SWEET SECURITY Creating a Defensive Raspberry Pi THE
SWEET SECURITY Creating a Defensive Raspberry Pi

THE HARDWARE • Raspberry Pi 2 Model B • 16 GB+ Micro SD • Case • Micro USB Power Supply
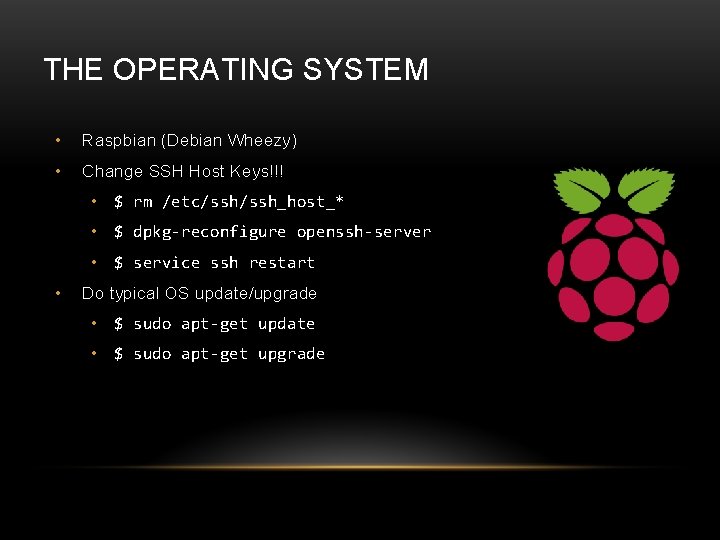
THE OPERATING SYSTEM • Raspbian (Debian Wheezy) • Change SSH Host Keys!!! • $ rm /etc/ssh_host_* • $ dpkg-reconfigure openssh-server • $ service ssh restart • Do typical OS update/upgrade • $ sudo apt-get update • $ sudo apt-get upgrade
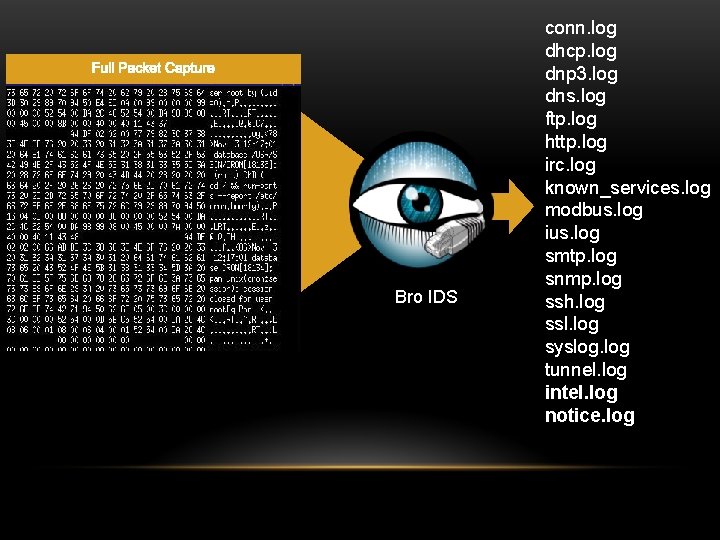
Bro IDS conn. log dhcp. log dnp 3. log dns. log ftp. log http. log irc. log known_services. log modbus. log ius. log smtp. log snmp. log ssh. log ssl. log syslog. log tunnel. log intel. log notice. log
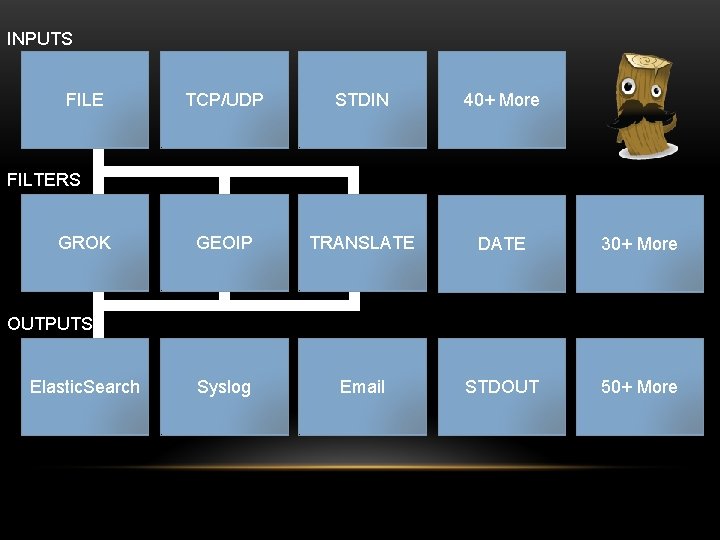
INPUTS FILE TCP/UDP STDIN 40+ More GEOIP TRANSLATE DATE 30+ More Syslog Email STDOUT 50+ More FILTERS GROK OUTPUTS Elastic. Search
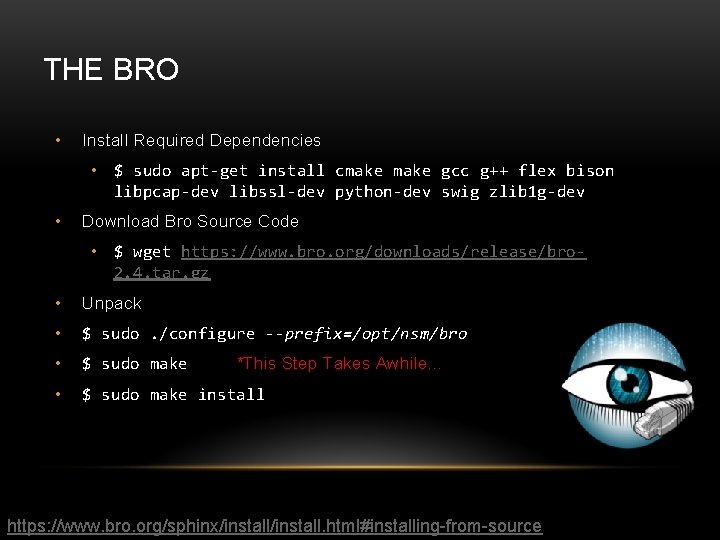
THE BRO • Install Required Dependencies • $ sudo apt-get install cmake gcc g++ flex bison libpcap-dev libssl-dev python-dev swig zlib 1 g-dev • Download Bro Source Code • $ wget https: //www. bro. org/downloads/release/bro 2. 