Publickey Cryptosystem using Non commutative ring 2002 10
Public-key Cryptosystem using Non commutative ring 2002. 10 Network Security 20022052 Min Sung Jun
Contents 1. Introduction 2. Objectives of my project 3. Newly proposed schemes - Ring based scheme ( NTRU ) - Sparse polynomials based scheme 4. Questions 5. References 2
1. Introduction n Most cryptographic protocols and algorithms base on abelian groups and finite fields n Advents of the new cryptographic systems l l l NTRU : Ring based cryptosystem D. Grant et. al scheme : based on sparse polynomials Braid : using non abelian group n The reason for these advents l To offer more efficiency, secrecy -> By using a specific property 3
2. Objectives of my project n Analysis of the new schemes l l Design method (know-how) Security analysis n Development of the schemes l l More secure or more efficient by using non commutative rings Proposal specific cryptographic schemes in NTRU or D. Grant scheme n Comparison l Commutative VS Non -commutative 4
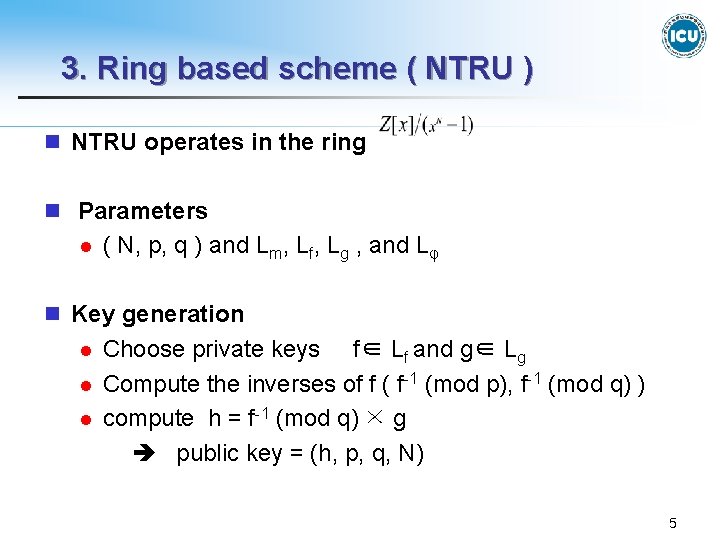
3. Ring based scheme ( NTRU ) n NTRU operates in the ring n Parameters l ( N, p, q ) and Lm, Lf, Lg , and Lφ n Key generation l l l Choose private keys f∈ Lf and g∈ Lg Compute the inverses of f ( f-1 (mod p), f-1 (mod q) ) compute h = f-1 (mod q) × g public key = (h, p, q, N) 5
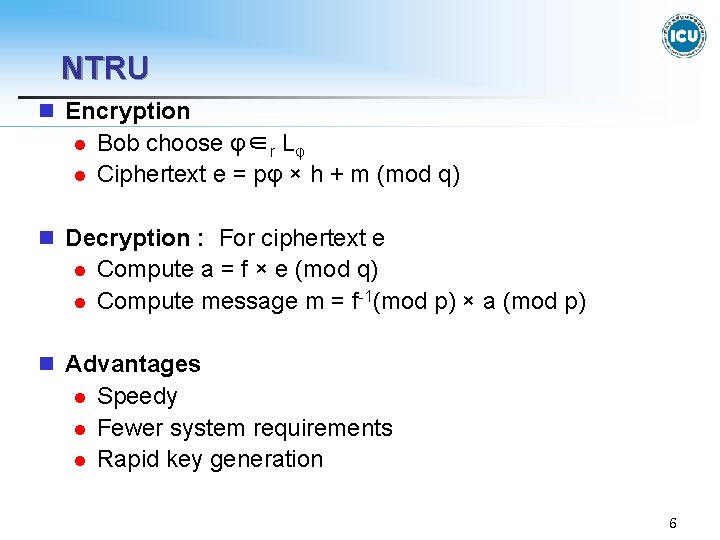
NTRU n Encryption l l Bob choose φ∈r Lφ Ciphertext e = pφ × h + m (mod q) n Decryption : For ciphertext e l l Compute a = f × e (mod q) Compute message m = f-1(mod p) × a (mod p) n Advantages l l l Speedy Fewer system requirements Rapid key generation 6
