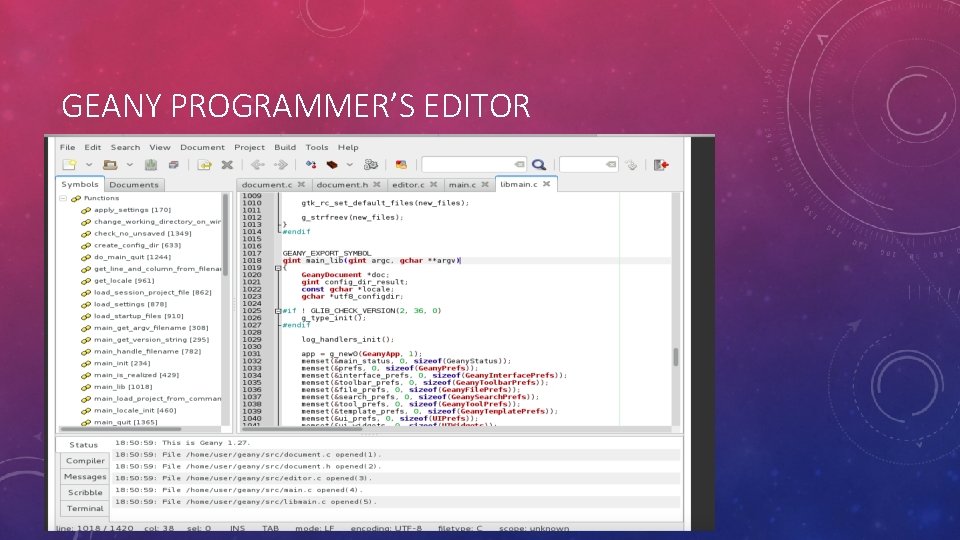
GEANY PROGRAMMER’S EDITOR
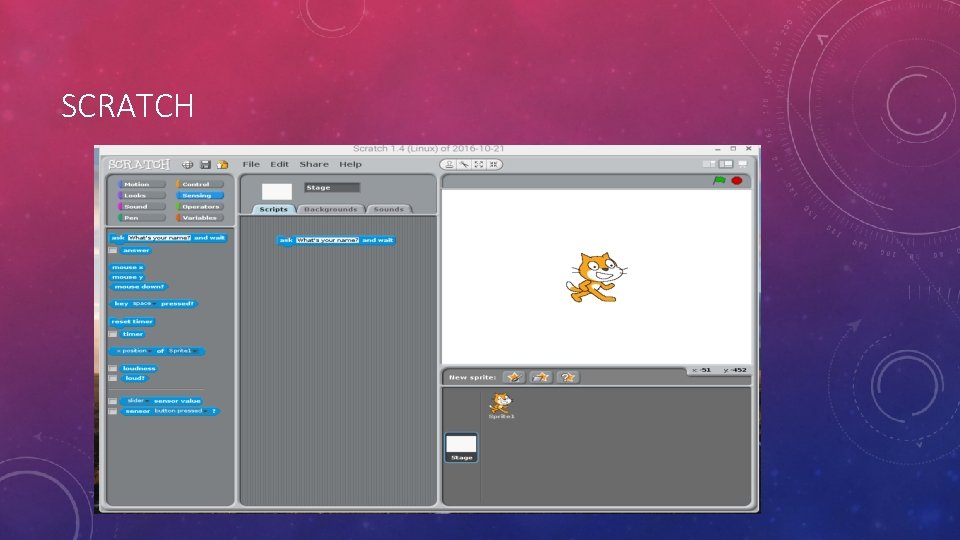
SCRATCH
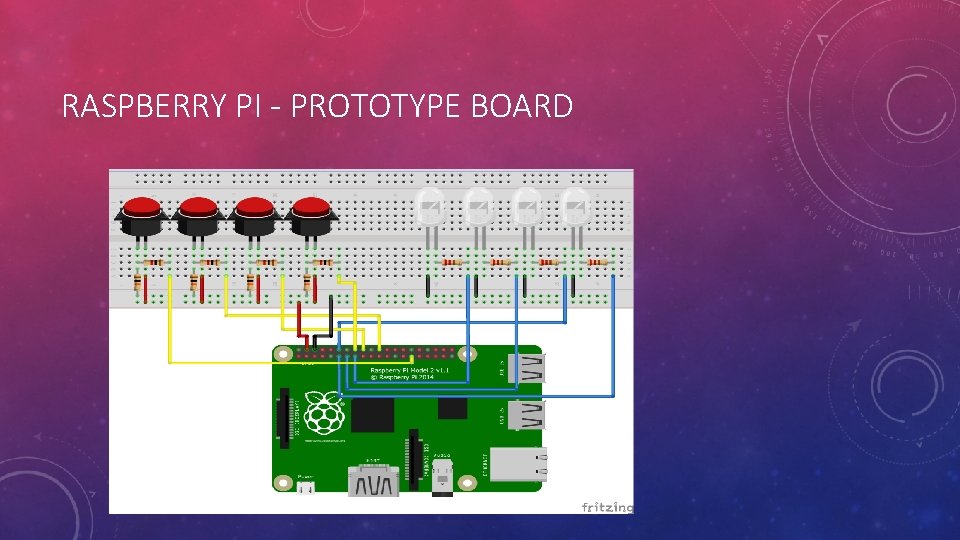
RASPBERRY PI - PROTOTYPE BOARD
![GPIO: GENERAL PURPOSE INPUT OUTPUT PINS (3 V 3) [2] GPIO: GENERAL PURPOSE INPUT OUTPUT PINS (3 V 3) [2]](http://slidetodoc.com/presentation_image_h2/3be67fba4289f005895f816cdd302ab0/image-19.jpg)
GPIO: GENERAL PURPOSE INPUT OUTPUT PINS (3 V 3) [2]
![GPIO- GENERAL PURPOSE INPUT OUTPUT [2] GPIO- GENERAL PURPOSE INPUT OUTPUT [2]](http://slidetodoc.com/presentation_image_h2/3be67fba4289f005895f816cdd302ab0/image-20.jpg)
GPIO- GENERAL PURPOSE INPUT OUTPUT [2]
![PYTHON [2] PYTHON [2]](http://slidetodoc.com/presentation_image_h2/3be67fba4289f005895f816cdd302ab0/image-21.jpg)