4. tar. gz • Unpack • $ sudo. /configure --prefix=/opt/nsm/bro • $ sudo make *This Step Takes Awhile… • $ sudo make install https: //www. bro. org/sphinx/install. html#installing-from-source
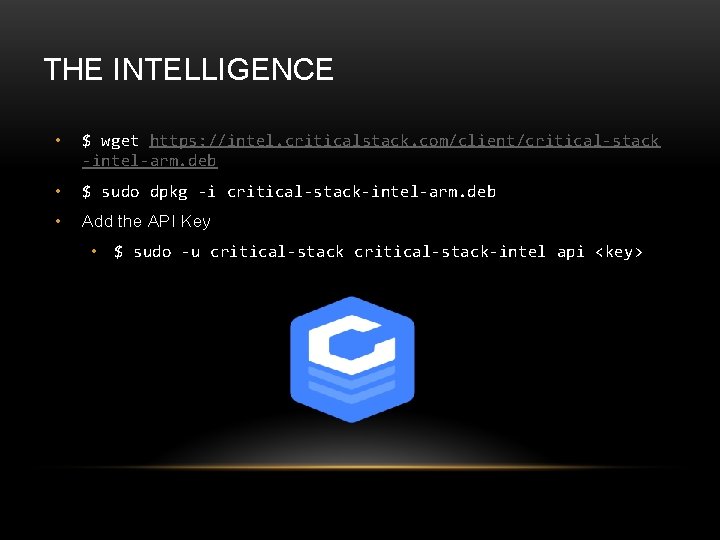
THE INTELLIGENCE • $ wget https: //intel. criticalstack. com/client/critical-stack -intel-arm. deb • $ sudo dpkg -i critical-stack-intel-arm. deb • Add the API Key • $ sudo -u critical-stack-intel api <key>
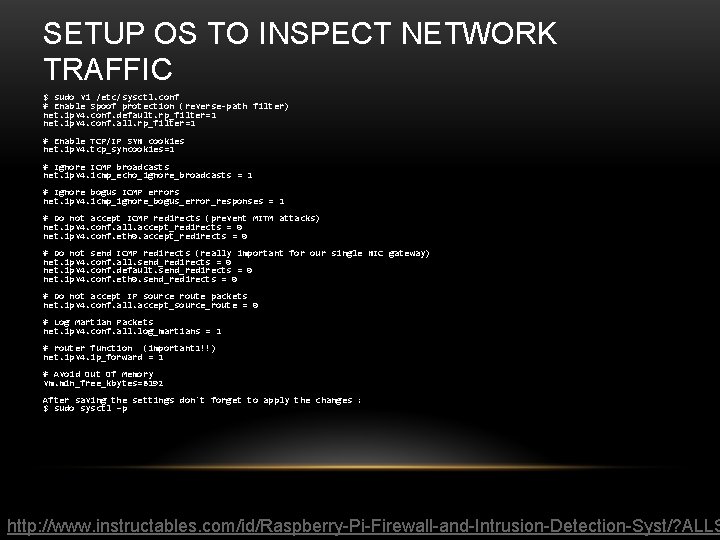
SETUP OS TO INSPECT NETWORK TRAFFIC $ sudo vi /etc/sysctl. conf # Enable Spoof protection (reverse-path filter) net. ipv 4. conf. default. rp_filter=1 net. ipv 4. conf. all. rp_filter=1 # Enable TCP/IP SYN cookies net. ipv 4. tcp_syncookies=1 # Ignore ICMP broadcasts net. ipv 4. icmp_echo_ignore_broadcasts = 1 # Ignore bogus ICMP errors net. ipv 4. icmp_ignore_bogus_error_responses = 1 # Do not accept ICMP redirects (prevent MITM attacks) net. ipv 4. conf. all. accept_redirects = 0 net. ipv 4. conf. eth 0. accept_redirects = 0 # Do not send ICMP redirects (really important for our single NIC gateway) net. ipv 4. conf. all. send_redirects = 0 net. ipv 4. conf. default. send_redirects = 0 net. ipv 4. conf. eth 0. send_redirects = 0 # Do not accept IP source route packets net. ipv 4. conf. all. accept_source_route = 0 # Log Martian Packets net. ipv 4. conf. all. log_martians = 1 # router function (important 1!!) net. ipv 4. ip_forward = 1 # Avoid Out Of Memory vm. min_free_kbytes=8192 After saving the settings don't forget to apply the changes : $ sudo sysctl –p http: //www. instructables. com/id/Raspberry-Pi-Firewall-and-Intrusion-Detection-Syst/? ALLS
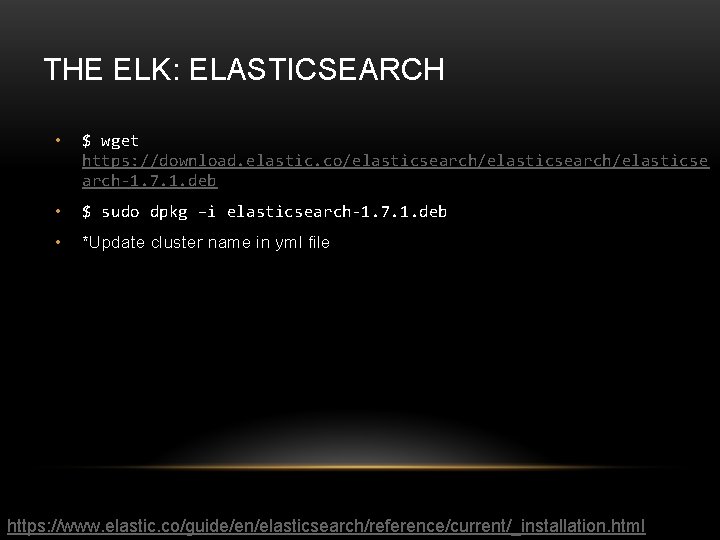
THE ELK: ELASTICSEARCH • $ wget https: //download. elastic. co/elasticsearch/elasticse arch-1. 7. 1. deb • $ sudo dpkg –i elasticsearch-1. 7. 1. deb • *Update cluster name in yml file https: //www. elastic. co/guide/en/elasticsearch/reference/current/_installation. html
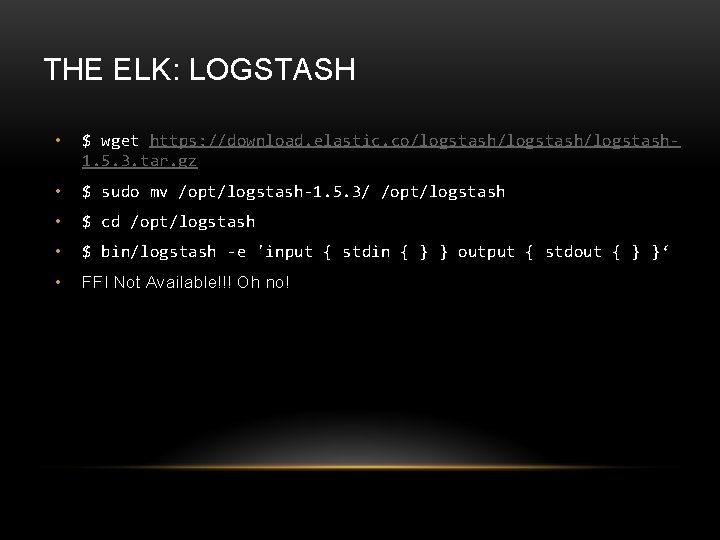
THE ELK: LOGSTASH • $ wget https: //download. elastic. co/logstash/logstash 1. 5. 3. tar. gz • $ sudo mv /opt/logstash-1. 5. 3/ /opt/logstash • $ cd /opt/logstash • $ bin/logstash -e 'input { stdin { } } output { stdout { } }‘ • FFI Not Available!!! Oh no!