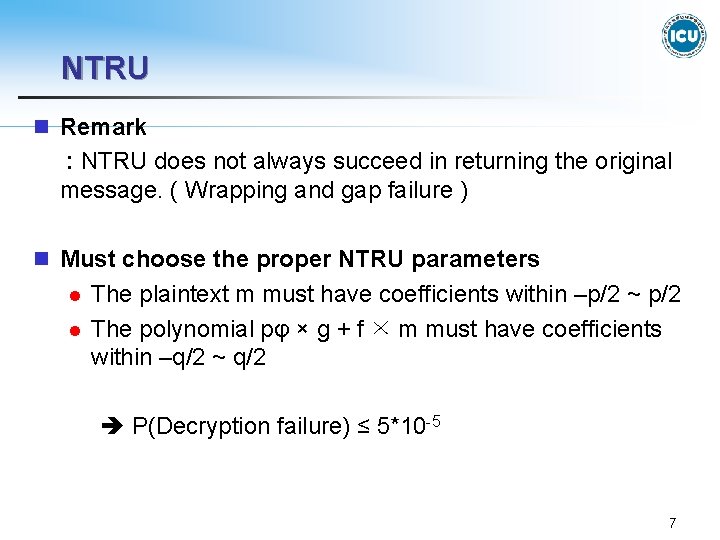
NTRU n Remark : NTRU does not always succeed in returning the original message. ( Wrapping and gap failure ) n Must choose the proper NTRU parameters l l The plaintext m must have coefficients within –p/2 ~ p/2 The polynomial pφ × g + f × m must have coefficients within –q/2 ~ q/2 P(Decryption failure) ≤ 5*10 -5 7
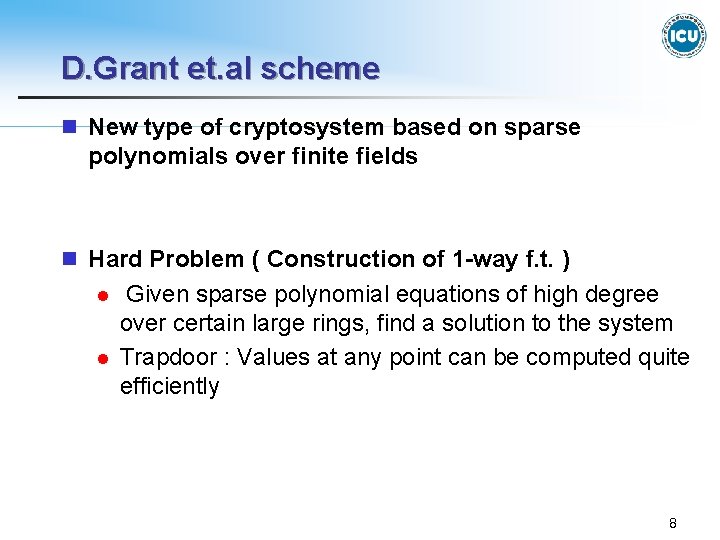
D. Grant et. al scheme n New type of cryptosystem based on sparse polynomials over finite fields n Hard Problem ( Construction of 1 -way f. t. ) l l Given sparse polynomial equations of high degree over certain large rings, find a solution to the system Trapdoor : Values at any point can be computed quite efficiently 8
![D. Grant et. al scheme n Construction of a Cryptosystem [Step 1] - System D. Grant et. al scheme n Construction of a Cryptosystem [Step 1] - System](http://slidetodoc.com/presentation_image/30ffdf9ff3f31bba1e58810b1ec869cf/image-9.jpg)
D. Grant et. al scheme n Construction of a Cryptosystem [Step 1] - System parameters l l Choose a large Fq Choose si , ti ∈Z+ , (1≤i≤k) [Step 2] l l Alice puts e 1 = 1, and selects v∈r. Fq Sekect e 2, e 3, …, ek∈r. Zq-1 [Step 3] l l l Alice selects h 1, h 2, …, hk ∈ Fq[x 1, …, xk] s. t. deg(hi)≤q-1 & at most ti-1 monomials Compute fi(x 1, …, xk) = hi(x 1, …, xk) - hi(a 1, …, ak), where ai = vei {f 1, …, fk} : Public 9
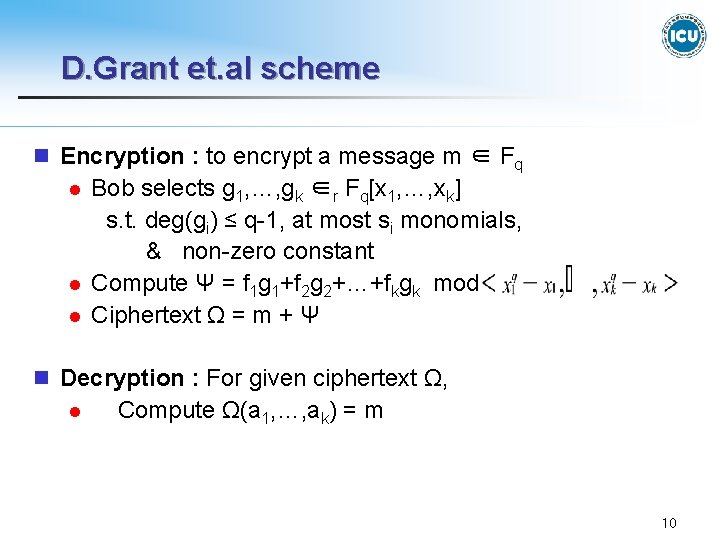
D. Grant et. al scheme n Encryption : to encrypt a message m ∈ Fq l l l Bob selects g 1, …, gk ∈r Fq[x 1, …, xk] s. t. deg(gi) ≤ q-1, at most si monomials, & non-zero constant Compute Ψ = f 1 g 1+f 2 g 2+…+fkgk mod Ciphertext Ω = m + Ψ n Decryption : For given ciphertext Ω, l Compute Ω(a 1, …, ak) = m 10