PYTHON [2]
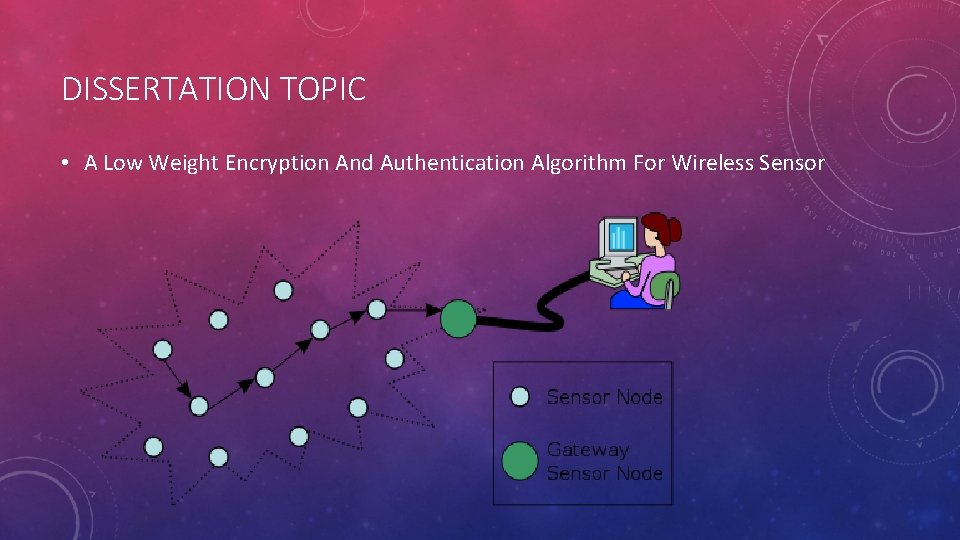
DISSERTATION TOPIC • A Low Weight Encryption And Authentication Algorithm For Wireless Sensor
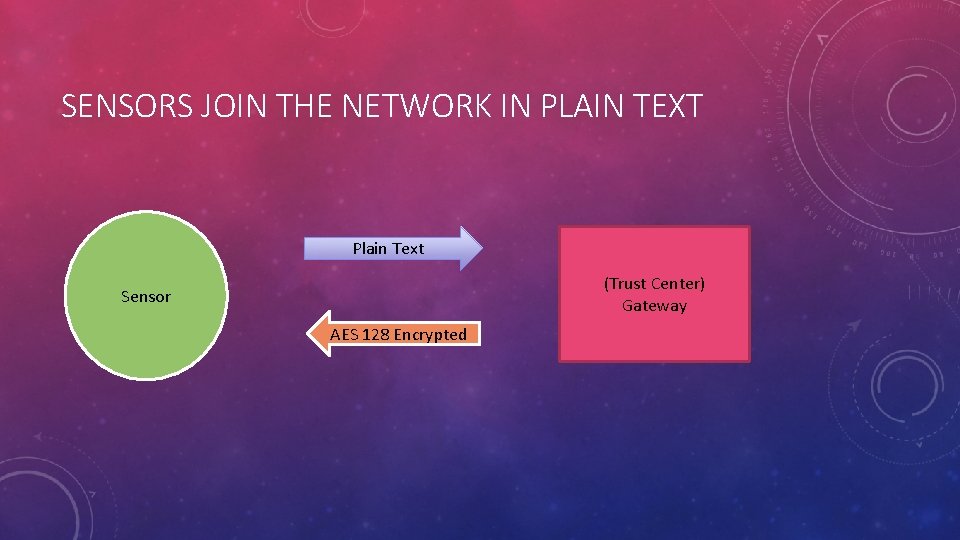
SENSORS JOIN THE NETWORK IN PLAIN TEXT Plain Text (Trust Center) Gateway Sensor AES 128 Encrypted
WIRELESS SENSOR NETWORK ATTACKS CATEGORIES • Based on Membership of attacker- (Inside Attacker and Outside Attacker) • Based on Strength- (Mote, Laptop) • Based on action taken upon data-(Passive and Active) • Based on security requirements. (Network Availability, Secret and Authentication Information Attacker)
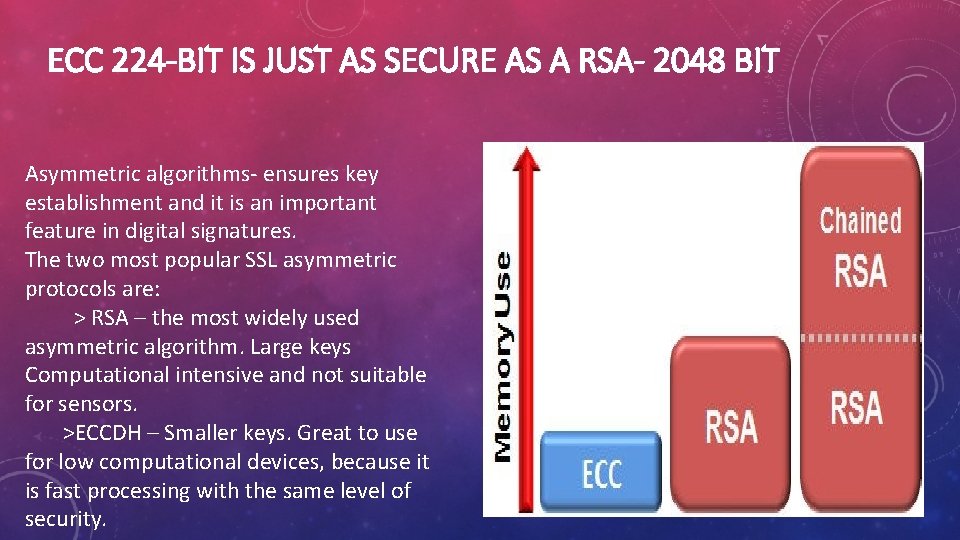
ECC 224 -BIT IS JUST AS SECURE AS A RSA- 2048 BIT Asymmetric algorithms- ensures key establishment and it is an important feature in digital signatures. The two most popular SSL asymmetric protocols are: > RSA – the most widely used asymmetric algorithm. Large keys Computational intensive and not suitable for sensors. >ECCDH – Smaller keys. Great to use for low computational devices, because it is fast processing with the same level of security.
EXPERIMENT Secure Communication between the Raspberry Pi
REFERENCES 1. Blue. J Retrieved from https: //www. bluej. org 2. Le. Masney, J, . (May 26, 2015) Introduction to Raspberry Pi Live. Lessons(Video Training) Retrieved From http: //my. safaribooksonline. com/video/hardware/raspberrypi/9780134173245? bookview=overview 3. Raspberry Pi Foundation, Raspberry Pi, Retrieved from https: //www. raspberrypi. org
- Slides: 27