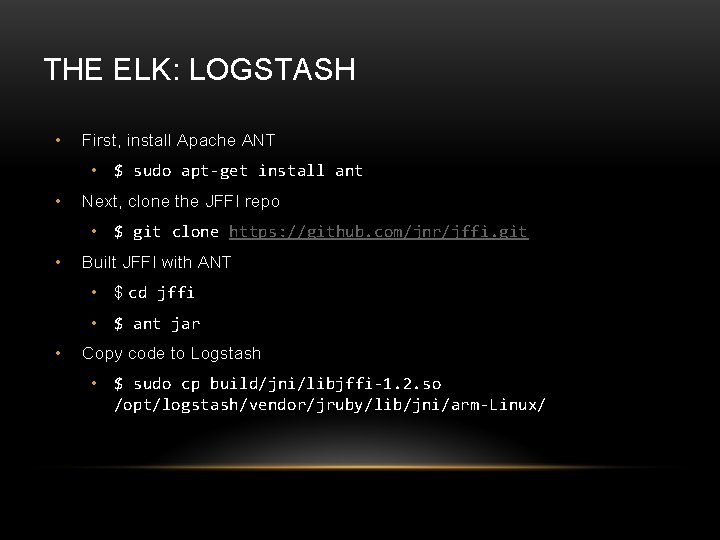
THE ELK: LOGSTASH • First, install Apache ANT • $ sudo apt-get install ant • Next, clone the JFFI repo • $ git clone https: //github. com/jnr/jffi. git • Built JFFI with ANT • $ cd jffi • $ ant jar • Copy code to Logstash • $ sudo cp build/jni/libjffi-1. 2. so /opt/logstash/vendor/jruby/lib/jni/arm-Linux/
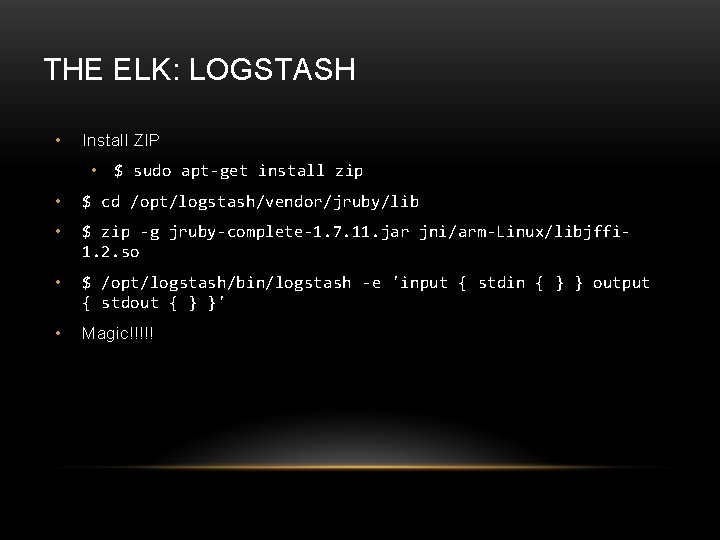
THE ELK: LOGSTASH • Install ZIP • $ sudo apt-get install zip • $ cd /opt/logstash/vendor/jruby/lib • $ zip -g jruby-complete-1. 7. 11. jar jni/arm-Linux/libjffi 1. 2. so • $ /opt/logstash/bin/logstash -e 'input { stdin { } } output { stdout { } }' • Magic!!!!!