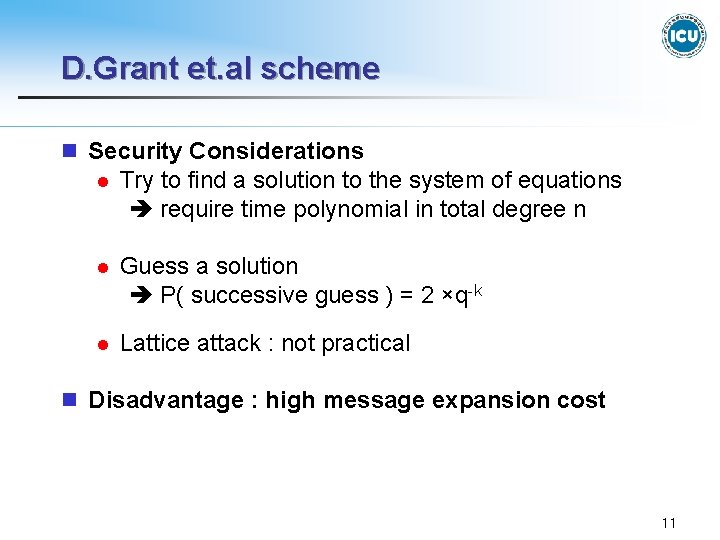
D. Grant et. al scheme n Security Considerations l Try to find a solution to the system of equations require time polynomial in total degree n l Guess a solution P( successive guess ) = 2 ×q-k l Lattice attack : not practical n Disadvantage : high message expansion cost 11
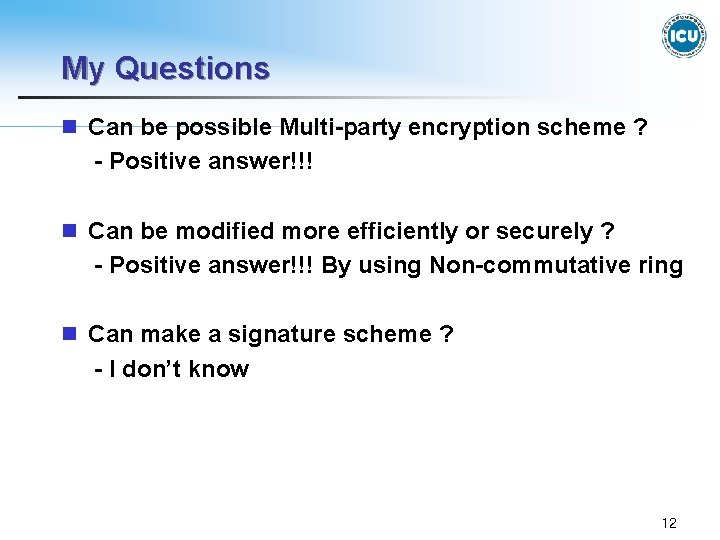
My Questions n Can be possible Multi-party encryption scheme ? - Positive answer!!! n Can be modified more efficiently or securely ? - Positive answer!!! By using Non-commutative ring n Can make a signature scheme ? - I don’t know 12
![References [1] J. Hoffstein, J. Pipher, and J. H. Silverman, “NTRU : A Ring-Based References [1] J. Hoffstein, J. Pipher, and J. H. Silverman, “NTRU : A Ring-Based](http://slidetodoc.com/presentation_image/30ffdf9ff3f31bba1e58810b1ec869cf/image-13.jpg)
References [1] J. Hoffstein, J. Pipher, and J. H. Silverman, “NTRU : A Ring-Based Public Key Cryptosystem”, Proceedings of ANTS , Portland (1998), Springer-Verlag [2] D. Grant et al, “ A Public key cryptosystem based on sparse polynomials”, Proc. International Conference on Coding Theory, Cryptography and Related Areas, Guanajuato, (1988), Springer-Verlag, Berlin, 2000, 114 -121 [3] P. Garret, Making, Breaking Codes : An Introduction to Cryptology, (2001), Prentice-Hall [4] T. Y. Lam, A First Course in Noncommutative Rings, (1990), Springer-Verlag New York. [5] http: //www. ntru. com 13
- Slides: 13