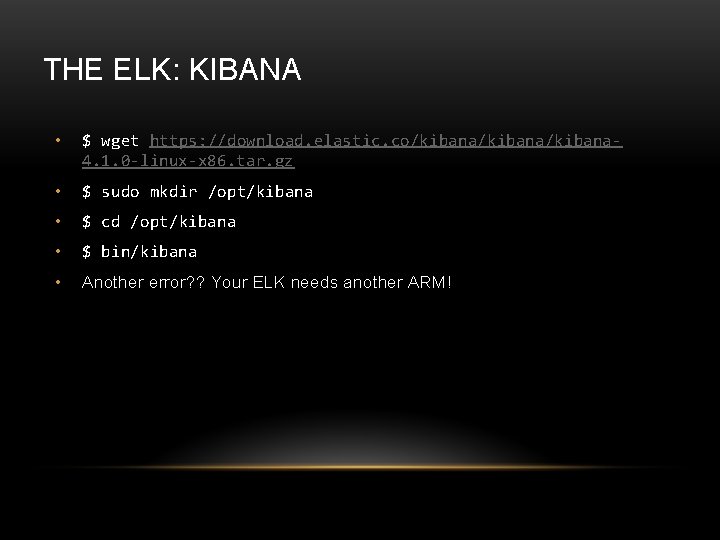
THE ELK: KIBANA • $ wget https: //download. elastic. co/kibana/kibana 4. 1. 0 -linux-x 86. tar. gz • $ sudo mkdir /opt/kibana • $ cd /opt/kibana • $ bin/kibana • Another error? ? Your ELK needs another ARM!
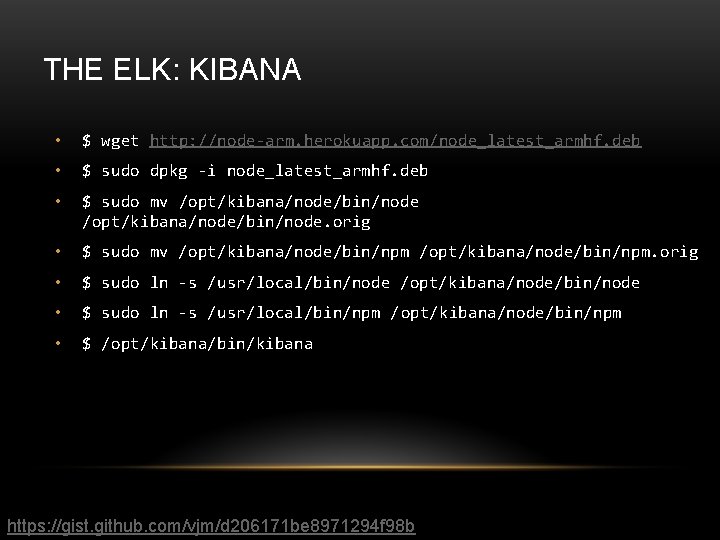
THE ELK: KIBANA • $ wget http: //node-arm. herokuapp. com/node_latest_armhf. deb • $ sudo dpkg -i node_latest_armhf. deb • $ sudo mv /opt/kibana/node/bin/node. orig • $ sudo mv /opt/kibana/node/bin/npm. orig • $ sudo ln -s /usr/local/bin/node /opt/kibana/node/bin/node • $ sudo ln -s /usr/local/bin/npm /opt/kibana/node/bin/npm • $ /opt/kibana/bin/kibana https: //gist. github. com/vjm/d 206171 be 8971294 f 98 b
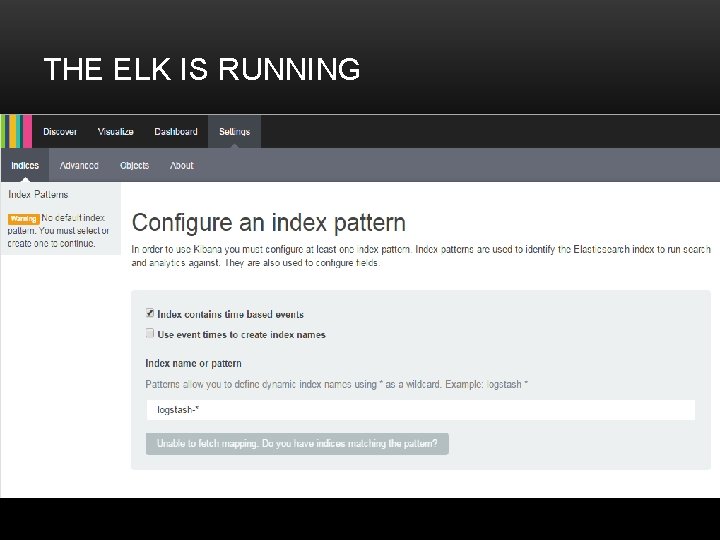
THE ELK IS RUNNING
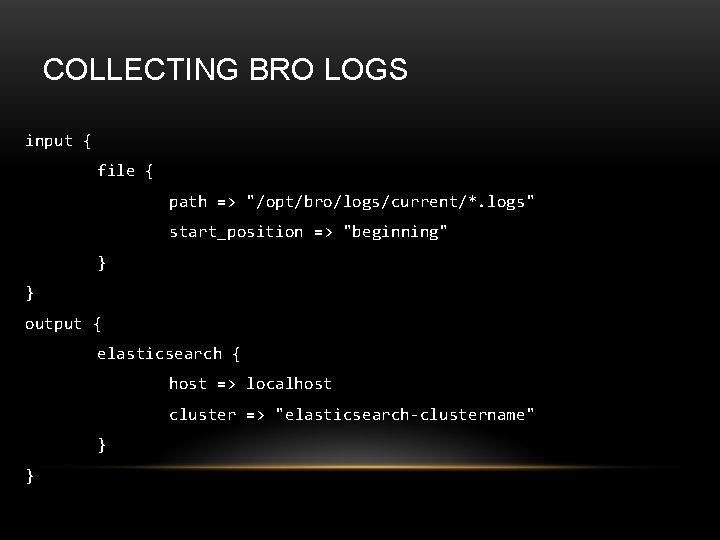
COLLECTING BRO LOGS input { file { path => "/opt/bro/logs/current/*. logs" start_position => "beginning" } } output { elasticsearch { host => localhost cluster => "elasticsearch-clustername" } }
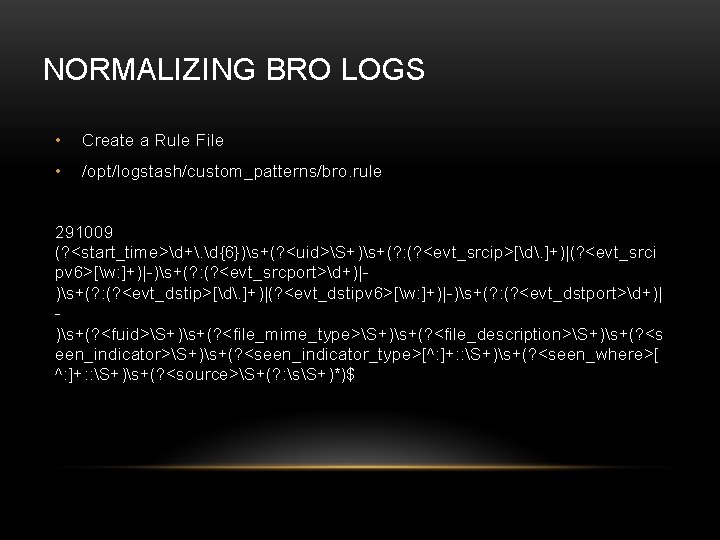
NORMALIZING BRO LOGS • Create a Rule File • /opt/logstash/custom_patterns/bro. rule 291009 (? <start_time>d+. d{6})s+(? <uid>S+)s+(? : (? <evt_srcip>[d. ]+)|(? <evt_srci pv 6>[w: ]+)|-)s+(? : (? <evt_srcport>d+)|)s+(? : (? <evt_dstip>[d. ]+)|(? <evt_dstipv 6>[w: ]+)|-)s+(? : (? <evt_dstport>d+)| )s+(? <fuid>S+)s+(? <file_mime_type>S+)s+(? <file_description>S+)s+(? <s een_indicator>S+)s+(? <seen_indicator_type>[^: ]+: : S+)s+(? <seen_where>[ ^: ]+: : S+)s+(? <source>S+(? : sS+)*)$
![NORMALIZING BRO LOGS filter { if [message] =~ /^(d+. d{6}s+S+s+(? : [d. ]+|[w: ]+|-)s+(? NORMALIZING BRO LOGS filter { if [message] =~ /^(d+. d{6}s+S+s+(? : [d. ]+|[w: ]+|-)s+(?](http://slidetodoc.com/presentation_image_h/ea9a4af6b2552204513b5f9aa77f0b69/image-18.jpg)
NORMALIZING BRO LOGS filter { if [message] =~ /^(d+. d{6}s+S+s+(? : [d. ]+|[w: ]+|-)s+(? : d+|)s+S+s+S+s+[^: ]+: : S+s+S+(? : sS+)*$)/ { grok{ patterns_dir => "/opt/logstash/custom_patterns" match => { message => "%{291009}" } add_field => [ "rule_id", "291009" ] add_field => [ "Device Type", "IPSIDSDevice" ] add_field => [ "Object", "Process" ] add_field => [ "Action", "General" ] add_field => [ "Status", "Informational" ] } } }
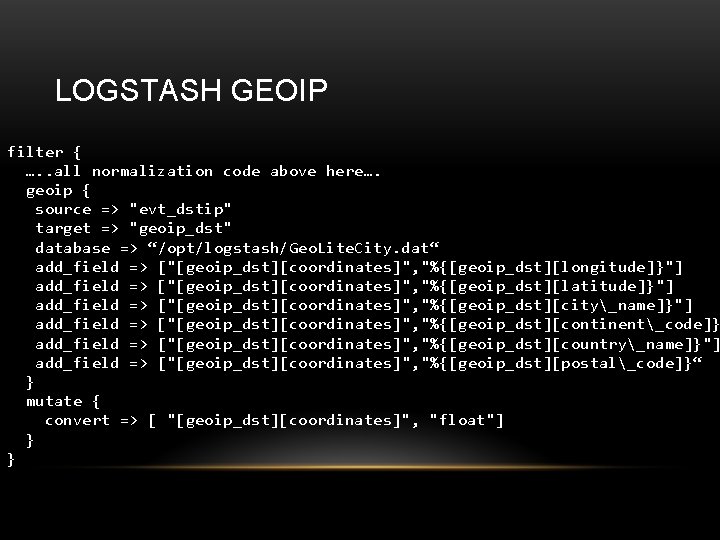
LOGSTASH GEOIP filter { …. . all normalization code above here…. geoip { source => "evt_dstip" target => "geoip_dst" database => “/opt/logstash/Geo. Lite. City. dat“ add_field => ["[geoip_dst][coordinates]", "%{[geoip_dst][longitude]}"] add_field => ["[geoip_dst][coordinates]", "%{[geoip_dst][latitude]}"] add_field => ["[geoip_dst][coordinates]", "%{[geoip_dst][city_name]}"] add_field => ["[geoip_dst][coordinates]", "%{[geoip_dst][continent_code]} add_field => ["[geoip_dst][coordinates]", "%{[geoip_dst][country_name]}"] add_field => ["[geoip_dst][coordinates]", "%{[geoip_dst][postal_code]}“ } mutate { convert => [ "[geoip_dst][coordinates]", "float"] } }
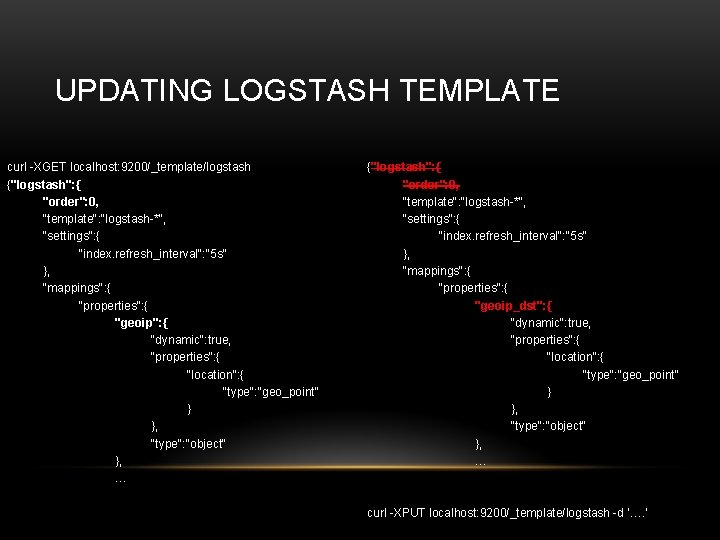
UPDATING LOGSTASH TEMPLATE curl -XGET localhost: 9200/_template/logstash {"logstash": { "order": 0, "template": "logstash-*", "settings": { "index. refresh_interval": "5 s" }, "mappings": { "properties": { "geoip": { "dynamic": true, "properties": { "location": { "type": "geo_point" } }, "type": "object" }, … {"logstash": { "order": 0, "template": "logstash-*", "settings": { "index. refresh_interval": "5 s" }, "mappings": { "properties": { "geoip_dst": { "dynamic": true, "properties": { "location": { "type": "geo_point" } }, "type": "object" }, … curl -XPUT localhost: 9200/_template/logstash -d ‘…. ’

DATE MATCH filter {. . all normalization code above here…. . …all Geo. IP code here. . date { match => [ "start_time", "UNIX" ] } }
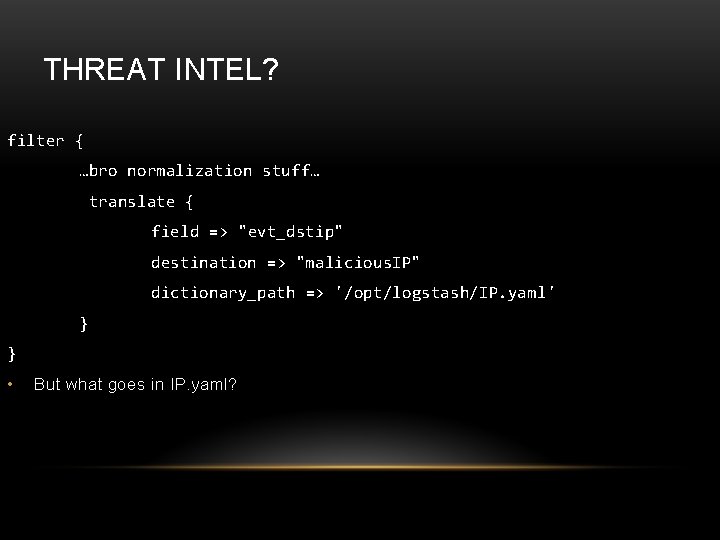
THREAT INTEL? filter { …bro normalization stuff… translate { field => "evt_dstip" destination => "malicious. IP" dictionary_path => '/opt/logstash/IP. yaml' } } • But what goes in IP. yaml?
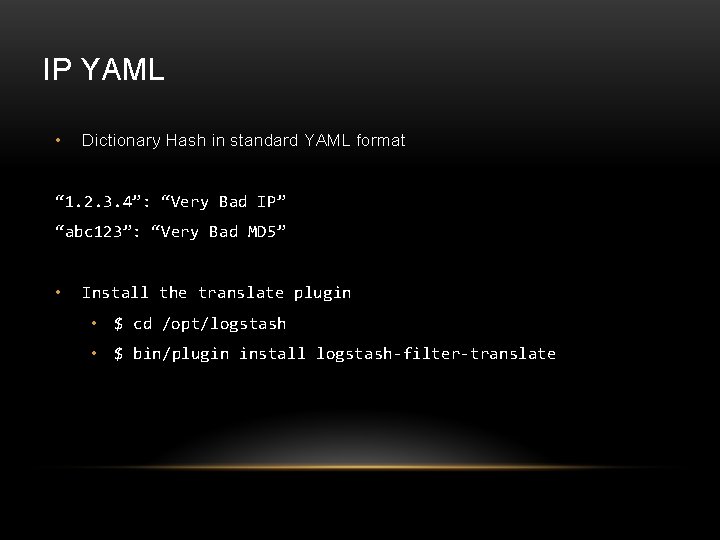
IP YAML • Dictionary Hash in standard YAML format “ 1. 2. 3. 4”: “Very Bad IP” “abc 123”: “Very Bad MD 5” • Install the translate plugin • $ cd /opt/logstash • $ bin/plugin install logstash-filter-translate

BRINGING IT TOGETHER
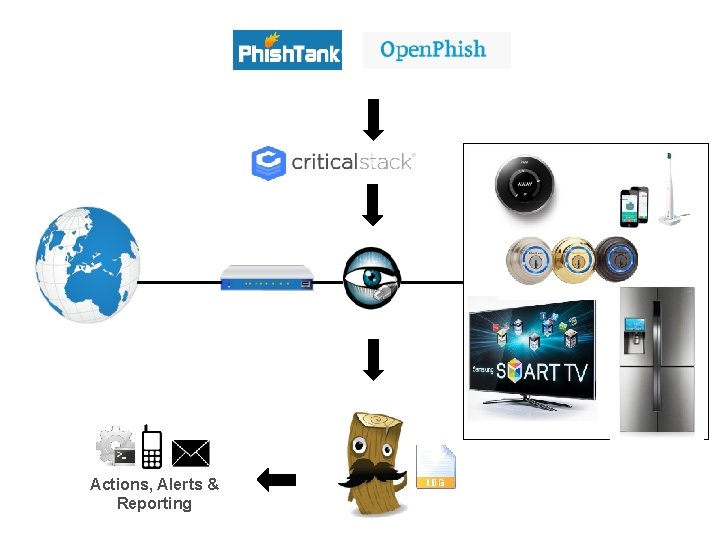
Internet Actions, Alerts & Reporting

CONTACT ME FOR MORE INFO tsmith@tripwire. com @mrtrav
- Slides: 26